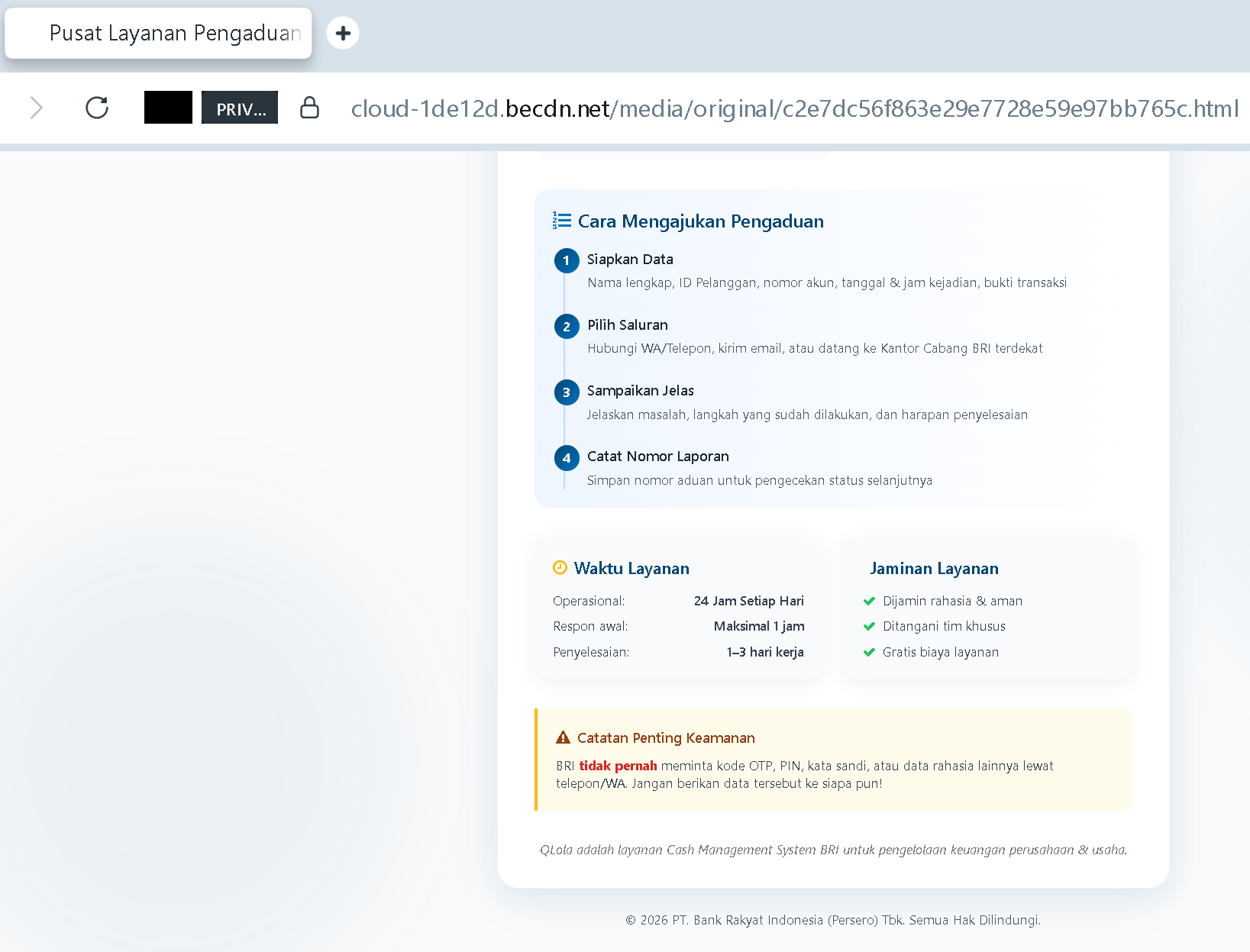
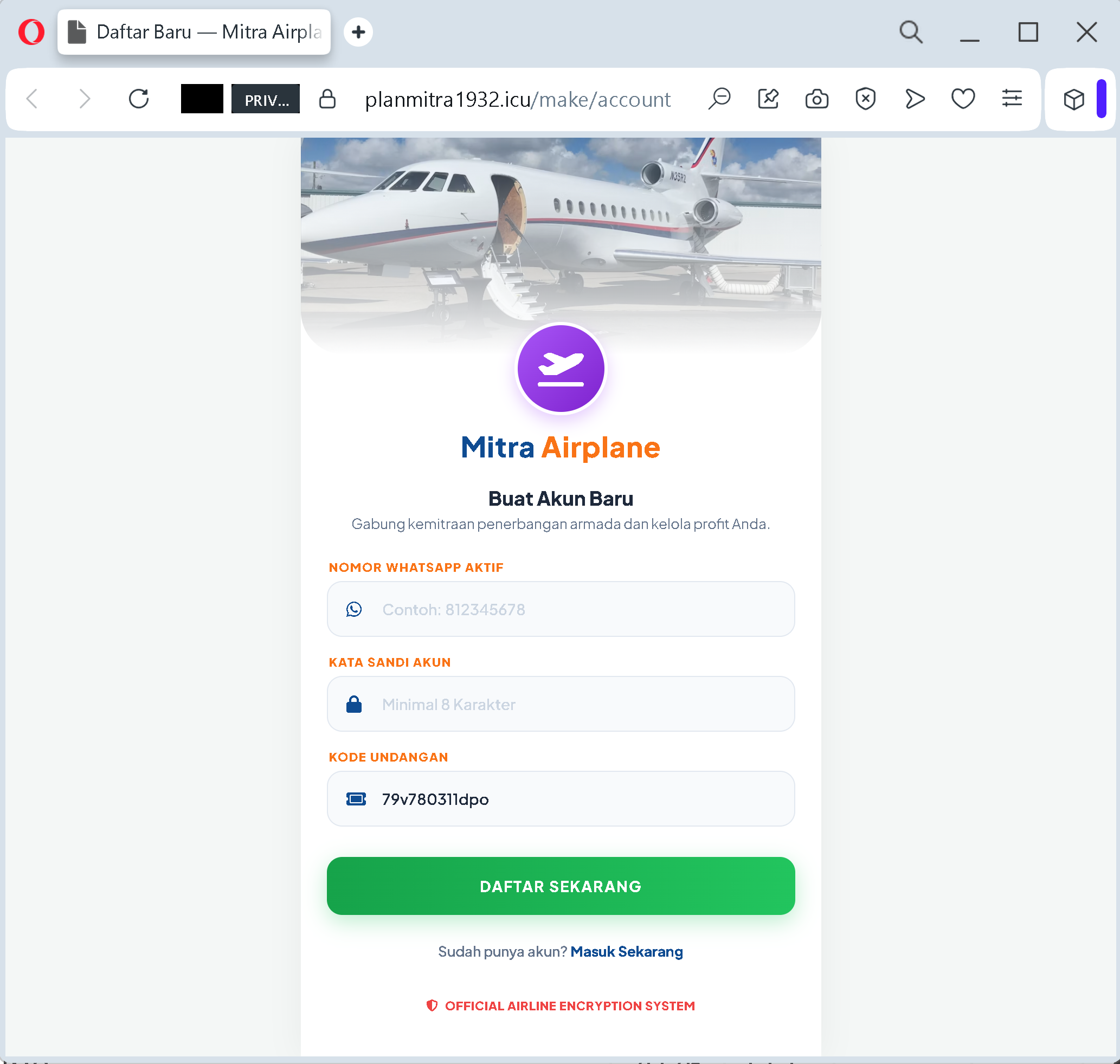
The headline on the screen promised a way out of the daily grind. “Gabung kemitraan penerbangan armada dan kelola profit Anda” – join an aviation fleet partnership and manage your profit. A sleek form asked for a WhatsApp number, a password, and an invitation code that was already filled in for you. At the bottom, in bold letters, the page declared itself an “OFFICIAL AIRLINE ENCRYPTION SYSTEM”.
