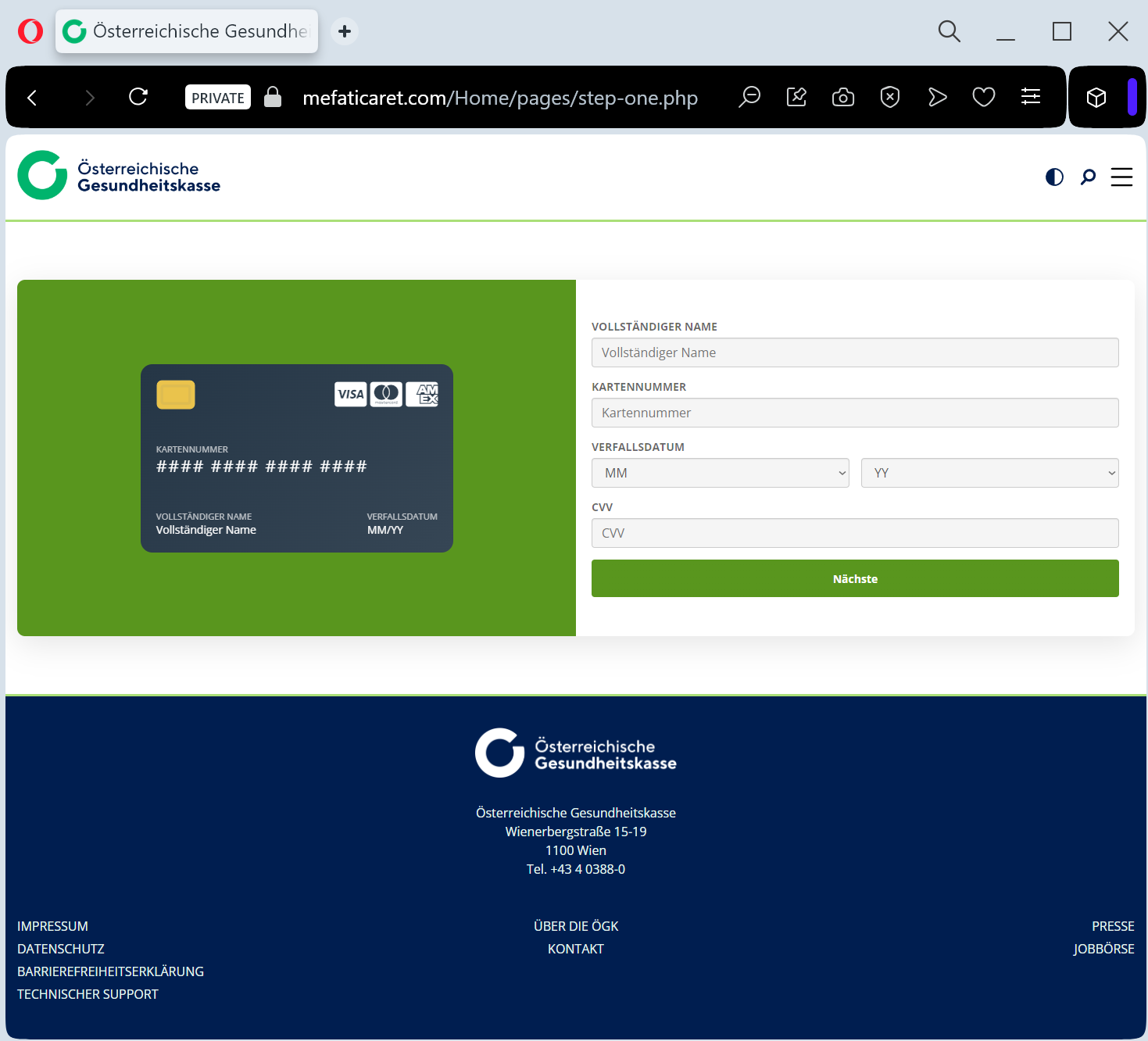
A phishing campaign impersonating the Austrian Health Insurance Fund (ÖGK) is targeting residents via SMS and email with fraudulent refund claims to steal personal information and banking credentials. The attack leads to a cloned portal designed to capture identity data, credit card details, and bank login information.
Austrian Health Insurance Fund (ÖGK) “Tax/Health Refund” Scam
Target: Residents of Austria and ÖGK (Österreichische Gesundheitskasse) members
Threat Level: High (Credit Card Skimming & Identity Theft)
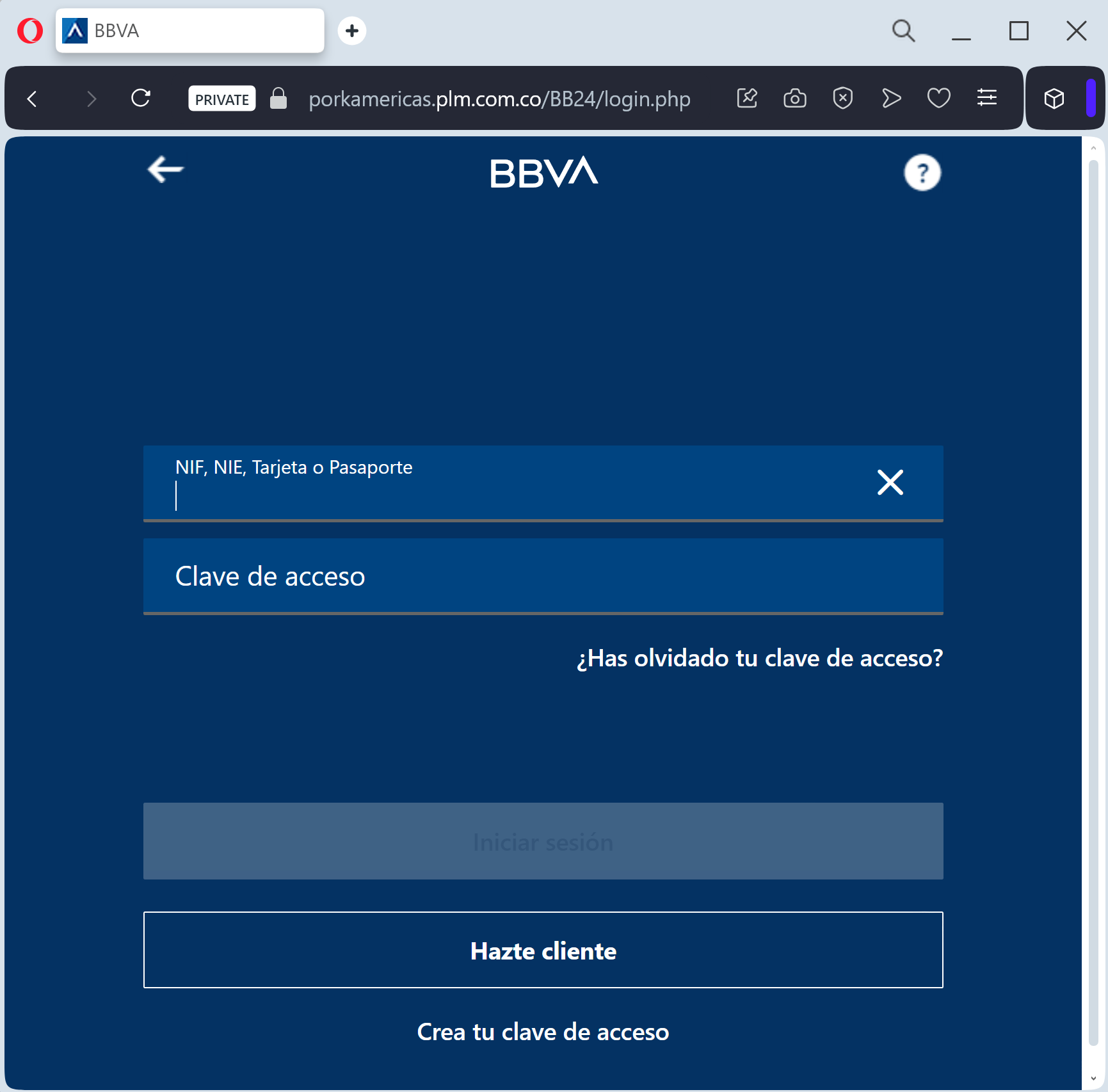
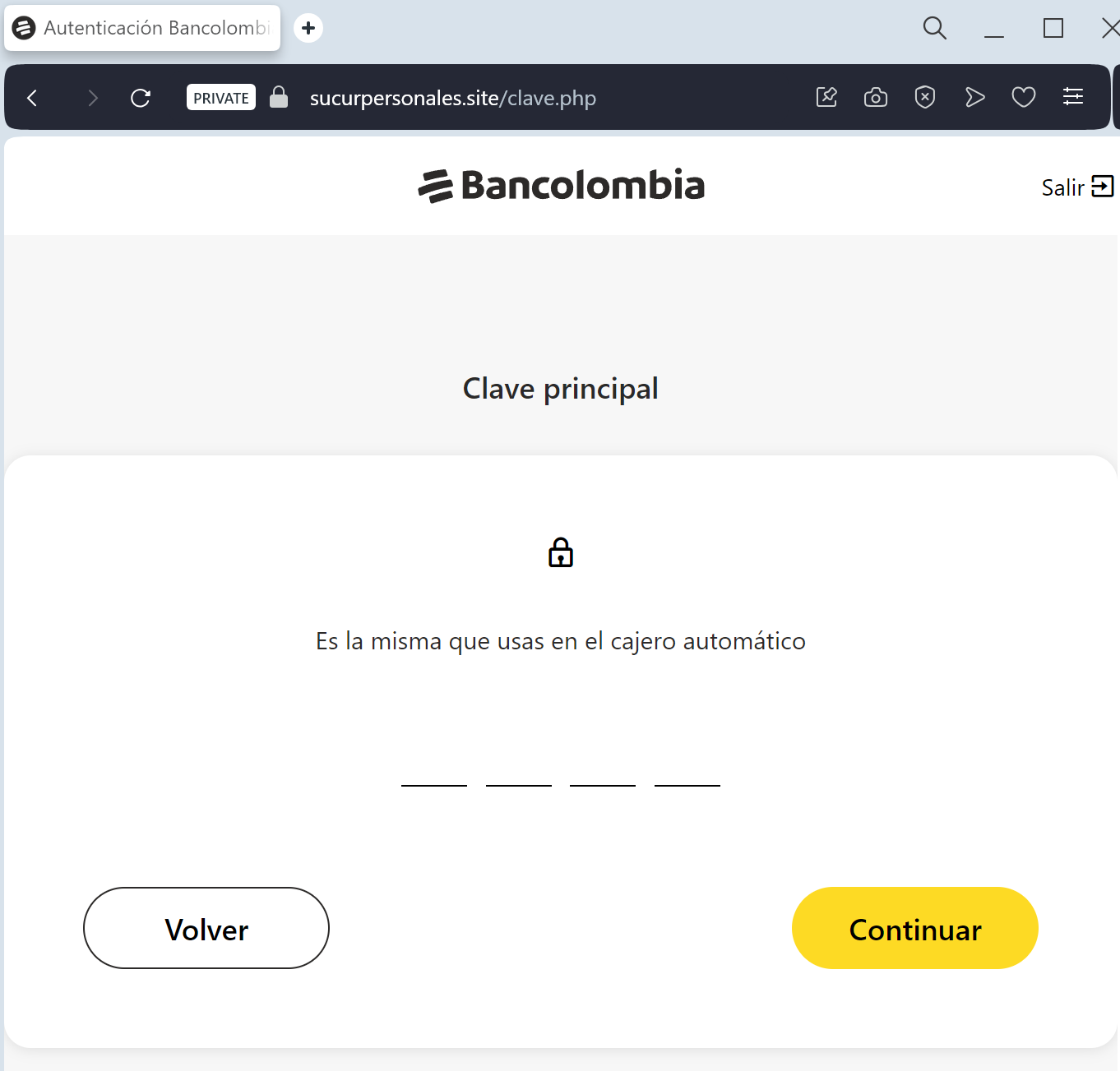
Phishing Method Description
This attack uses Public Institution Impersonation. Victims receive an SMS (Smishing) or Email claiming they are entitled to a “Rückerstattung” (Refund) or a “Health Tax Credit” from the Austrian Health Insurance Fund (ÖGK).
