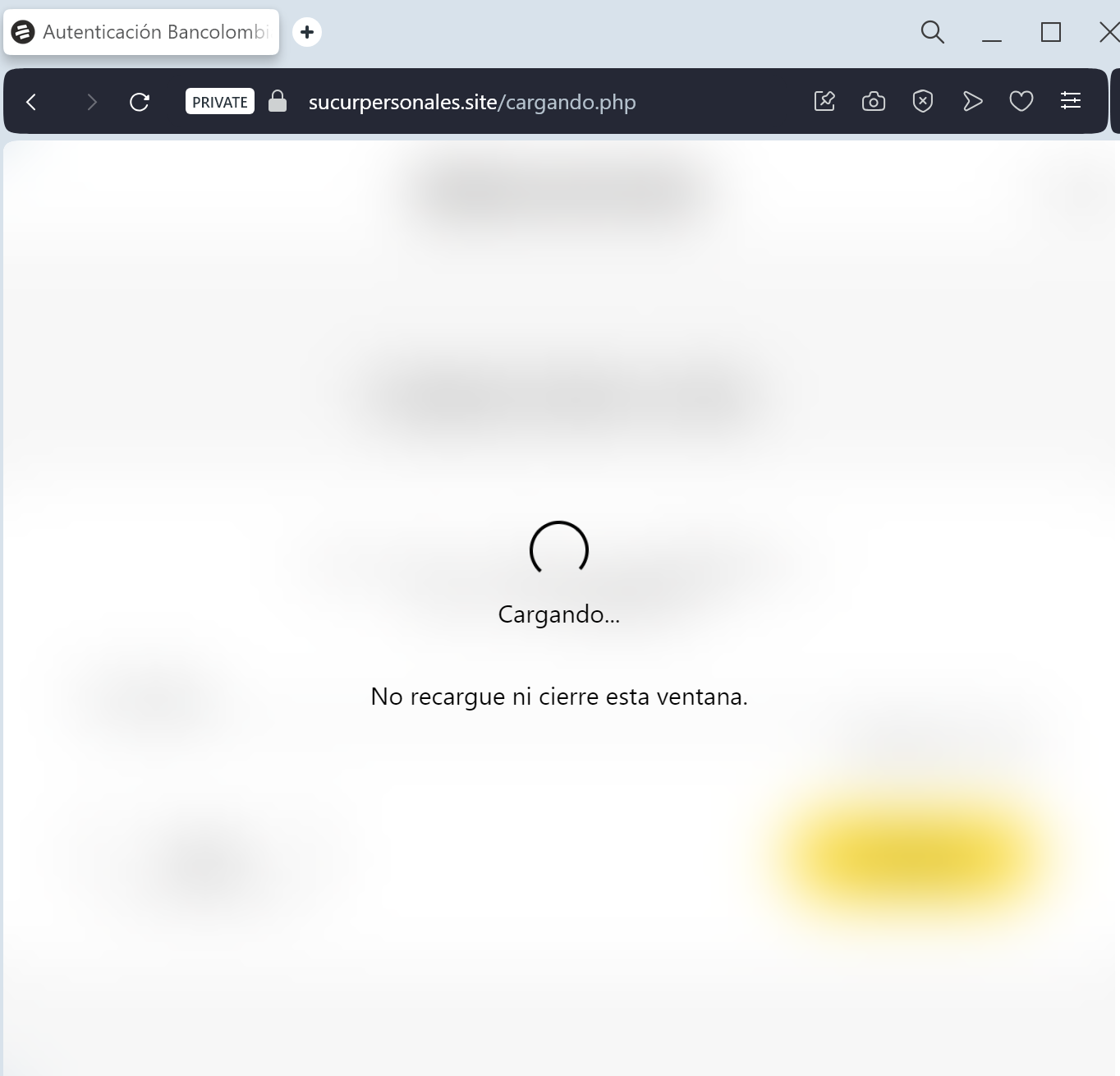
A phishing campaign targeting Bancolombia users employs fake “account blocked” alerts via SMS to steal credentials for the Bancolombia Personas mobile application, including usernames and real-time OTPs. The attack uses fraudulent websites to impersonate the bank’s login portal and pressures victims into entering sensitive information.
