This phishing campaign uses “Free $750 PayPal Gift Cards” via social media and pop-ups to lure victims, characterizing a classic survey scam designed to harvest personal data and distribute malware. Victims are induced through a fake, high-value reward offer, ultimately leading to data theft through “verification” steps that require inputting sensitive information or downloading malicious applications. You can read the full case analysis at antiphishing.biz.
Threat Intel: This deceptive layout was logged, cross-checked, and neutralized firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the dangerous destination URL has been completely disabled within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
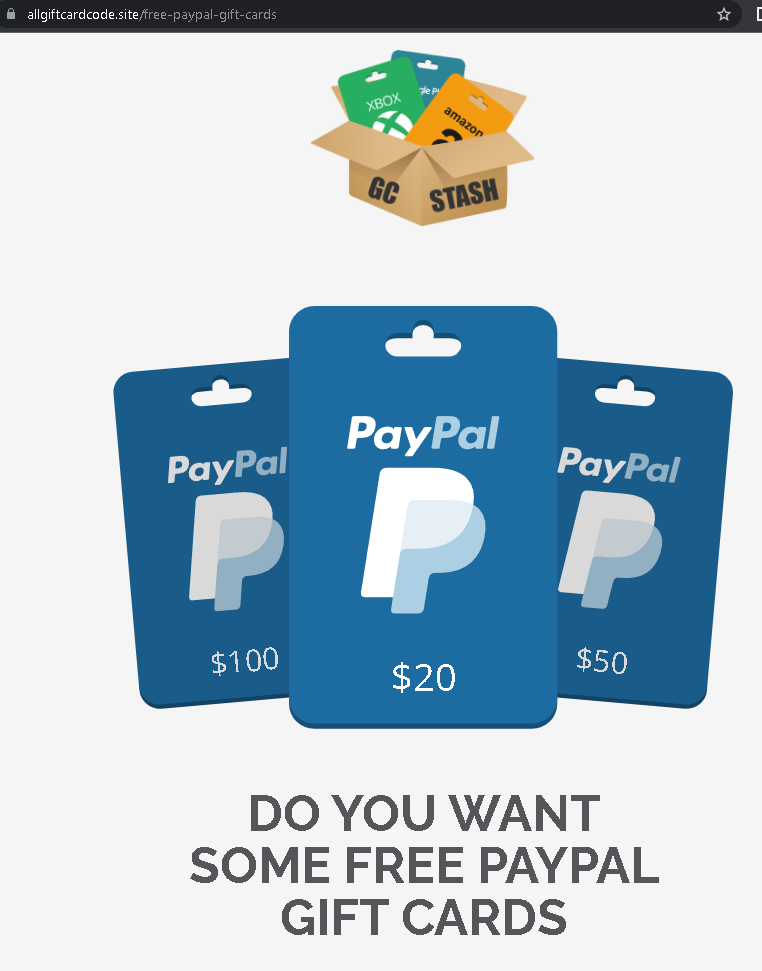
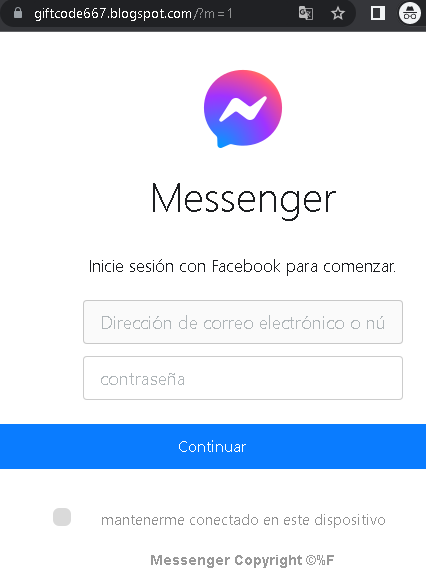
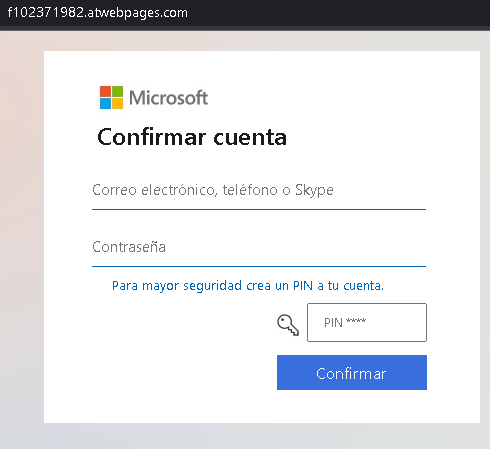
Screenshot #1: The Landing Page (The Hook)
The Trap: Displays a professional-looking “PayPal Gift Card” with high-value amounts. It uses official logos and colors to build trust.