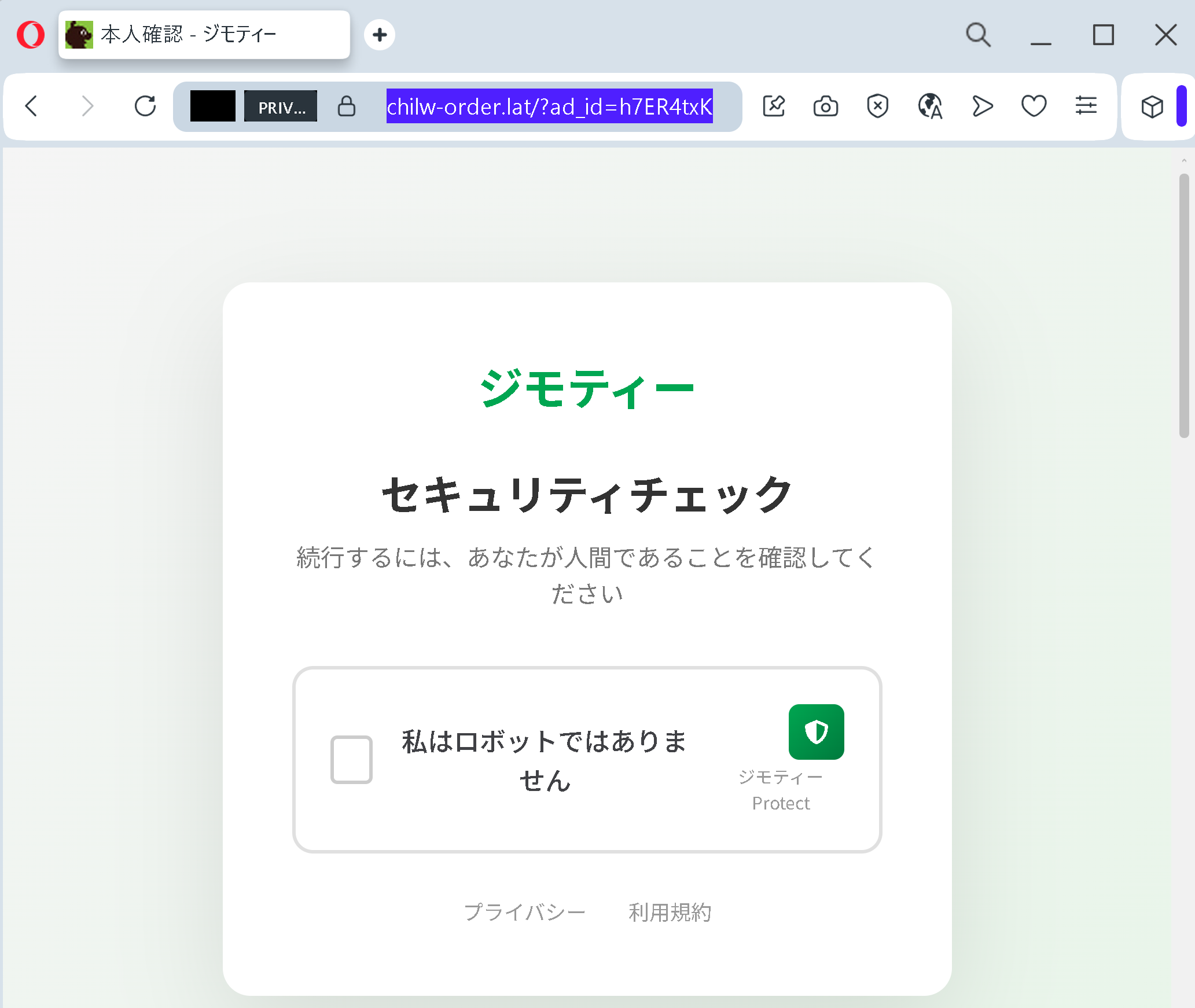
Incident Report: This malicious interface was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our automated link scanning workflows. To protect the public, the phishing source domain has been fully defanged within our infrastructure. We document and analyze these live visual patterns to help security researchers and users recognize deceptive clone designs before financial damage occurs.