Security Notice: This malicious interface was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the hostile origin link has been fully defanged within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
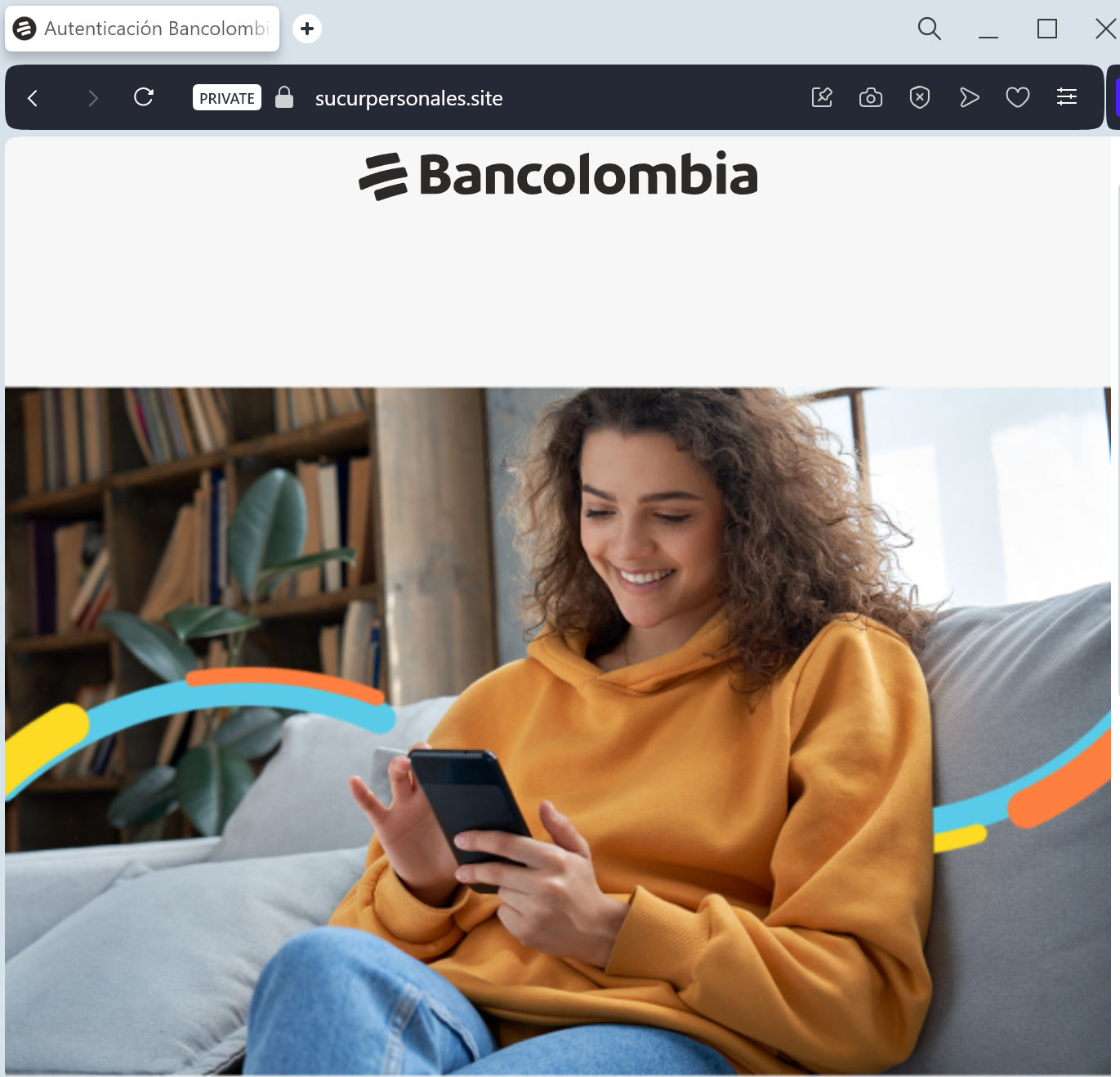
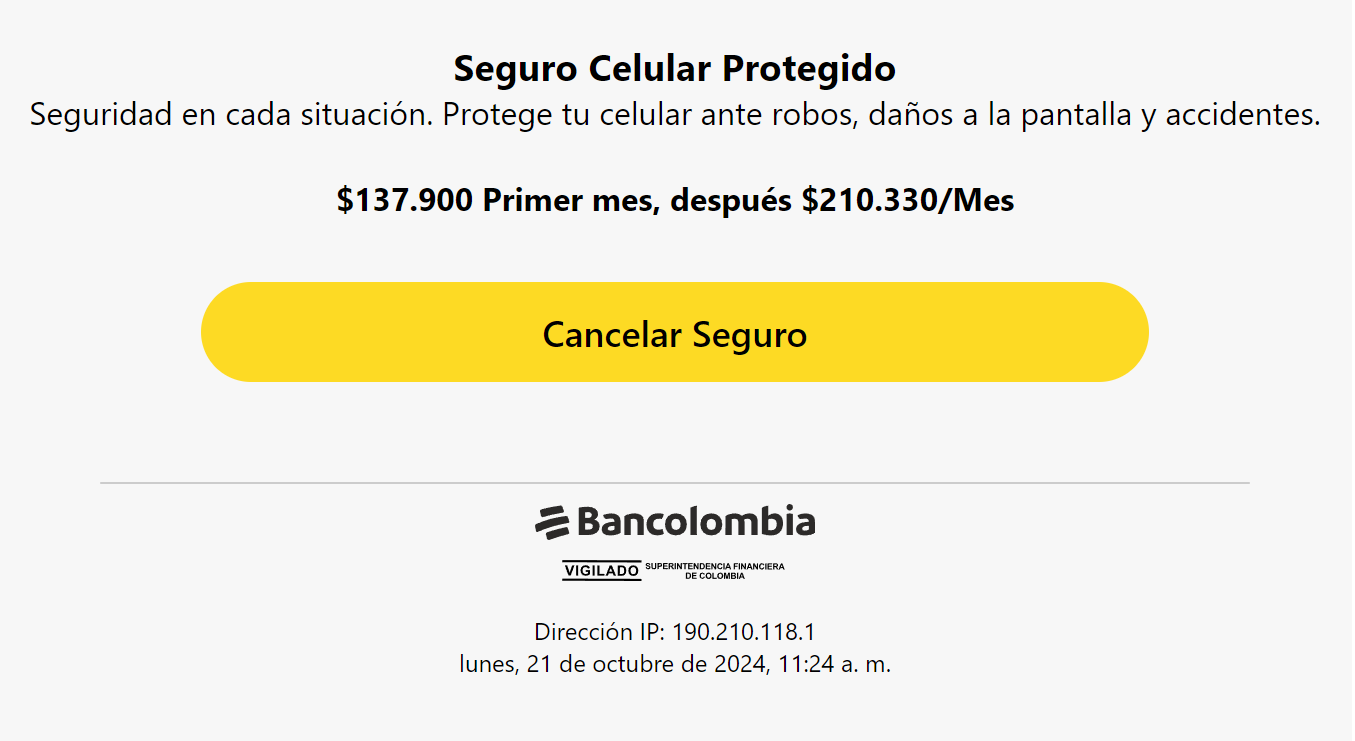
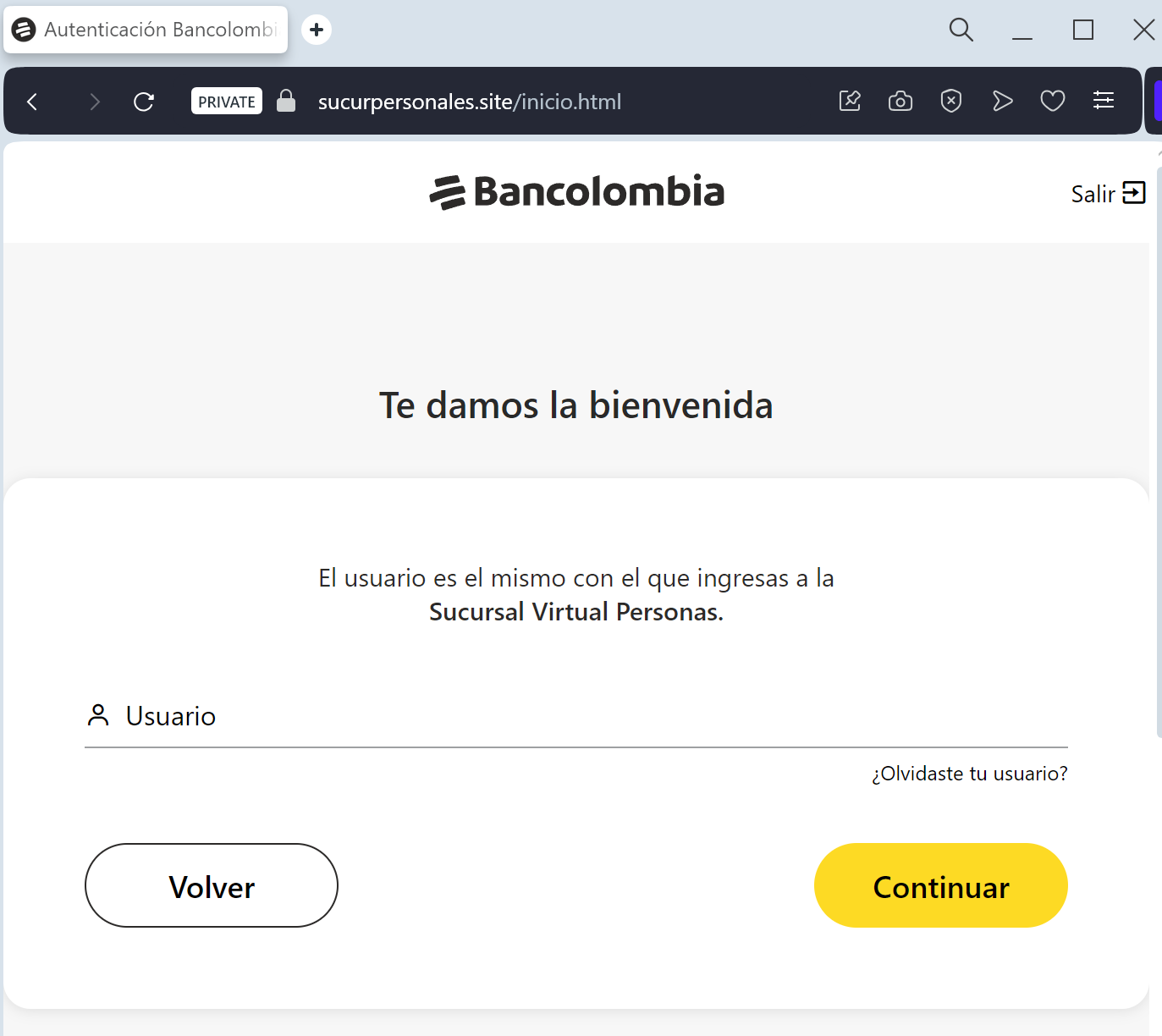
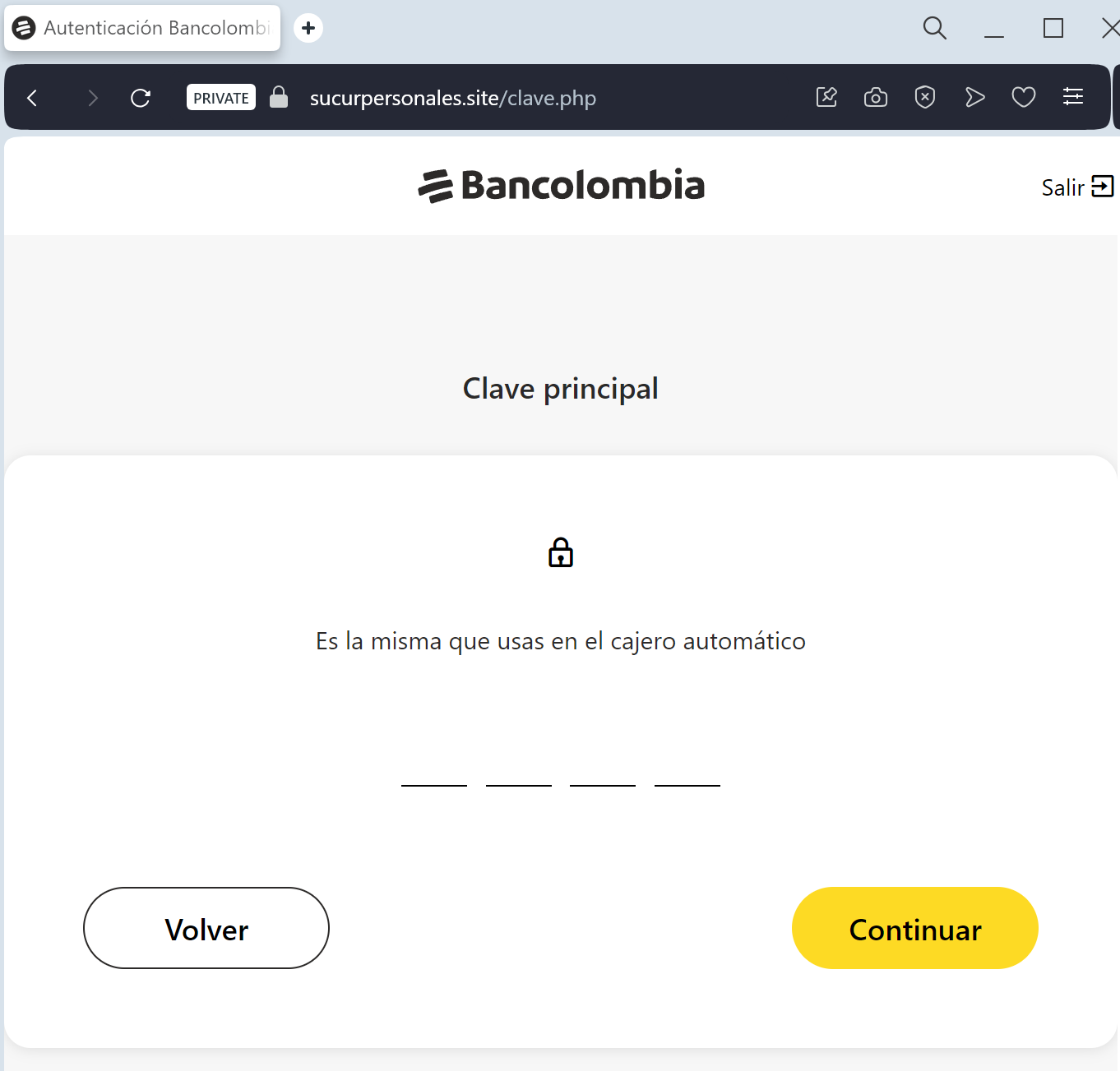