The Psychology: “Free money” triggers an impulsive reaction. The user is asked to click a button to “Claim” or “Win,” which begins the redirection to the malicious forms.
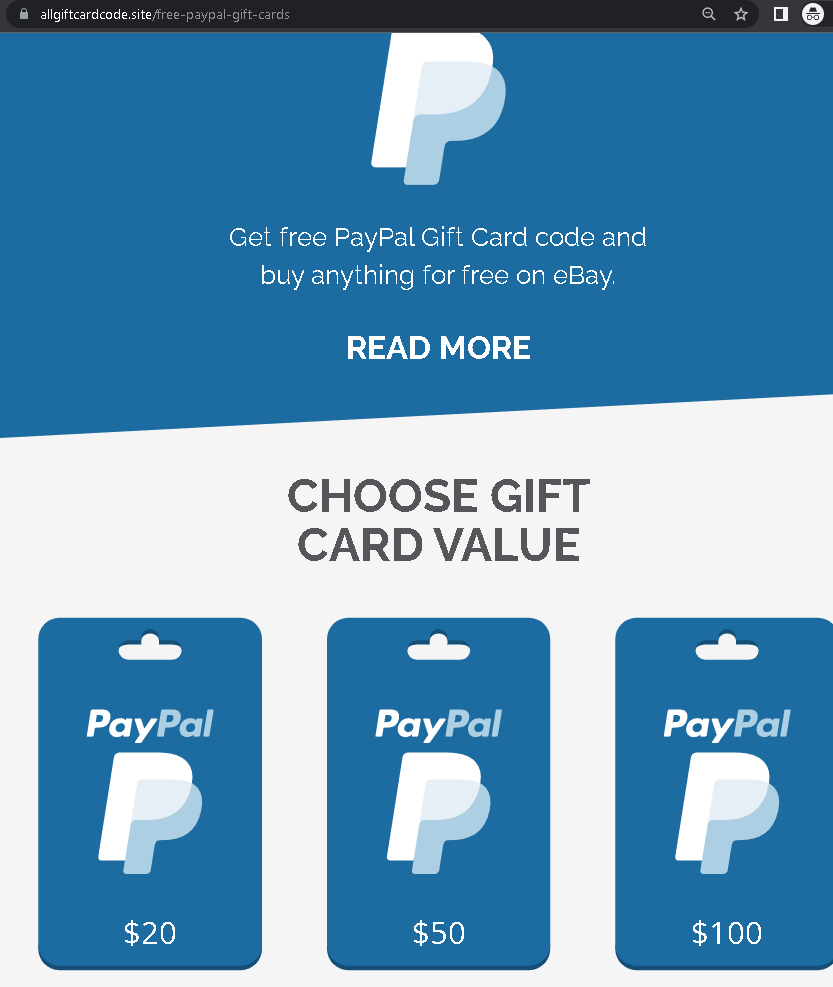