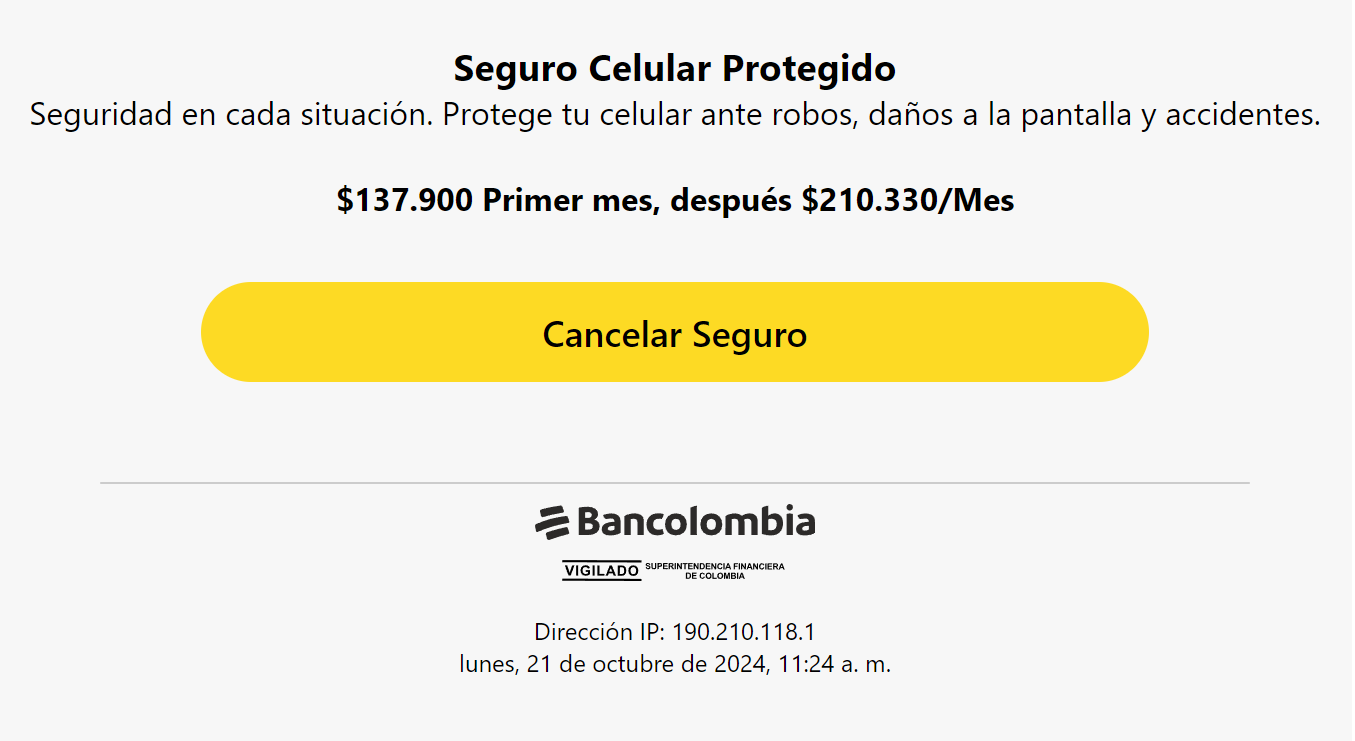
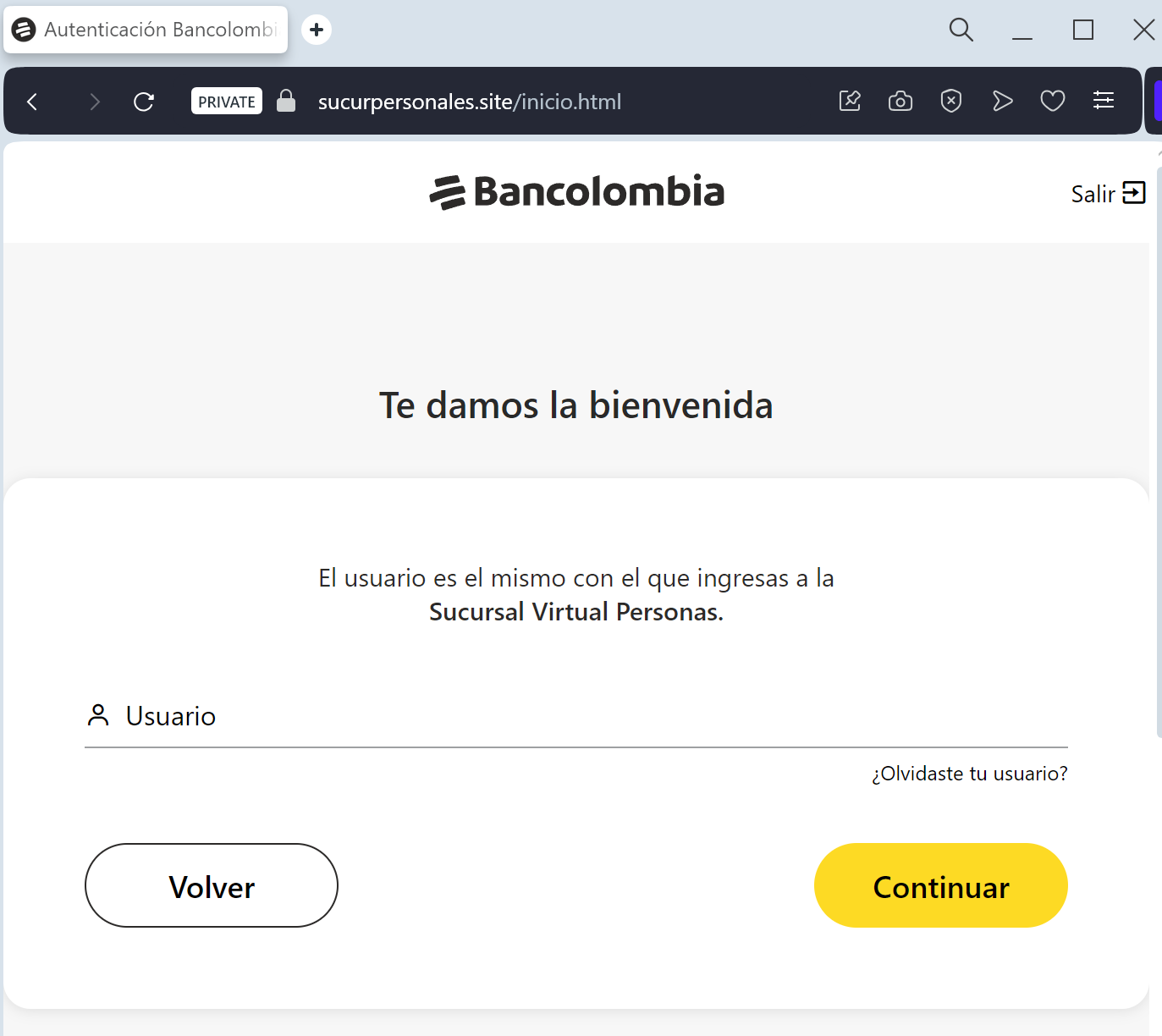
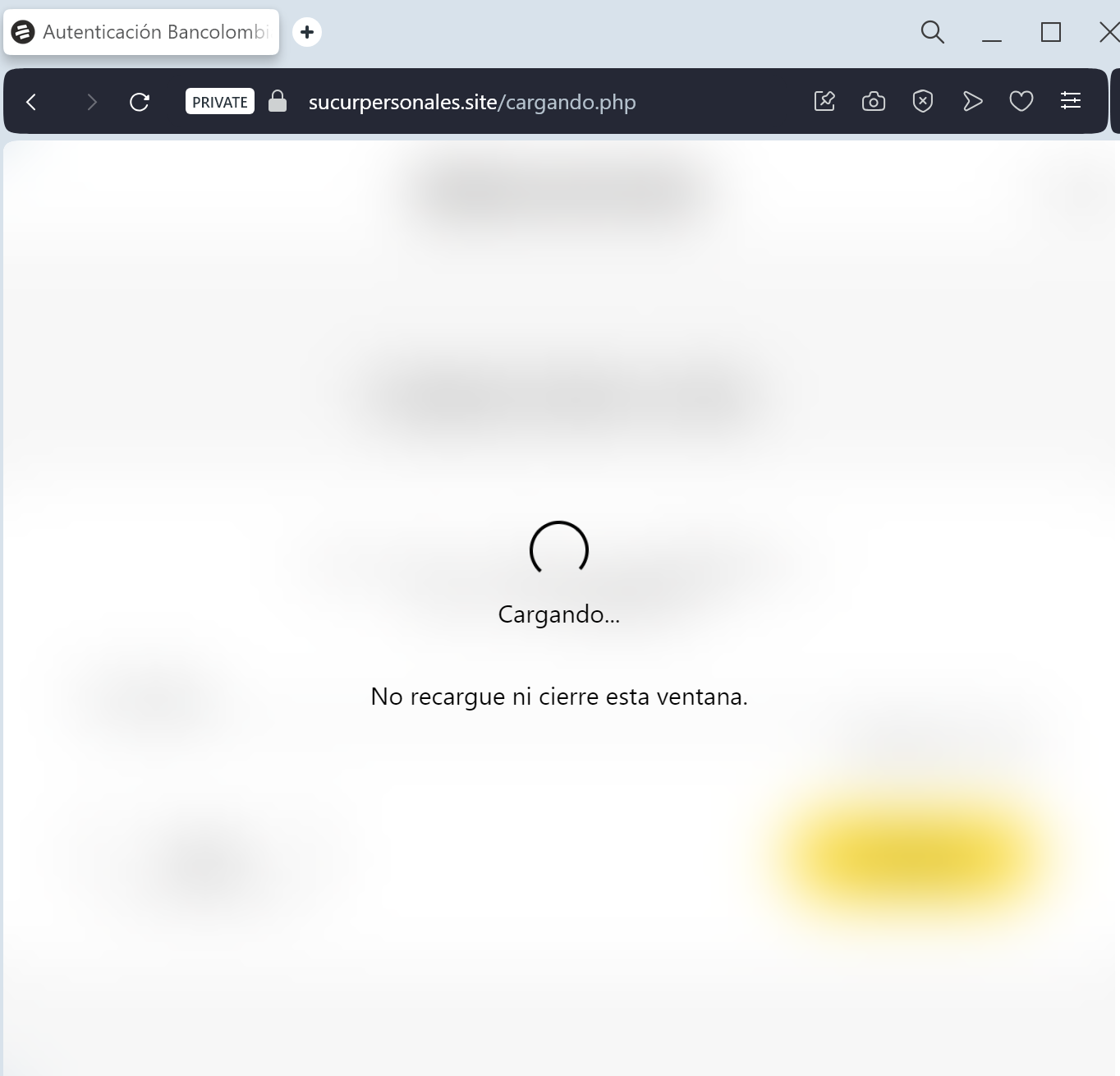
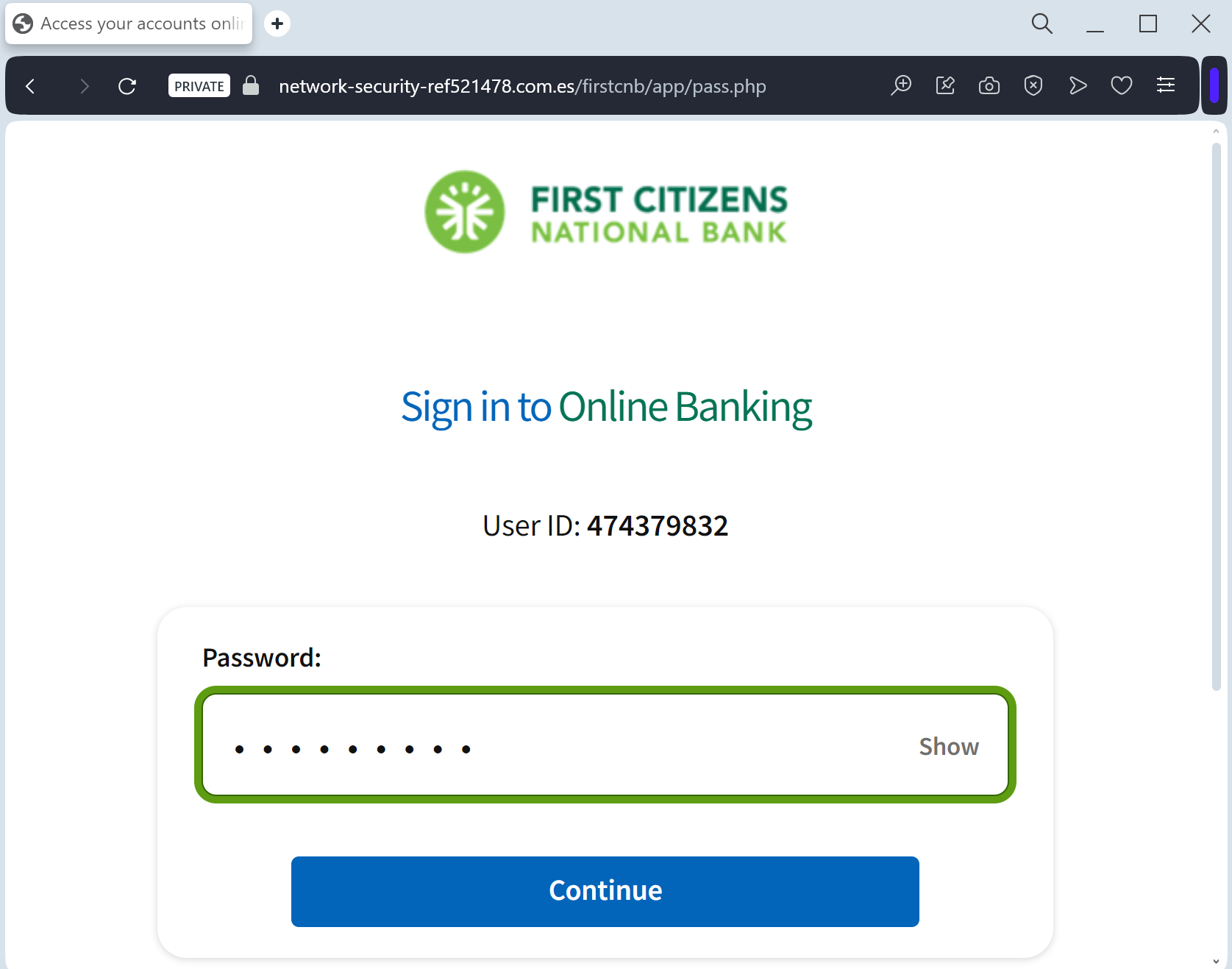
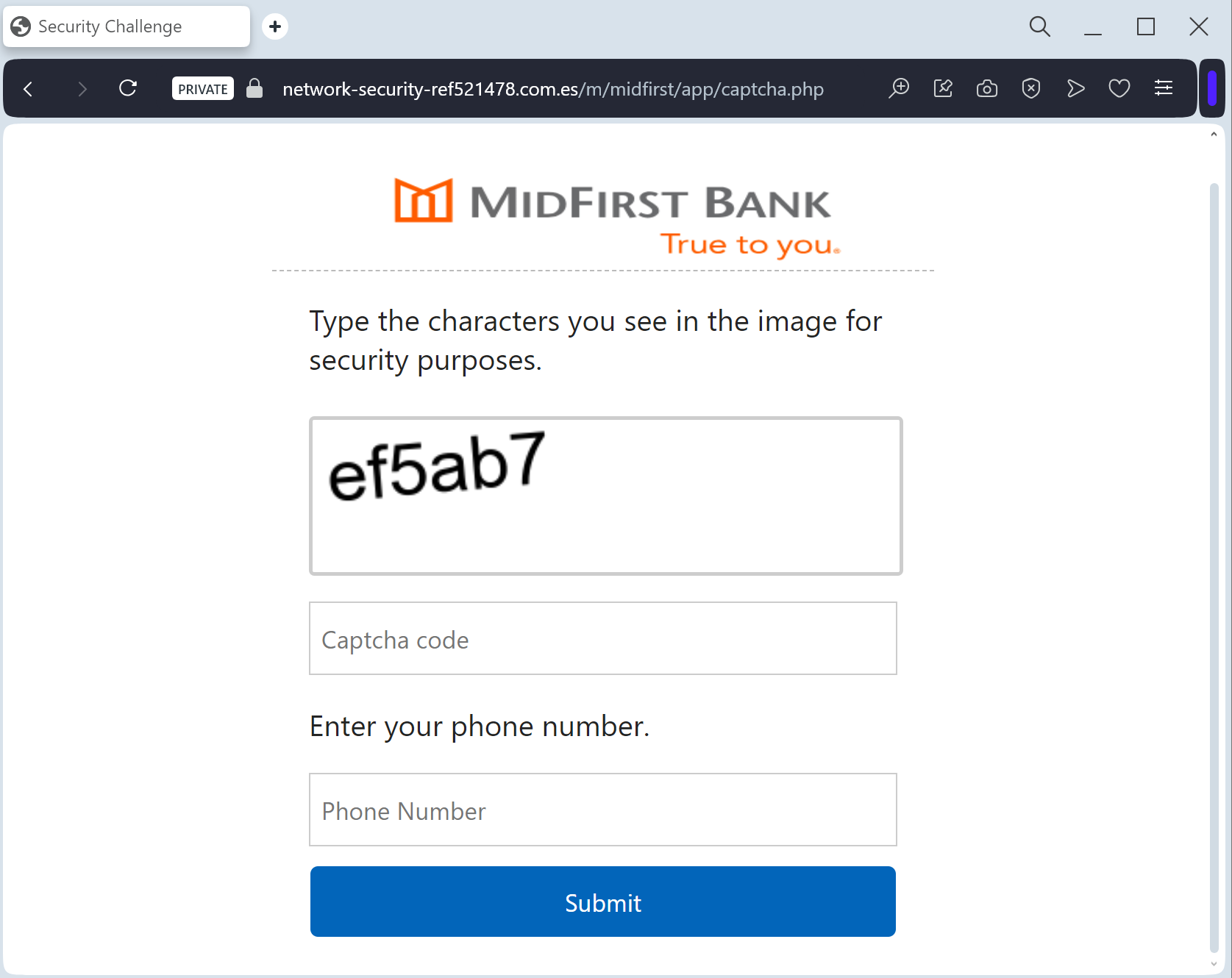
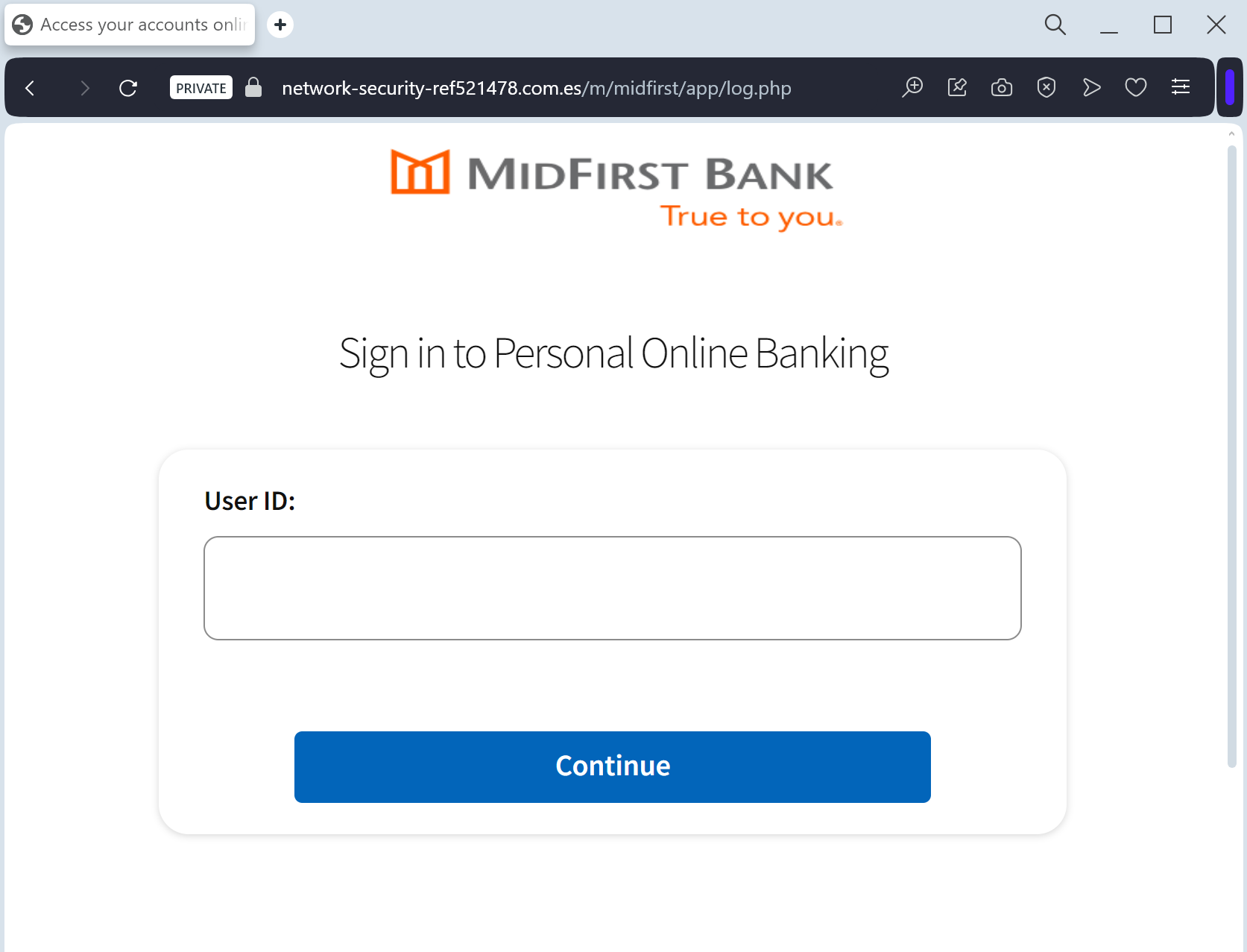
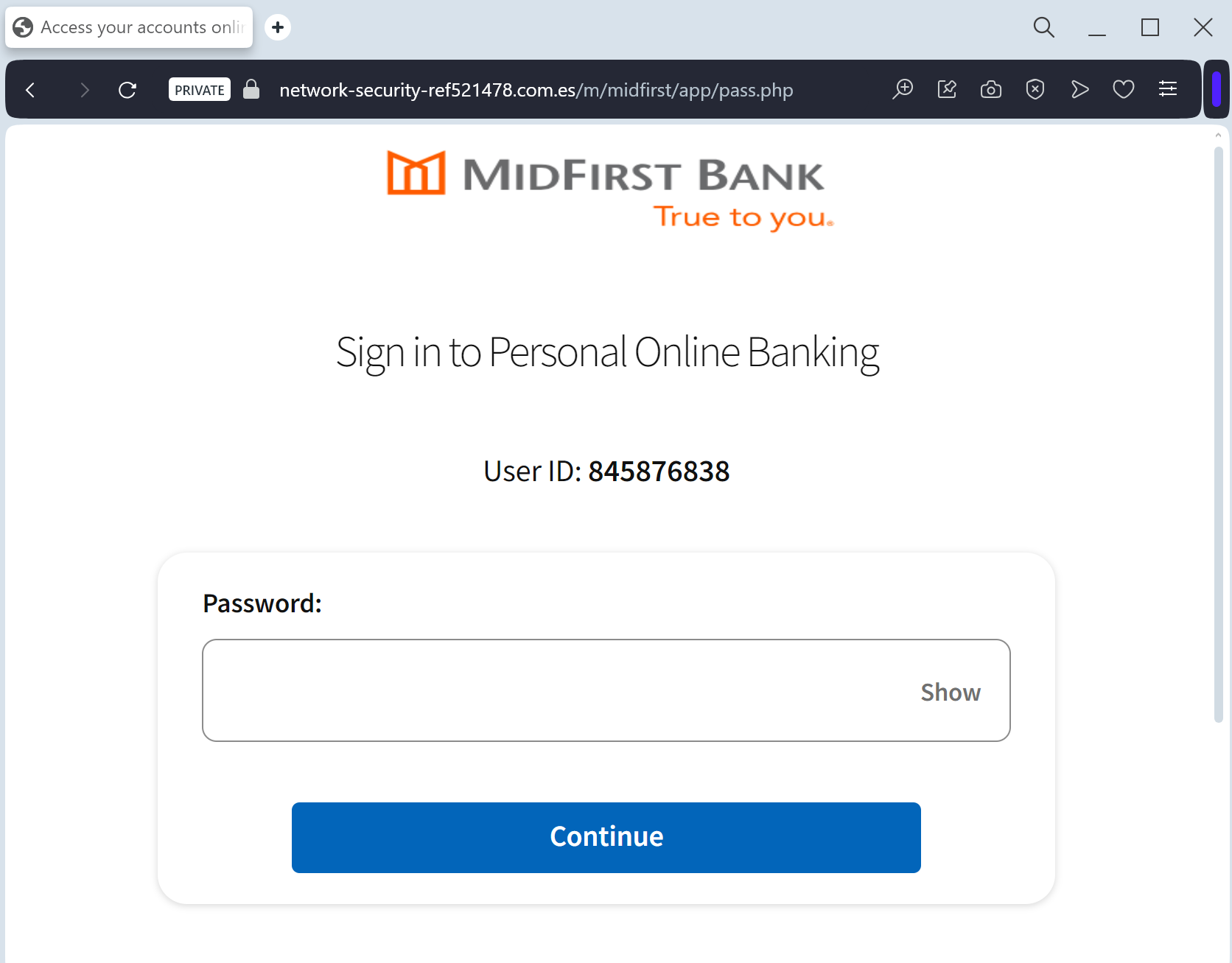
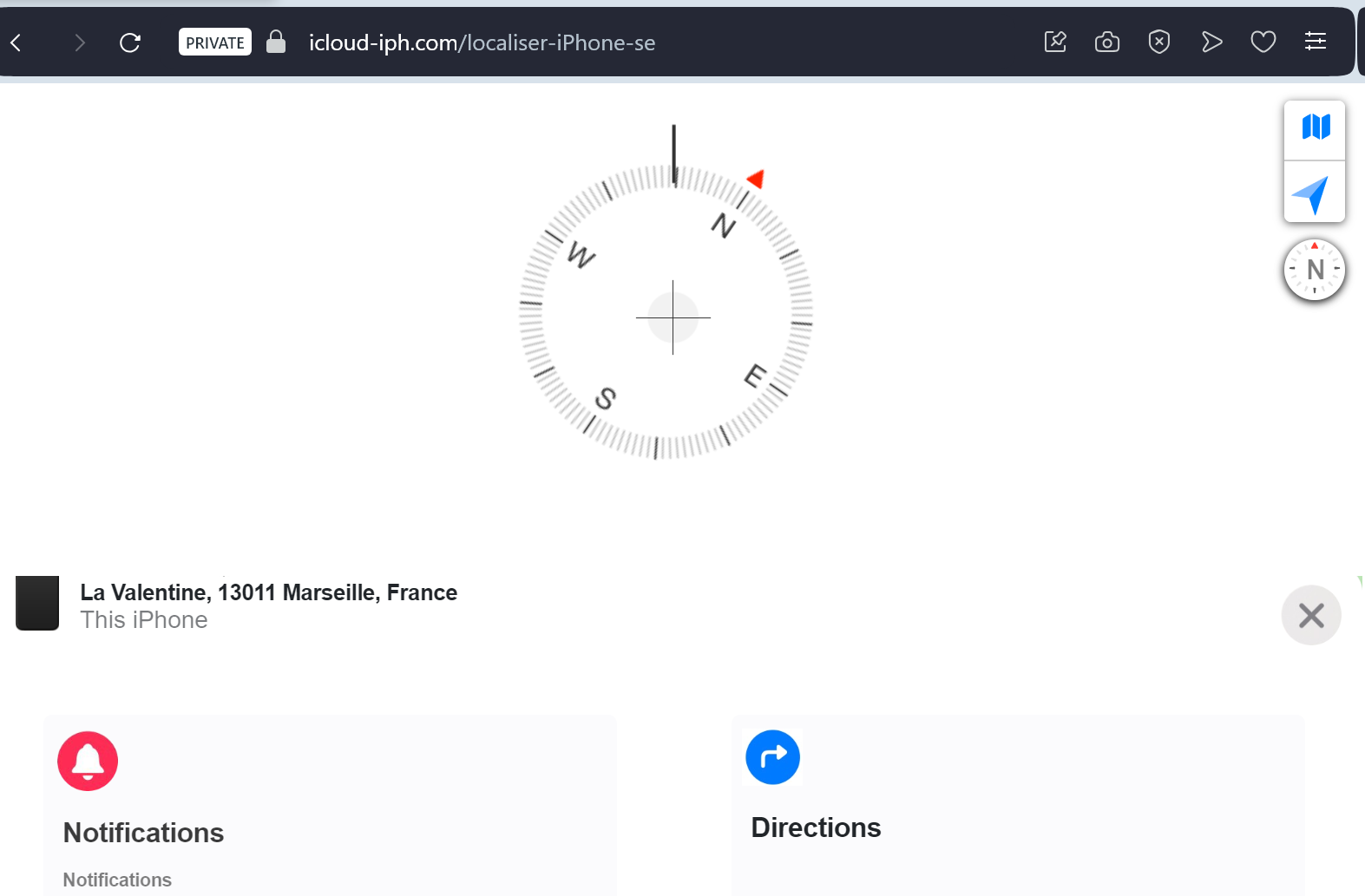
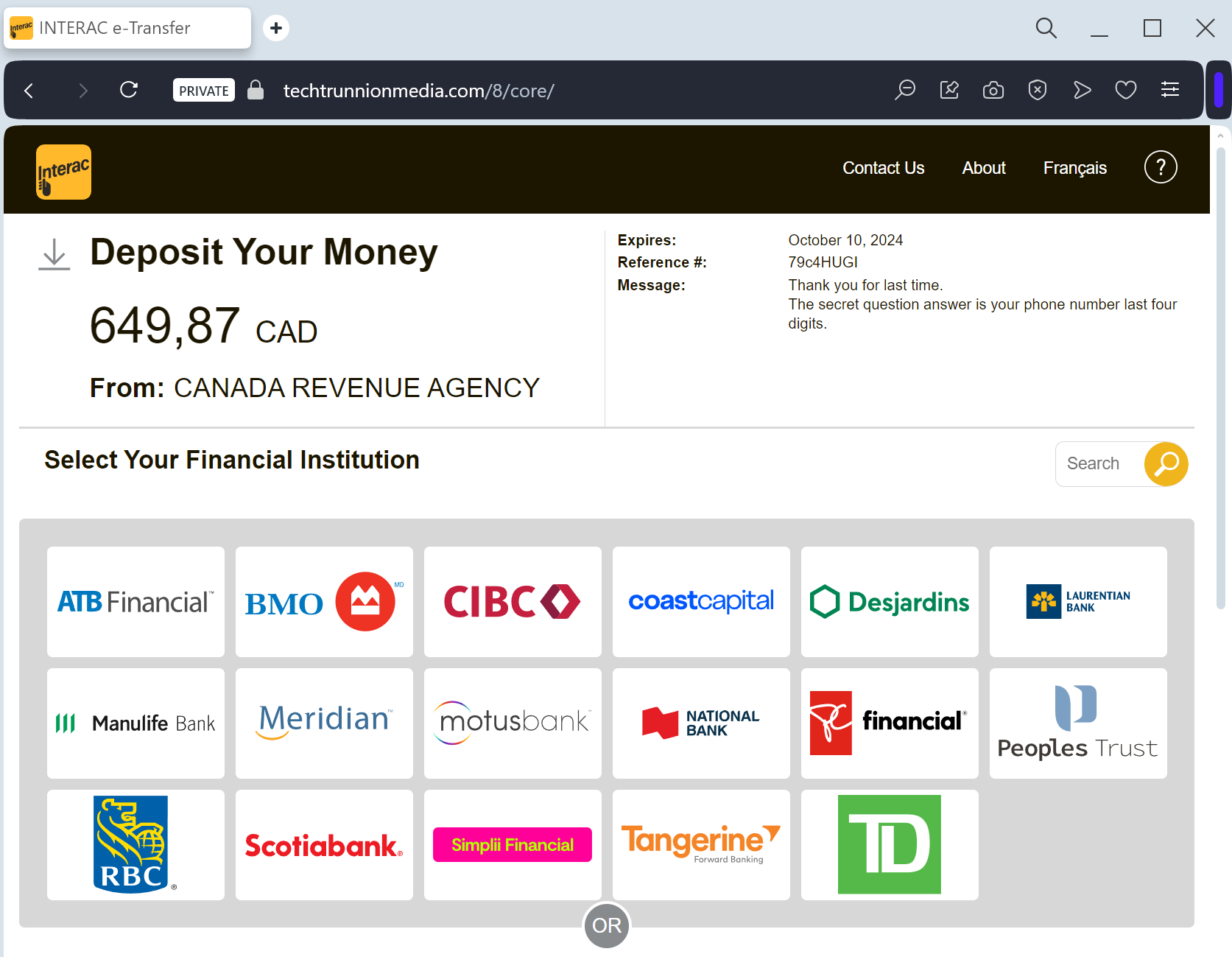
