A phishing campaign targeting RWE AG customers in Germany uses fake energy refund emails to steal sensitive personal and financial data, including online banking credentials, via a fraudulent portal. The scam pressures users with urgent deadlines to claim a “refund for overpaid electricity costs” and directs them to malicious domains, such as kunden-rwe.net, to enter credentials. To protect against this threat, customers should only log in through the official rwe.com portal and report suspicious messages.
Target: RWE AG Customers and Energy Consumers in Germany
Threat Level: High (Financial Identity & Bank Access Theft)
Phishing Method Description
This attack leverages Utility Provider Impersonation. Scammers send out Phishing Emails or SMS (Smishing) claiming that due to a billing error or a government energy subsidy, the customer is entitled to a “Refund” (Guthaben) or “Climate Bonus.”
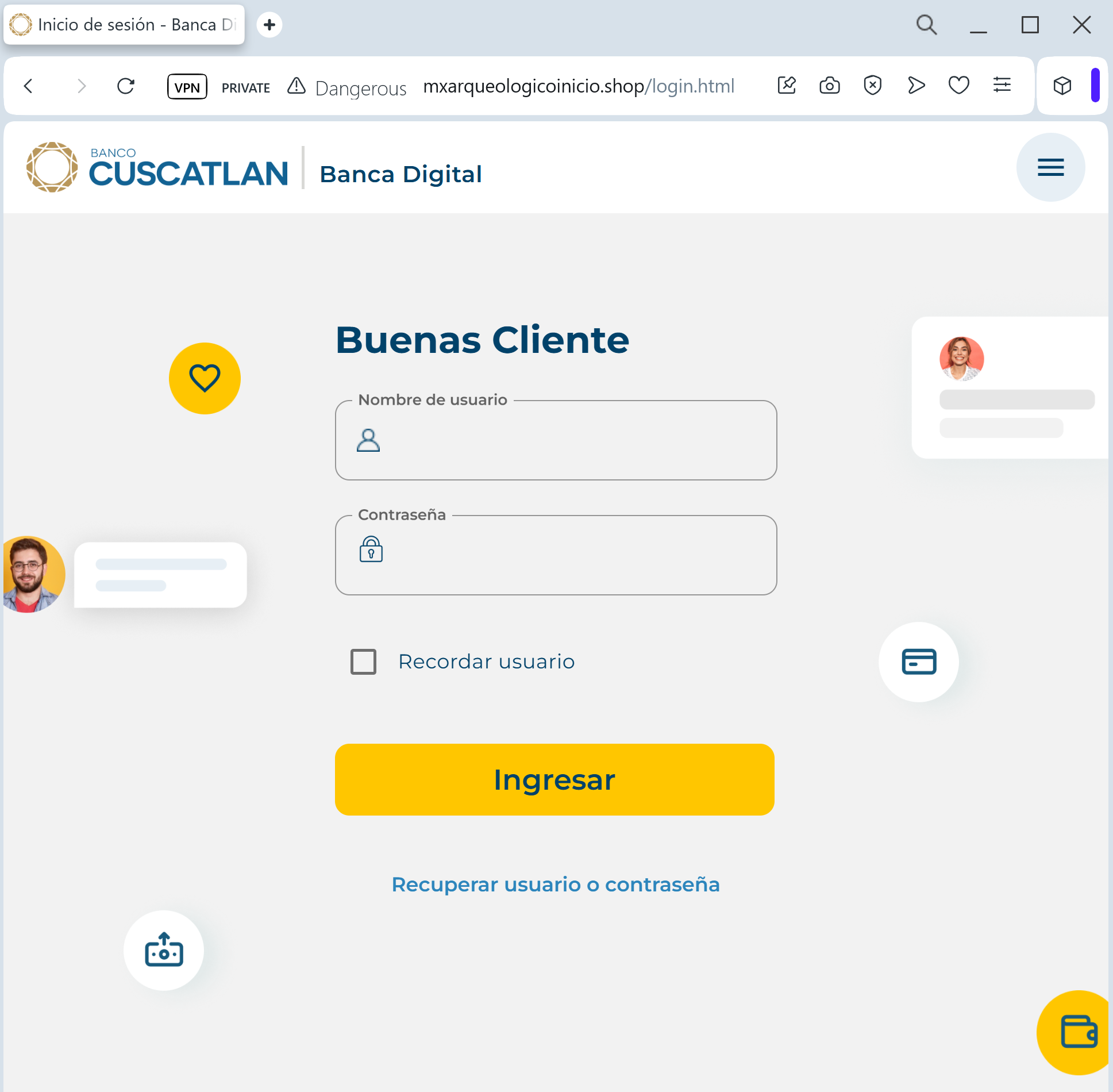
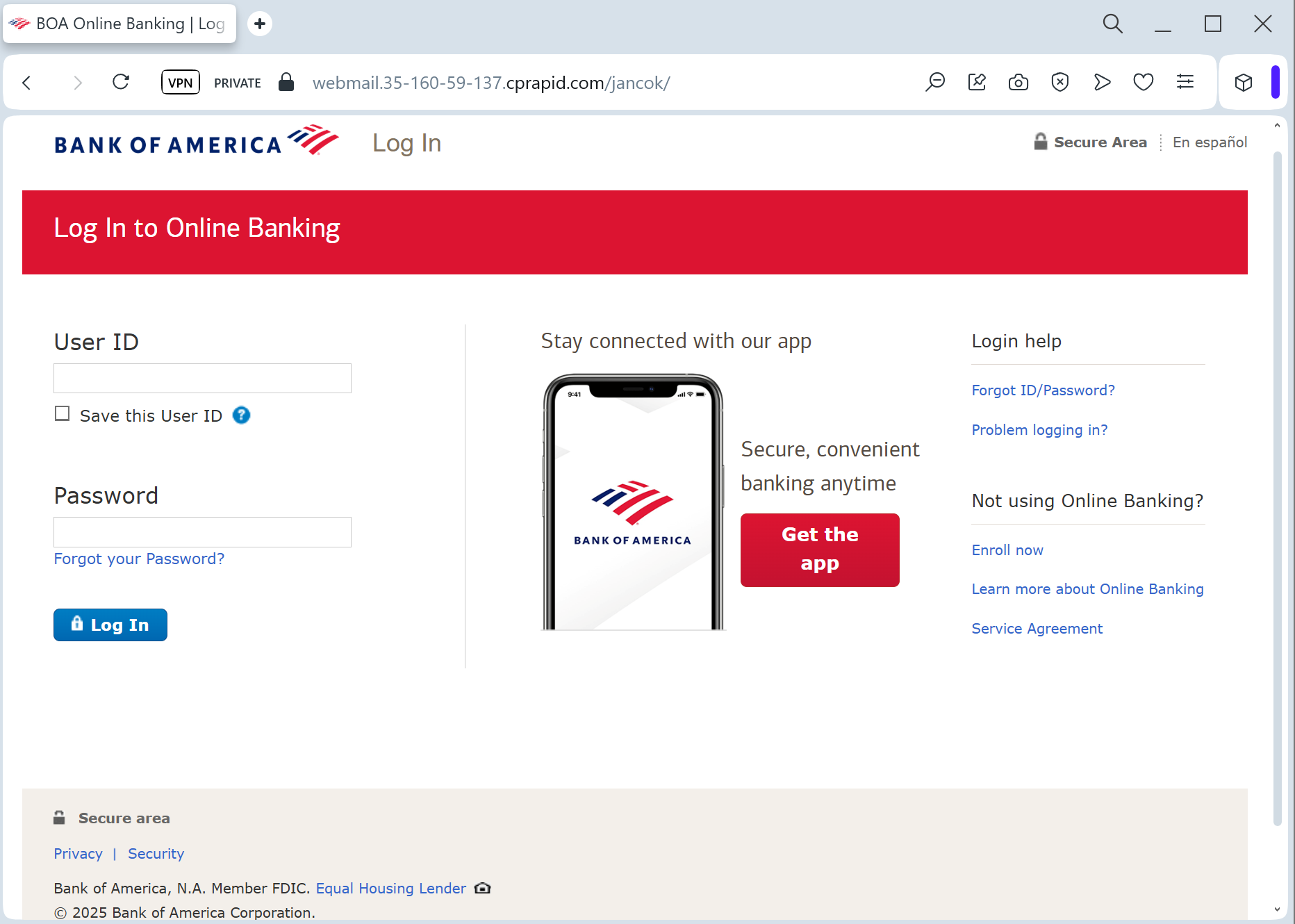
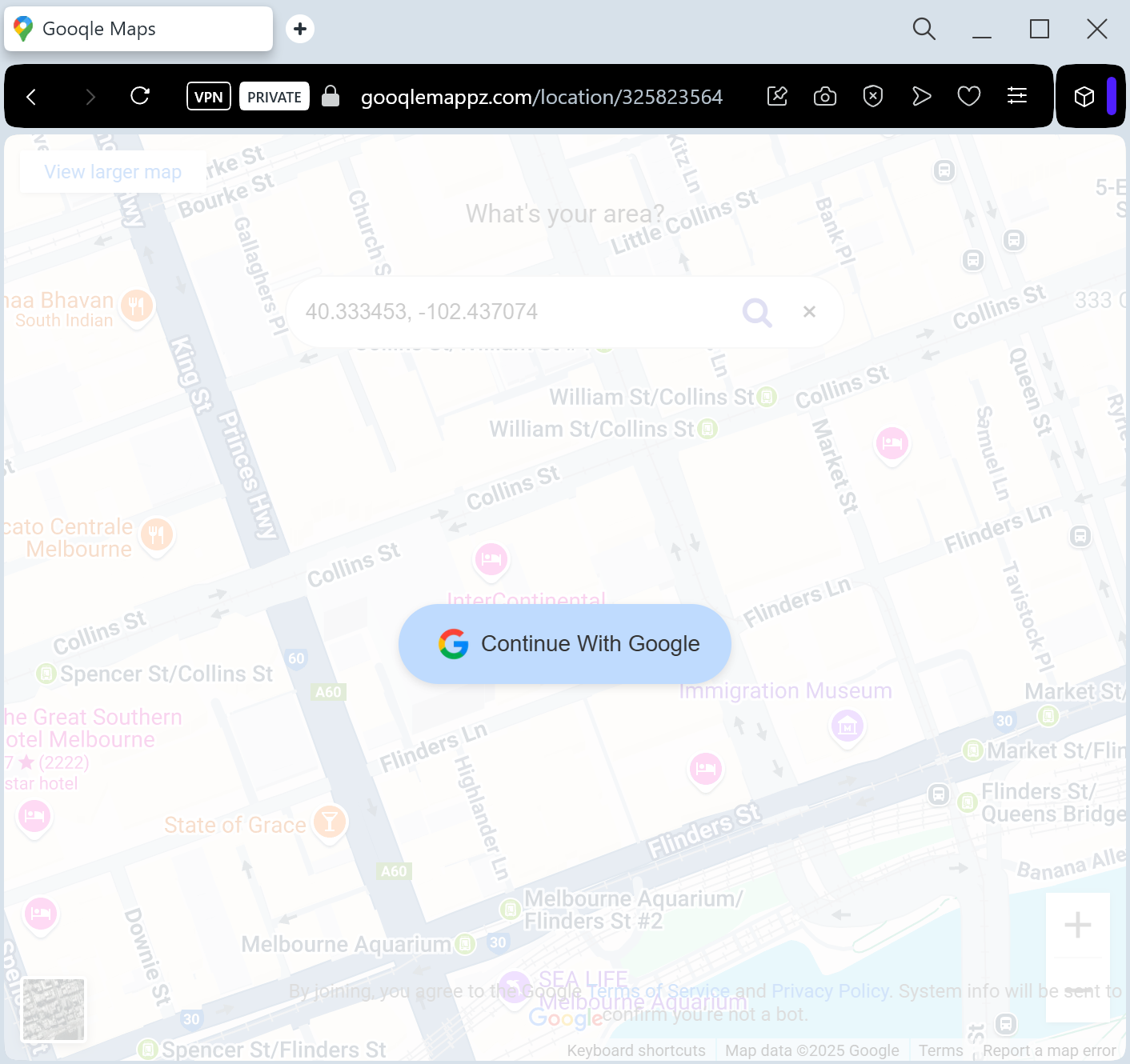
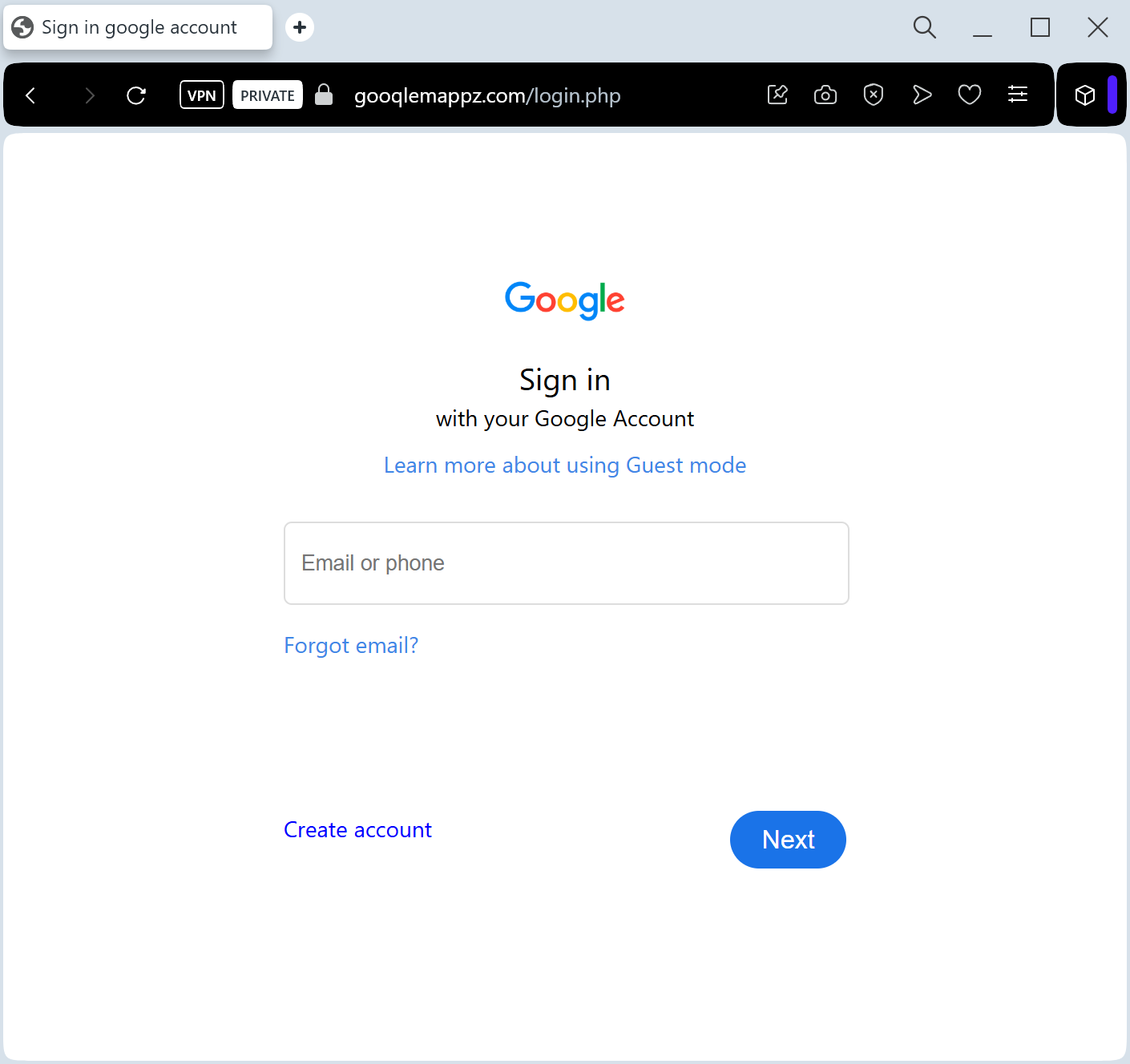
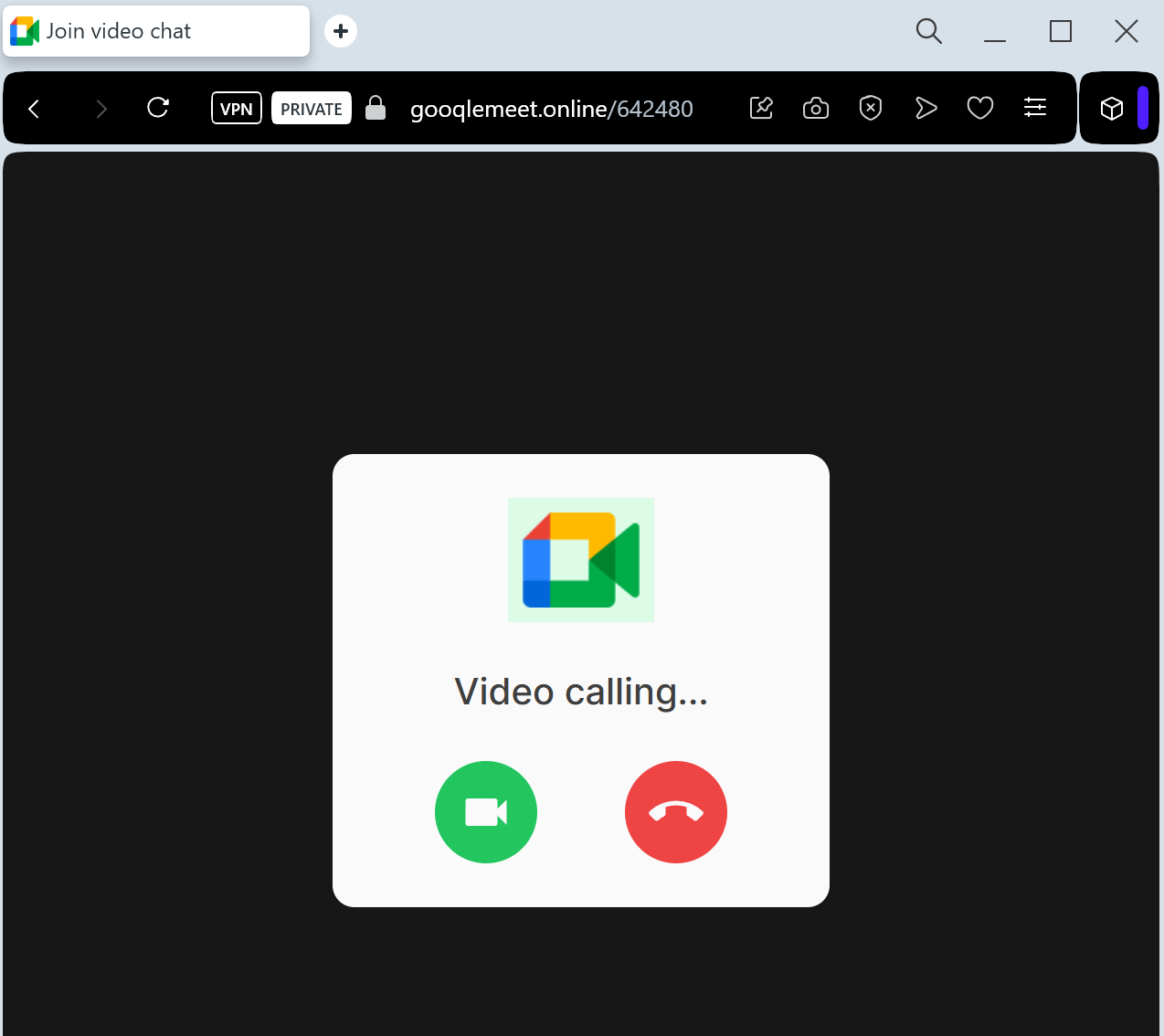
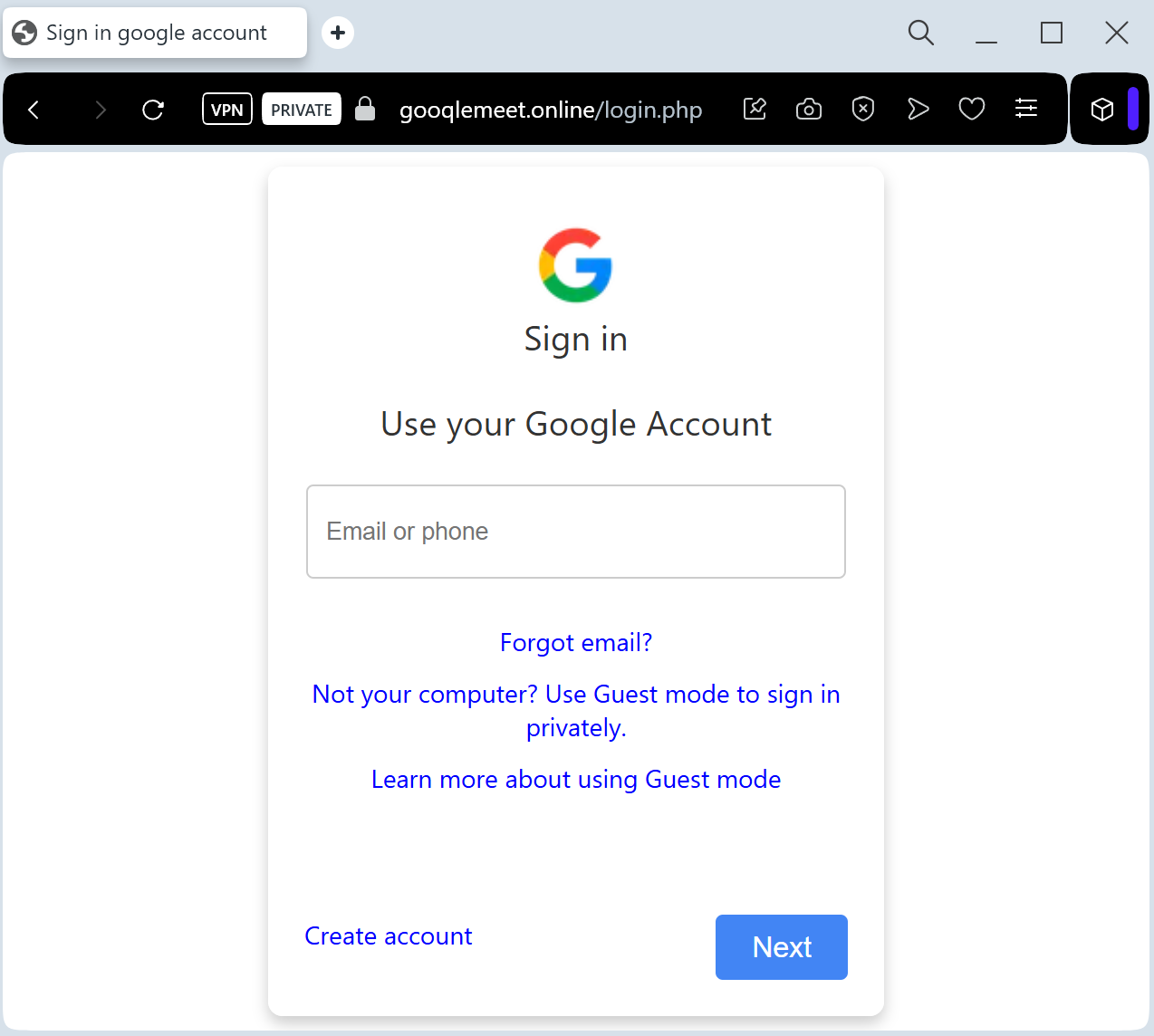
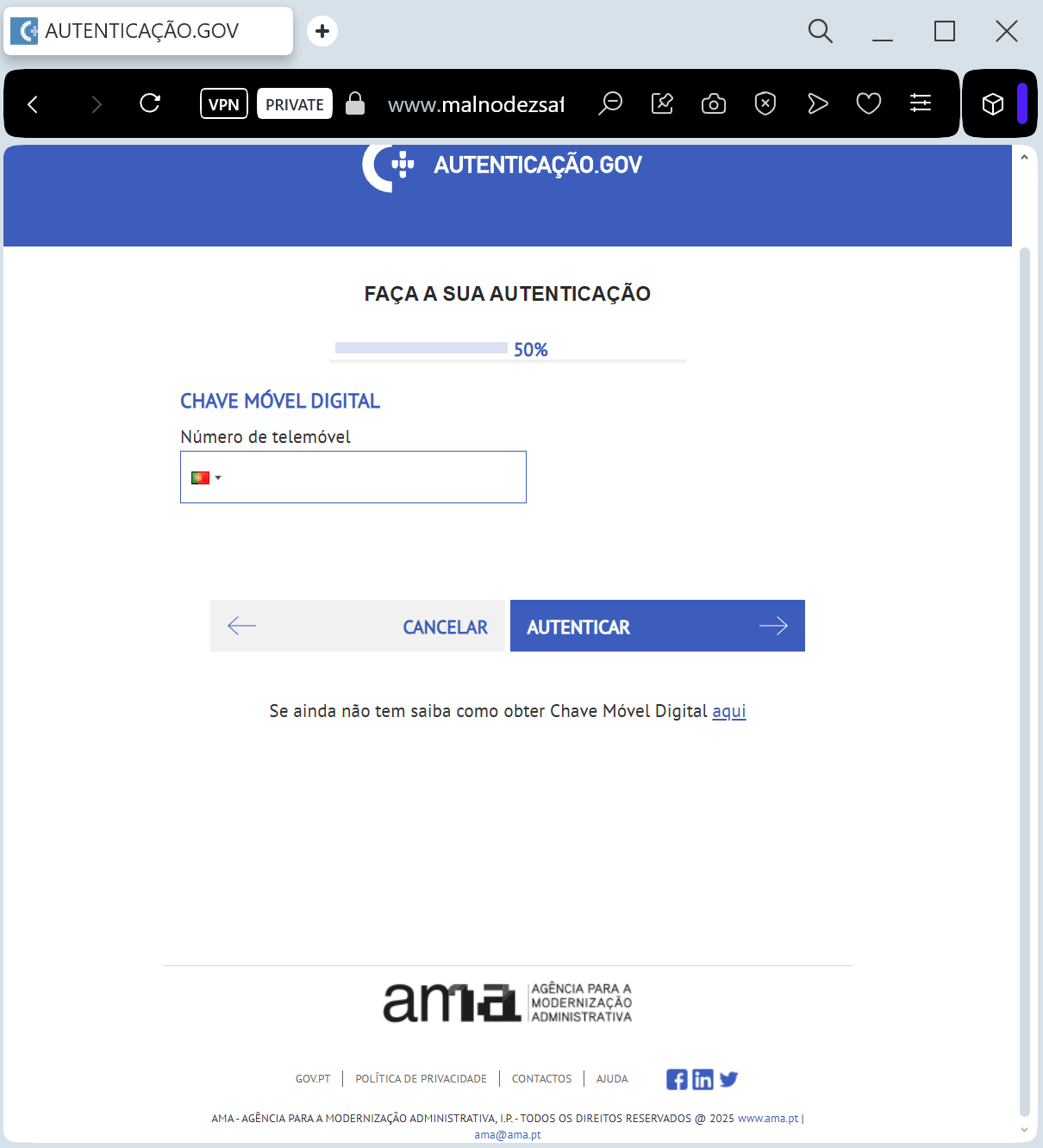
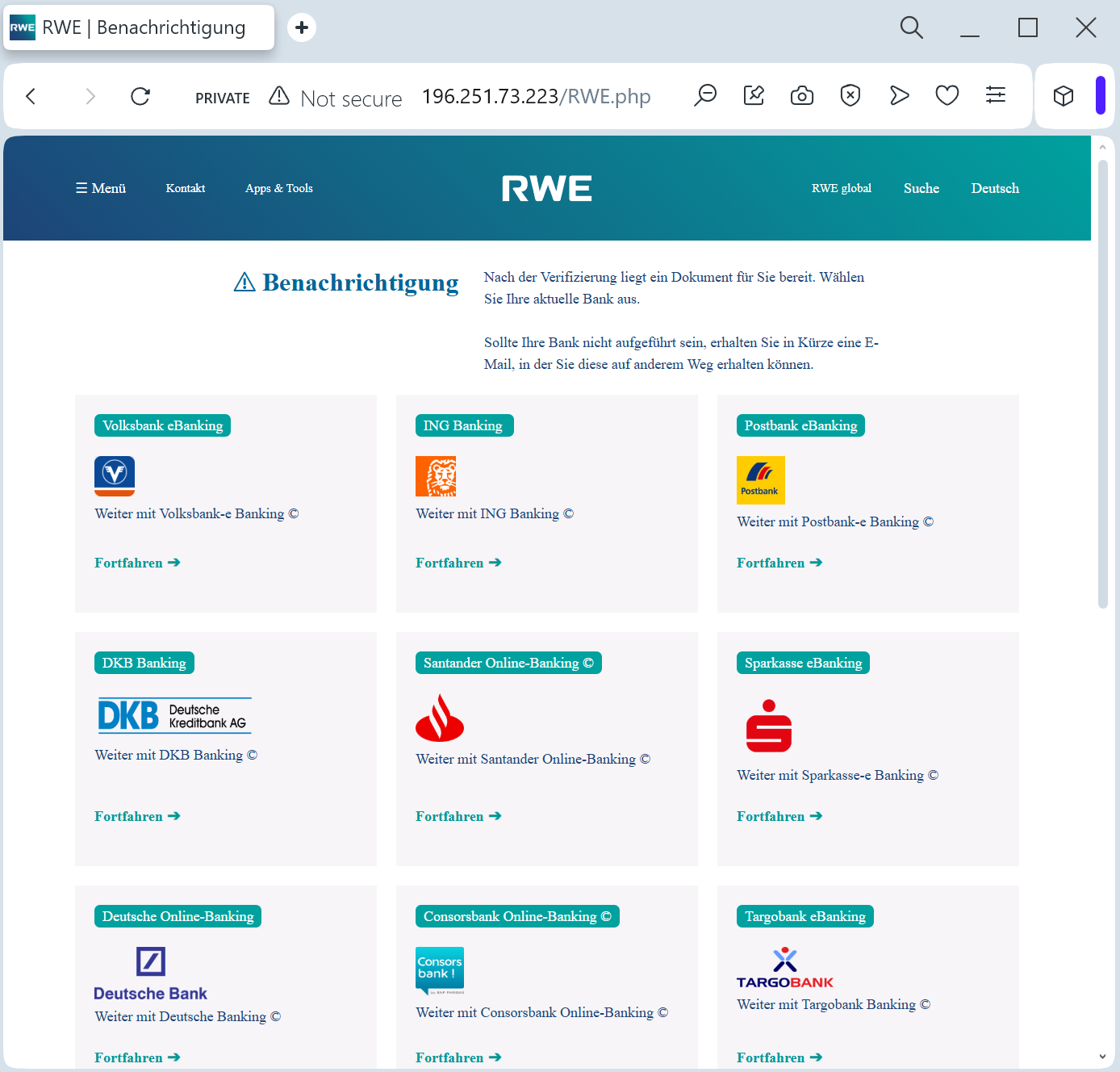
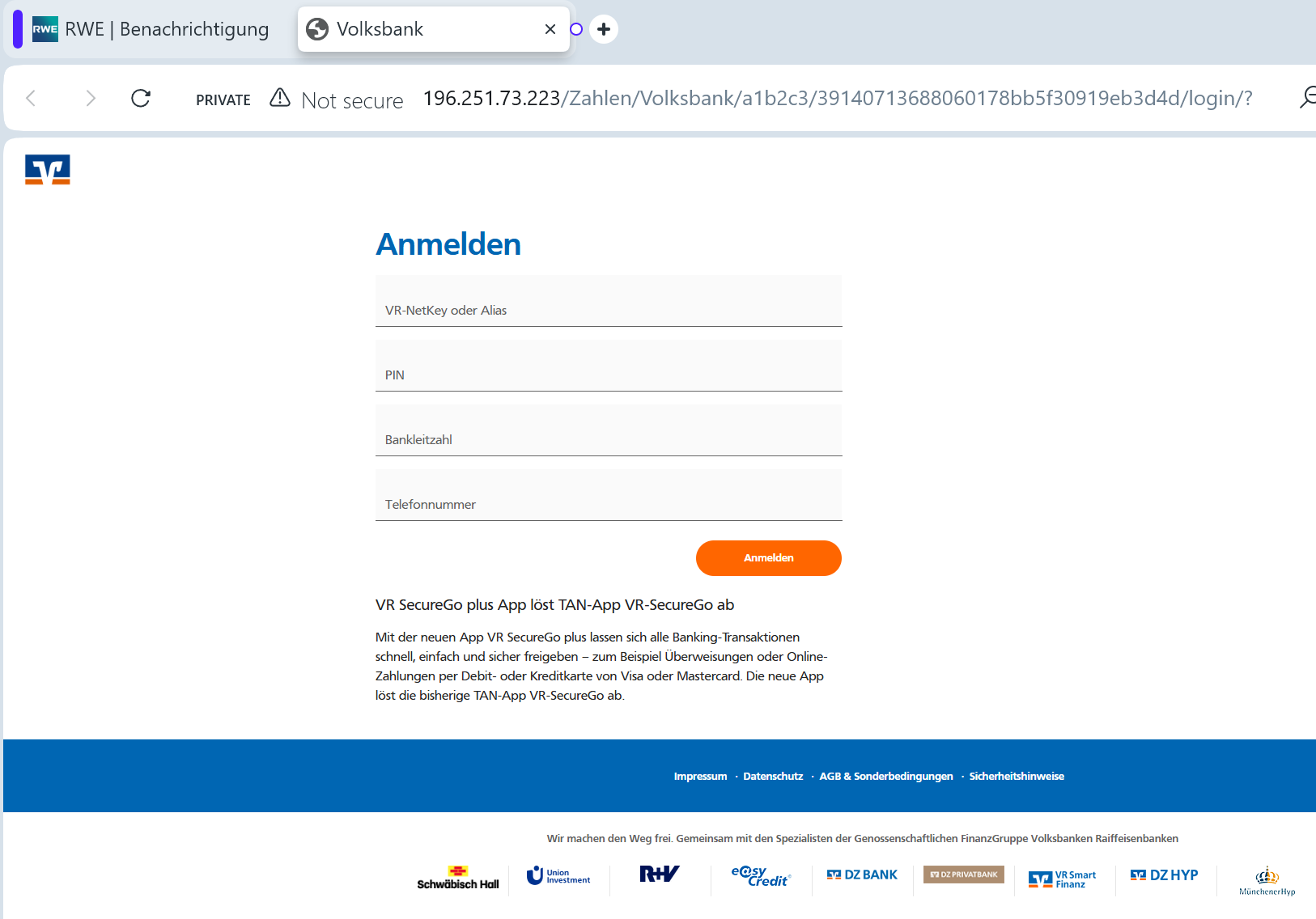
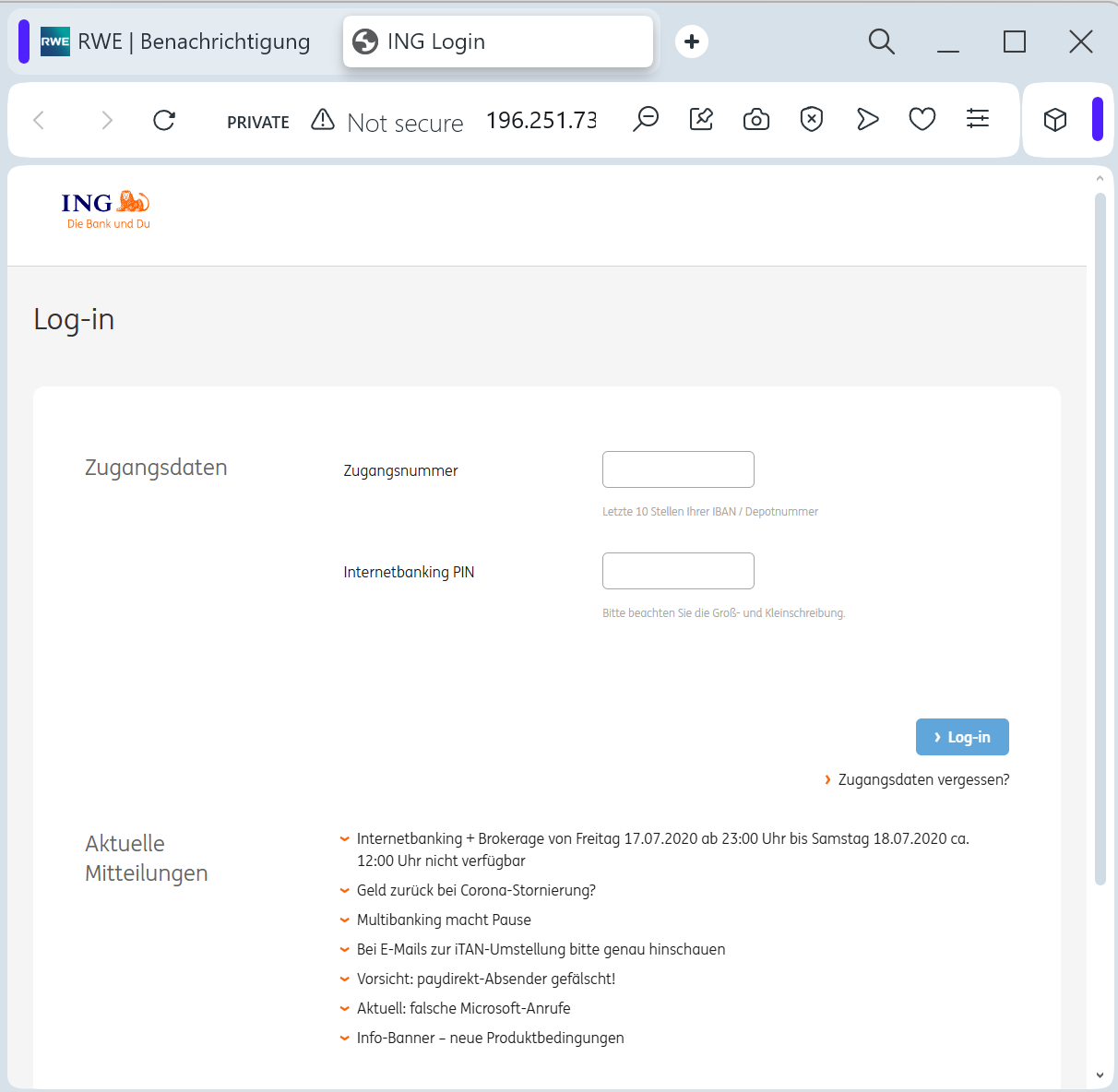
