eBay / Kleinanzeigen Phishing – Fake “Ticket Sold” & Card Harvesting Scam (German Variant)
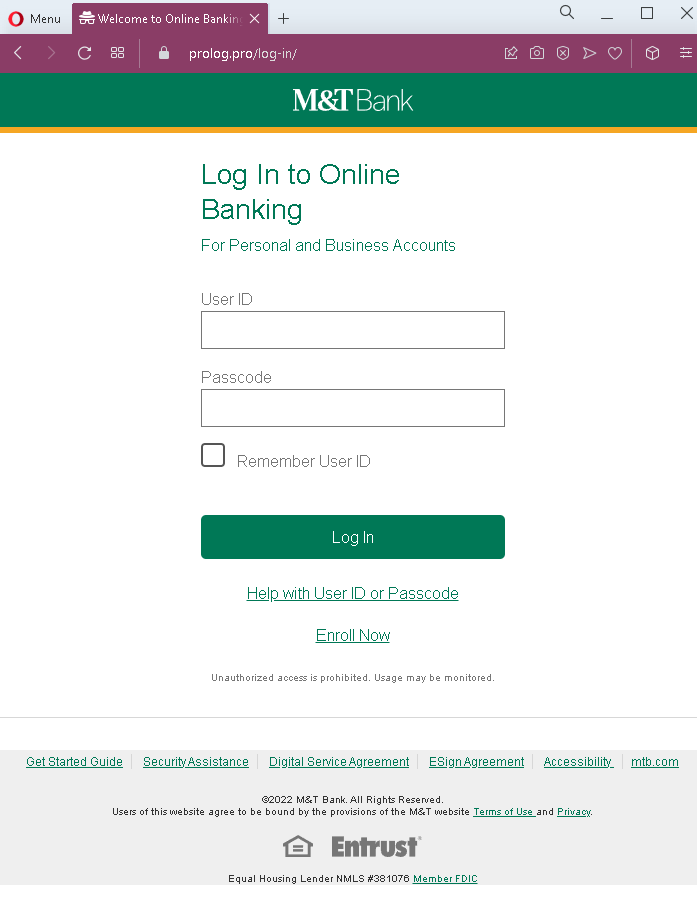
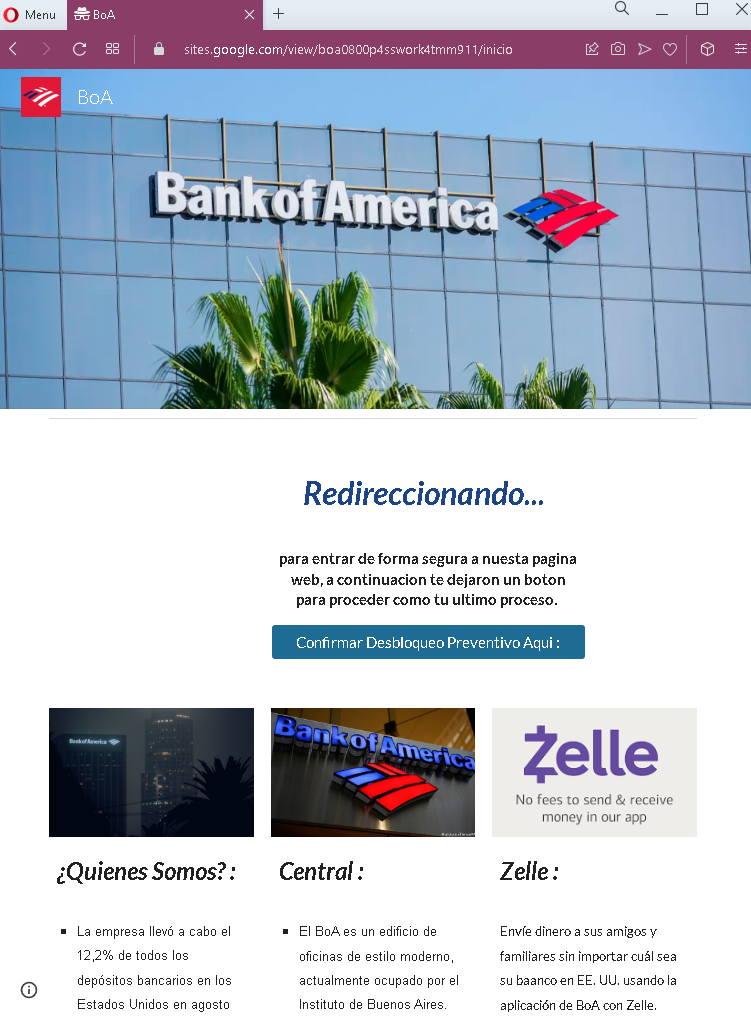
This phishing campaign impersonates eBay (or the German eBay Kleinanzeigen platform) to target sellers. The scam creates a fake “item paid” page for a high-demand concert ticket, then directs the seller to a credit card harvesting form under the guise of “receiving” payment.