If you have seen anything like this – a slick website, a promise of passive income from aircraft leases, and a “special” invitation code – you are looking at the exact moment a criminal hopes to catch you. The platform behind that page is not an airline. It is not a legitimate investment. It is a trap. And the only “encryption” happening is the money disappearing from your wallet.
This guide is written for everyone in Indonesia who has ever seen a WhatsApp message about “investasi bodong”, a Facebook ad promising huge returns from “aviation partnerships”, or a link to a professional‑looking investment portal. You are not a cybersecurity expert. You are someone who wants a better life for your family, and that makes you a target. Criminals know that hope, when combined with urgency and a fake “invitation”, is the most powerful weapon they have.
By the end of this guide, you will understand exactly how the “Mitra Airplane” scam works, why it is part of a much larger criminal wave sweeping across Indonesia, and – most importantly – the simple, unforgettable rules that will keep your money in your pocket and your future in your own hands.
The Anatomy of the Trap: How “Mitra Airplane” Really Works
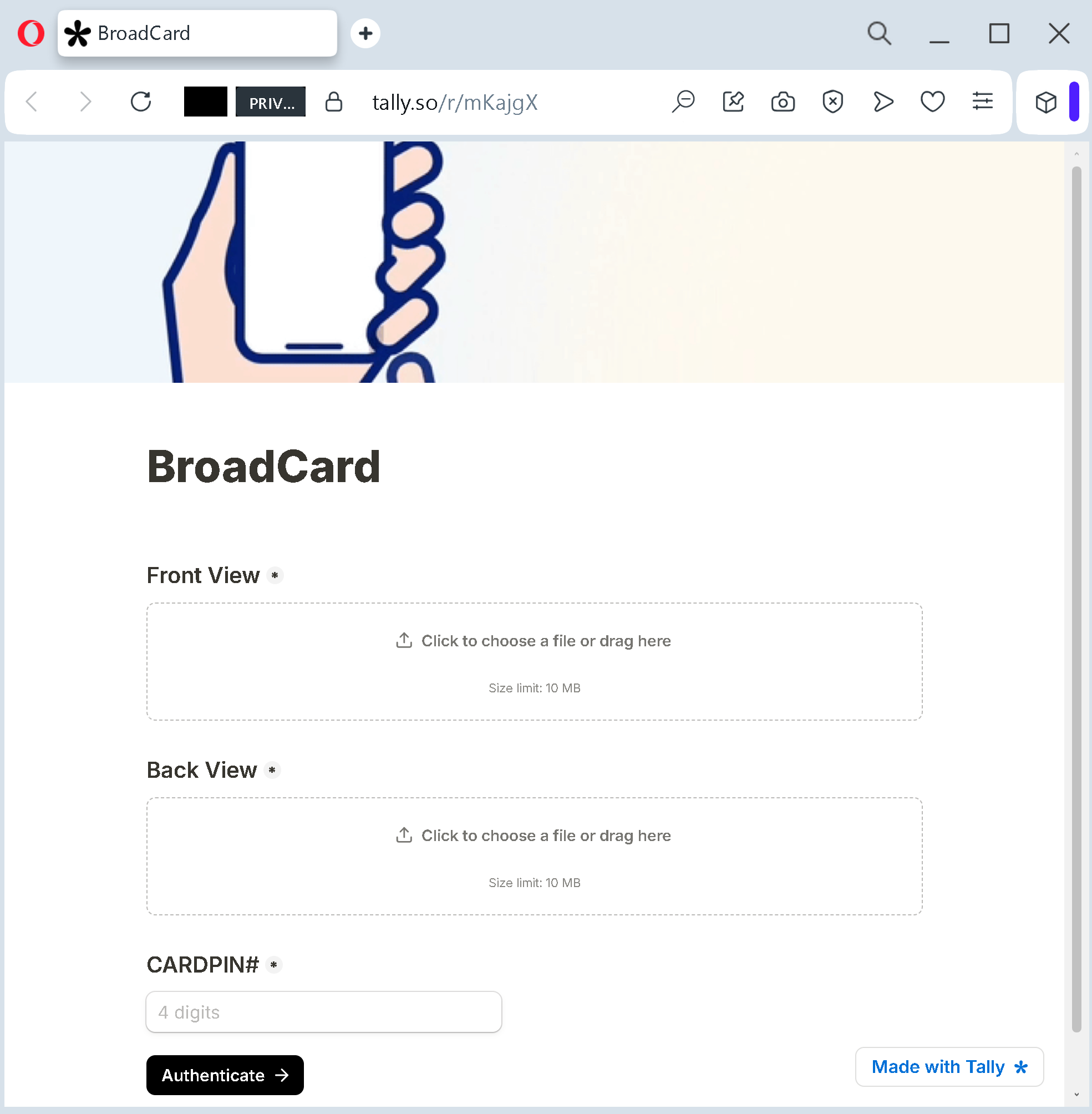
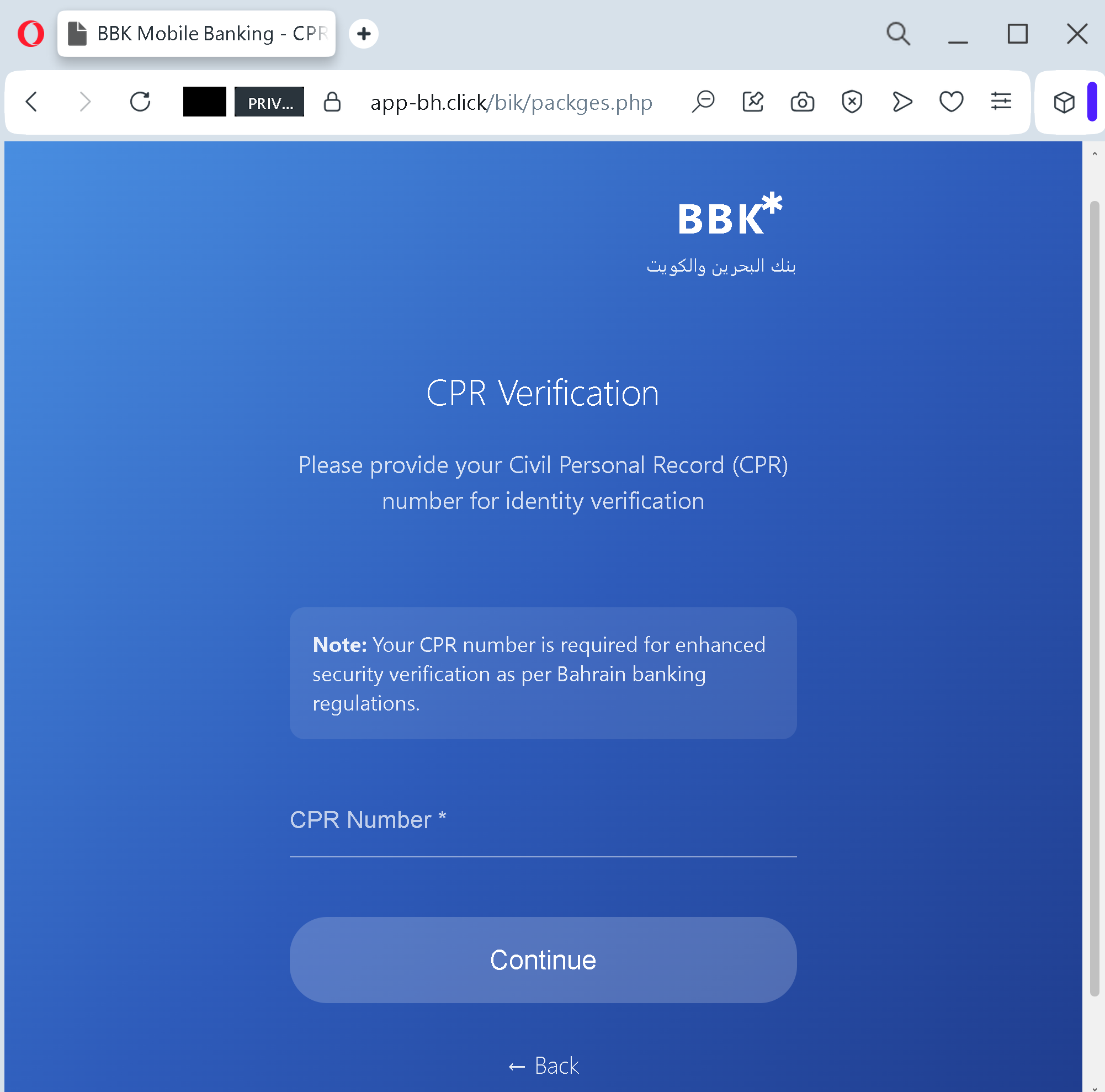
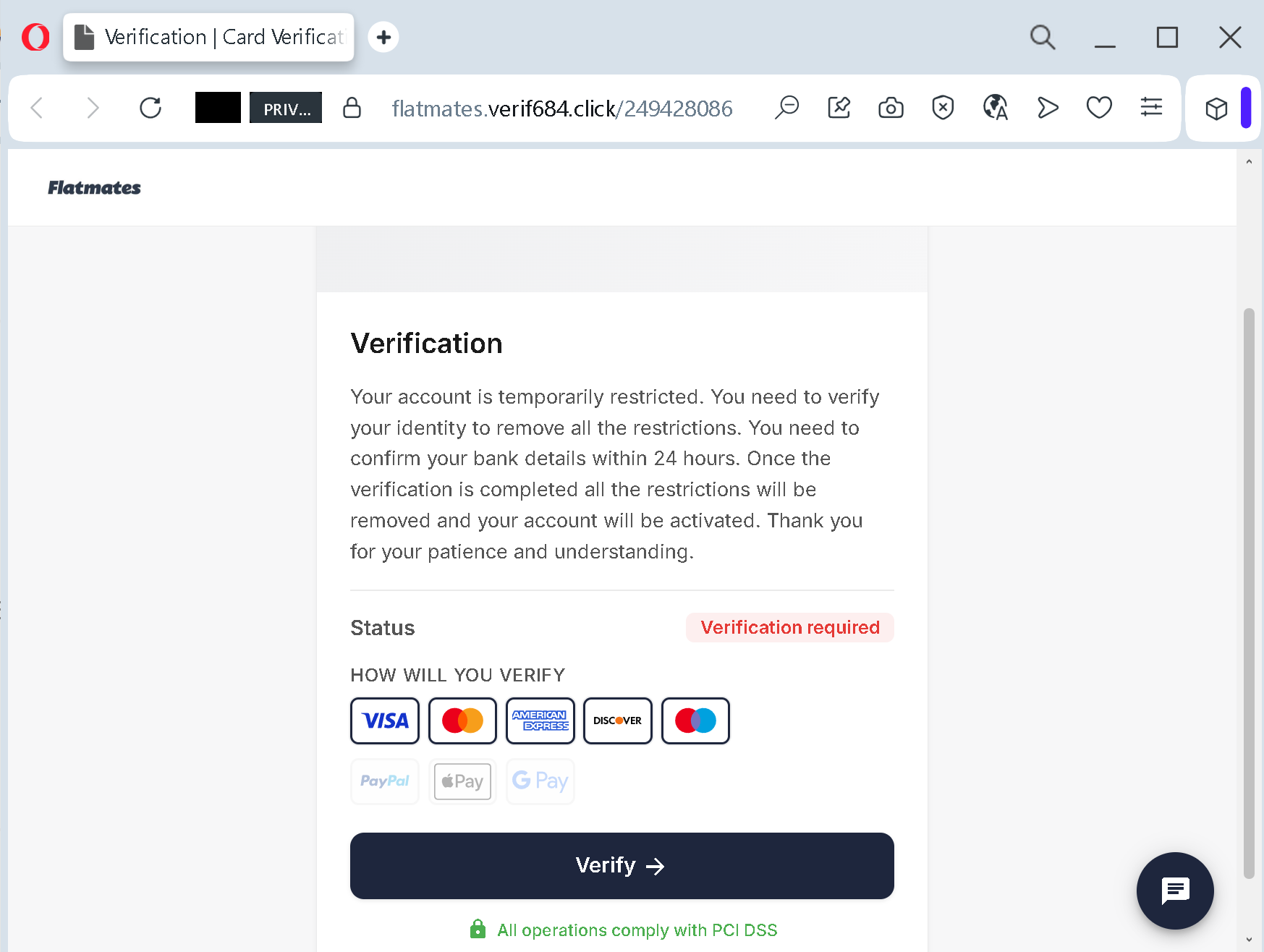
The screenshot shows a registration page that is deceptively simple. It asks for three things: your WhatsApp number, a password, and an invitation code. That is all. But behind that minimal interface lies a fully engineered criminal operation.
