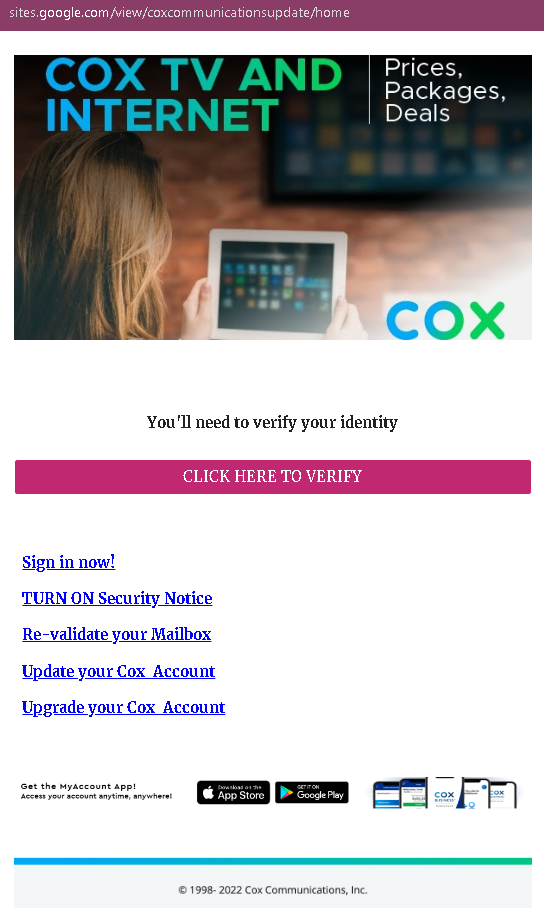
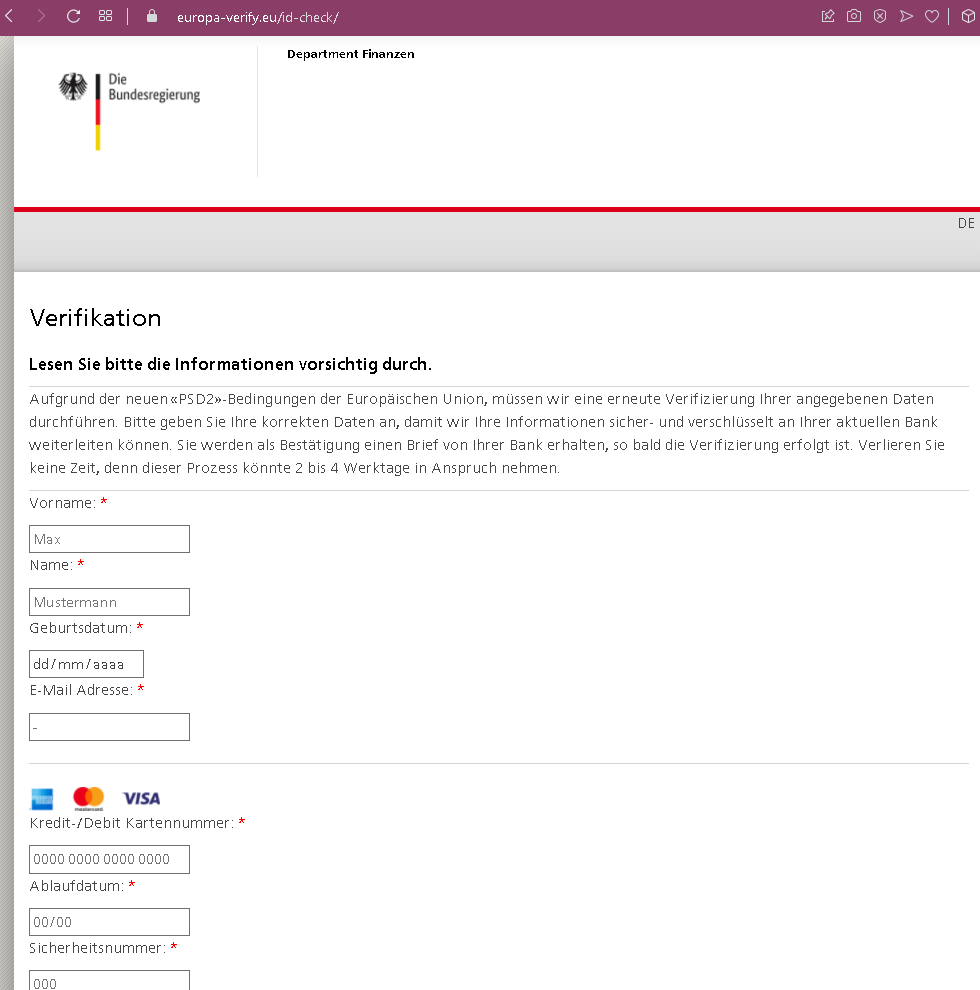
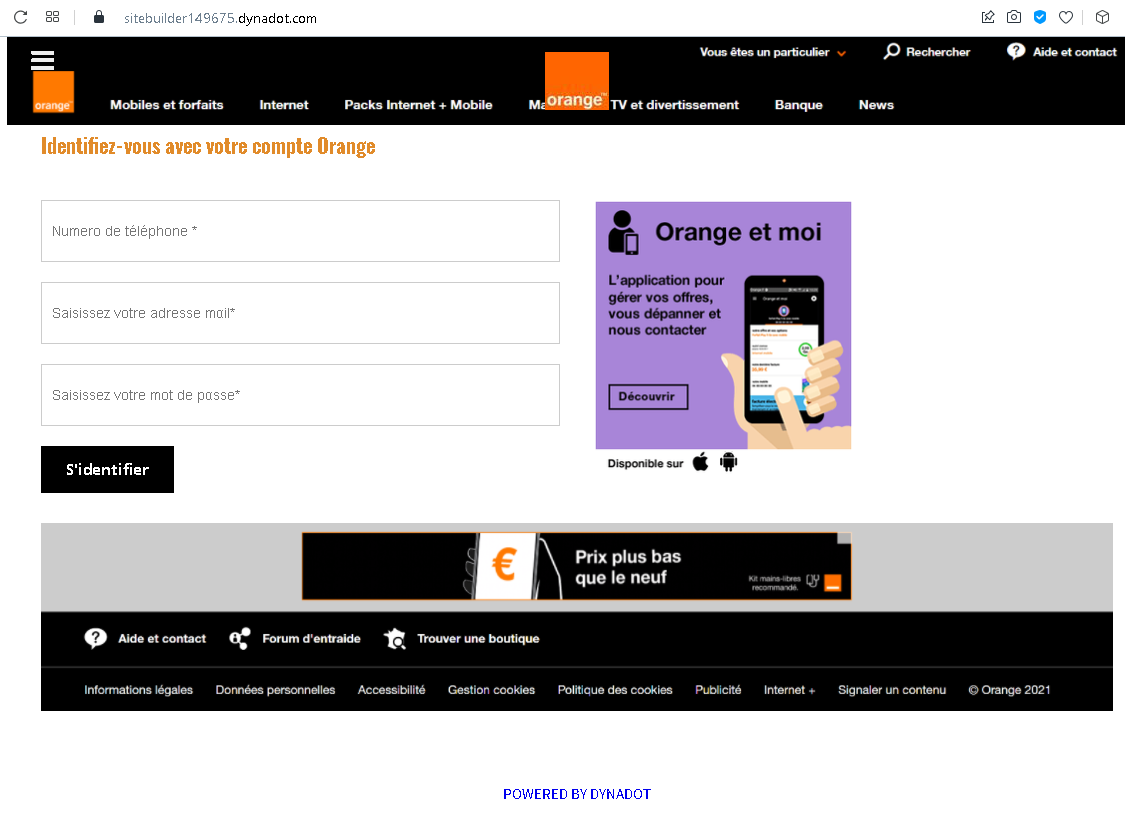
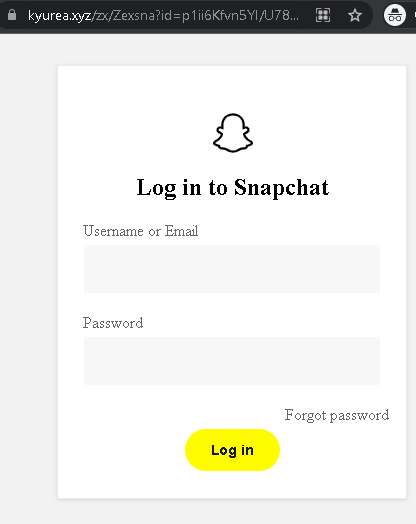
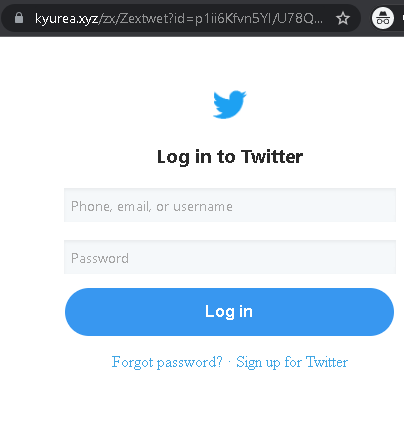
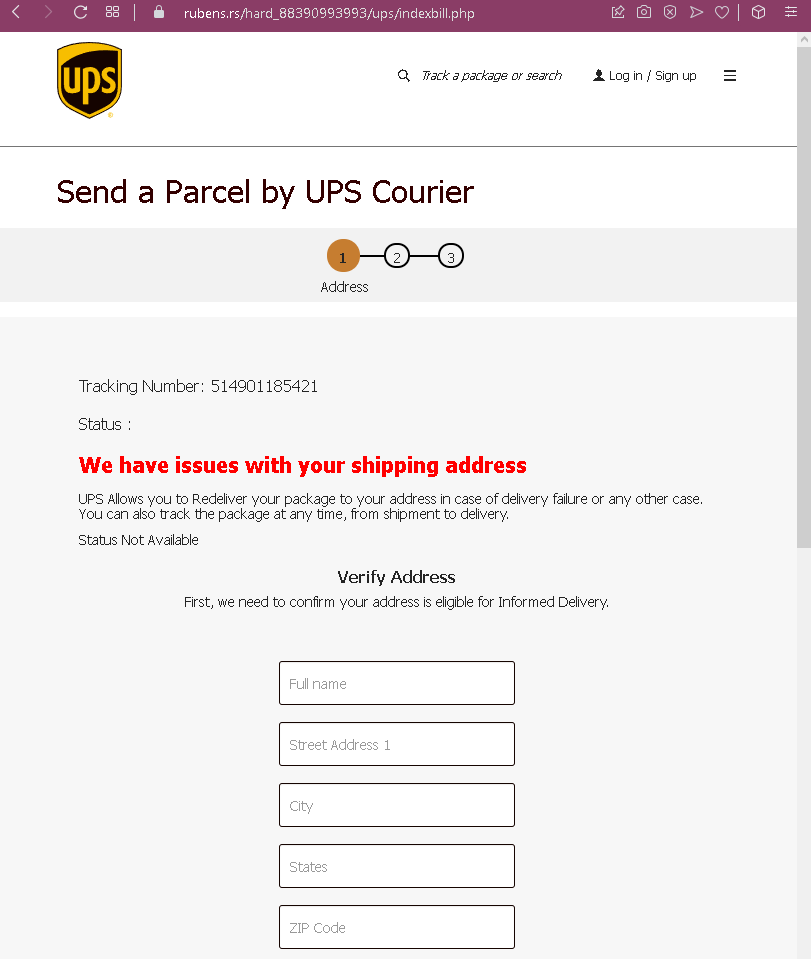
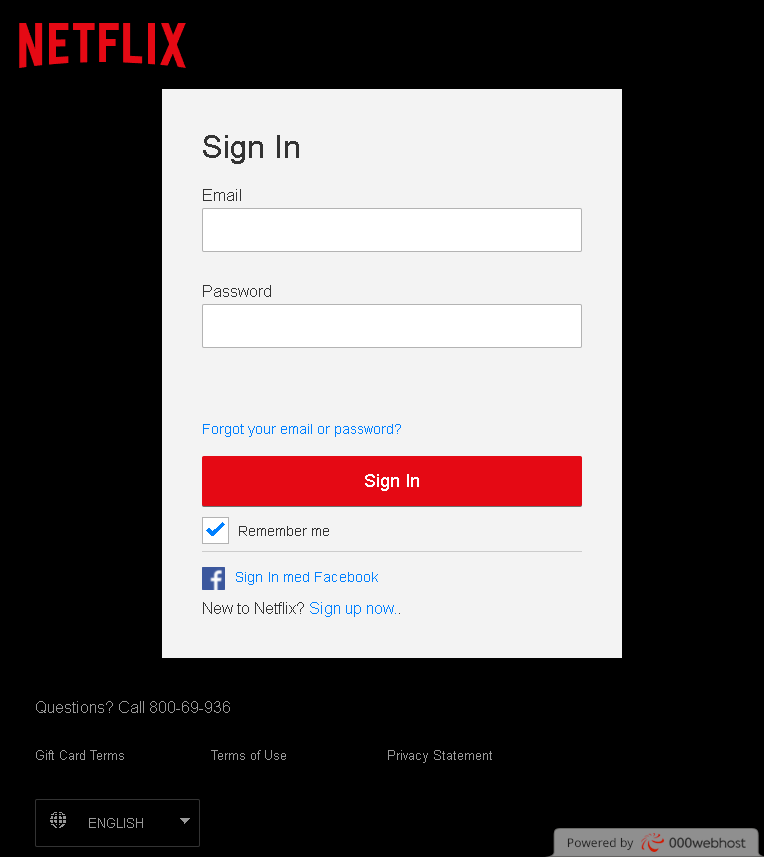
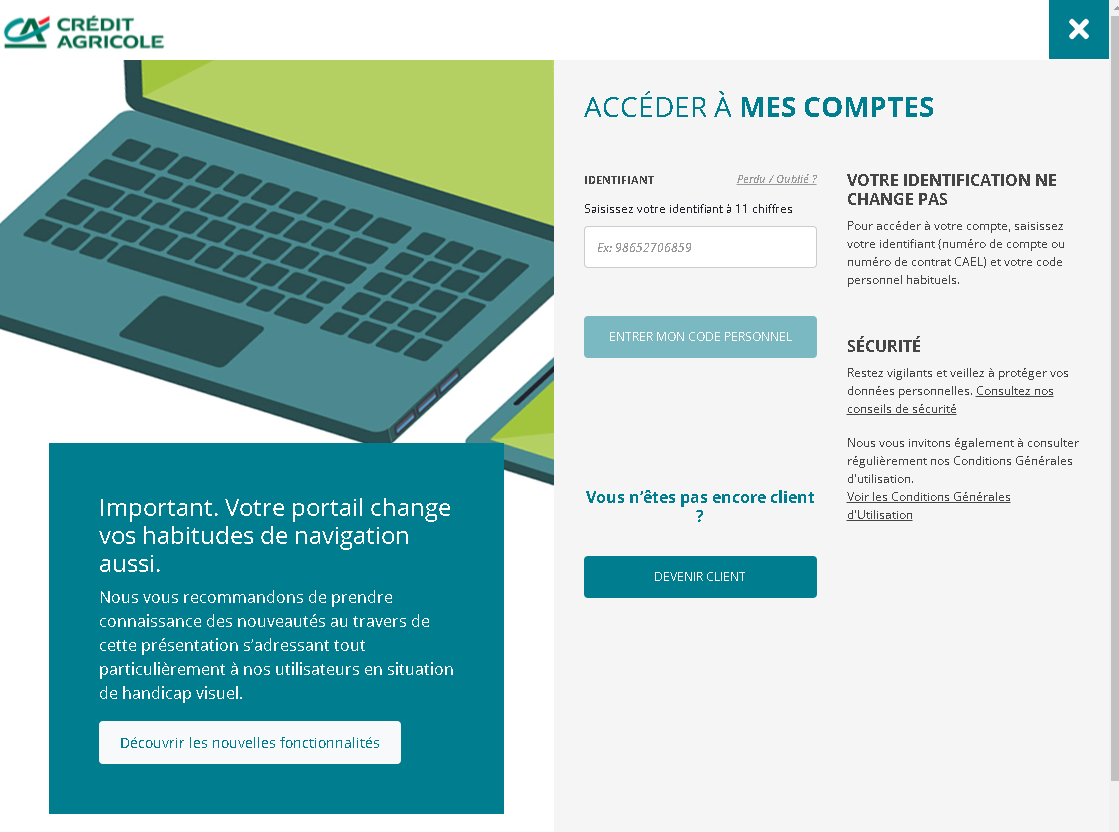
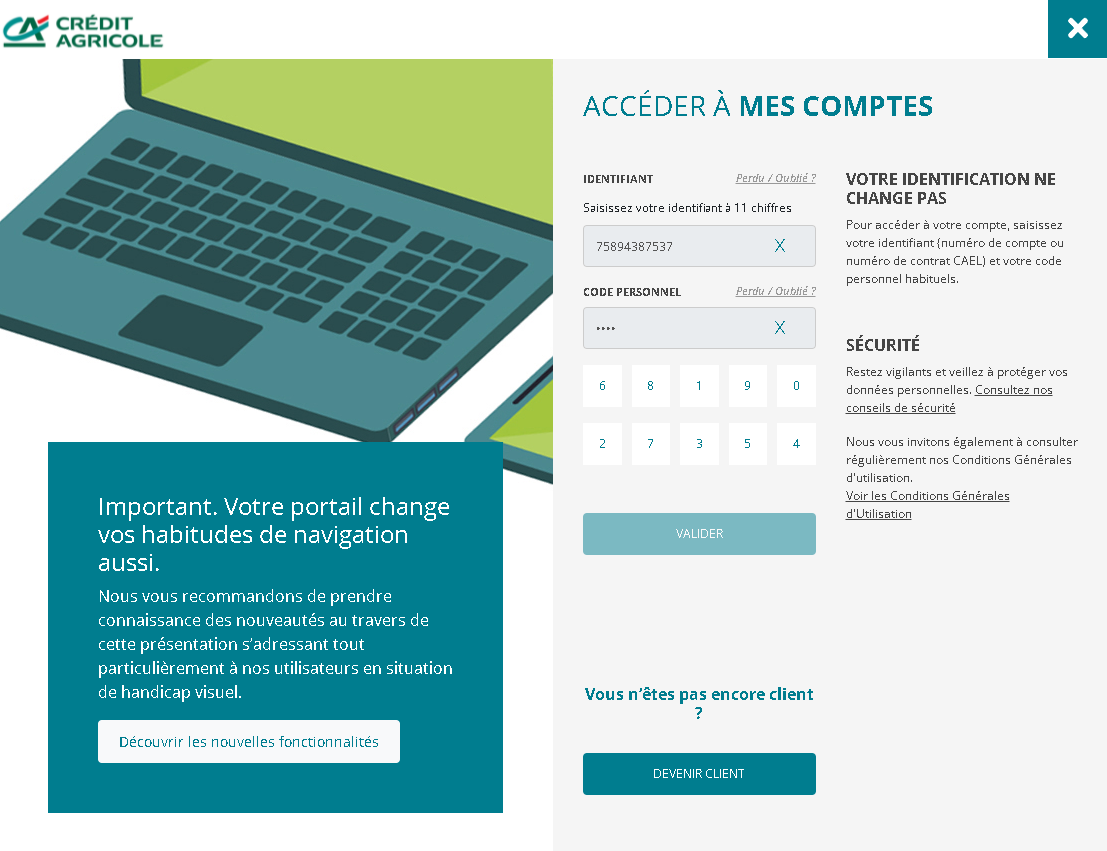
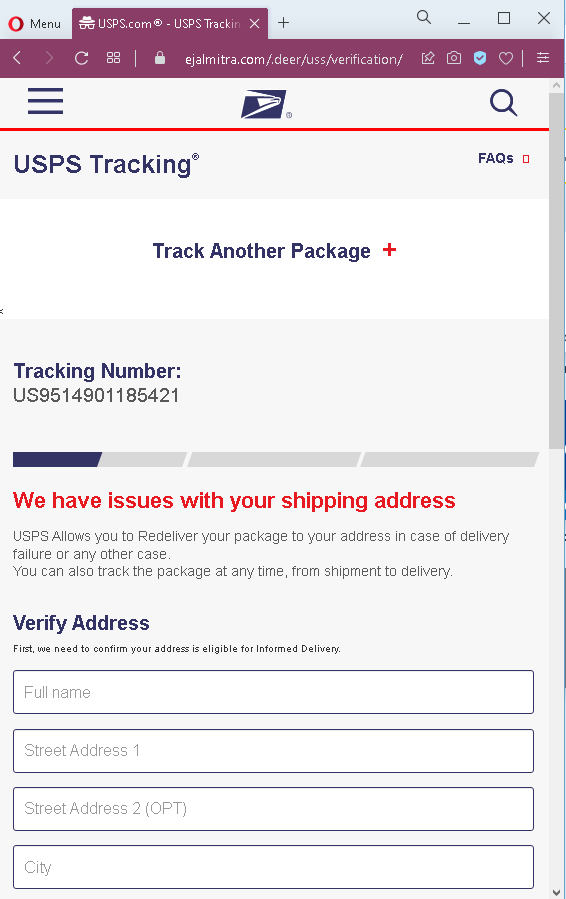
The fake USPS tracking case is a logistics impersonation attack that utilizes smishing to steal credit card data under the guise of an “incomplete address” or small fee. Victims are directed to