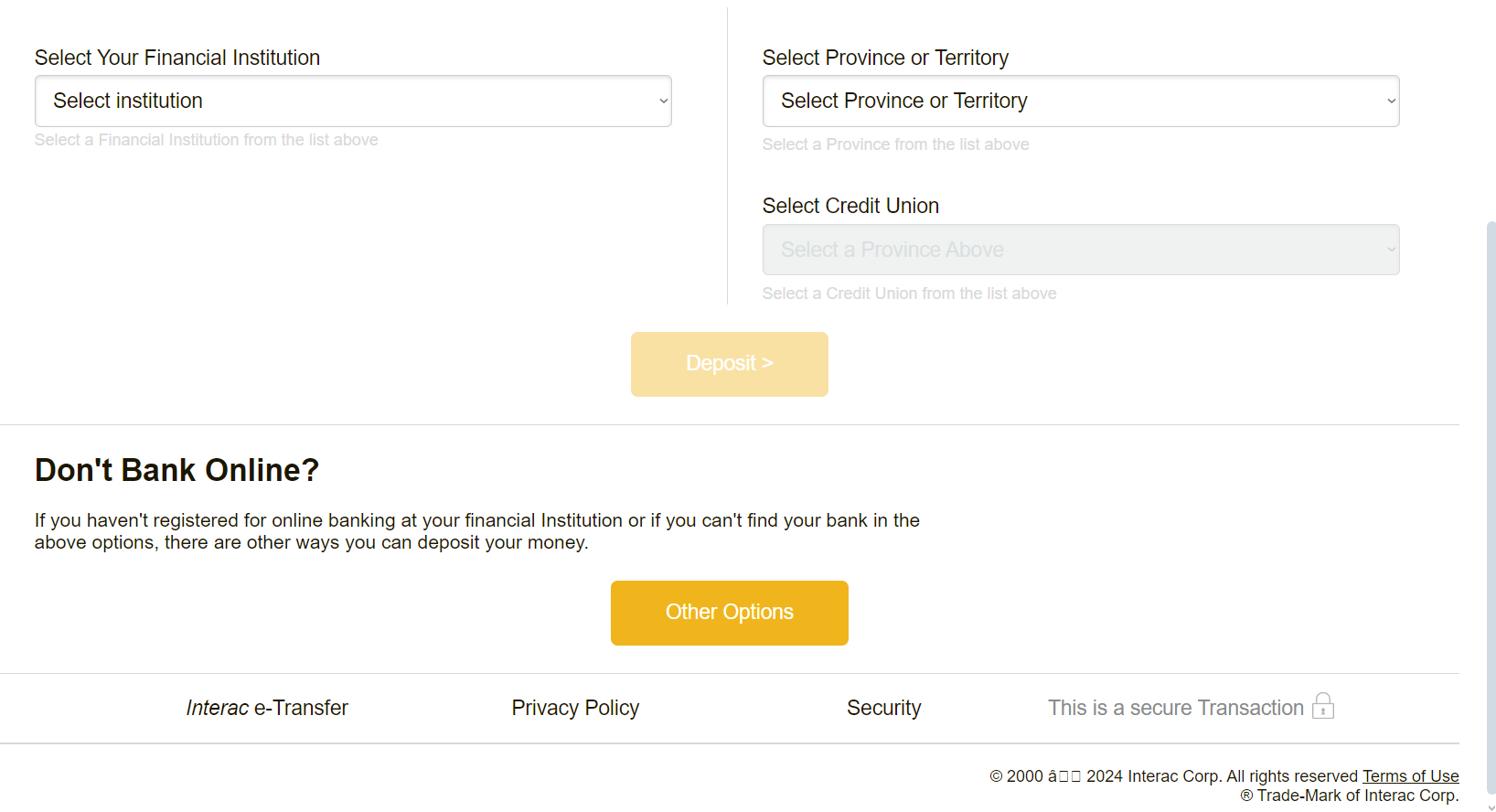
The link leads to a professional clone of the ÖGK or MeineSV (Social Insurance) portal. To “process the refund,” the victim is led through a series of forms designed to harvest:
Full Name and Address
Date of Birth (Geburtsdatum)
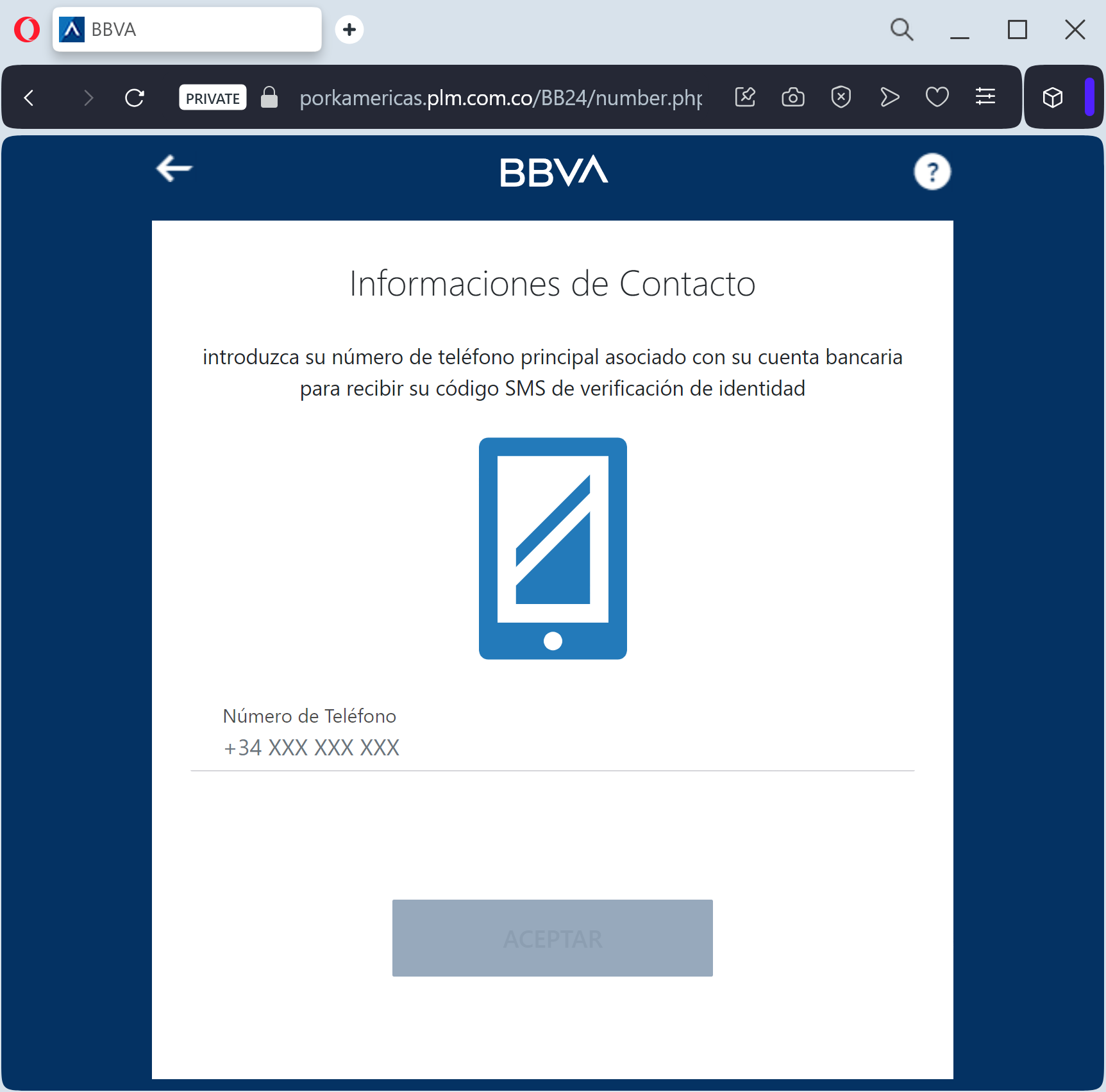
Mobile Phone Number
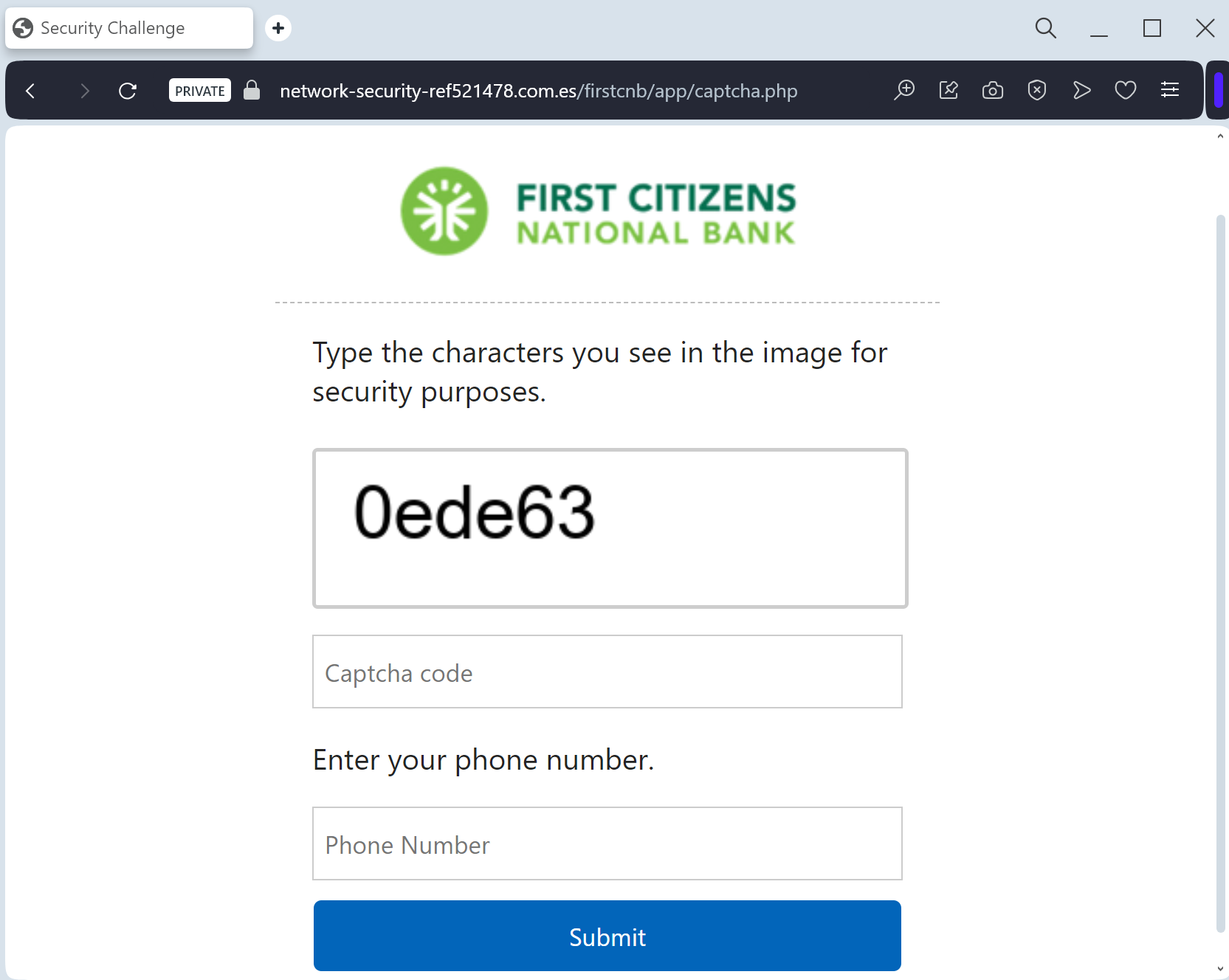
