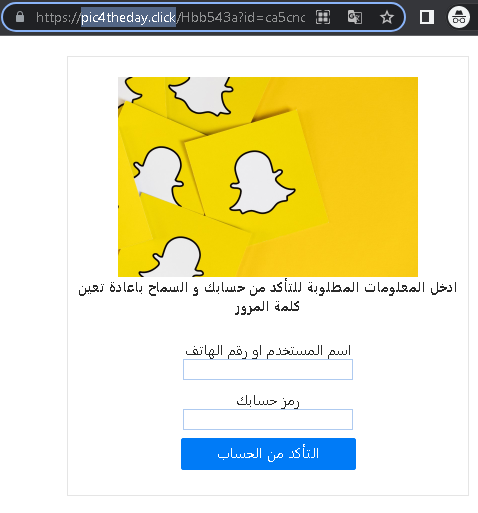
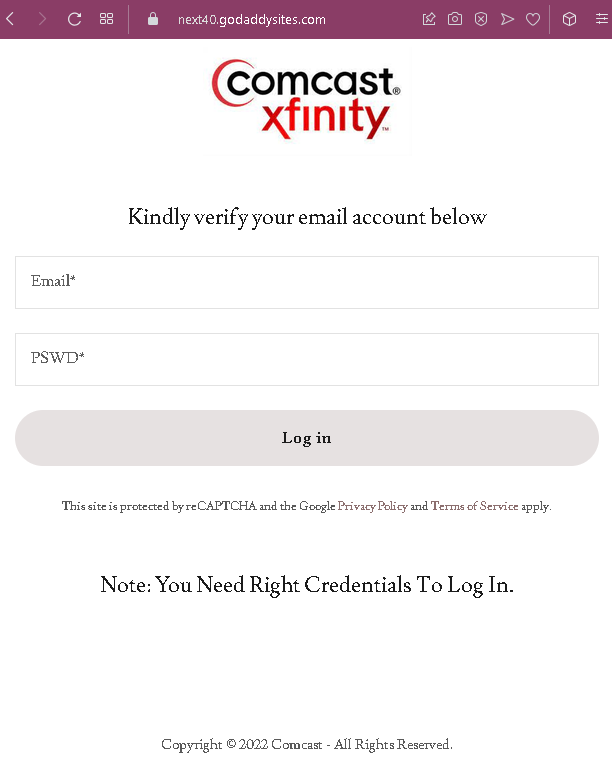
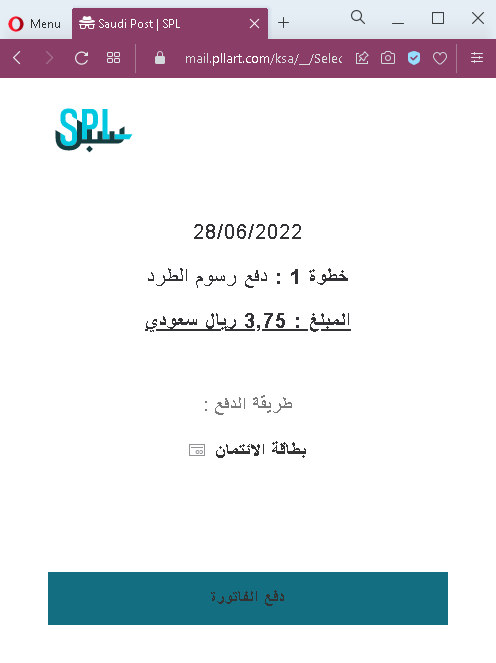
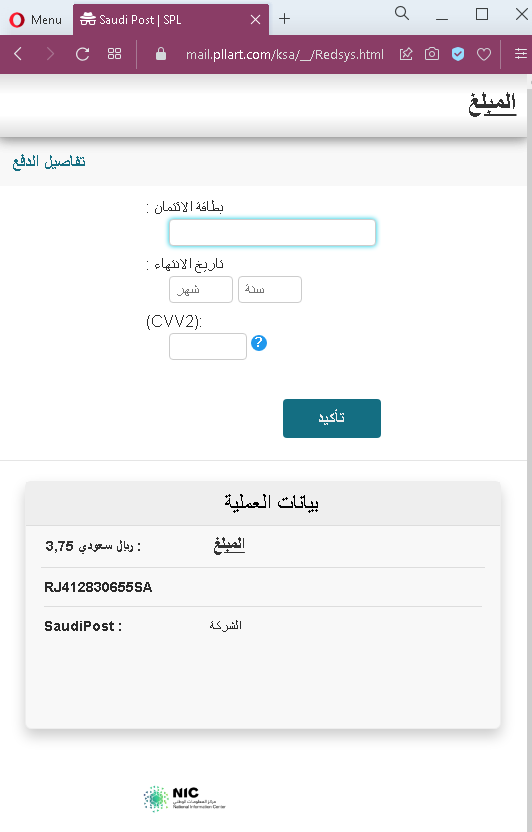
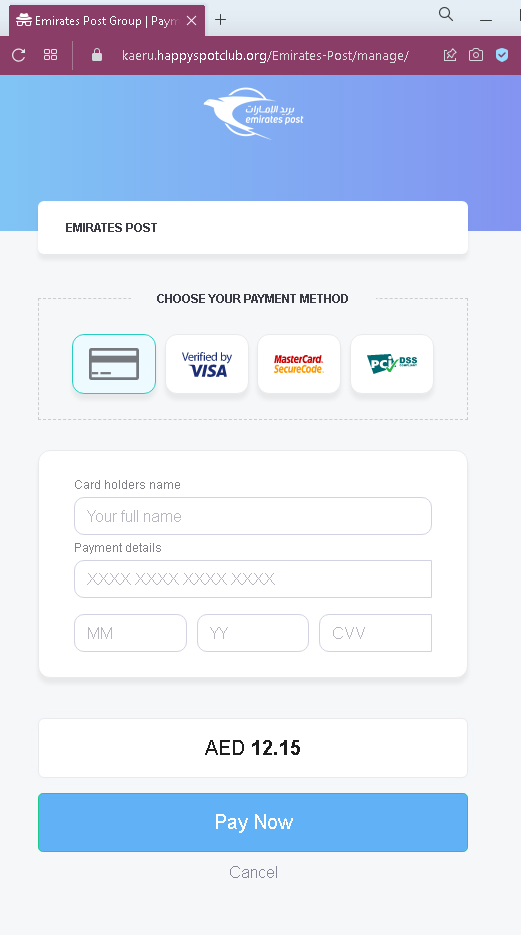
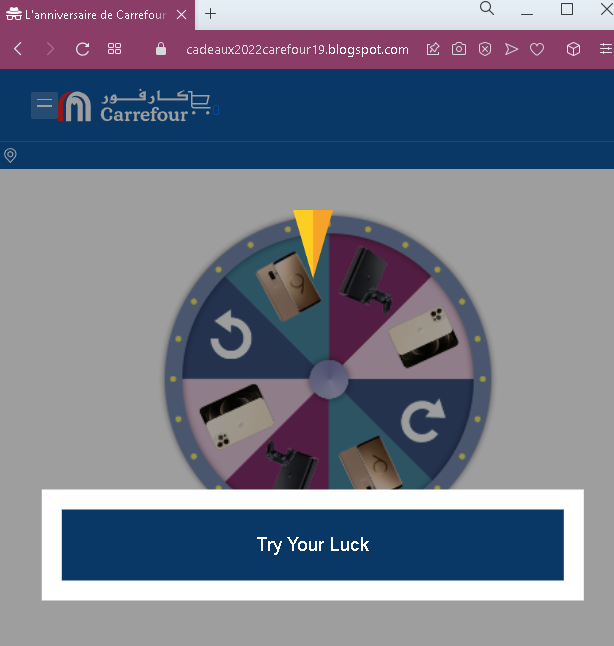
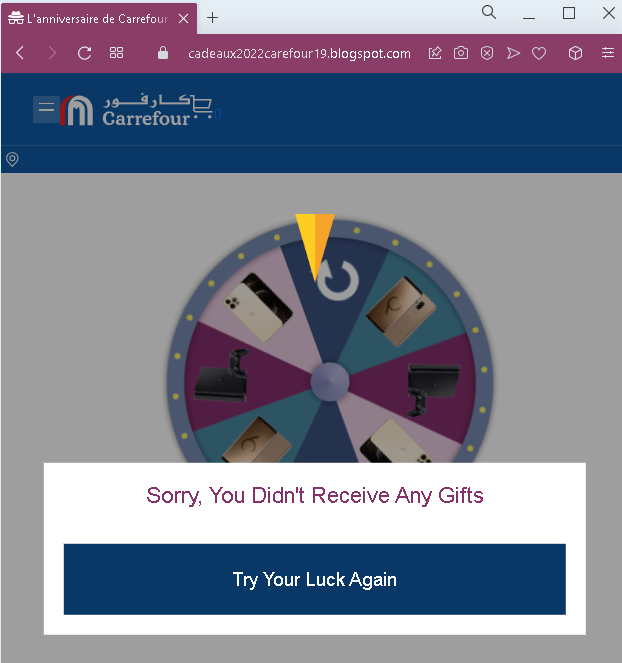
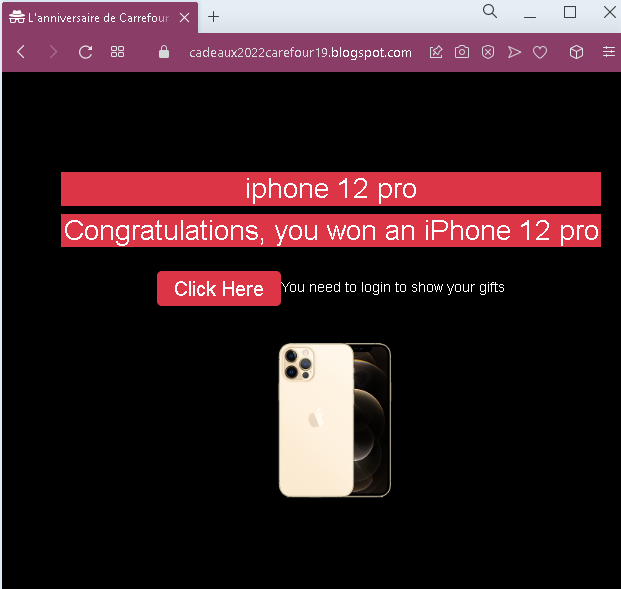
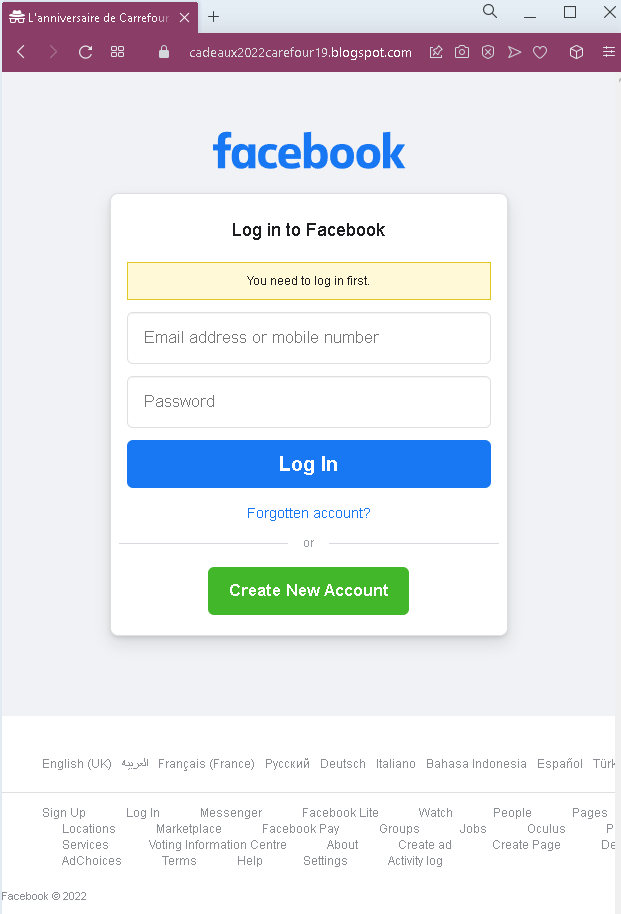
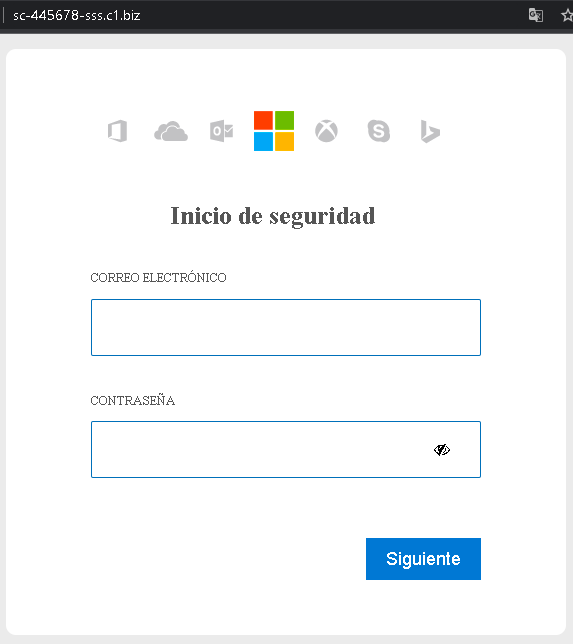
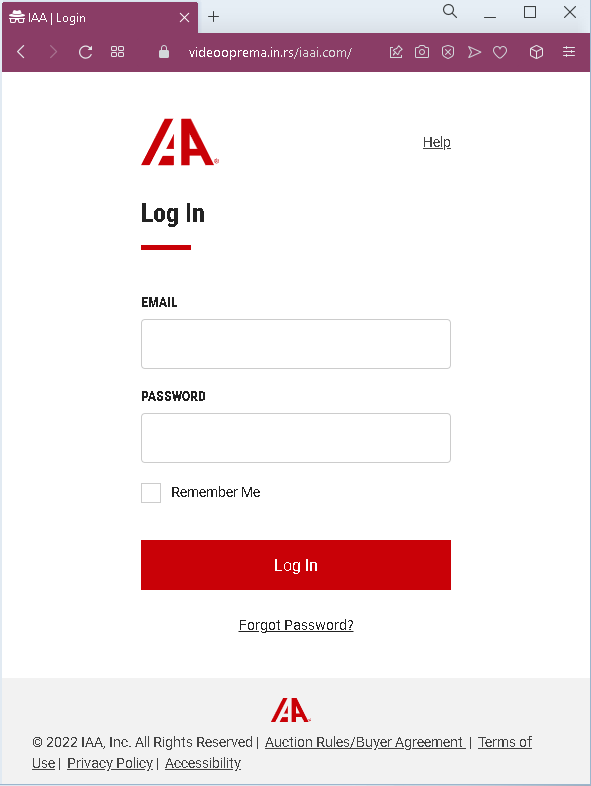
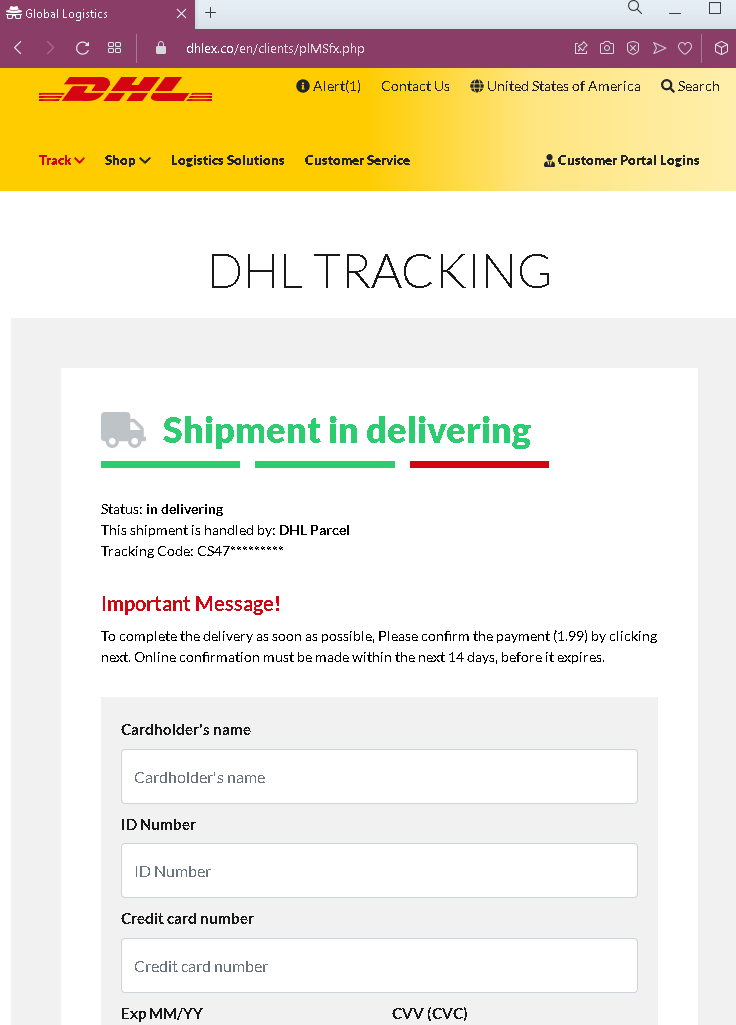
