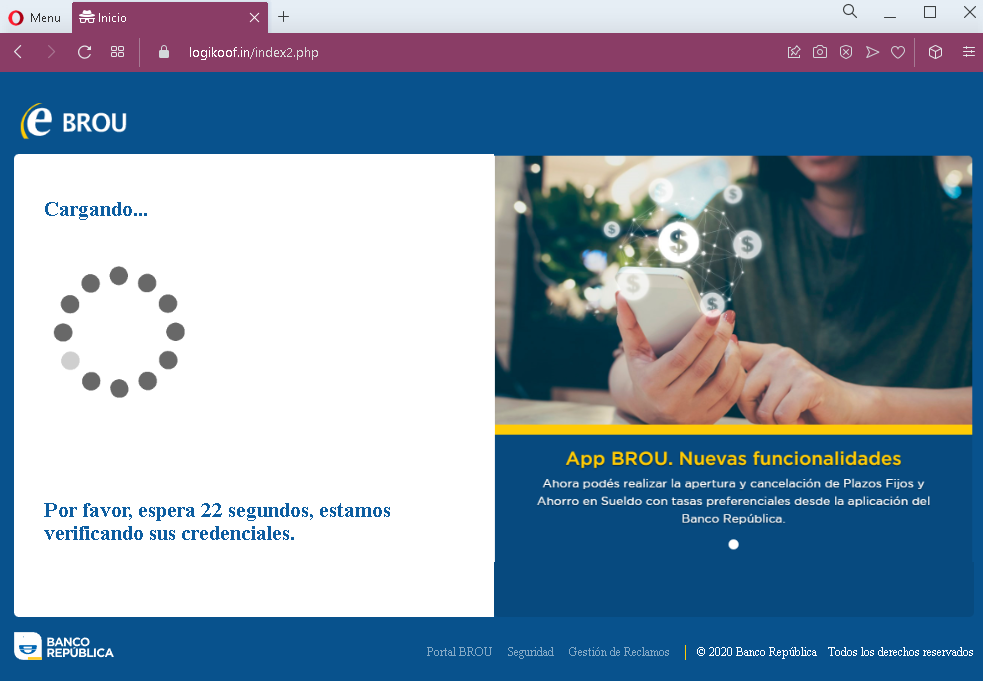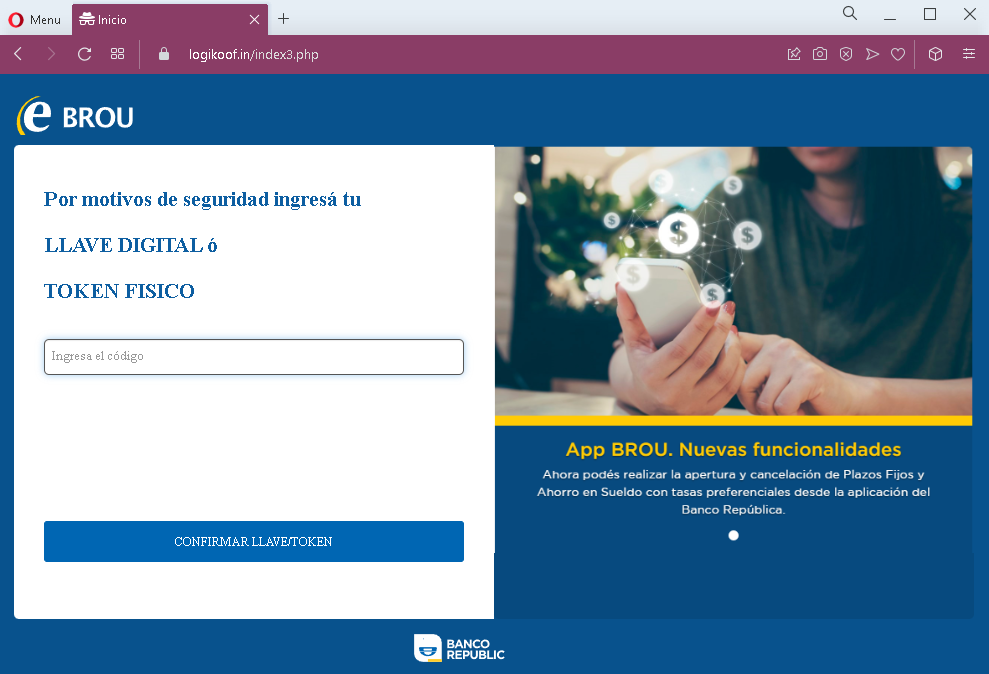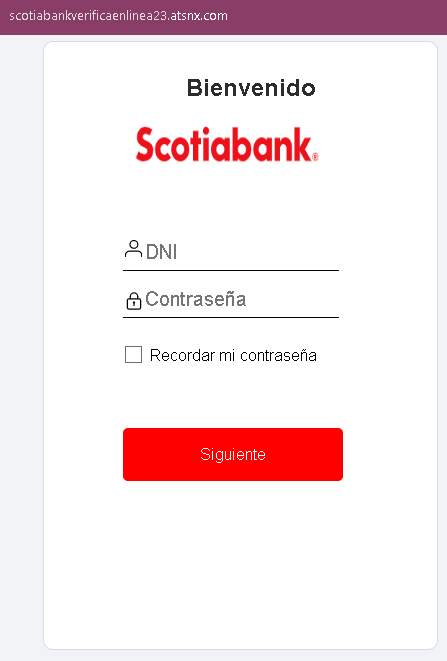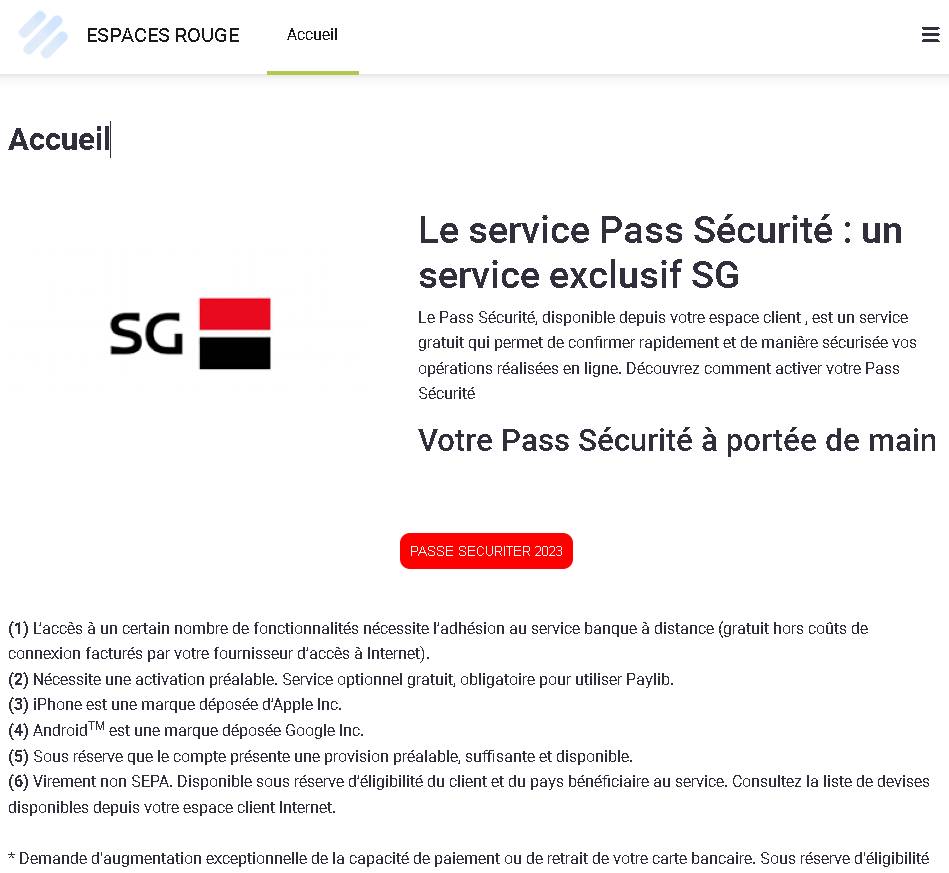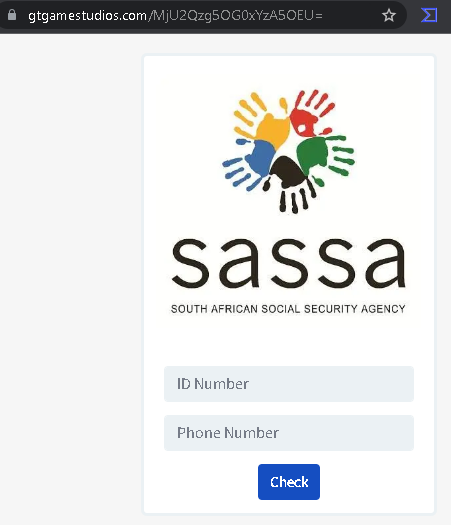
SASSA Phishing – Fake Verification Page Stealing Personal Information
This phishing campaign impersonates SASSA (South African Social Security Agency) , which manages social grants (including the COVID-19 Social Relief of Distress grant) for millions of South Africans. The page is designed to steal recipients’ personal information—specifically their ID Number and Phone Number—which can be used for identity theft, grant fraud, or to gain access to banking details.