Credit/Debit Card Details (Number, Expiration Date, and CVV)
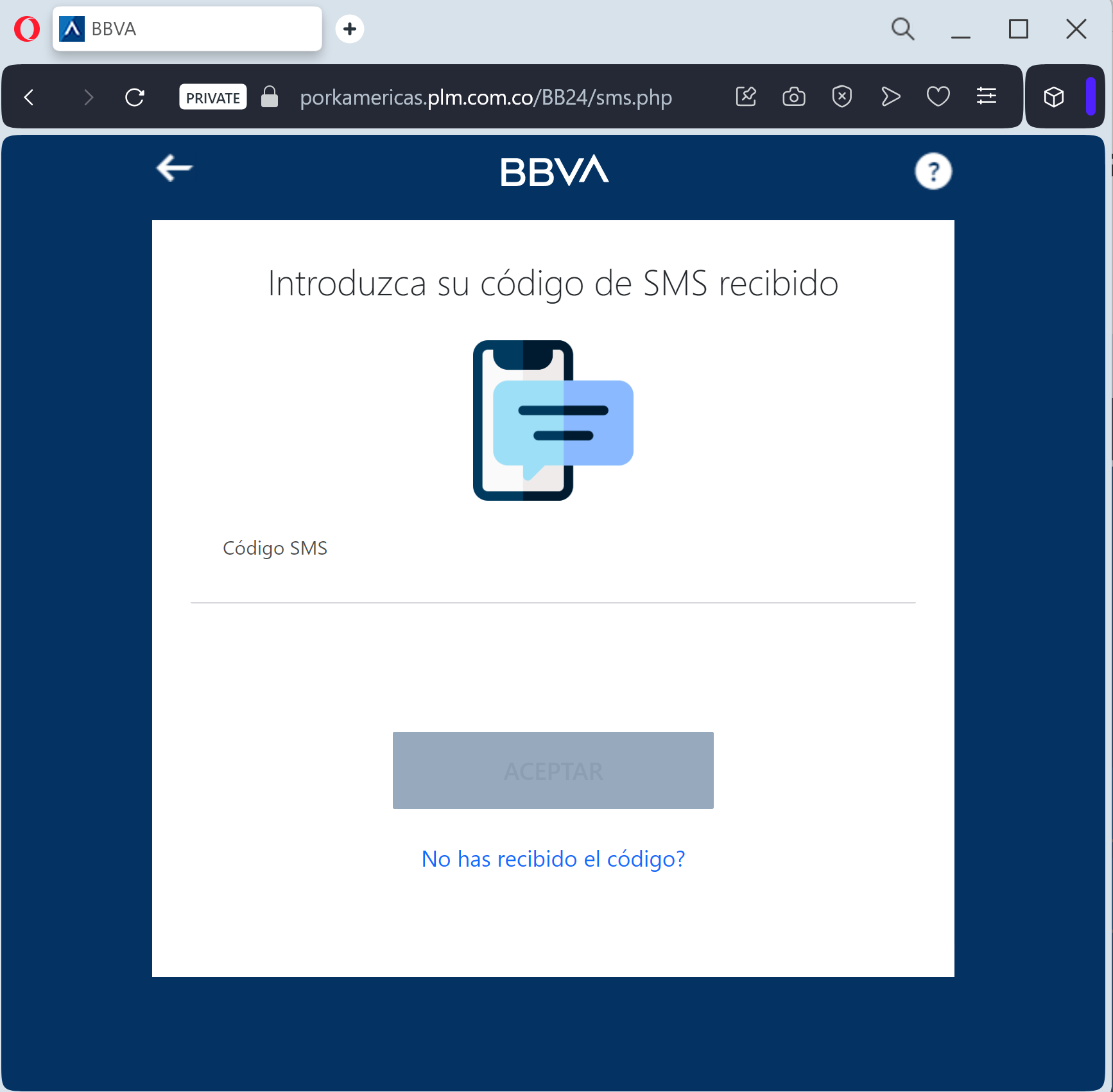
SMS 3D-Secure Codes: Intercepted in real-time to authorize fraudulent payments instead of receiving a refund.
Red Flags to Watch For
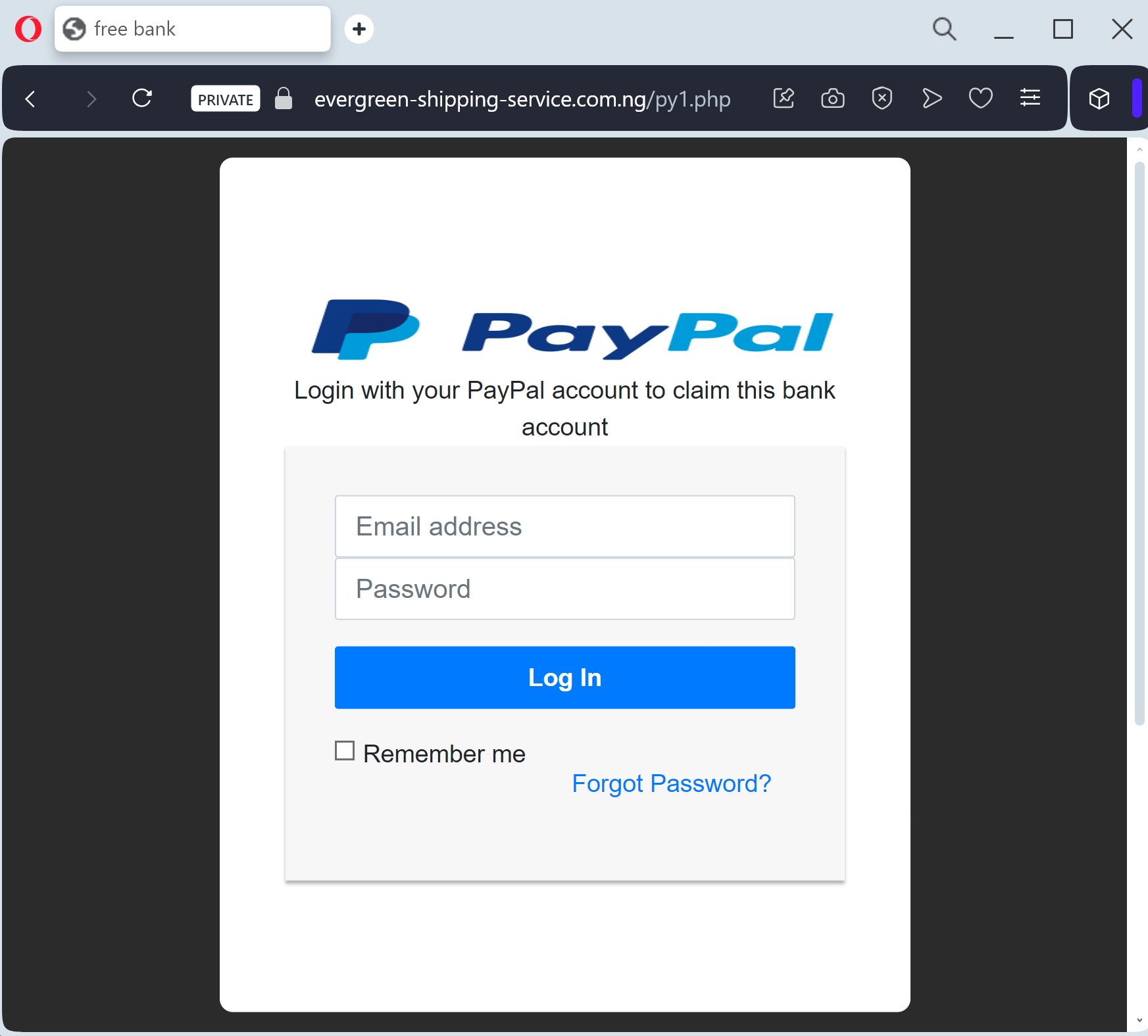
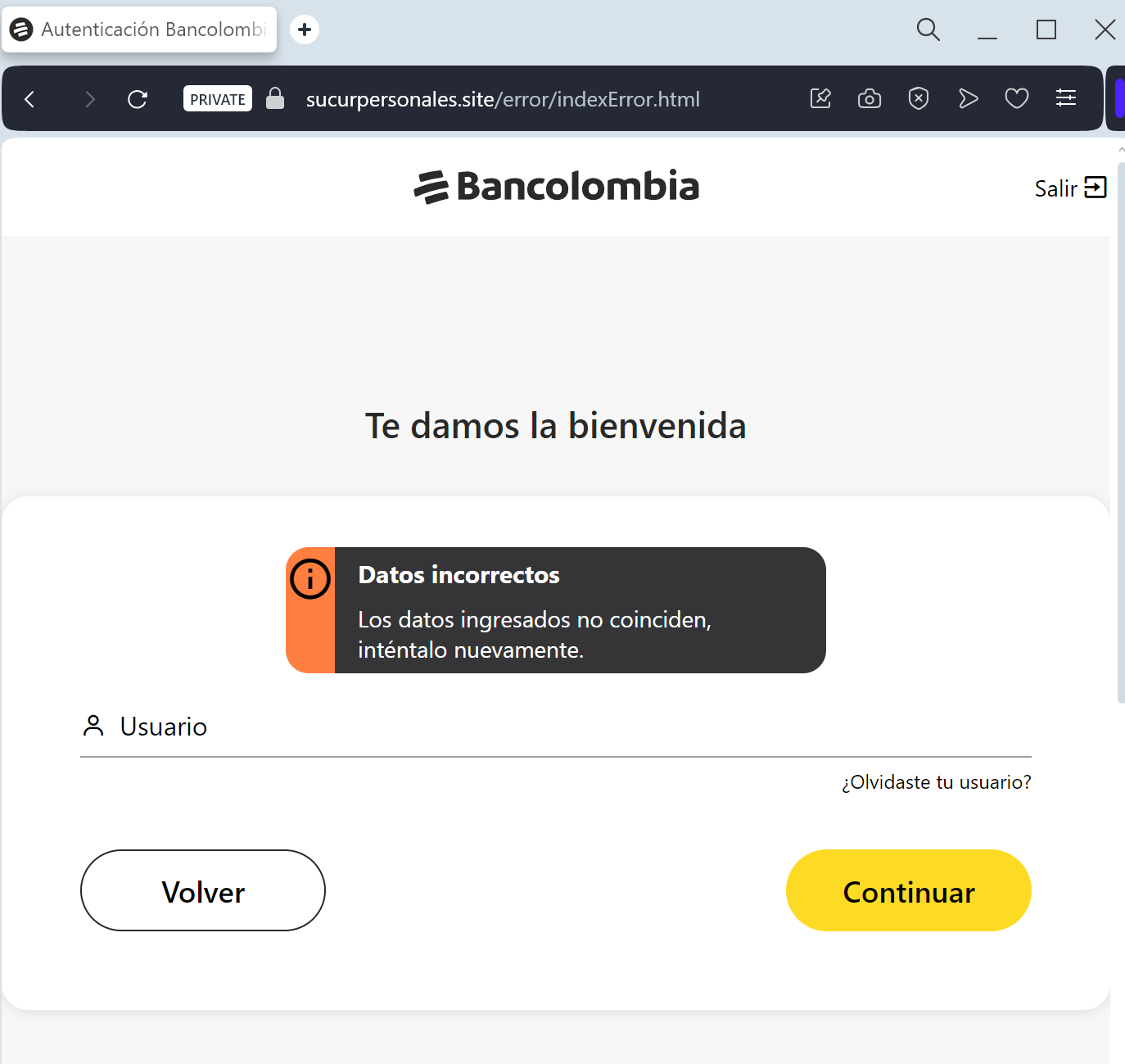
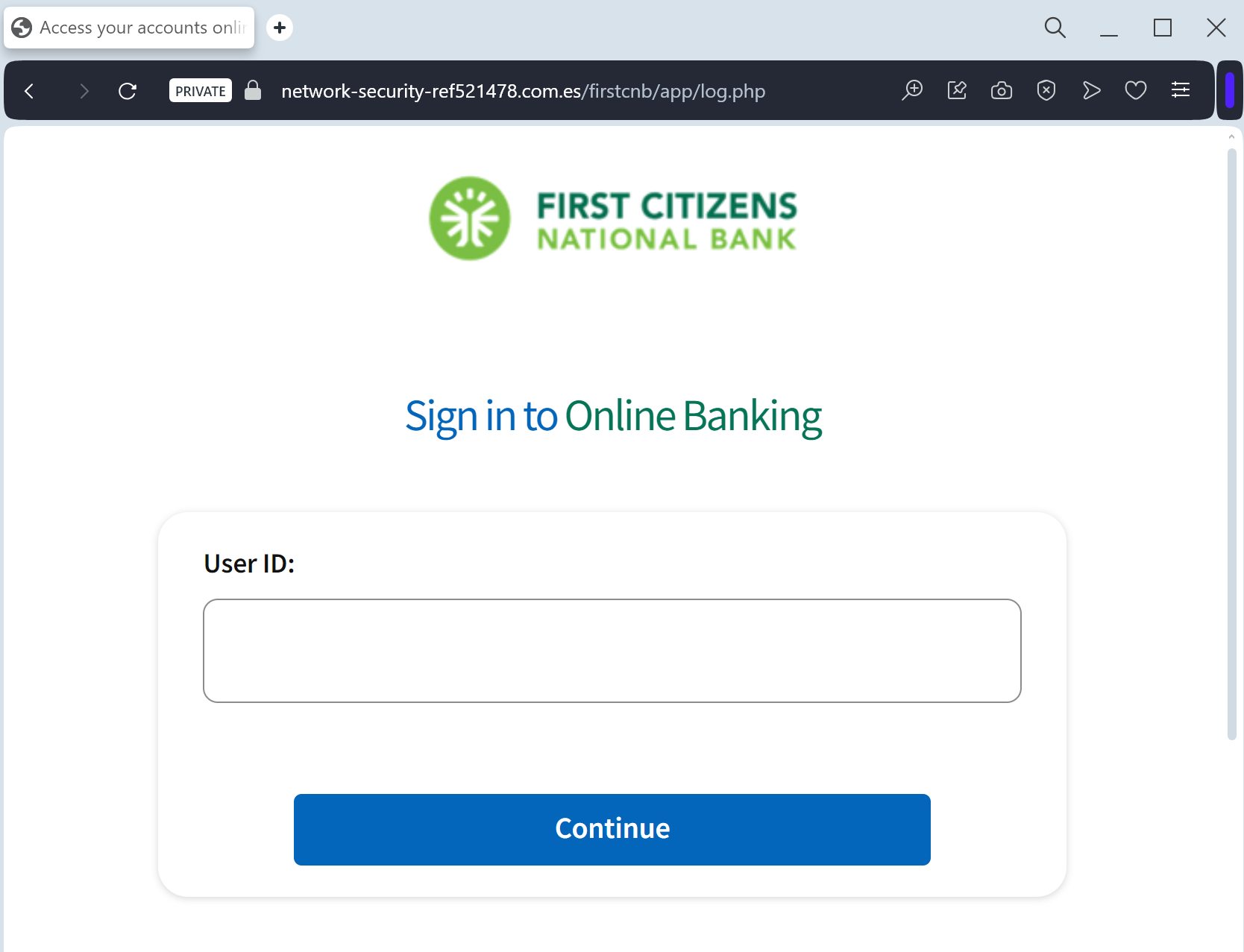
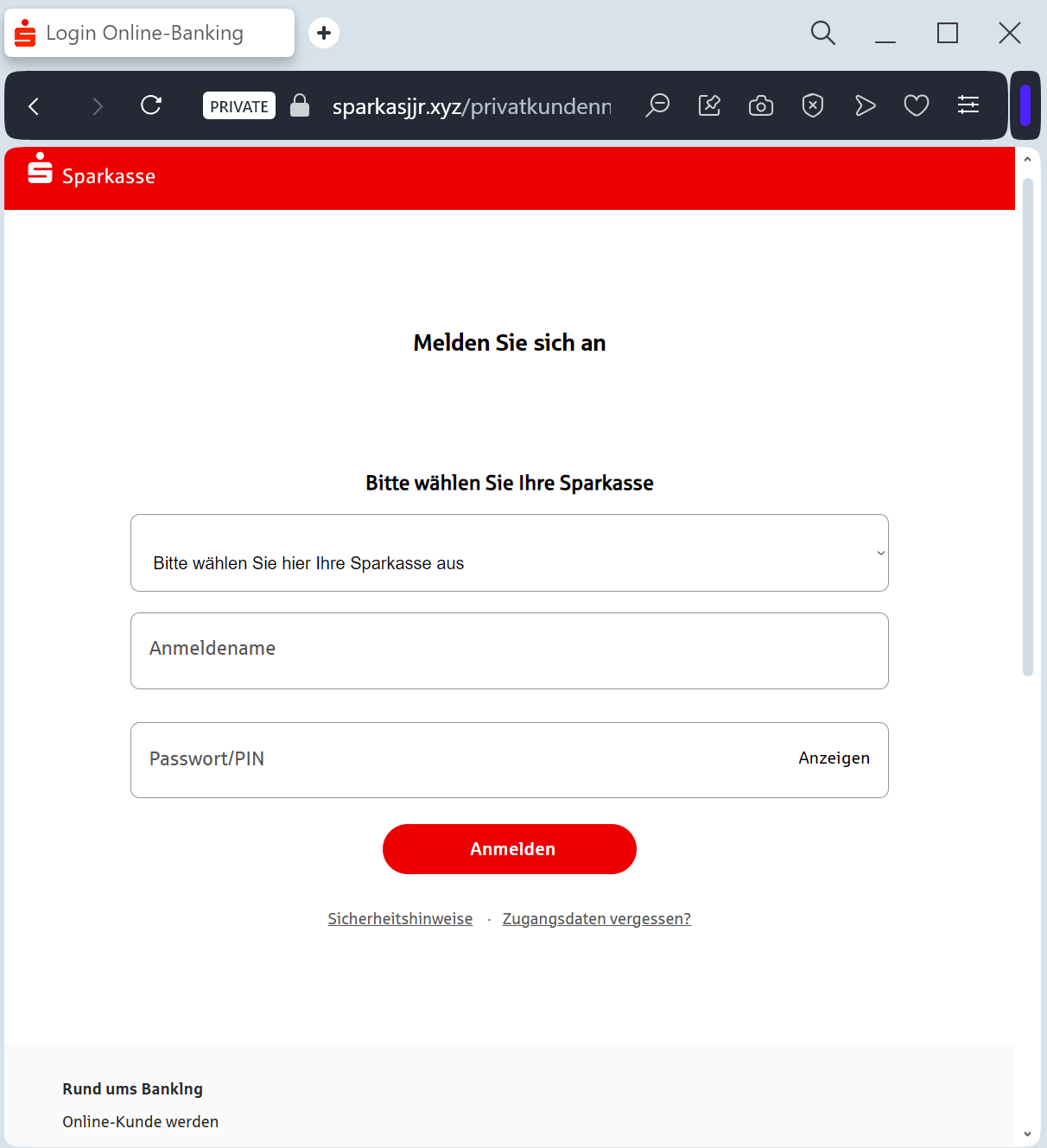
