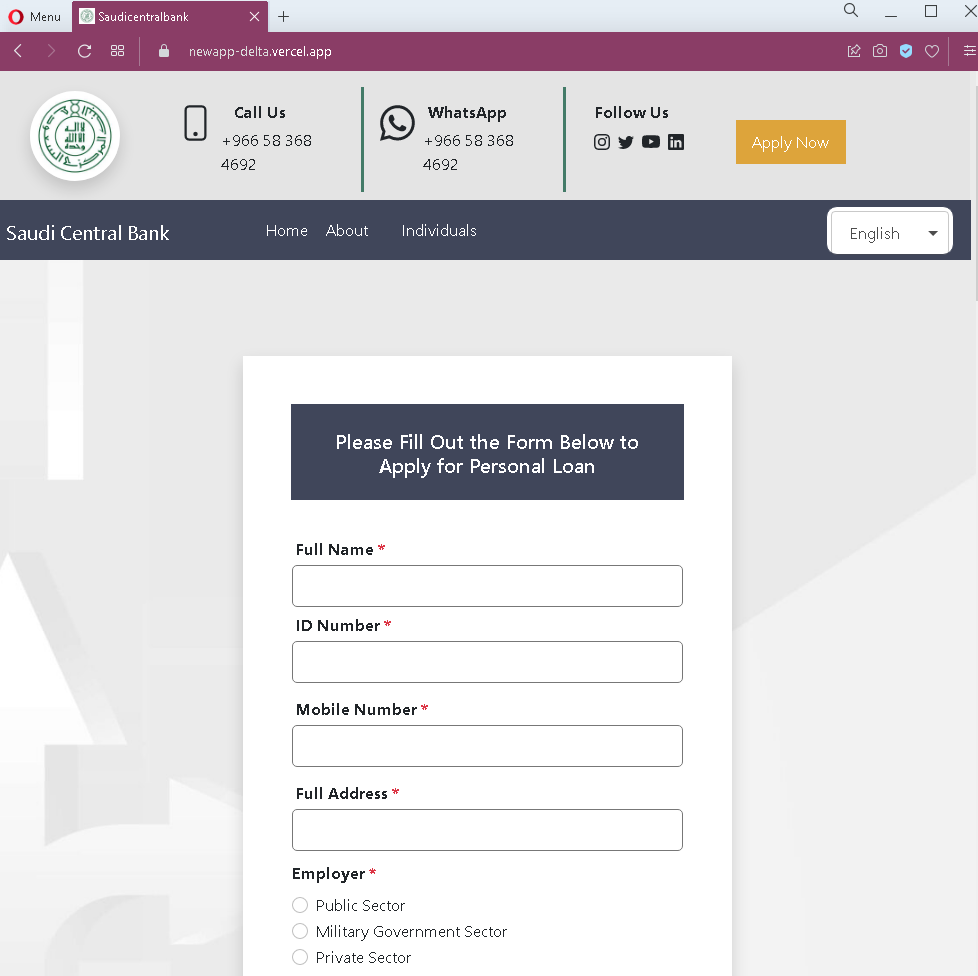
Gumtree Classifieds Phishing – Fake “Payment Received” Scam (UK Variant)
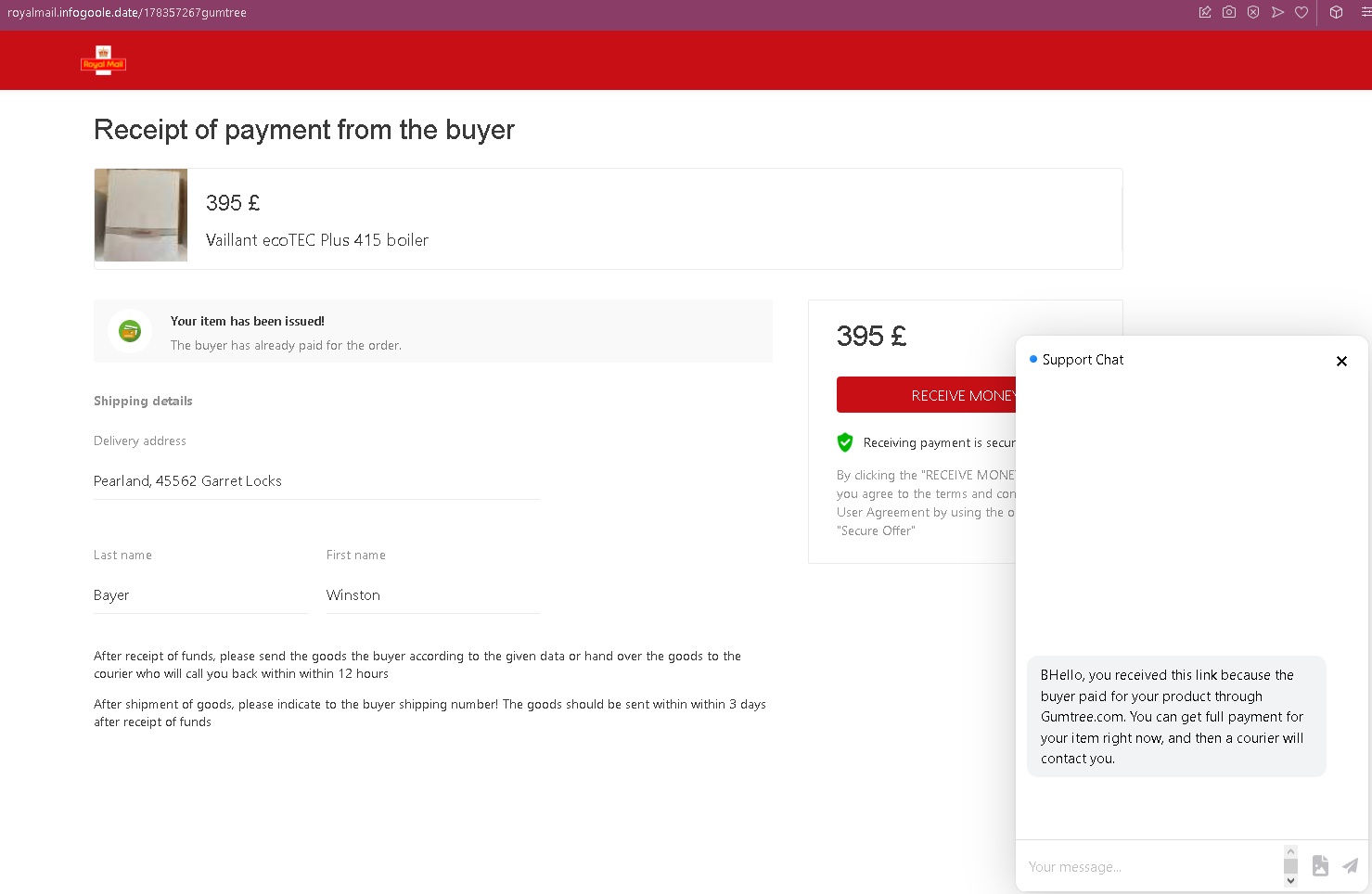
This phishing campaign impersonates Gumtree, a widely used classified advertisements platform in the United Kingdom. The scam targets sellers by creating a fake “payment received” page that claims a buyer has already paid for an item. The page includes a fake chat support window to add credibility and pressure the seller into entering credit card details on a following page.
How it works:
A seller receives a message—likely via Gumtree’s messaging system, SMS, email, or another chat app—from a supposed buyer claiming to have paid for the item. The message includes a link to this phishing page.