How it works:
A seller receives a message—likely via the platform’s messaging system—from a supposed buyer claiming to have paid for a listed item. The message includes a link to the first phishing page.
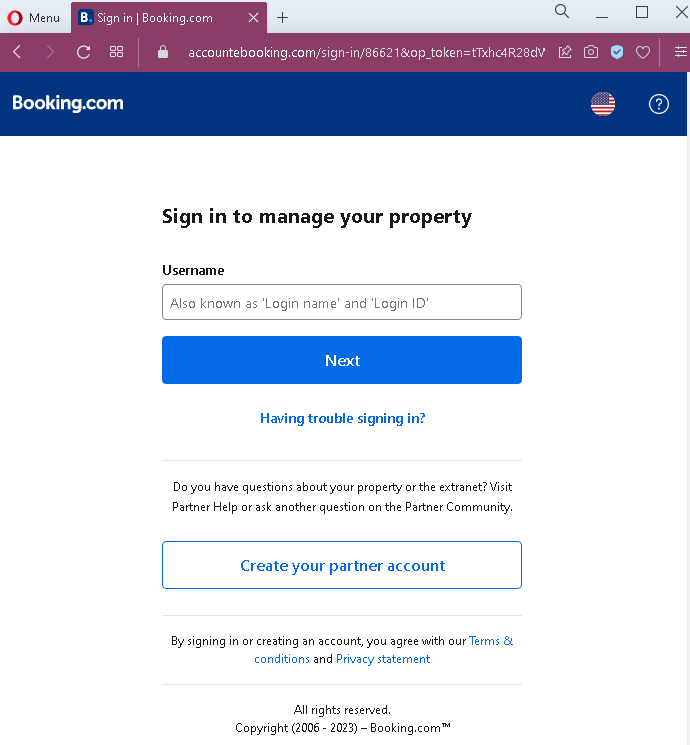
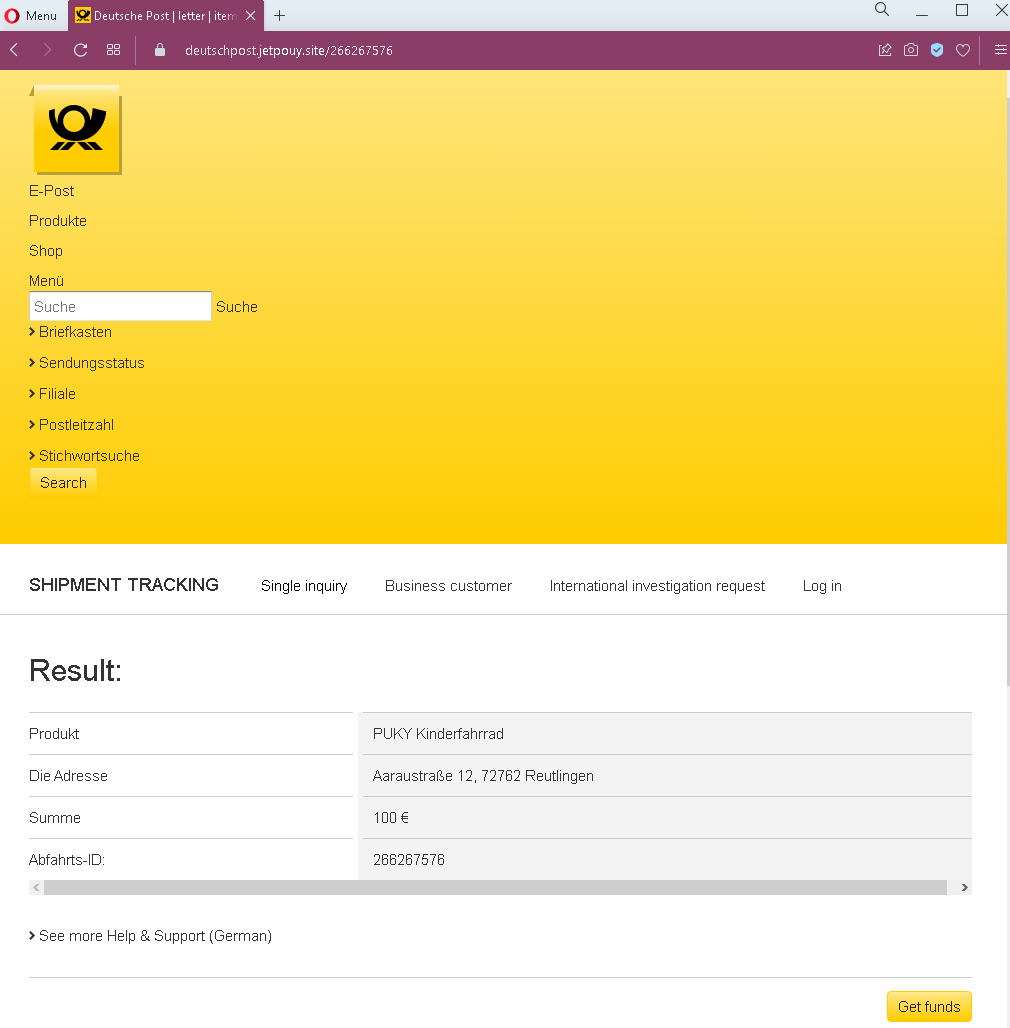
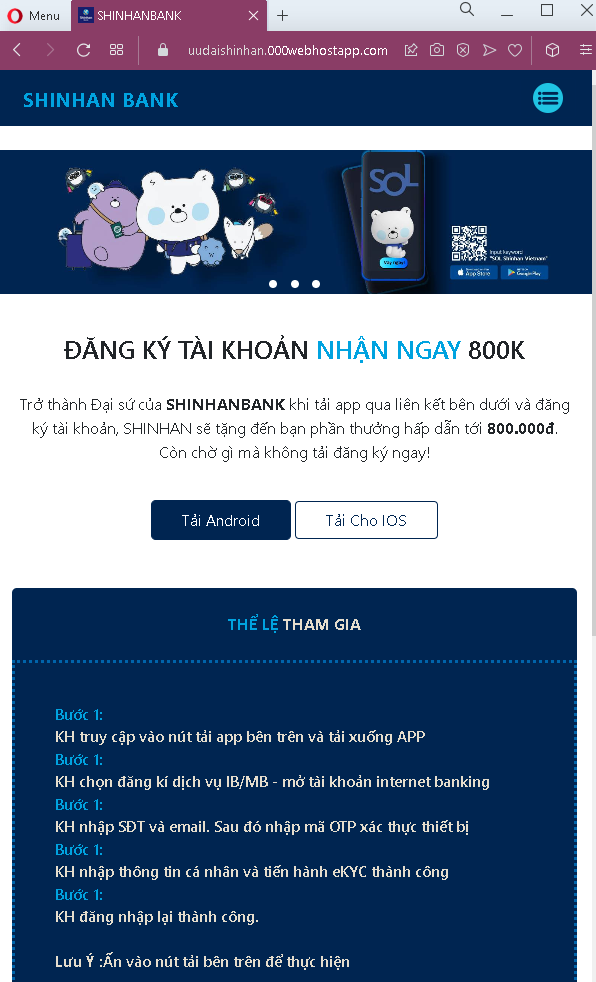