The Fake Aviation Legend
The text on the page reads: “Buat Akun Baru / Gabung kemitraan penerbangan armada dan kelola profit Anda” – Create a new account / join an aviation fleet partnership and manage your profit. This is the bait. The criminals know that Indonesians understand the value of travel and logistics. Aviation sounds prestigious, global, and profitable. By wrapping their scam in the language of “airline encryption” and “fleet management”, they borrow credibility they have never earned.
No legitimate airline or aviation investment platform will ever ask you to invest through a simple web form with no background checks, no legal disclosures, and no registration number. Real aircraft leasing or fleet partnerships involve contracts, lawyers, and regulators – not a WhatsApp number and a password.
The WhatsApp Trap
The first field on the form asks for your “NOMOR WHATSAPP AKTIF”. In Indonesia, your WhatsApp number is not just a communication tool. It is often linked directly to your digital wallet balances in GoPay, OVO, DANA, and other popular services. When you hand over your active WhatsApp number to a criminal, you are giving them a direct line to your payment ecosystems.
Once you register, the scammers will contact you via WhatsApp. You will be assigned a personal “account manager”. You will be shown fake screenshots of other members withdrawing daily profits. You will be shown a dashboard where your “aircraft share” grows by 2‑3% every day. The pressure will be friendly at first, then urgent. “Limited prize-drawing features available.” “Special promotion ends tonight.” “Your fleet needs one more payment to activate full returns.”
This is not aviation management. This is a pig butchering operation – a long‑term psychological manipulation designed to drain every rupiah you own. In a similar case recently uncovered in Solo Raya, Indonesian police arrested an entire pig butchering syndicate that had used the exact same methods: building emotional relationships over WhatsApp, then guiding victims to fake crypto and investment platforms.
The Invitation Code That Is Not a Secret
The form includes a field labelled “KODE UNDANGAN” – invitation code – which is already filled in: 79v780311dpo
The Fake Security Badge
At the bottom of the page, in prominent letters, the text reads “OFFICIAL AIRLINE ENCRYPTION SYSTEM”. This is a complete fabrication. Real airlines and financial platforms do not need to announce that they use encryption. Encryption is a technical standard, not a marketing badge. The criminals put this text on the page for one reason only: to make you feel safe. They want you to think, “If they have an encryption system, my money must be protected.” In reality, the only thing being encrypted is the communication between your browser and the scammer’s server. Your money, once transferred, is completely unprotected.
The Profit That Never Comes
After you register, the scam continues. You will be encouraged to make an initial “investment” – often a relatively small amount, perhaps Rp 500,000, to buy a “virtual aircraft wing”. Your dashboard will show a profit growing every day. You will be allowed to withdraw small amounts to build your trust. This is the critical phase. When you successfully withdraw Rp 50,000 or Rp 100,000, your belief in the platform solidifies. You think, “This is real. Other people are getting money.”
What you do not see is that those small payouts come from the deposits of other victims. The criminals are using a classic Ponzi scheme: paying early investors with the money of later investors. As long as new victims keep signing up, the platform appears to work. But the moment you try to withdraw a large sum – or the moment the criminals have collected as much money as they think they can – the website will disappear. Your account will be blocked. Your WhatsApp number will be ignored. And your money will be gone.
Real Stories of Heartbreak and Narrow Escape
The Banyumas Pensioner Who Lost Her Retirement Savings
A retired teacher in Banyumas, Central Java, thought she had found a way to pay for her grandchildren’s school fees. She joined an investment scheme that promised extraordinary returns. Her pension was modest, but the promise of quick profit was too tempting. She invested her savings. Then more. Then she borrowed from friends, thinking the returns would cover everything. Instead, she found herself trapped in a cycle of debt.
She later told investigators: “Dari sanalah ia sadar telah masuk dalam perangkap investasi bodong.” – “That was when she realised she had fallen into a fake investment trap.” By the time the fraud was uncovered, she had lost hundreds of millions of rupiah. Her retirement, planned over decades, was gone in months.
The Solo Syndicate That Stole Rp 41 Billion in Ten Months
Between July 2025 and May 2026, an international pig butchering syndicate operated out of Sukoharjo, Central Java. They targeted victims primarily in the United States, building fake romantic relationships over WhatsApp and then guiding their victims to fake crypto trading platforms. Over ten months, the syndicate recorded profits of Rp 41.1 billion (approximately US$2.2 million). More than 133 victims were confirmed, and investigators believe the true number is higher.
When Indonesian police finally raided the operation, they found an entire infrastructure dedicated to deception: fake trading interfaces, fabricated withdrawal proofs, and teams of people whose only job was to keep victims emotionally engaged and financially draining.
The “Mitra Airplane” scam works exactly the same way, except the fake crypto platform has been replaced with a fake aviation partnership. The technology is different; the psychology is identical.