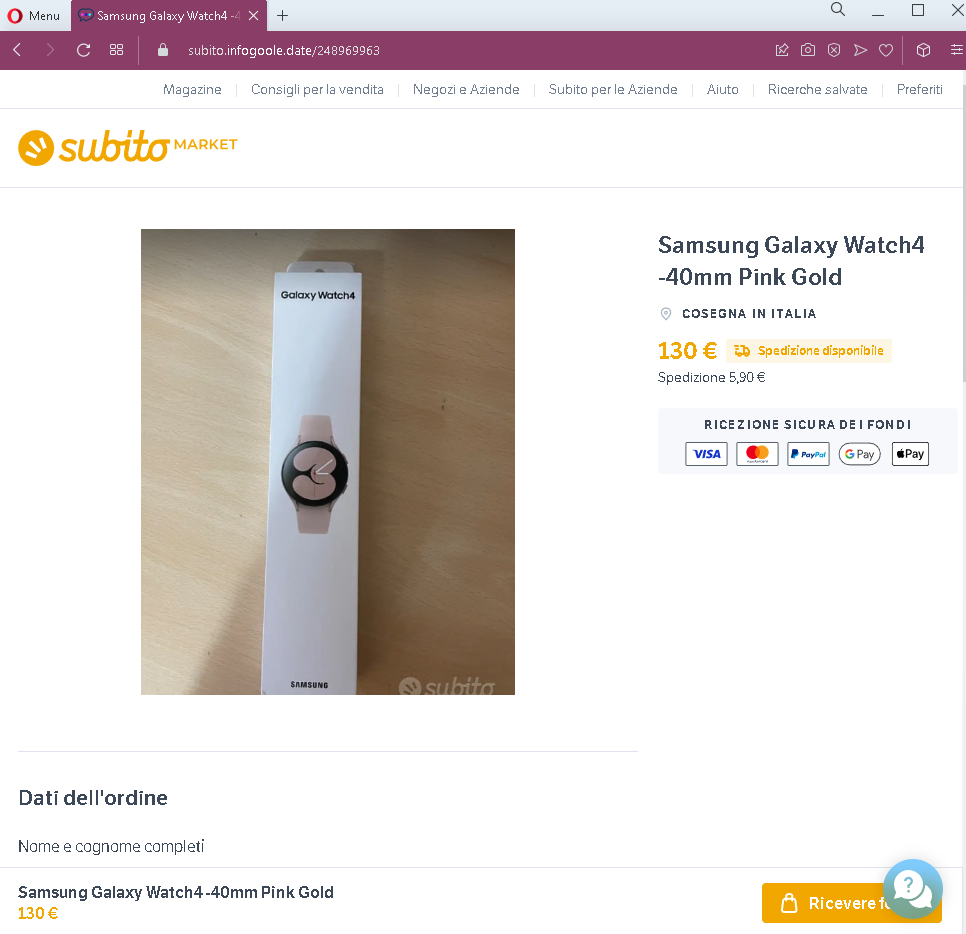
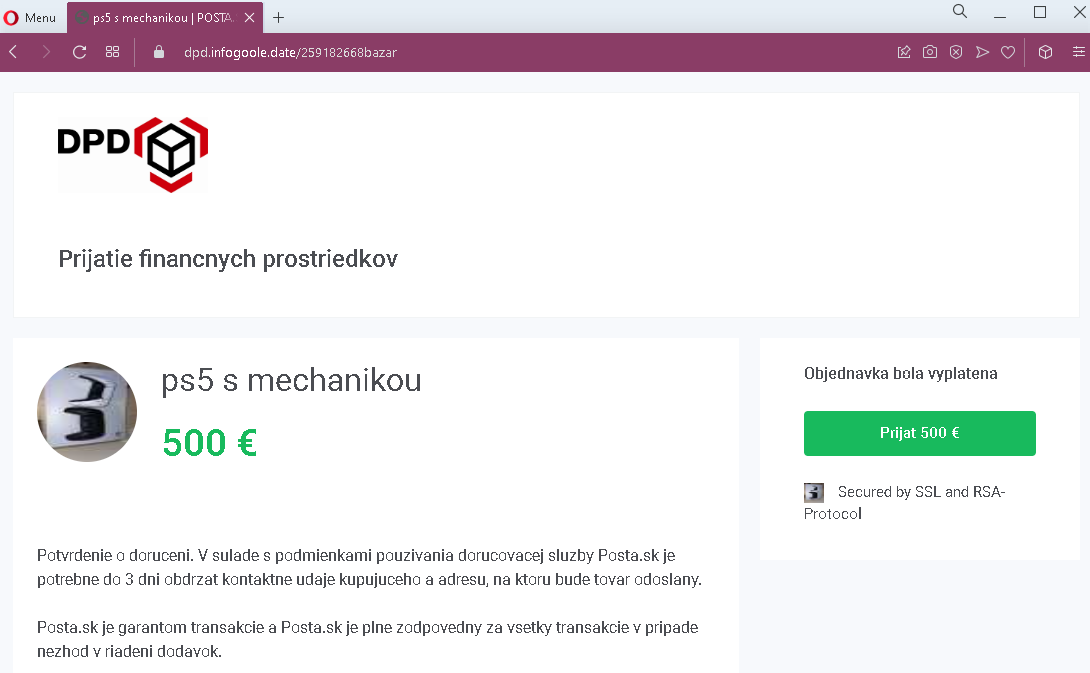
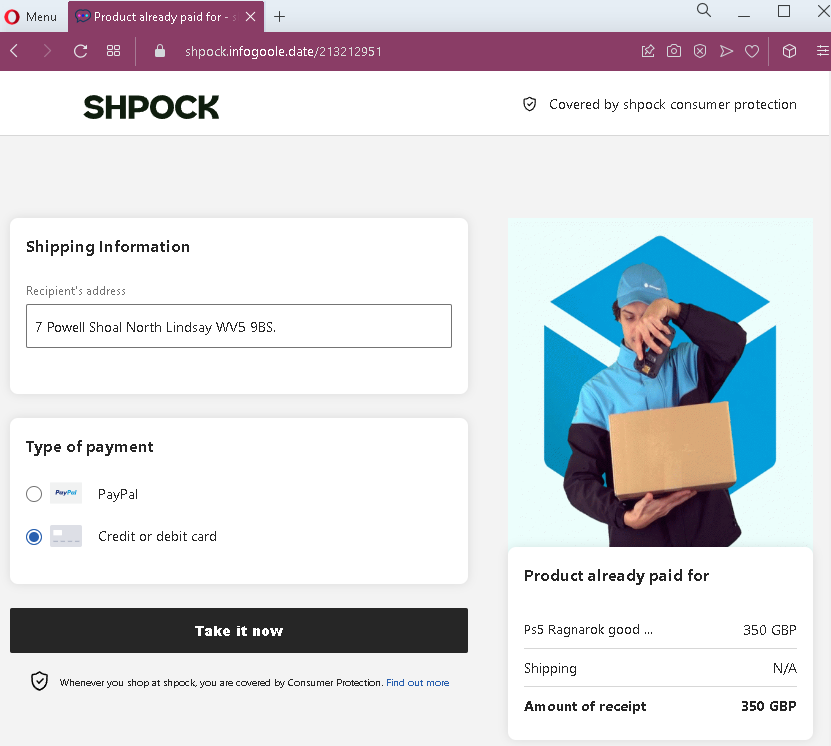
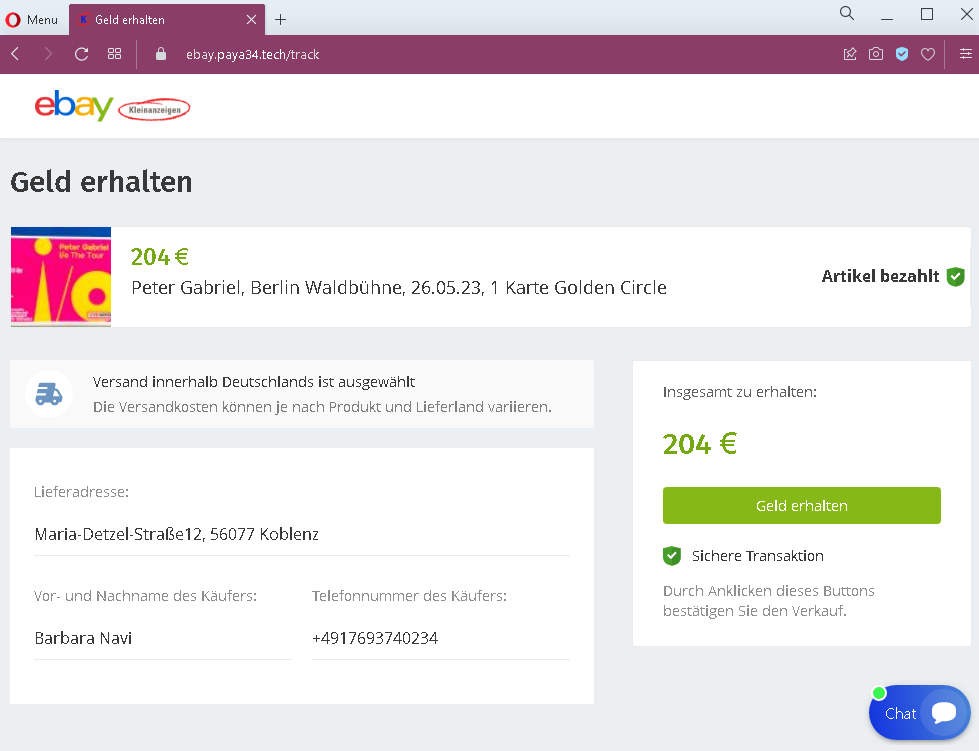
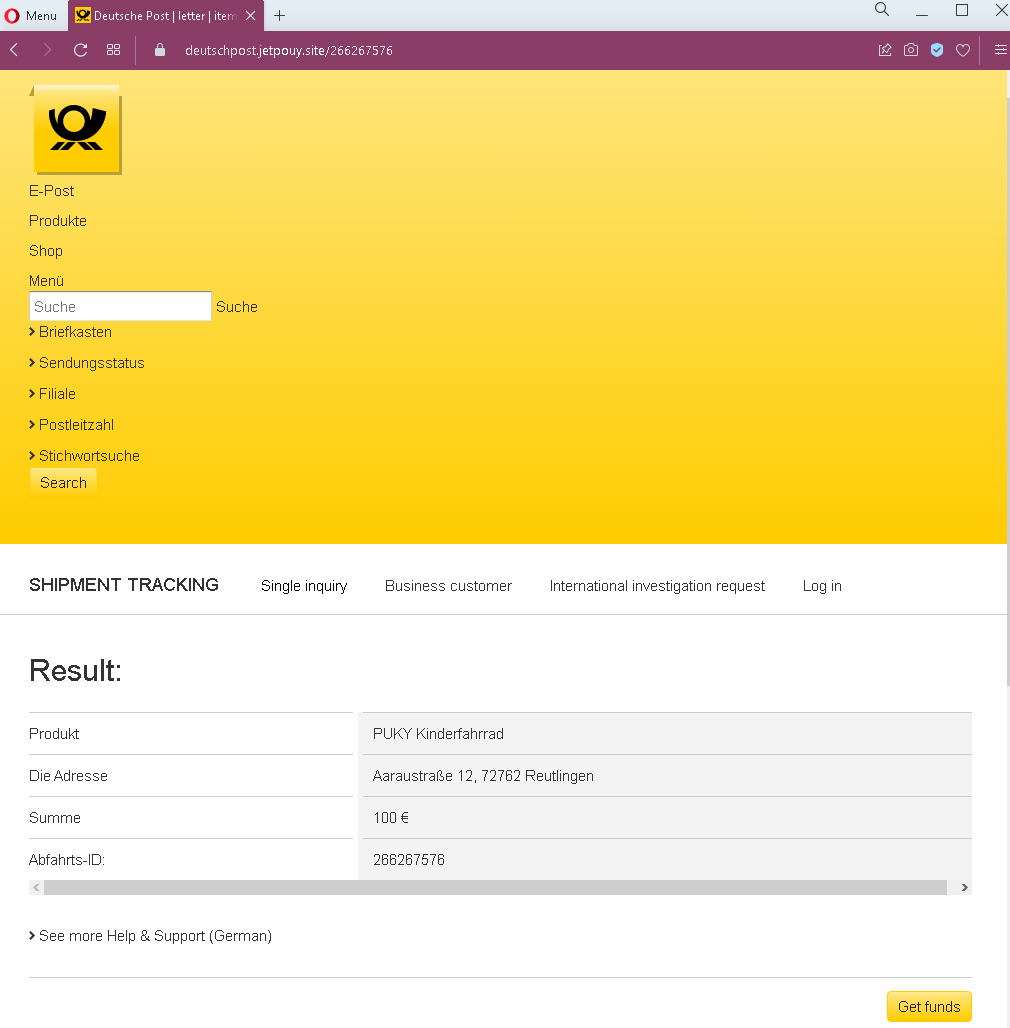
The Fake Payment Confirmation Page
This single page displays:
- A prominent payment receipt heading
- An item description (in this case, a boiler model) with a price in GBP (£395)
- Fabricated buyer details, including a name and a shipping address
- A message stating that the buyer has already paid and that the seller should ship the item or await a courier after “receiving funds”
- Instructions implying that the seller must take action to claim the payment