a cloned website that captures personal, shipping, and banking details to be used for identity theft or sold on the dark web. The official USPS domain is usps.com, and any SMS link requesting payment is a scam, as official notifications do not contain such links.
Threat Intel: This malicious interface was intercepted, verified, and locked down firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the hostile origin link has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users detect replica fraud techniques before financial damage occurs.
Cybersecurity Measures: How to Avoid USPS “Delivery Failure” Phishing
To protect your credit card details and personal information from package delivery scams, follow these essential safety rules:
1. The “Redelivery Fee” Red Flag
Phishing sites almost always claim that a small fee (e.g., $0.30 or $1.99) is required to “redeliver” a package due to an “incomplete address.”
- Action: USPS does not charge redelivery fees via text message links. If a site asks for your CVV code (the 3 digits on the back of your card) to pay a tiny fee for a parcel, it is 100% a scam designed to steal your full card data.
2. Verify the Official Domain (The URL Rule)
Scammers use lookalike URLs that mimic the official USPS tracking page (e.g., usps-delivery-update.com, track-usps-package.net, redeliver-usps.xyz).
- Action: The only official website for the United States Postal Service is ://
usps.com. Before entering any information, ensure the address bar shows exactly this domain. Any other variations are fraudulent.
3. Ignore “Address Verification” SMS Links
Scammers send “Smishing” (SMS phishing) messages claiming: “The USPS package has arrived at the warehouse but cannot be delivered due to incomplete address information.”
- Action: USPS never sends unsolicited text messages with clickable links. If you receive a text about a package you didn’t expect (or even one you did), do not click the link.
4. Use the Official USPS Tracking Tool
If you are actually expecting a package, the safest way to check its status is directly through official channels.
- Action: Go to ://
usps.commanually and type your tracking number into the search bar, or use the official USPS Mobile app. If there is a real address issue, it will be flagged there without requiring a credit card.
5. Look for “Generic” Urgent Language
Phishing messages use high-pressure tactics to bypass your critical thinking (e.g., “Action required within 12 hours” or “Package will be returned to sender”).
- Action: Take a breath and look at the sender’s phone number. If it’s a standard 10-digit number (often with a non-US area code) or an email from a random domain (like @
gmail.comor @outlook.com), it is a fraud.
6. Report the Scam
By reporting these messages, you help telecommunications companies block these numbers for everyone.
- Action: In the USA, you can forward suspicious SMS messages to 7726 (SPAM). You can also report USPS-themed phishing to
uspis.gov(U.S. Postal Inspection Service).