The link leads to a sophisticated fake page that mimics the RWE “Meine RWE” customer portal. To “receive the refund,” the victim is prompted to:
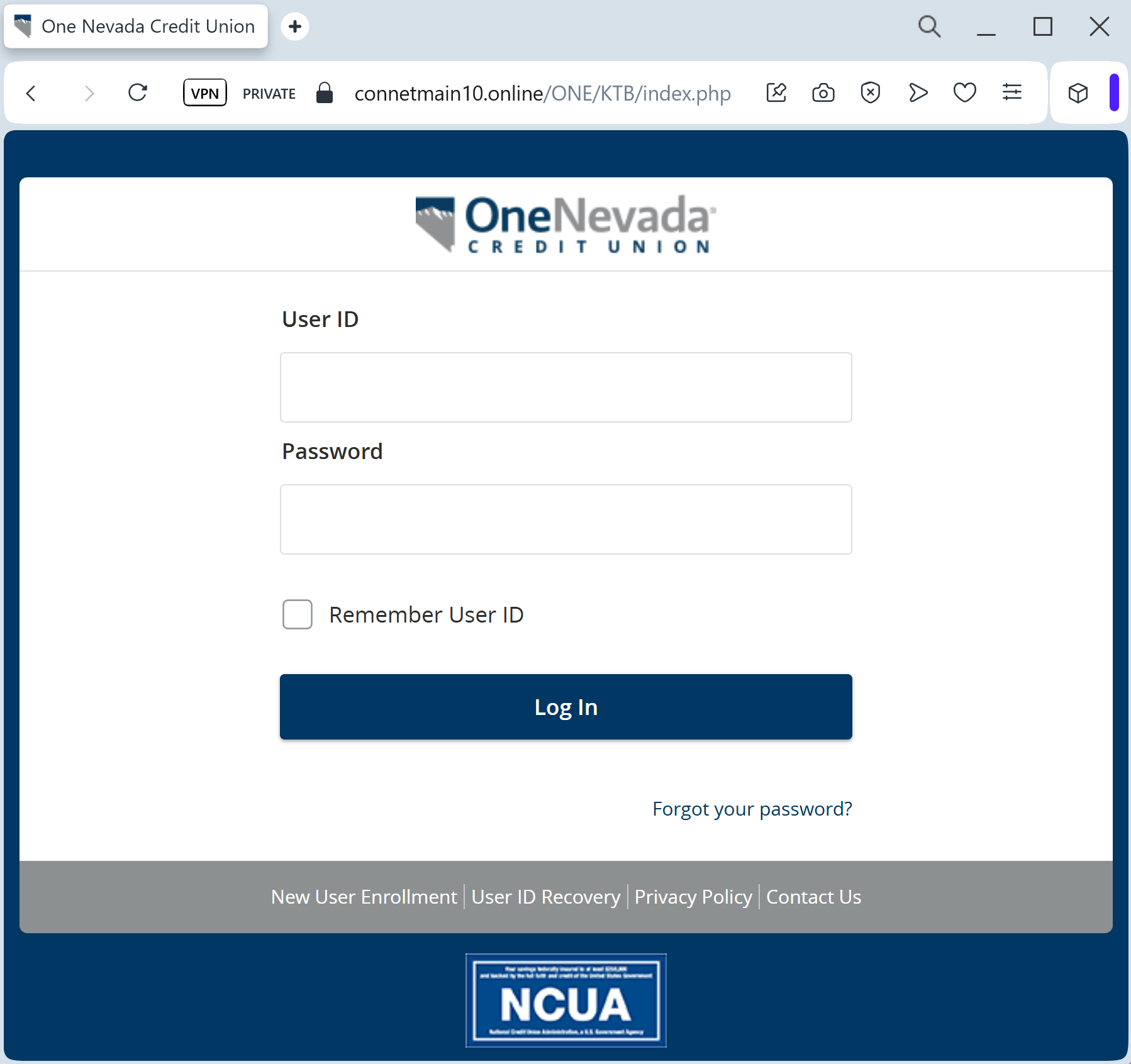
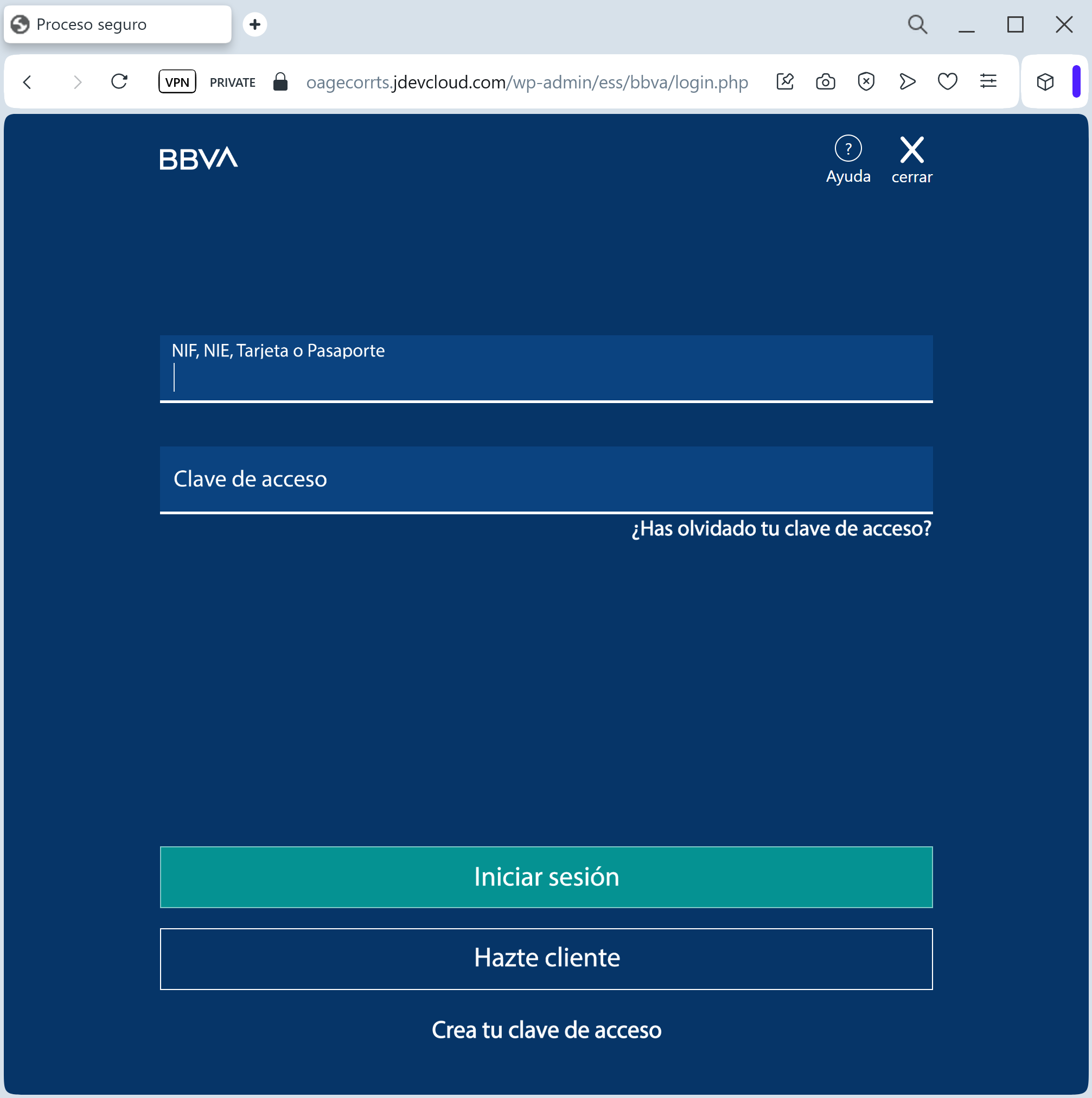
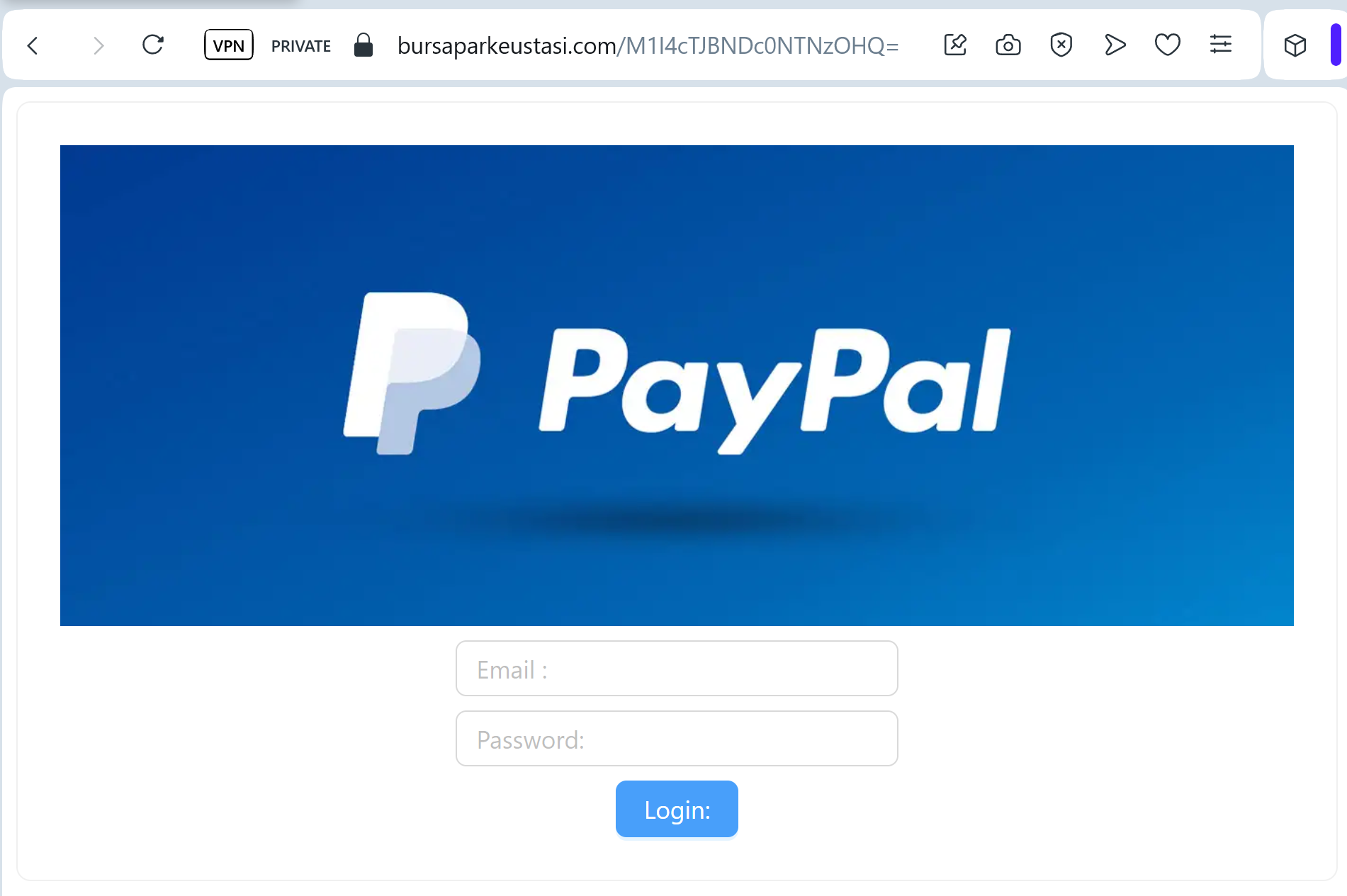
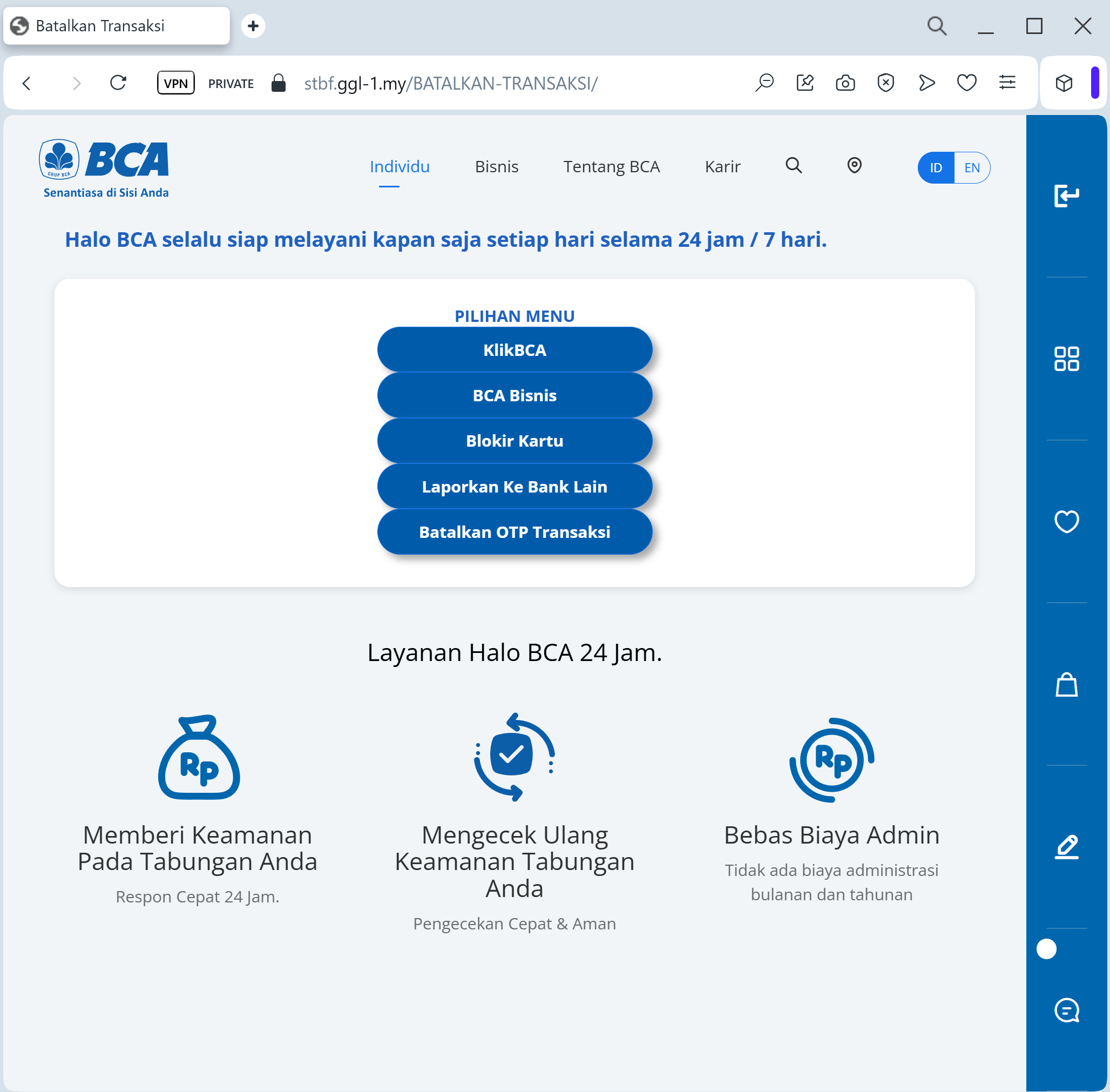
Select their Bank (using a multi-bank gateway menu)
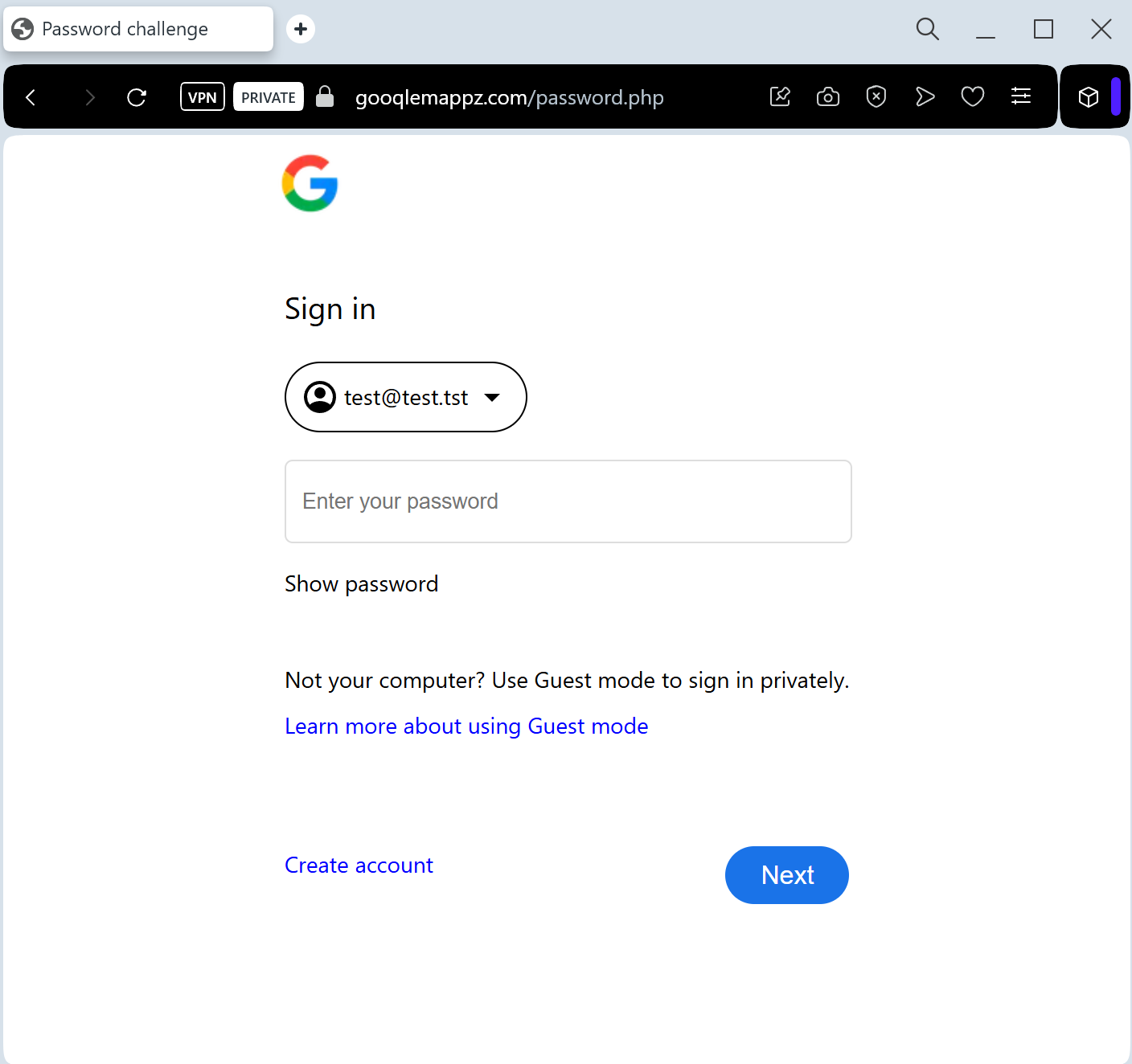
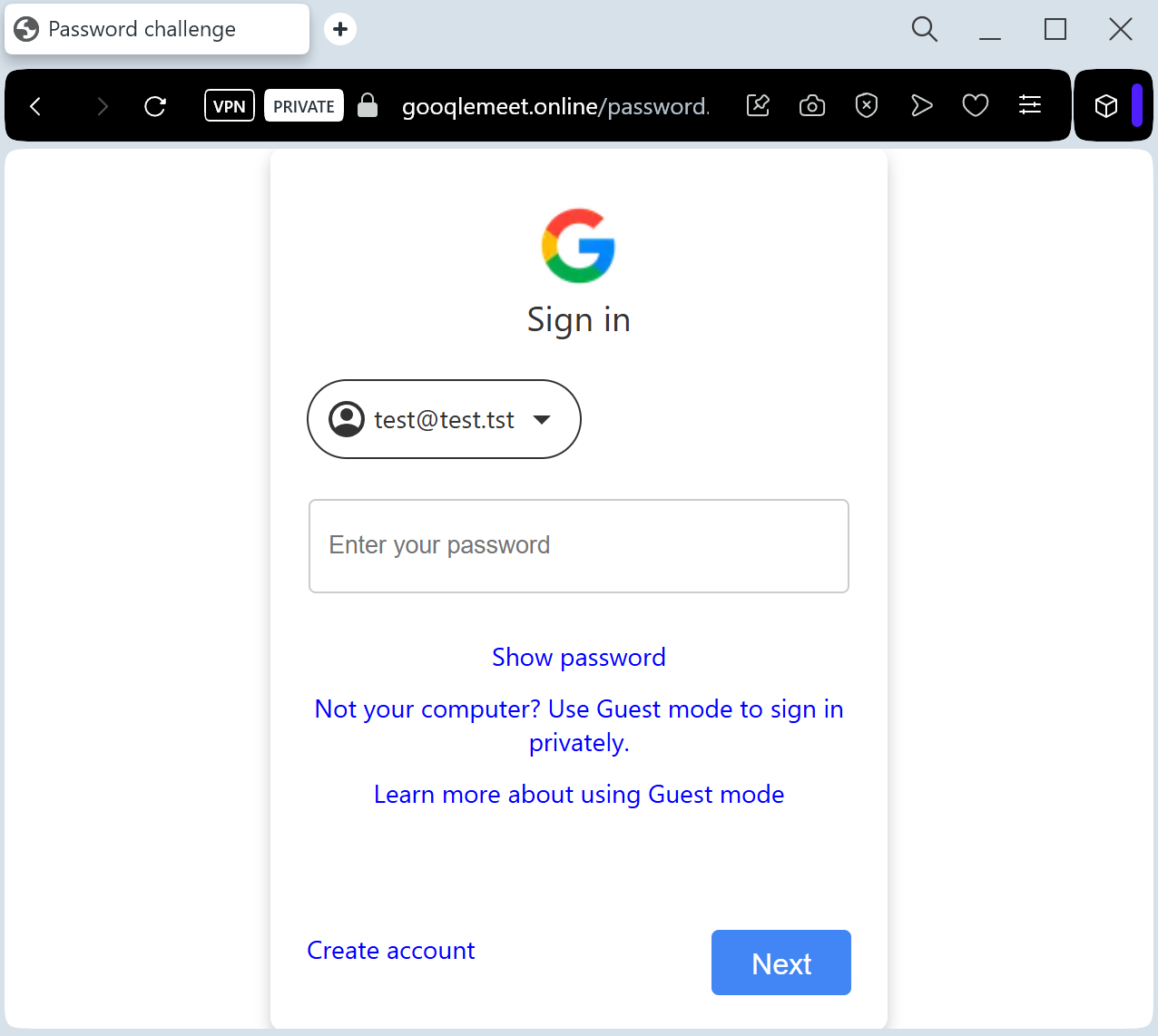
Enter Online Banking Login Credentials (PIN and Username/ID)