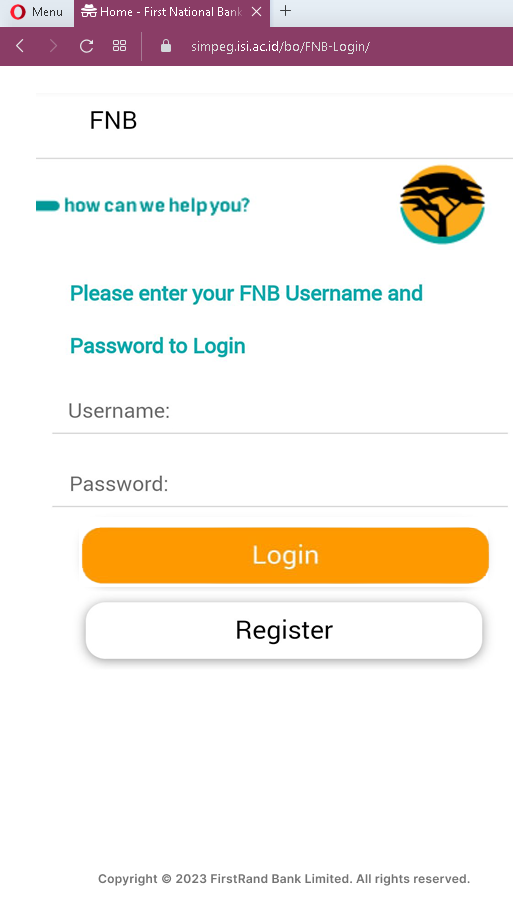
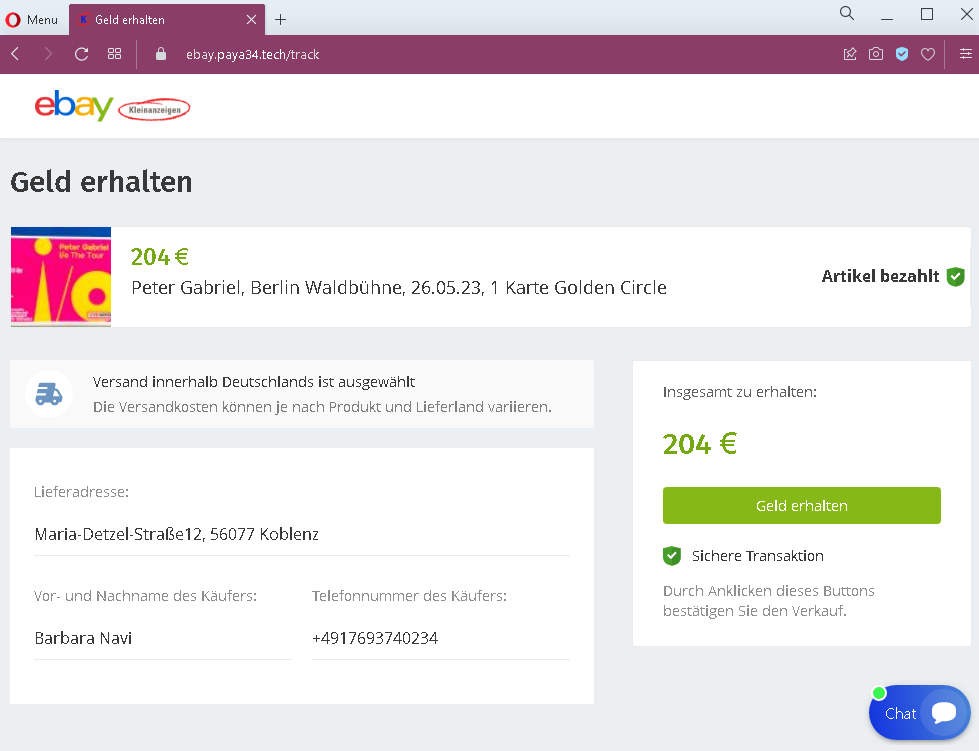
Step 1 – Fake “Item Paid” Confirmation Page
The first page displays:
- A heading suggesting funds are ready to be received
- A specific event: a concert ticket (Peter Gabriel in Berlin) with a price in euros (€204)