Deceptive Domain: The official domain is gesundheitskasse.at (or meinesv.at). Phishing sites use lookalikes such as oegk-refund.online, meinesv-at.com, oegk-erstattung.net, or free subdomains like oegk-at.web.app.
Requests for Credit Card Info for a Refund: Public health funds and tax offices in Austria pay out refunds via Bank Transfer (IBAN). They will never ask for your credit card’s CVV or expiration date to “send” you money.
Language Tone: Messages claiming “Immediate action required to avoid losing your credit” are classic social engineering tactics.
How to Protect Yourself
Use ID Austria: Whenever possible, use the official ID Austria (formerly Handy-Signatur) for secure authentication. Official portals like meinesv.at always use this secure login method.
The “No Link” Rule: Government and health agencies will never send you a link via SMS to ask for your bank or card details.
Check the Official Portal: If you are expecting a refund, log in directly to the official MeineSV portal or the ÖGK App by typing the address manually.
Verify by Phone: If in doubt, call the official ÖGK service line at 05 0766-0 to check if any refund notifications were actually sent.
Expert Security Tip:
This is a Refund-to-Skimming attack. Scammers exploit the fact that people are always happy to receive “found money.” Remember: If a government agency or health fund needs to pay you, they already have your bank account on file. Never provide your CVV code to “receive” a payment.