Provide a TAN/OTP Code: The fake site intercepts the authorization code in real-time, allowing attackers to authorize fraudulent outgoing transfers instead of depositing a refund.
⚠️ Red Flags to Watch For
Deceptive Domain: The official domain is rwe.com. Phishing sites use lookalikes such as rwe-erstattung.online, energie-guthaben.net, rwe-kundenportal.com, or compromised third-party URLs.
The “Refund” Hook: Energy companies usually settle refunds by crediting them toward your next bill or automatically transferring them to the IBAN already on file. They never send links asking you to log in to your bank to “receive” money.
Generic Communication: While the page looks professional, the initial email often lacks your specific customer contract number (Vertragskontonummer).
🛡️ How to Protect Yourself
Check Your Bill: If you are expecting a refund, check your last physical or digital bill. If there is a credit, it will be clearly stated there.
The “No Bank Login” Rule: Never log into your bank via a link provided in a utility email. If RWE needs your bank details, they will ask you to update them securely within their official portal that you access manually.
Verify the Sender: Check the sender’s email address. Official RWE communications come from @rwe.com. Be wary of addresses that look “similar” but are slightly off (e.g., @rwe-service.de).
Direct Access: Always type ://rwe.com manually into your browser to access the “Meine RWE” area.
💡 Expert Security Tip:
This is a Payment Gateway Scam. By asking you to “select your bank,” scammers are not trying to send you money—they are trying to gain access to your bank account. Real utility companies already have your bank details if you pay by SEPA direct debit. They will never ask you to “log in to your bank” to process a refund.