The Woman Who Realised Just Before the Transfer
A woman in East Java was invited to an “aviation investment” group on WhatsApp. The admins posted daily screenshots of members withdrawing profits. She was impressed. She was ready to transfer Rp 90 million – her family’s savings – into the platform. But something stopped her. The account name for the transfer was not a corporate bank account. It was a personal account belonging to an individual she had never met.
She asked the group admin why the payment was going to a personal account. The admin gave a vague answer about “processing fees”. She asked again. The admin blocked her. Hours later, the entire WhatsApp group disappeared. She had come within one click of losing her life savings. Her only mistake was asking a question. Her only defence was not trusting the silence that followed.
The Tarakan Resident Who Saw Through the Facebook Lie
A man in Tarakan, North Kalimantan, received a Facebook message from an attractive profile. The conversation moved to WhatsApp. Within days, the “new friend” was offering an exclusive investment opportunity. The returns were 10‑20% per month – numbers that no legitimate financial instrument can deliver. The man remembered a government public service announcement: “Jangan tergiur tawaran imbal hasil tinggi dalam waktu cepat” – “Do not be tempted by offers of high returns in a short time”. He blocked the contact and reported the profile. He lost nothing except a few hours of his time.
These stories share a common thread. The people who lost money all ignored the same red flags. The people who kept their money all paused, asked a question, or remembered a simple warning.
The Four Red Flags That Give Away the Aviation Investment Scam – Every Time
You do not need to be a financial expert to spot these traps. You just need to know what to look for.
Red Flag One: The Promise of “Easy Profit” from an Industry You Do Not Understand
Real aviation leasing is a complex, capital‑intensive business. It requires licences, insurance, maintenance contracts, and regulatory approvals. No legitimate company offers “partnerships” to random individuals through a web form. If the business model is not explained in plain, verifiable terms, the investment is a scam.
Red Flag Two: The Invitation Code That Comes from a Stranger
If someone you do not know personally sends you an invitation code for an investment platform, that person is almost certainly earning a commission from every rupiah you deposit. The code is not a secret pass to wealth. It is a tracking number for your future losses.
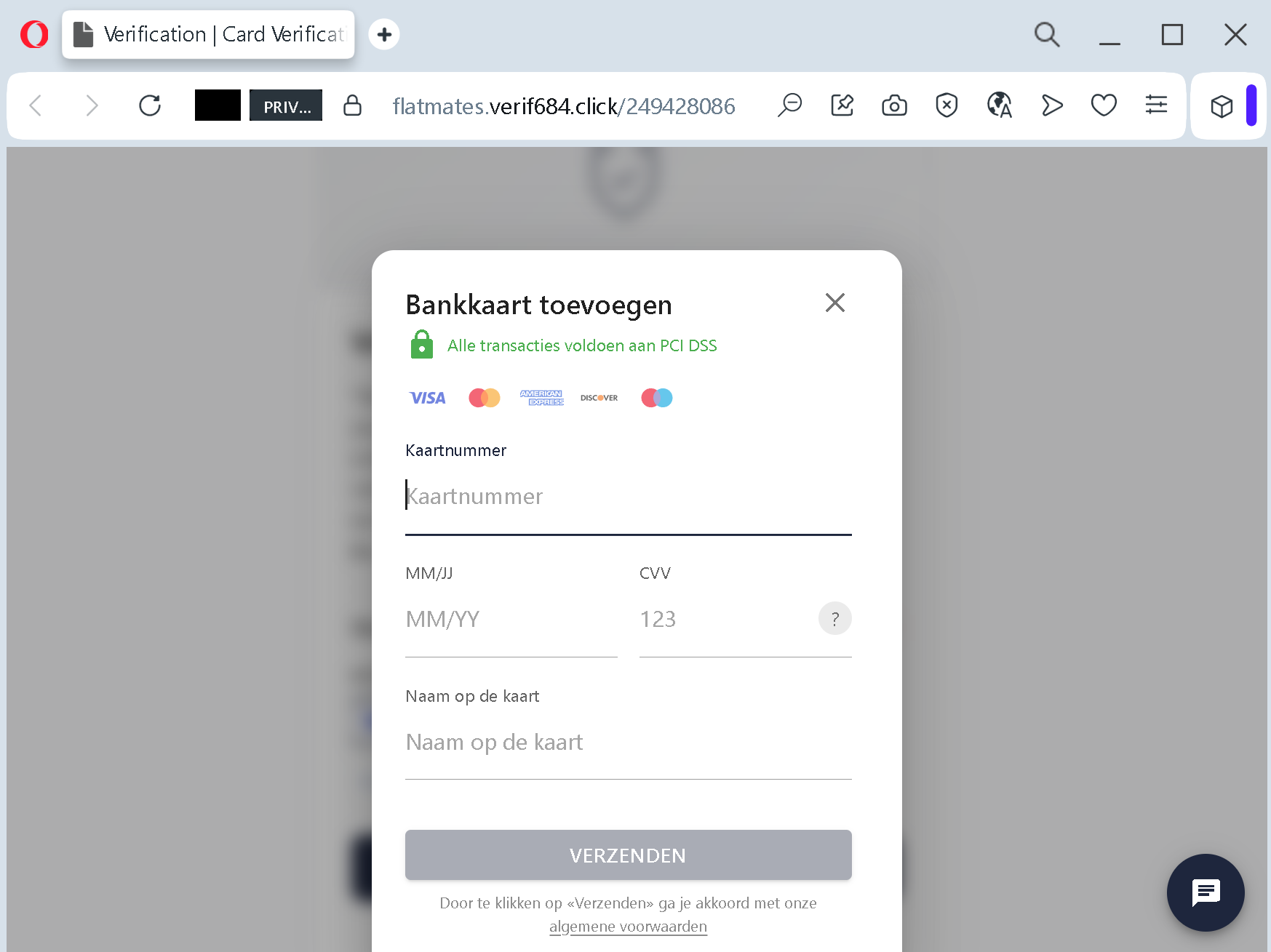