- A statement that the item has been paid
- Fabricated buyer details, including a name, phone number, and shipping address in Germany
- A prominent button implying the seller can claim or receive the money
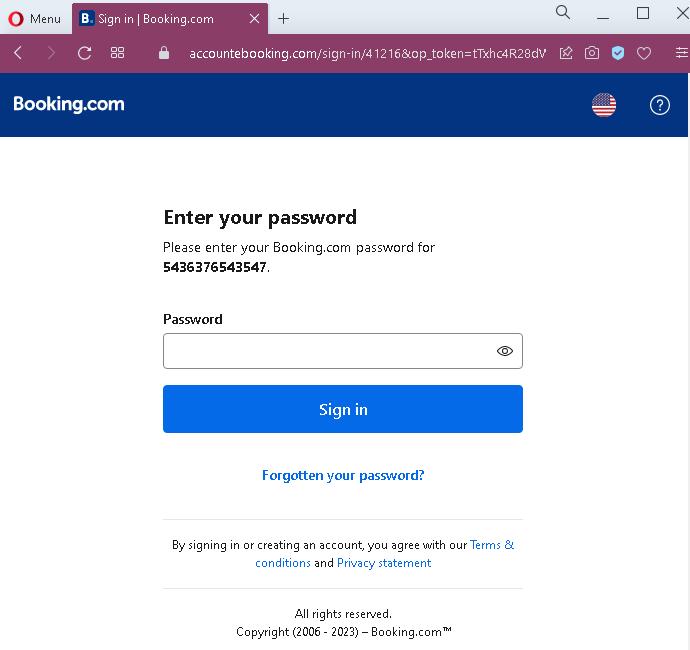
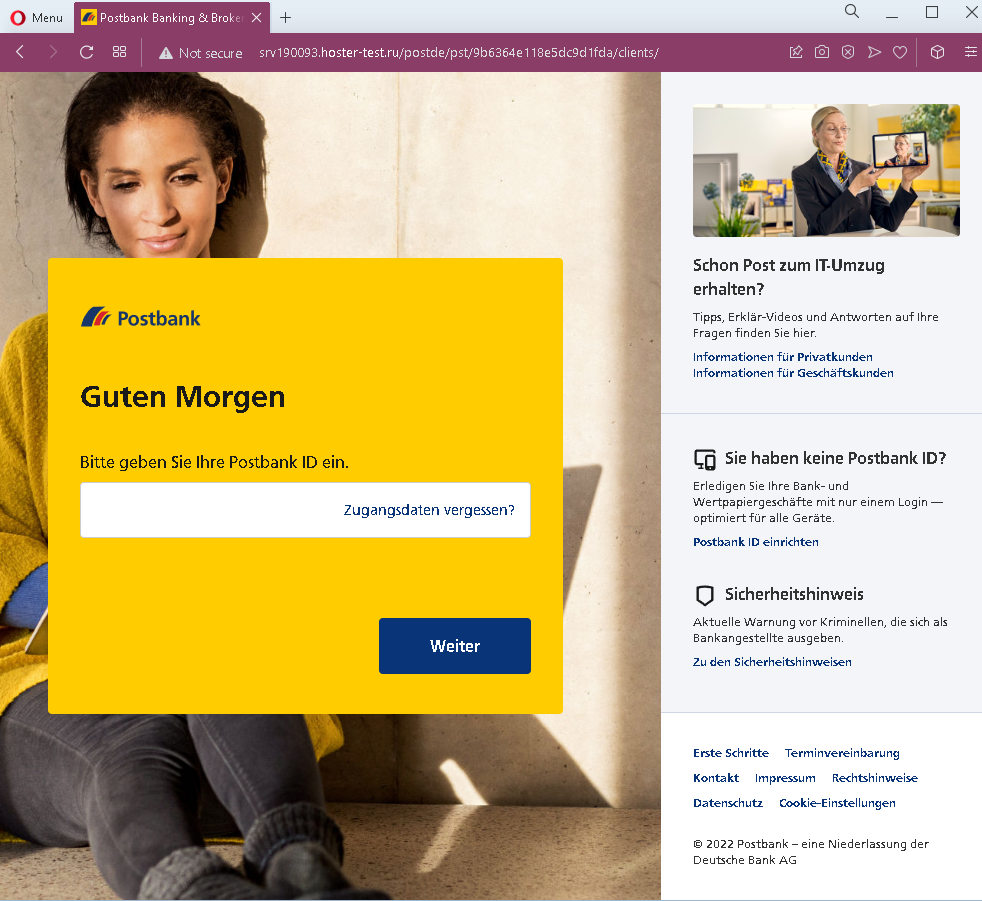
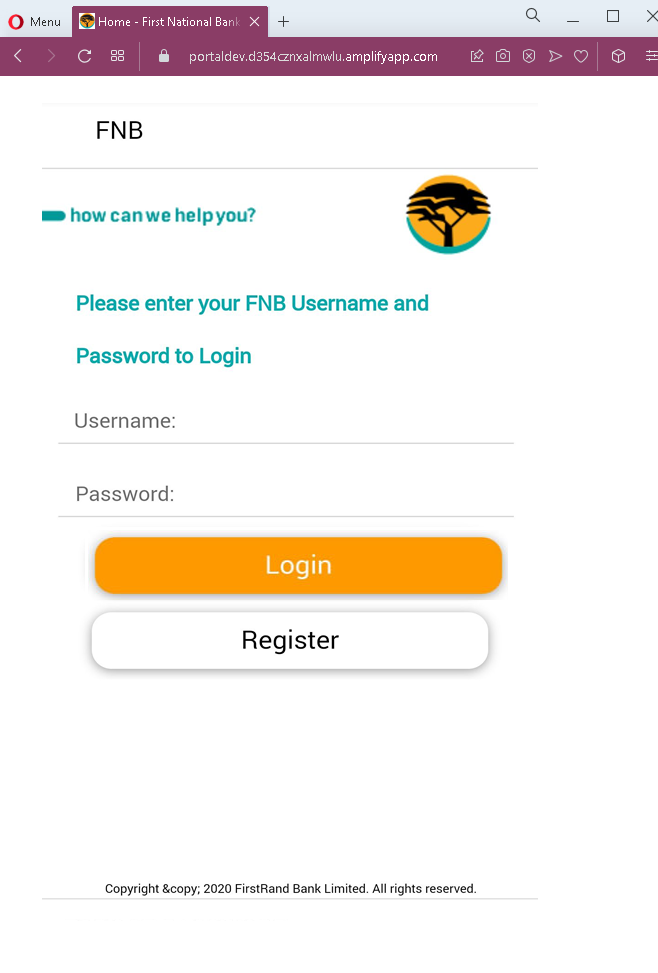