How it works:
The victim receives a phishing SMS, WhatsApp message, or social media link claiming that their SASSA grant is ready for collection, requires verification, or that they need to update their details to receive payment. The message includes a link to this fake SASSA page. The victim is asked to enter their ID Number and Phone Number, with the likely promise of confirming grant status, unlocking funds, or completing a registration.
The goal:
The attacker aims to collect:
- South African ID numbers (a critical piece of personal identification)
- Phone numbers (used for SMS-based two-factor authentication and SIM swapping)
With this information, the attacker can:
- Fraudulently claim or redirect social grants
- Attempt SIM swapping to take over mobile numbers and gain access to banking accounts
- Commit identity theft or sell the data to other criminals
- Use the information for further phishing attacks
Red flags to watch for:
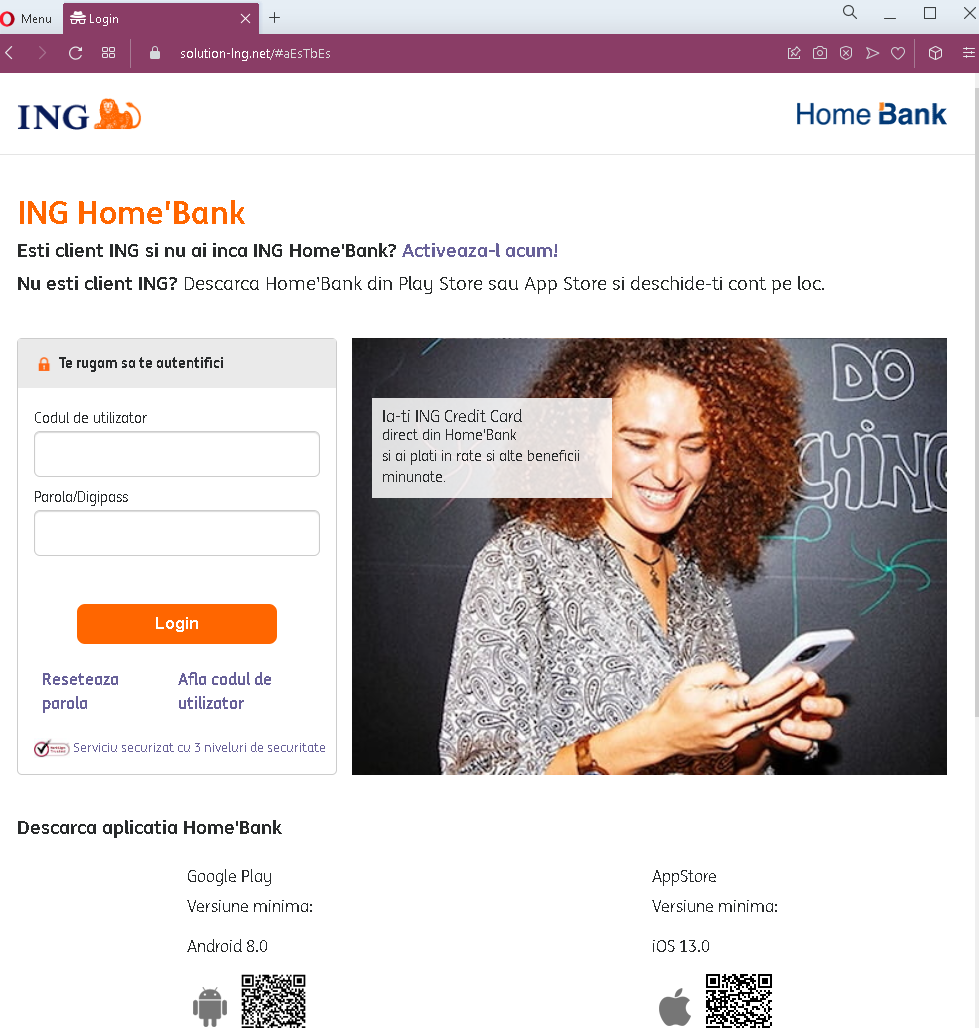
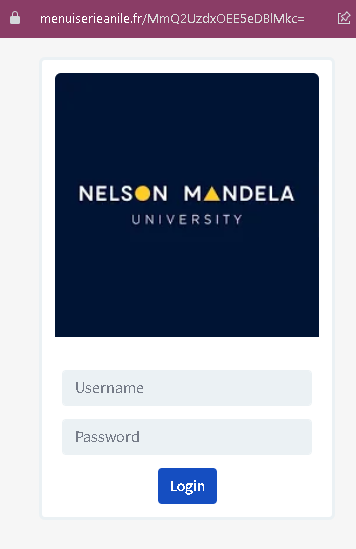
- Suspicious URL: The page is hosted on a domain (
gigamestudios.com) that is notsassa.gov.zaor any official SASSA domain. Legitimate SASSA services are accessed throughsassa.gov.zaor the official SASSA mobile app. - Extremely minimal design: The page lacks official SASSA branding, security notices, and navigation elements present on the real SASSA website. It is a simple form with only two fields.
- No personalization or verification: The page does not ask for a reference number, grant type, or any identifier that would link to a legitimate SASSA record.
- Unsolicited request for personal information: SASSA does not send SMS or WhatsApp messages with links requiring recipients to enter their ID and phone number to “unlock” or “verify” grants. Official communications direct recipients to the official website or app, and they do not ask for such information via external links.