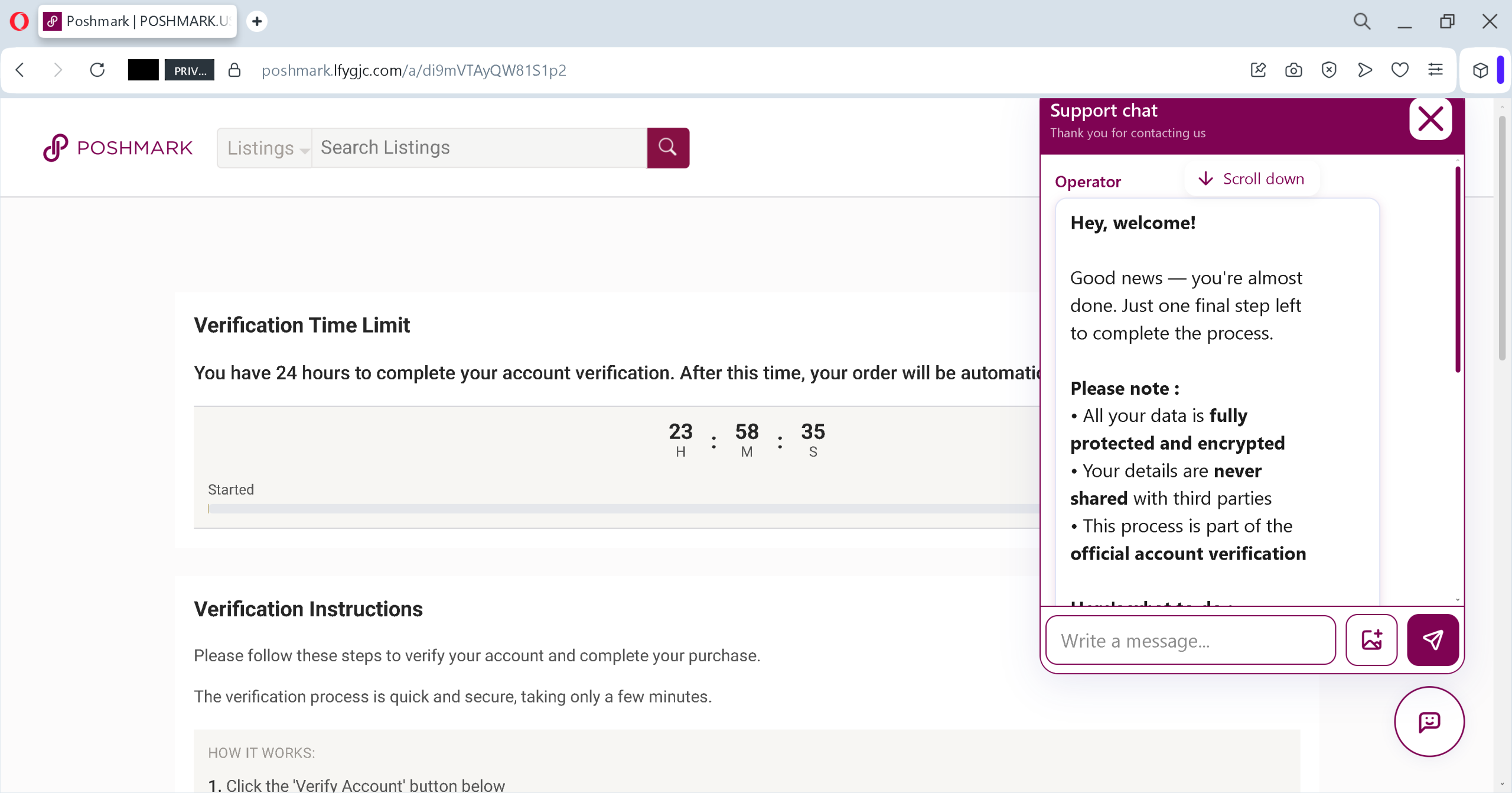
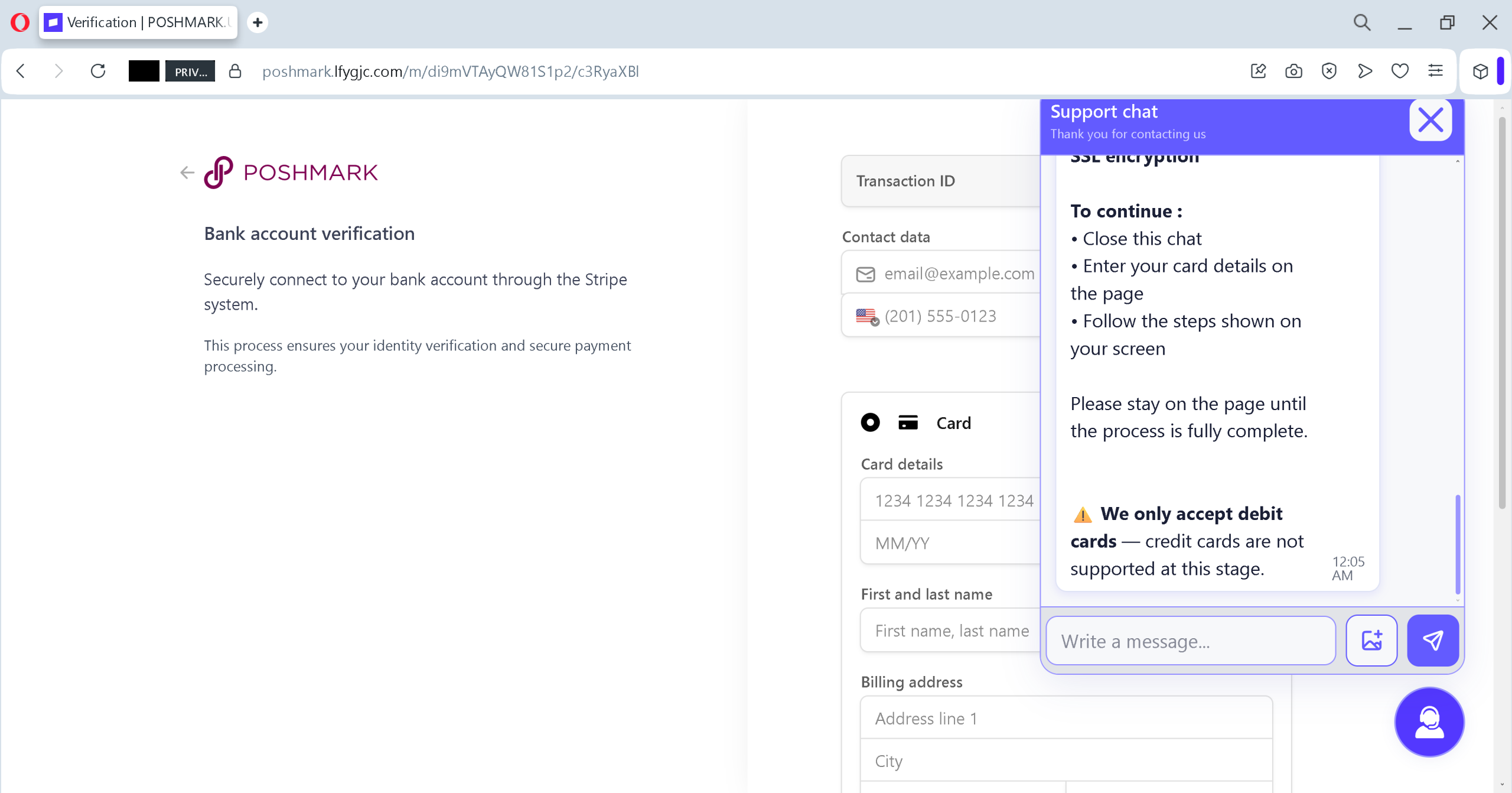
Red Flag Three: The Payment Goes to a Personal Bank Account
No legitimate investment platform will ask you to transfer money to an individual’s personal bank account. Real companies use corporate accounts held in the company’s registered name. Before you send any money, check the account name. If it is a personal name – Pak Budi, Ibu Siti, or any individual you do not know – you are sending money to a scammer. Period.
Red Flag Four: The Platform Is Not Registered with OJK
Otoritas Jasa Keuangan (OJK) is the Indonesian government agency that regulates financial services. Every legitimate investment platform must be registered with OJK and display its registration number. The “Mitra Airplane” page has no registration number. It has no legal disclosures. It has nothing except a form and a fake security badge.
OJK has repeatedly warned the public: before you invest, check the legal status of the platform through OJK’s official website. In 2025 alone, OJK received 4,971 reports of illegal investment activities. Between 2017 and mid‑2025, the government’s “Satgas Pasti” task force identified 1,811 illegal investment entities. Those are not statistics. Those are traps that real people fell into.
The Expert Playbook: Three Rules to Keep Your Money Safe
The following rules are not optional. They are the difference between building your future and losing everything you have worked for.
Rule One: Never, Ever Invest Through a WhatsApp Link
If an investment opportunity arrives through WhatsApp, Telegram, or any messaging app – especially from someone you have never met in person – treat it as 100% fraudulent. Legitimate financial companies do not recruit customers through unsolicited WhatsApp messages. The moment a stranger sends you an investment link, you are the product, not the partner.
Rule Two: Check the Company’s Legal Status Before You Send One Rupiah
Open your browser. Type www.ojk.go.id
Rule Three: If It Sounds Too Good to Be True, It Is a Trap
Every fake investment platform promises extraordinary returns with “no risk”. Real investments carry real risks. No airline, no crypto exchange, no magical WhatsApp group can deliver 10‑20% monthly returns without unlicensed promotional your principal. The moment you hear a number that sounds too high, your only correct response is to close the page and walk away.
What to Do If You Have Already Fallen for This Scam
If you have already registered on a platform like “Mitra Airplane” or transferred money to a suspicious account, do not panic. But do not wait, either. Time is the enemy.