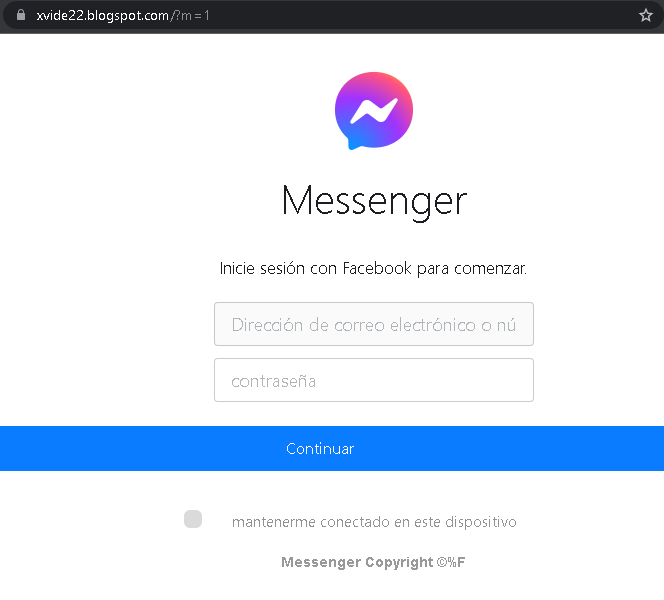
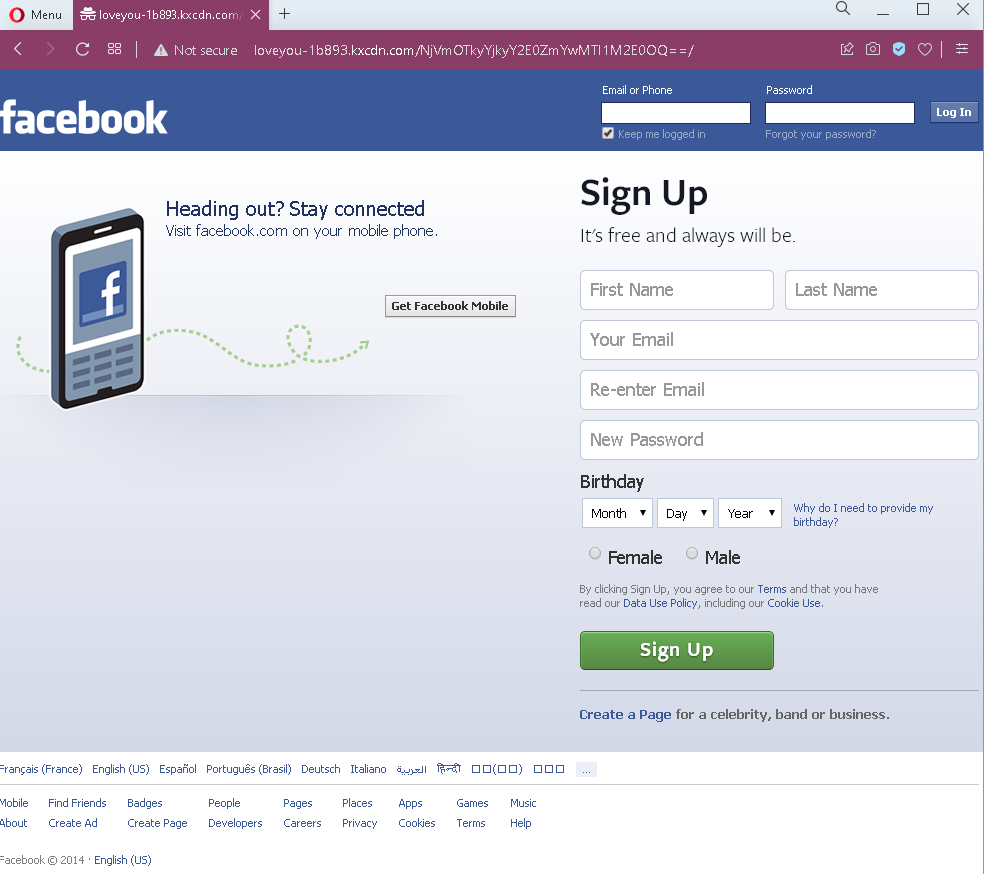
Screenshot #2: The Fake Survey / Verification
The Trap: The site asks simple questions like “How often do you use PayPal?” or “Which brand do you prefer?”
