Who This Guide Is For
This is for you – the Tise seller who uses the app to clear out your wardrobe, make some extra cash, or run a small second-hand business. You are not a cybersecurity expert, and you should not have to be one just to sell a pair of jeans online.
Tise is a beloved platform, especially in Norway and the rest of the Nordics. It calls itself the largest community for buying and reselling second-hand fashion in the region, with millions of users across Norway, Sweden, Denmark, and Finland. And last year, the global giant eBay saw how special this community is, acquiring Tise to help it grow even further. It is a great place. But as the community gets bigger, the people who want to take advantage of it get smarter.
This guide will show you exactly how a new, highly convincing scam works. We will walk through every step the criminals take, from the first message in your chat inbox to the fake page that tries to steal your card details. We will look at the tricks they use to make you panic, the small details they copy to make their fake page look real, and – most importantly – the simple, everyday habits that will protect your money forever.
The Story Of A Scam That Almost Worked
Let me tell you what happens to a Tise seller when they become the target of this attack. You will recognise the sequence immediately, because it is designed to look just like a normal sale.
Act One: The “Interested Buyer”
It all starts with a message inside your Tise chat. A person expresses interest in an item you have listed. They seem genuine. They ask a normal question. You feel good – a sale might be coming.
Then, suddenly, they claim to have made the payment. They say they have sent the money. But there is a problem. To “receive the funds” or “confirm the sale”, you need to click a short link they provide. They might even sound helpful or a little urgent, saying something like, “Just click this link to complete the transaction on your end.”
This is the hook. The scammer knows that you are excited about the sale. You want it to go smoothly. And because the message comes from inside the Tise chat – where all your legitimate conversations happen – your guard is already down.
In many cases, the link is sent through a shortener or an intermediate web address. This is a deliberate tactic. The criminals use these extra steps to hide the real destination from automated security scanners, making it harder for anyone to flag the link as dangerous before it reaches you.
Act Two: The Page That Looks Just Like Home
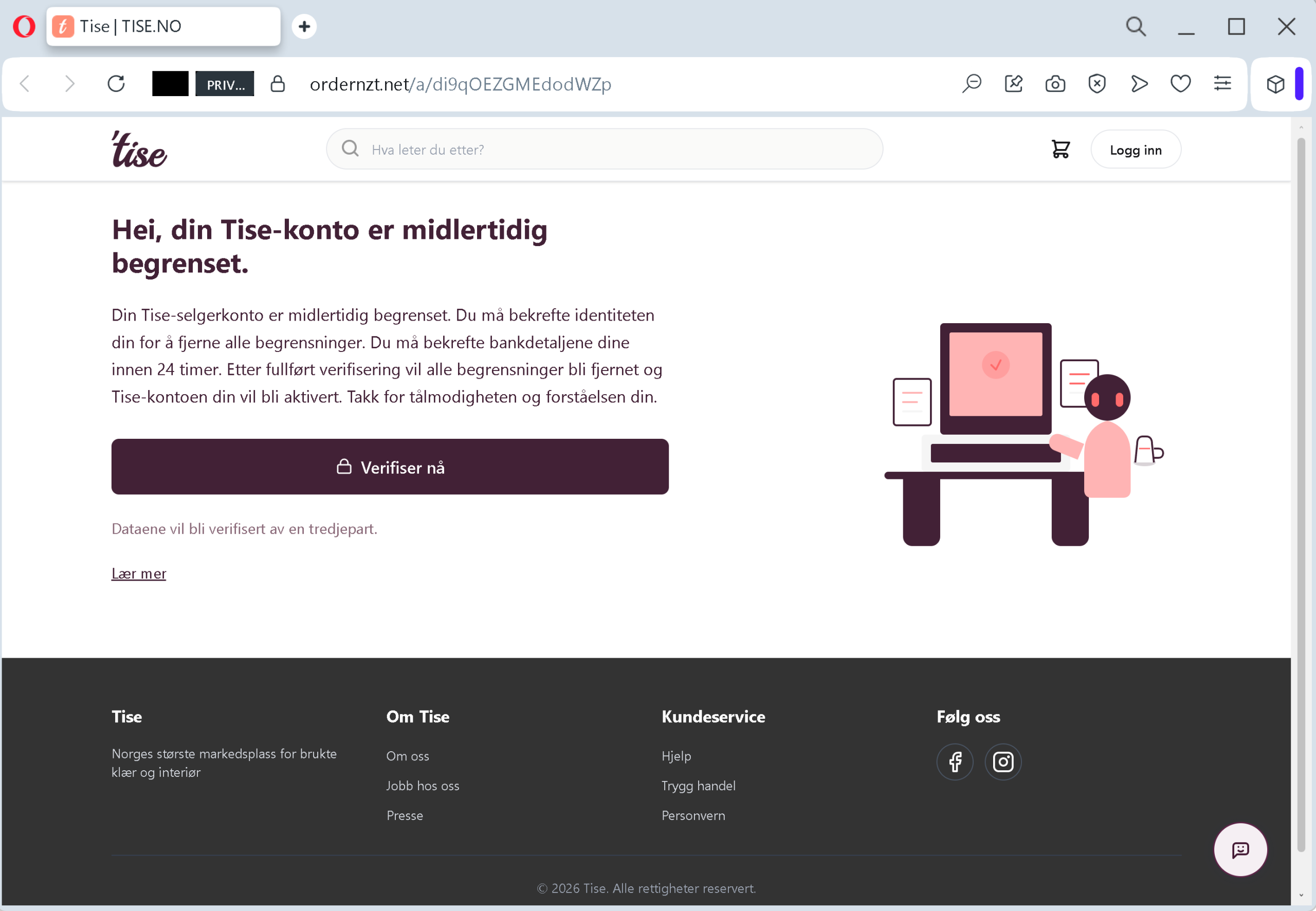
When you click the link, you are not taken to Tise. You are taken to a page that is designed to look exactly like Tise.