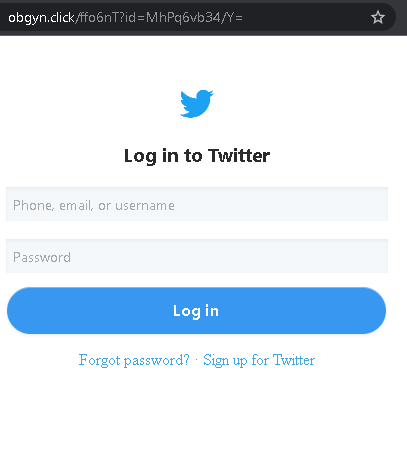
A phishing campaign targeting Banco Ripley in Chile uses smishing and email, directing users to a cloned website that mimics the official login portal to steal RUT numbers, passwords, and dynamic tokens. This Man-in-the-Middle (MitM) attack specifically aims to bypass security measures by harvesting real-time OTP codes to facilitate unauthorized transactions.
Threat Intel: This spoofed page was logged, cross-checked, and neutralized firsthand by the
Antiphishing.bizsecurity team during our automated link scanning workflows. To protect the public, the hostile origin link has been completely disabled within our infrastructure. We document and analyze these live visual patterns to help security researchers and users recognize deceptive clone designs before financial damage occurs.
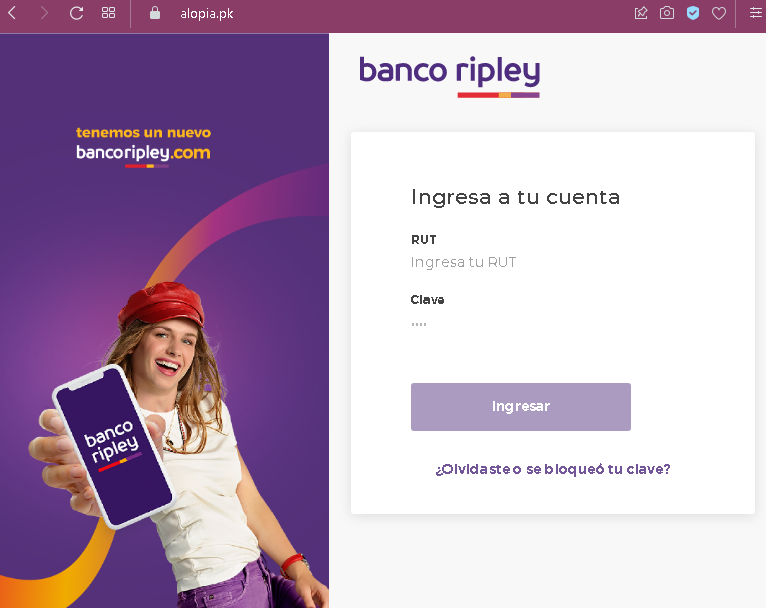
A Banco Ripley (Chile) phishing campaign targets users via smishing and email, directing them to a cloned website to steal credentials, Tax IDs (RUT), and real-time security codes. Attackers use urgent, fraudulent “security update” alerts to hijack Multipass/Soft Token codes to authorize illicit transfers, utilizing lookalike domains like bancoripley-cl-seguridad.com.
Protect Yourself: Access Banco Ripley only via the official app or website, never click links in unexpected messages, and remember that banks never ask for full security codes to log in or update profiles.

The Banco Ripley case exemplifies a real-time proxy attack designed to bypass Multi-Factor Authentication (MFA) by hijacking dynamic tokens (MultiPass/Soft Token) in real time. Victims are tricked into providing authorization codes on a fake site, allowing attackers to immediately take over accounts or register new devices. Protect yourself by recognizing that banks never request these codes to “update data,” and always verify the URL strictly matches the bank’s domain.