The Intent: This is a “Low-Friction” tactic. By making the user perform small tasks, the scammer builds “investment” and commitment, making the victim more likely to provide sensitive data in the next step.
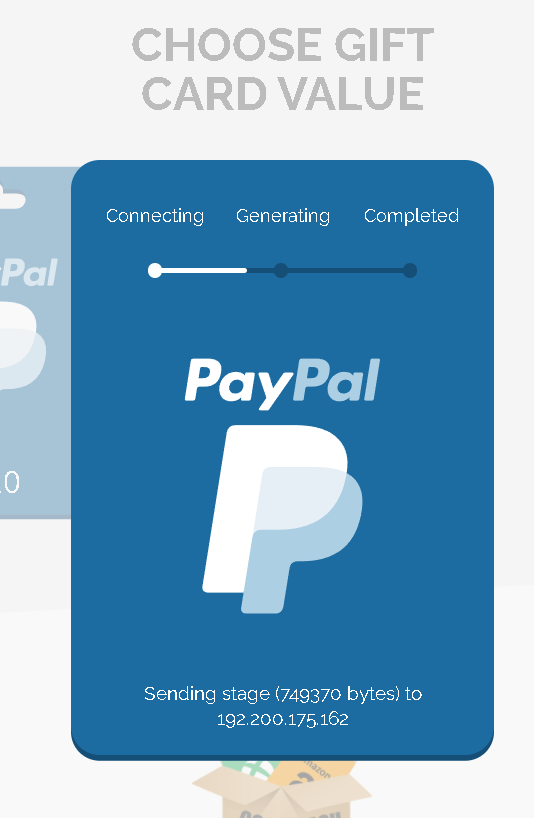
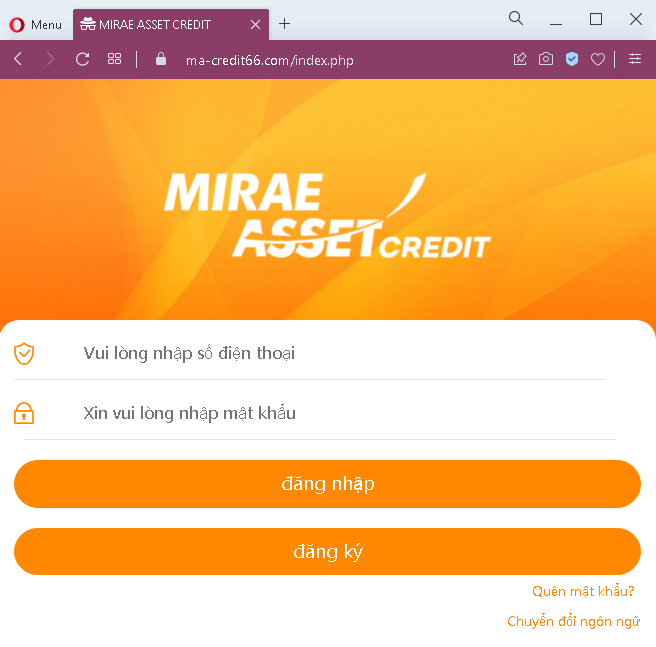
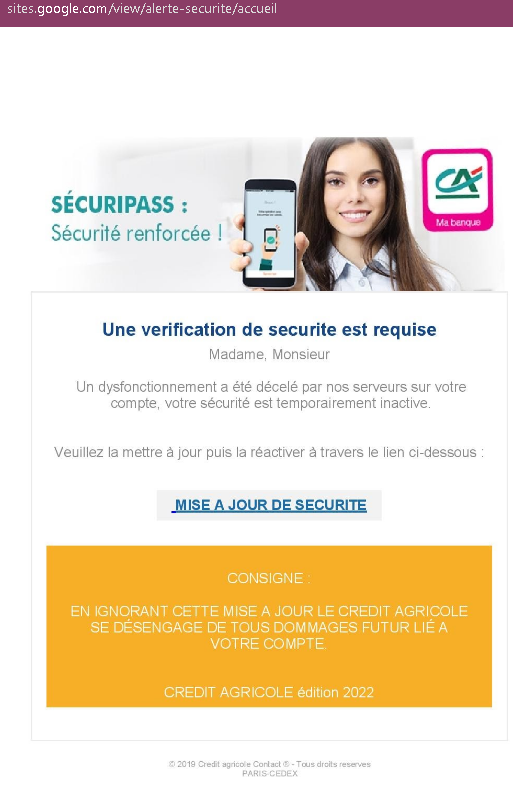
Screenshot #3: Personal Data Harvesting (Fullz)
The Trap: To “receive the gift card,” the user is asked for their Full Name, Home Address, and Date of Birth.