- A prominent button designed to initiate the “receipt” of funds
- A fake chat support window that appears to show a pre-written message claiming to be from Gumtree support, explaining that the buyer paid through Gumtree and that the seller can get full payment immediately
The goal:
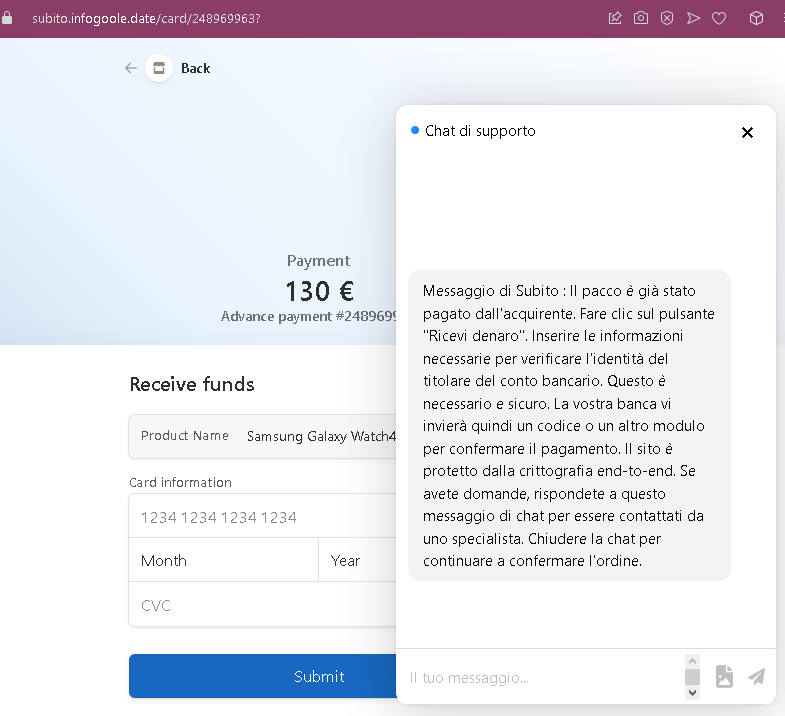
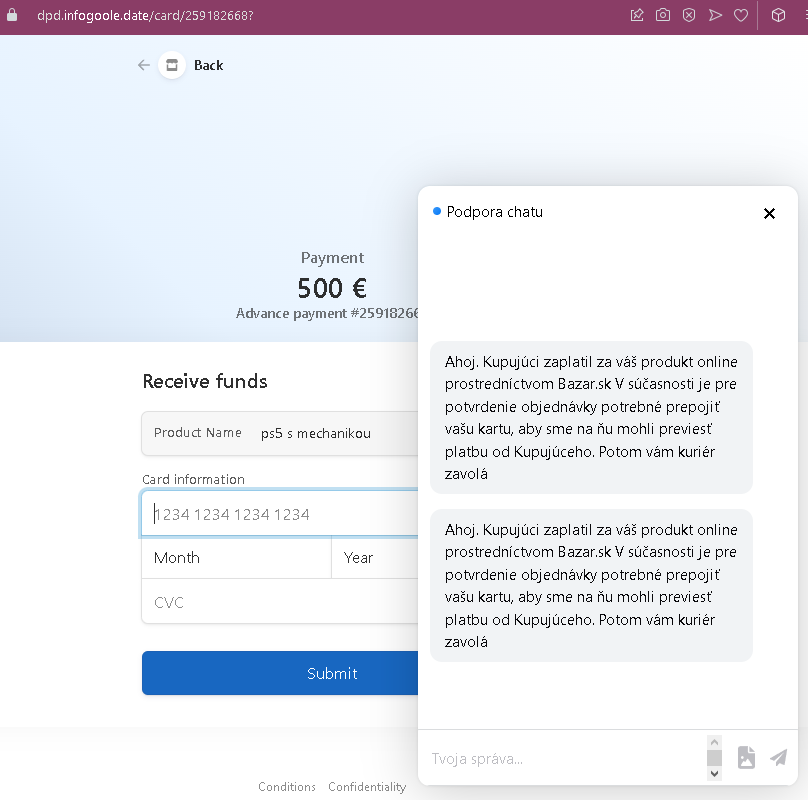
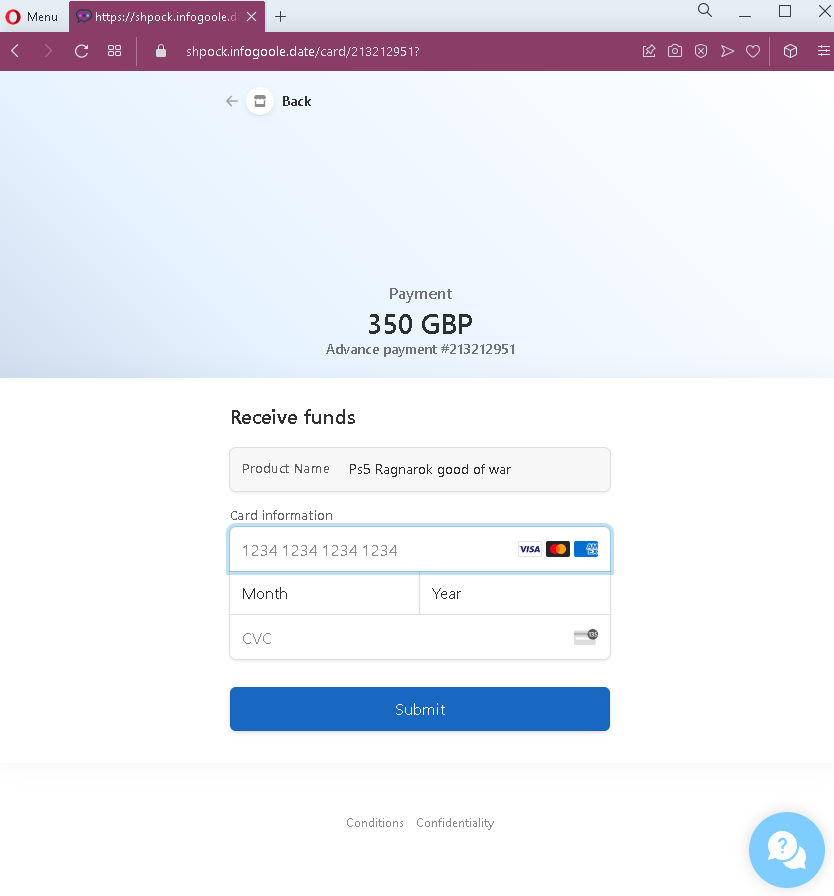
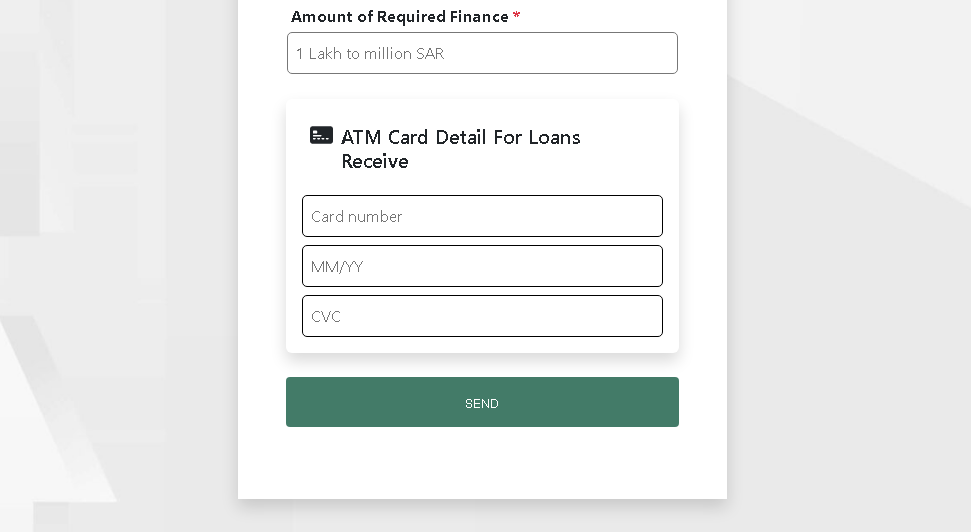
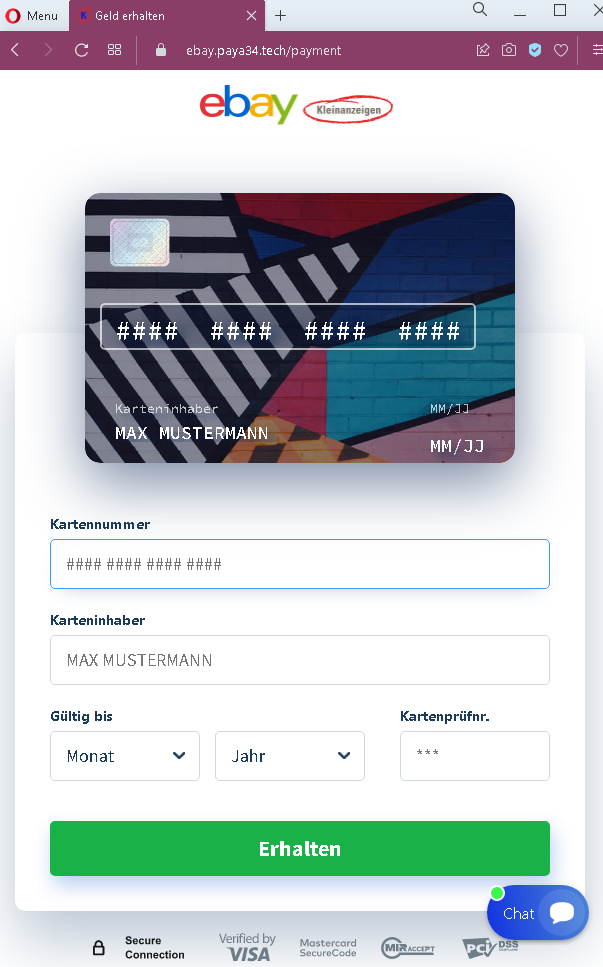
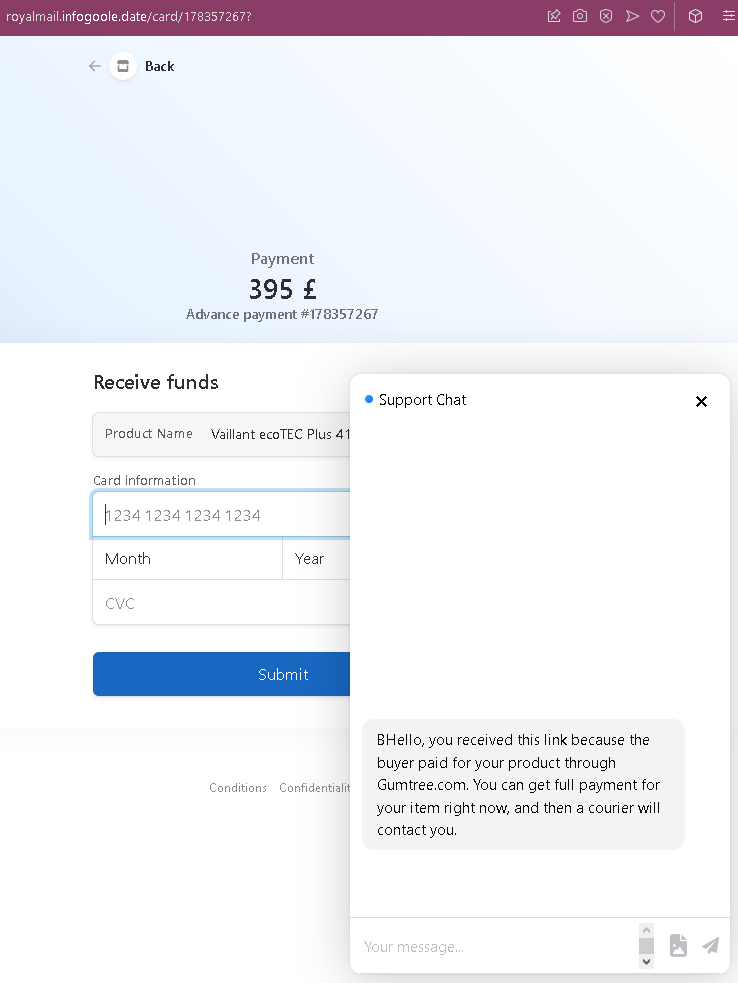
The attacker intends to steal the seller’s credit card details. While this screenshot does not show the card entry form, the pattern from similar scams indicates that clicking the “receive” button