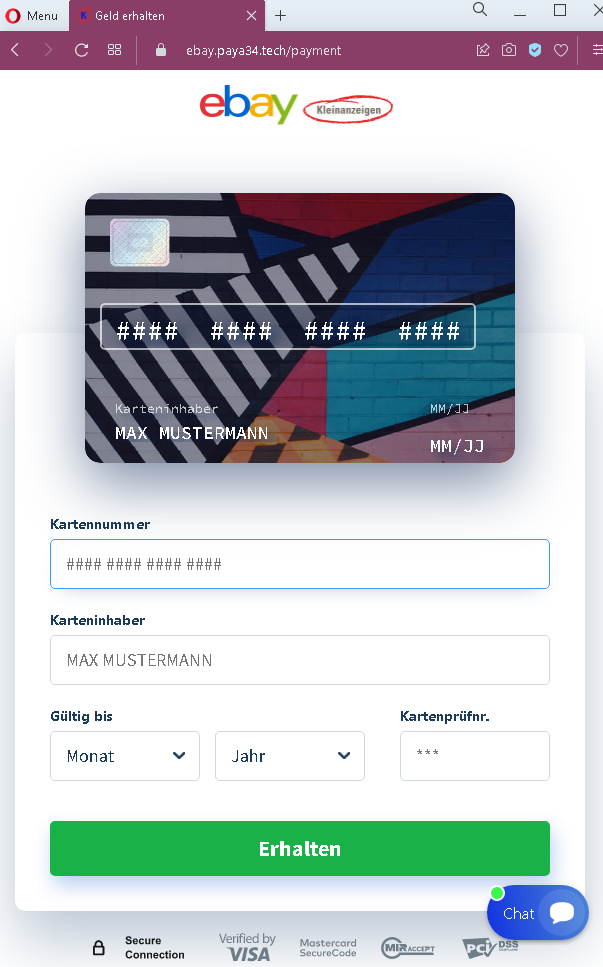
Step 2 – Credit Card Harvesting Page
After clicking the button, the seller is taken to a second page that:
- Uses eBay branding
- Requests full credit card details: cardholder name, card number, expiration date, and (implied) security code
- Includes payment brand logos (Visa, Mastercard) and a “Secure Connection” badge to appear trustworthy
The goal:
The attacker steals the seller’s credit card details. There is no actual buyer or payment—the entire transaction is fabricated. The concert ticket and the €204 price are realistic, making the scam plausible.