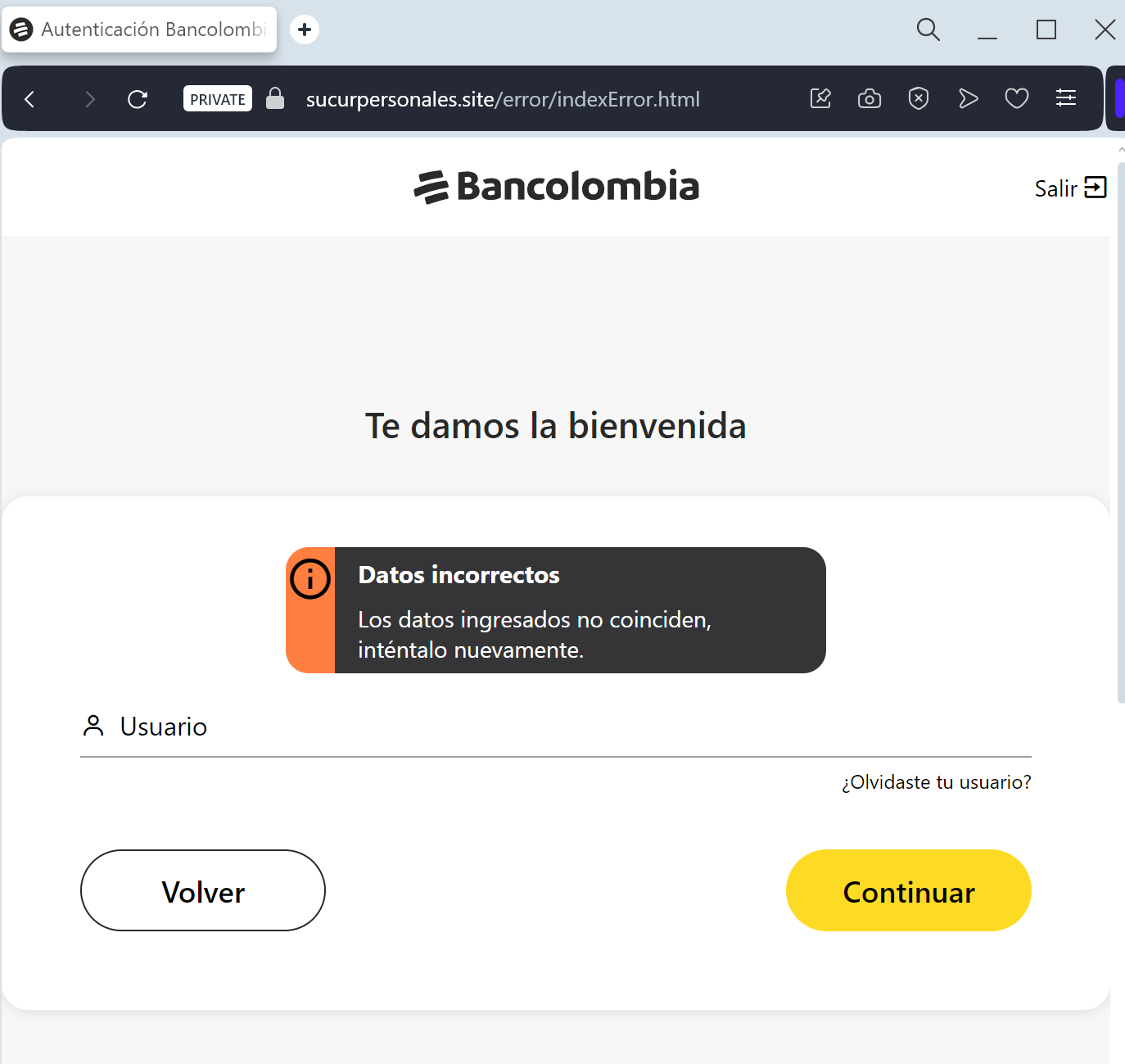
This phishing campaign against Bancolombia uses urgent SMS messages to lure victims to a fake “Sucursal Virtual Personas” portal. Attackers utilize a Man-in-the-Middle (MitM) method to harvest user credentials and dynamic keys, facilitating unauthorized access to financial accounts.
Expert Security Tip: Real-Time Dynamic Key Interception
The Method:
This Bancolombia phishing attack is a high-level Man-in-the-Middle (MitM) deceptive tactic. Scammers aren’t just looking for your password; they are waiting in real-time to intercept your Clave Dinámica (Dynamic Key).
The Trap:
When you enter your credentials on this fake page, the attacker simultaneously logs into the actual Bancolombia server. The moment the bank asks for your 6-digit security code, the phishing site prompts you to enter it. By providing that code, you are giving the threat actor a “one-time pass” to authorize a fraudulent transfer or register a new device to your account.
How to Protect Yourself:
The “Context” Rule: If a website asks for your Dynamic Key (Clave Dinámica) immediately after you enter your password — without you performing a specific transaction — it is 100% a phishing trap.
App-Only Authorization: Treat your Dynamic Key as a digital signature. Only use it inside the official Bancolombia App or on the bank’s official website that you accessed by typing ://bancolombia.com manually.
Zero Trust for Links: Bancolombia will never send you a link via SMS or Email to “synchronize” or “update” your security keys. Any such request is a scam.