First, stop all further payments immediately. Do not send another rupiah, no matter what promises the “account manager” makes. Every additional payment will be lost just like the first.
Second, contact your bank immediately. Use the official customer service number on your debit card or your banking app. Tell them that you may have sent money to a fraudulent investment account. Ask them to freeze your account and to attempt to reverse the transfer. Act quickly – reversals are more likely within 24 hours.
Third, change your password immediately. If you used the same password on the fake platform that you use for your email, social media, or other financial accounts, change those passwords now. The criminals may try the stolen credentials on other services.
Fourth, report the scam to the authorities. File a report with the Indonesian National Police through their online complaint portal. Report the platform to OJK through their consumer protection hotline 157. Report the WhatsApp number to the Ministry of Communication and Digital Affairs. Your report could help shut down the platform and protect other victims.
Fifth, save every piece of evidence. Take screenshots of the registration page, the WhatsApp conversation, the transfer receipts, and any dashboard screens. These will be essential for police investigations and bank disputes.
A Final Word
The “Mitra Airplane” registration page is not an aviation partnership. It is not a legitimate investment. It is a digital trap, laid in plain sight, designed to deceptive tactic your hope for a better life. The criminals behind it do not own any planes. They do not have any fleet. What they have is a professional‑looking website, a fake encryption badge, and a network of recruiters earning commissions from every rupiah you lose.
But the scam has a fatal weakness. It relies entirely on you not knowing the rules. You now know the rules. Never trust an investment link sent by a stranger. Never send money to a personal bank account. Never believe promises of quick, risk‑free profit. Always check the registration status with OJK. Always trust your suspicion over their reassurance.
Share this guide with your family, your neighbours, and your friends. Post it in your WhatsApp groups. The more people understand how this scam operates, the harder it becomes for criminals to profit. Your future is worth more than a fake dashboard of fake profits. Do not let a stranger take it away from you.
This fraudulent platform was identified and analysed as part of standard cyber threat monitoring.