The Impact: This information is sold on the Dark Web as “Fullz” (full identity profiles). It allows criminals to bypass security questions on other accounts or commit identity theft.
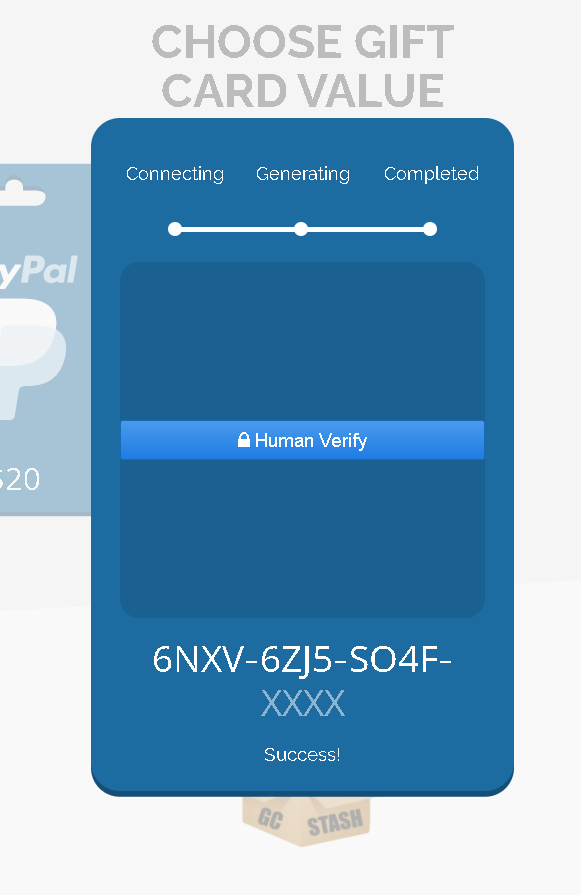
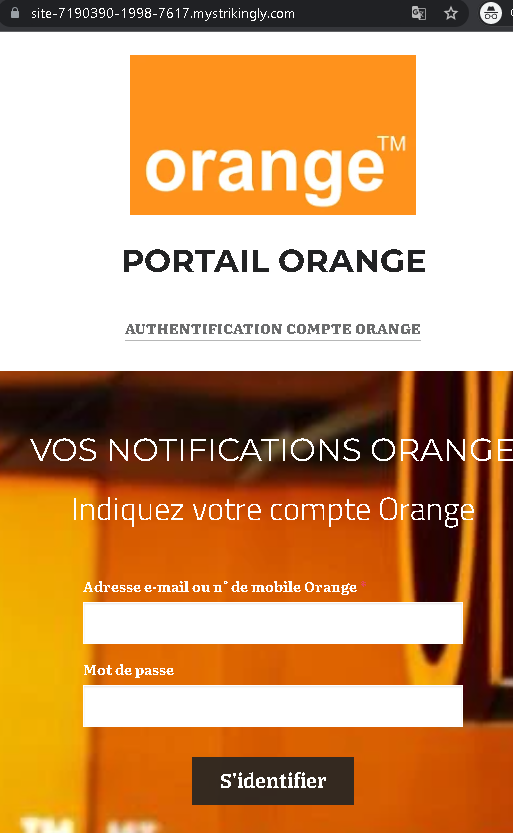
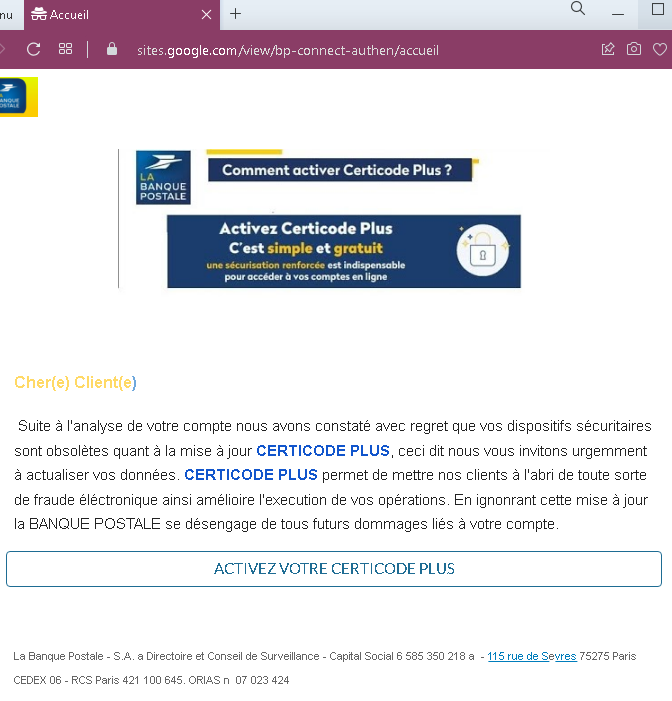
Screenshot #4: The Payment / Shipping Fee Form (The Kill)
The Trap: The final step claims a small “Processing Fee” or “Shipping Charge” ($1.00 – $2.00) is required to send the gift card.
The Impact: This form is a Credit Card Skimmer. Once you enter your Card Number, Expiry, and CVV, the attacker has full access to your funds. The “gift card” never arrives, but the fraudulent charges start immediately.
Here is the detailed breakdown of the Fake PayPal Gift Card scam . This is a classic “Reward Bait” scheme used to harvest financial data and personal information.
Fake “Free PayPal Gift Cards” Scam
Target: Global PayPal users looking for discounts or rewards.
Threat Level: High (Financial Fraud & Identity Theft)
Phishing Method Description
This attack uses Social Engineering by promising a “Free $750 PayPal Gift Card” or similar high-value rewards. These scams are often spread via social media ads, WhatsApp messages, or “reward” websites. The goal is to lead the victim through a series of “verification steps” that eventually steal their credit card data and account credentials.
Protection Measures (Safety Rules)
- 1. The “Too Good to Be True” Rule:
PayPal (and other major companies) does not give away $500 or $750 gift cards for free via third-party websites or surveys. If the offer seems excessive, it is 100% a scam. - 2. Check the Domain (URL):
Official PayPal offers only exist on ://paypal.com. Any other domain (e.g.,paypal-rewards-2024.net,win-paypal-gift.xyz) is a phishing site. - 3. Never Pay to Receive a Prize:
A legitimate prize or gift card should never require you to provide your credit card’s CVV code or pay a “verification fee.” This is the primary red flag for financial skimming. - 4. Official Communication Only:
Check your official PayPal app or log in directly topaypal.com. If there is a real reward, it will be listed in your Rewards or Offers section inside your secure account.