- Generic form: The page only collects ID and phone number—no additional context about why this information is needed or what grant it pertains to.
What to do if you encounter this:
- Do not enter your ID Number, Phone Number, or any other personal information on this page.
- If you are a SASSA grant recipient, always access your grant information by typing
sassa.gov.zadirectly into your browser, using the official SASSA mobile app, or visiting a SASSA office in person. - If you have already entered your ID and phone number, contact SASSA’s fraud hotline immediately to report potential compromise and monitor your grant status for unauthorized changes.
- Report the phishing page to SASSA’s fraud department and to the South African Police Service (SAPS) or the Southern African Fraud Prevention Service (SAFPS).
Why this scam is effective:
SASSA grants are a lifeline for millions of vulnerable South Africans. Scammers prey on beneficiaries who may be less familiar with digital security practices. The promise of grant payments or the threat of losing benefits creates urgency. The simple form—asking only for ID and phone number—seems innocuous, but these two pieces of information are the keys to committing grant fraud and identity theft.
Protective measures:
- Always verify SASSA-related messages by logging into your official SASSA account through the official website (
sassa.gov.za) or app—never through links in SMS or WhatsApp messages. - SASSA will never ask you to click a link to “unlock” or “verify” your grant via SMS. Official communications come via secure channels and do not request sensitive information through external forms.
- Never share your ID number or personal details in response to an unsolicited message.
- Enable two-factor authentication on your banking and mobile accounts to reduce the risk of SIM swapping.
- Be aware of common grant scams: if a message promises payment or threatens loss of benefits unless you click a link and provide personal details, it is almost certainly a scam.