The criminals have built a perfect visual copy. The layout uses the same typography, the same logo formatting, the same search bar placement, and the same corporate color palette as the real Tise. They even use flawless Norwegian text. If you are a local seller, this page speaks your language with complete accuracy.
This is not a coincidence. This is brand impersonation. The goal is to make you feel comfortable and familiar, so you do not question where you really are.
Act Three: The 24-Hour Lockdown Message
At the top of this fake page, you see a headline that stops you cold: “Hei, din Tise-konto er midlertidig begrenset” – “Hi, your Tise account is temporarily restricted.”
The message below explains that your seller account has been locked. It says you have a strict deadline – within 24 hours – to confirm your identity and your bank details. If you do not act, you will lose access to your account.
This is the panic trigger. The thought of your account being locked, especially right when you are trying to complete a sale, creates instant anxiety. Your brain shifts into problem-solving mode. The urgency pushes you to act fast, without double-checking anything.
And right there, on the page, is a large, inviting button that reads “Verifiser nå” – “Verify now”.
Act Four: The Form That Takes Everything
You click the button. A new page opens. It asks for your full credit card number, expiration date, CVV code, and your BankID codes.
Let me be extremely clear: This is not a verification. This is a harvest.
With these four pieces of information, the criminals do not need to guess anything. They can drain your bank account immediately. They can initiate unauthorized wire transfers without any further input from you. They can sell your complete financial profile – your name, your card number, your security codes – on underground marketplaces where other criminals buy them in bulk.
And here is the part that should make you angry, not scared: A legitimate marketplace never demands that a seller enter full credit card details to receive money for a sold item. Payments on Tise are handled through pre-linked bank accounts. You set up your payment method once. You do not re-enter your card information every time someone buys something from you.
The Three Dirty Tricks That Make This Scam So Dangerous
The criminals behind this operation are not guessing. They have studied how real people think and behave online. They have built their attack around three psychological tricks that are almost impossible to resist unless you know what to look for.
Trick One: They Start Inside The Trust Zone
The initial message arrives in your official Tise chat inbox. That is the most trusted place on the platform. You have had dozens of real conversations there. Your brain has learned to associate that inbox with safety and legitimacy.
By starting the attack there, the scammer bypasses your first line of defense. You do not question the message because it is sitting right next to all your other real conversations. This is a deliberate choice. They are hiding in plain sight.
Trick Two: They Create A Manufactured Emergency
The 24-hour lockdown notice is pure panic fuel. When people are afraid of losing their account – and the money that comes with it – they stop thinking clearly. They stop checking URLs. They stop asking smart questions. They just want to fix the problem as fast as possible.
Incident Report: This deceptive layout was logged, cross-checked, and neutralized firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the dangerous destination URL has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
The scammers are counting on that exact reaction. The deadline is fake. The lockdown does not exist. The only real emergency is the one they created inside your head.
Trick Three: They Steal Legitimacy From Real Brands
The fake page uses the exact same fonts, colors, and logos as the real Tise. It even copies the official language and tone. This is not an accident. The scammers know that your brain sees those familiar elements and relaxes. The brand has done the hard work of building trust over years. The criminal just steals that trust and uses it against you.