leads to a second page requesting full credit card number, expiry date, and CVC. There is no actual payment—the buyer, the order, and the support chat are all fabricated.
Red flags to watch for (without quoting specific text):
- Illogical request flow: The page asks the seller to “receive” money but does so by directing them to a button that leads to a card entry form. In legitimate transactions, sellers receive money directly to their bank account or PayPal—they never need to enter card details to claim payment.
- Fake chat support: The embedded chat window is not a live support feature but a scripted message designed to reassure the victim. Legitimate Gumtree transactions do not include a live chat pop-up that explains payment processes on third-party pages.
- Suspicious URL: The page is hosted on a domain that is not
gumtree.com. Always check the address bar before entering any information. - Vague buyer address: The shipping address appears nonsensical (“Pearland_45562 Garret Locks”)—a tactic to make the listing seem specific without using real identifiable information.
- No account login required: A legitimate sale on Gumtree would appear in the seller’s account dashboard after logging in. This page bypasses account authentication entirely and asks for sensitive information directly.
- Pressure to ship: The page instructs the seller to ship the item after “receiving funds” and within a specific timeframe, creating urgency to bypass critical thinking.
- Mixed branding: While the page references Gumtree in the fake chat, the overall design lacks official Gumtree branding consistency and security indicators.
What to do if you encounter this:
- Do not click the button to “receive” funds or proceed to any next step.
- Do not enter any credit card details, even if a subsequent page asks for them.
- If you are selling on Gumtree, always log into your account directly (by typing
gumtree.cominto your browser) to check for real sales and messages. Legitimate transactions appear in your account inbox and dashboard. - Never trust links sent by buyers claiming they have paid—especially if they direct you to an external page.
- If you have already entered your credit card details, contact your bank immediately to block the card and dispute any unauthorized charges.
- Report the phishing page to Gumtree’s support team.
Why this scam is effective:
Gumtree is one of the UK’s most popular platforms for selling second-hand goods, especially household items like appliances. Sellers are often eager to complete a sale and may click a link in a message without suspicion. The fake chat support window is a particularly convincing touch—it mimics the “live chat” features common on e-commerce sites and provides a seemingly helpful explanation for why the seller needs to “claim” the payment. The £395 price point is realistic for a boiler, making the scam plausible.
Protective measures:
- Always verify any sale by logging directly into your Gumtree account—never through a link sent in a message.
- Never enter credit card details to receive payment. Sellers provide payout details (bank account) during account setup; payments are processed automatically.
- Be suspicious of any page that includes a pop-up chat window claiming to explain a payment process—legitimate platforms do not use such tactics on external pages.
- If a buyer sends you a link to “claim” payment, treat it as a red flag and verify directly through the platform’s official app or website.
- Enable two-factor authentication (2FA) on your email and any linked payment accounts.