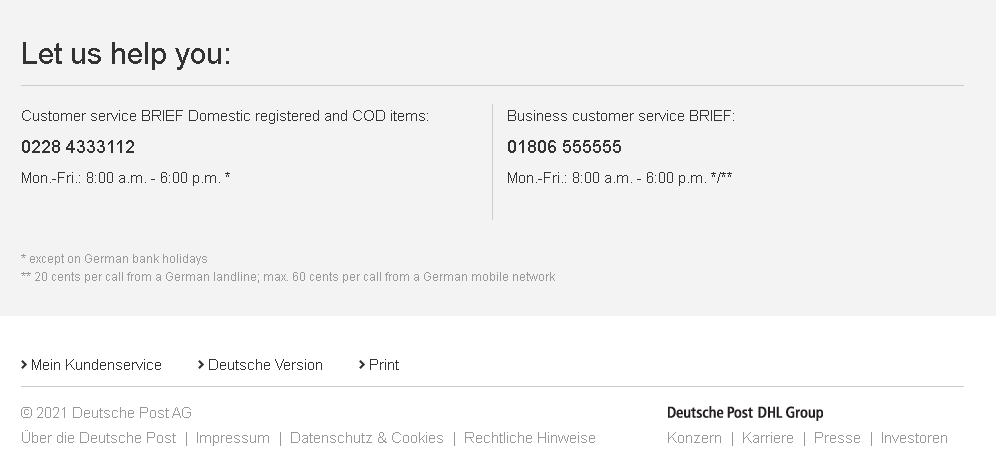
Red flags to watch for:
- Illogical request for card details: A seller receiving money should never be asked to enter their credit card number, expiration date, and security code. Receiving funds requires bank account details (IBAN) or a linked payout method—not card credentials.
- No eBay Kleinanzeigen branding on first page: The first page lacks clear eBay Kleinanzeigen branding, despite referencing a sale. The second page uses generic eBay branding, but the flow is inconsistent with how the platform actually processes payments.
- Suspicious URL: The pages are hosted on a domain that is not
ebay.de,ebay-kleinanzeigen.de, or any official eBay domain. Always check the address bar. - Fake buyer details: The provided buyer address and phone number are likely fabricated. In legitimate transactions on eBay Kleinanzeigen, payment is typically handled in person or via direct bank transfer—not through a third-party payment page.
- No account login required: A legitimate sale would appear in the seller’s account dashboard after logging in. This scam bypasses account authentication entirely.
- Generic card form: The second page lacks integration with eBay’s actual payment systems (such as the platform’s integrated checkout) and uses a generic form design.
What to do if you encounter this:
- Do not click the button to “receive” money.
- Do not enter your credit card details, cardholder name, expiration date, or security code on such pages.
- If you are selling on eBay Kleinanzeigen or similar platforms, always log into your account directly (by typing the official URL) to check for real sales and messages.
- Never trust links sent by buyers claiming they have paid—especially those directing you to external pages.
- If you have already entered your credit card details, contact your bank immediately to block the card and dispute any unauthorized charges.
- Report the phishing page to the platform’s support team.
Why this scam is effective:
The German classifieds market is active, and concert tickets for popular artists like Peter Gabriel are frequently sold second-hand. The €204 price is realistic for a “Golden Circle” ticket. Sellers are often eager to complete a sale quickly. The use of the eBay brand on the second page (even if generic) adds a layer of false familiarity for German users.
Protective measures:
- Always verify any sale by logging directly into your account (e.g., eBay Kleinanzeigen)—never through a link sent in a message.
- Never enter credit card details to receive payment. Sellers provide payout details (bank account) during account setup; payments are processed automatically or arranged in person.
- Be suspicious of any message that creates urgency or claims payment is already “waiting” but requires you to click an external link.
- If a buyer sends you a link to “claim” payment, treat it as a red flag and verify directly through the platform’s official app or website.
- On eBay Kleinanzeigen, prefer local, cash-on-pickup transactions for high-value items. If shipping, use the platform’s integrated payment system (if available) or a traceable bank transfer—never a link-based “card” form.