And in case you still have doubts, the page displays a title in your browser tab that says “Tise | TISE.NO”. That looks convincing. But the actual address in your browser’s address bar – the real URL – has nothing to do with Tise. It is a cheap, generic domain like the one identified in this attack, ordernzt.net
The One Rule That Will Save You Every Time
If you remember only one thing from this entire guide, make it this:
Never, ever click a payment or verification link sent to you by another user inside a marketplace chat.
No matter how official the message looks. No matter how urgent the warning seems. No matter how nicely the “buyer” asks.
Instead, do this simple, five-second habit:
Open a new tab in your browser. Manually type the real Tise website address – tise.comtise.no
If there is a genuine problem with your account, you will see a notification there. Right inside the official platform. If you see nothing – and you will see nothing – then the message you received was a scam. Close it, report it, and move on with your day.
That one habit – typing the official URL yourself instead of clicking a link – will shut down this entire attack before it even gets started.
Expert Tips: How To Stay One Step Ahead Of The Scammers
Here is the advice that security professionals share with their own families. Follow these rules, and you will become a very difficult target for criminals.
Turn on two-factor authentication (2FA) right now. This is your digital seatbelt. It means that even if someone steals your password, they cannot get into your account without a one-time code sent to your phone. Tise supports this. Go into your account settings and turn it on. It takes two minutes and adds a massive layer of protection.
Keep all conversations inside the Tise chat. The Tise Help Center explicitly warns users: if someone asks to move the conversation to another platform like Messenger, WhatsApp, or SMS, that is a major red flag. There is no legitimate reason to take a transaction outside Tise’s own system. Doing so is almost always an attempt to bypass the platform’s security controls.
Never click links sent by another user. This is Tise’s own advice, and it is golden. Links sent in chat messages are often attempts at phishing, where the person tries to obtain sensitive information such as card details. The link might look unusual or overly long, or it might pretend to belong to a legitimate service like a shipping company. If it is a link, do not touch it.
Check the address bar like a detective. Before you enter any personal information on a webpage, look at the browser’s address bar. Is the domain exactly tise.comtise.no.net.top.xyzAntiphishing.biz team noted that the fake page in this attack used the domain ordernzt.net
Understand how payments actually work. Tise handles payments through pre-linked bank accounts. You set up your payment method once. You do not re-enter your card details to receive money for a sale. If a page asks for your full credit card information, CVV, or BankID codes to “verify” you, you are looking at a scam. Legitimate marketplaces never demand this.
Be suspicious of urgency. Any message that says “act now or your account will be locked” or “you have 24 hours to verify” is almost certainly a scam. Real companies do not pressure you with ticking clocks. They give you time to respond through official channels.
Use a virtual card for online selling. Many banks and services (such as Revolut, Privacy.com, or others) offer virtual card numbers – temporary cards with spending limits. If you use a virtual card for your marketplace transactions, even if a scammer steals the number, they cannot exceed the limit you set. And you can cancel the virtual card instantly without affecting your main bank account.
What To Do If You Think You Have Been Targeted
Do not panic. But do not wait, either. Take these steps immediately.
Call your bank right now. Use the phone number on the back of your credit or debit card. Tell them that your card details may have been compromised in a phishing attack. Ask them to block the card and issue a new one. If any fraudulent charges have already appeared, report them immediately. The faster you act, the more likely you are to get your money back.
Review your recent transactions. Look for small test charges (often very small amounts like $0.00 or $1.00) as well as larger ones. Criminals sometimes test a card with a tiny transaction before making a big purchase. Report anything you do not recognise.
Change your Tise password. Even if the phishing page did not ask for your password, it is better to be safe. Choose a strong, unique password that you do not use on any other website.
Enable 2FA if you have not already. This will prevent anyone from taking over your Tise account, even if they manage to steal your login credentials later.
Report the phishing attempt to Tise. Use the in-app reporting tools to flag the user who sent you the suspicious message. The Tise Help Center has a simple way to do this. Your report could help protect other sellers from falling into the same trap.
Consider filing a police report. In some cases, especially if you have suffered a financial loss, contacting the police can be an important step.
A Final Word From The Security Team
The phishing attack described in this guide was intercepted, verified, and disabled by the Antiphishing.biz security team during their daily link moderation work. The dangerous domain no longer works. But new domains will appear tomorrow, and the week after, and the month after that.
The criminals behind these attacks are counting on one thing: that you will act before you think. They want you to click first and ask questions later. Do not give them that satisfaction.
Build a new habit today. When a message lands in your chat inbox claiming a payment has been made or your account is restricted, do not click. Do not panic. Do not follow the link. Open a fresh browser tab. Type tise.comtise.no
That extra thirty seconds will save you from a world of financial pain.
Stay safe out there. And if you found this guide helpful, share it with every seller you know. The more people understand this scam, the harder it becomes for criminals to profit.
