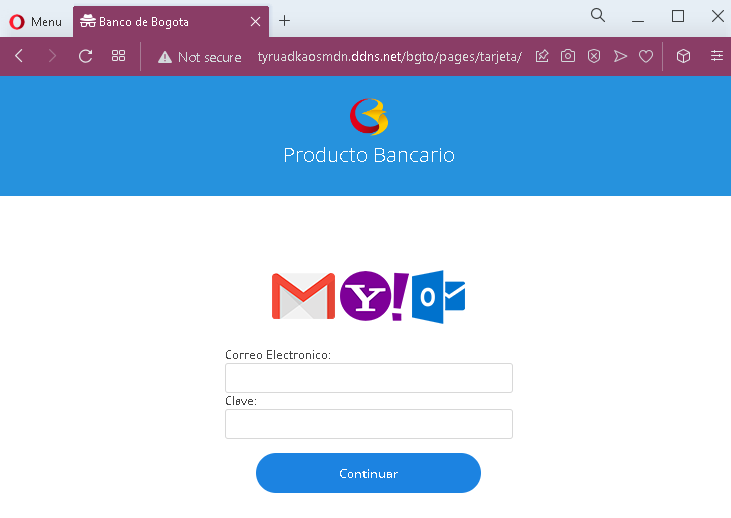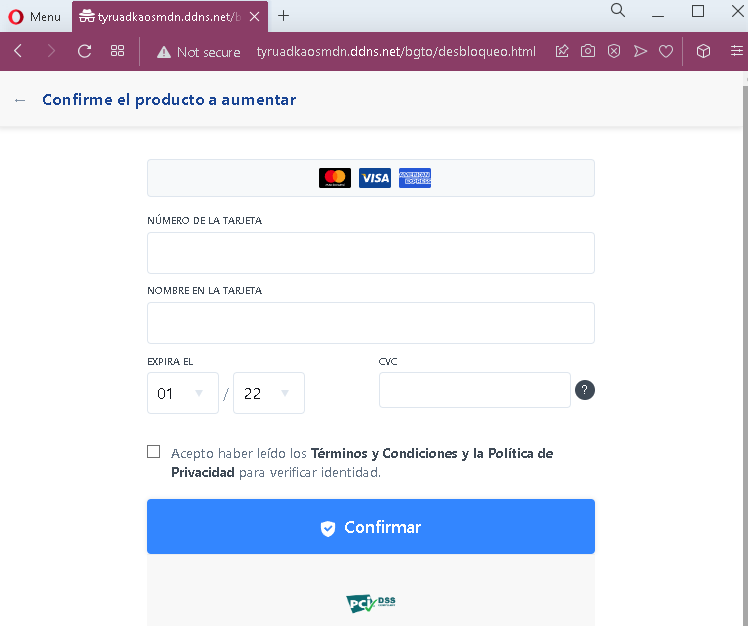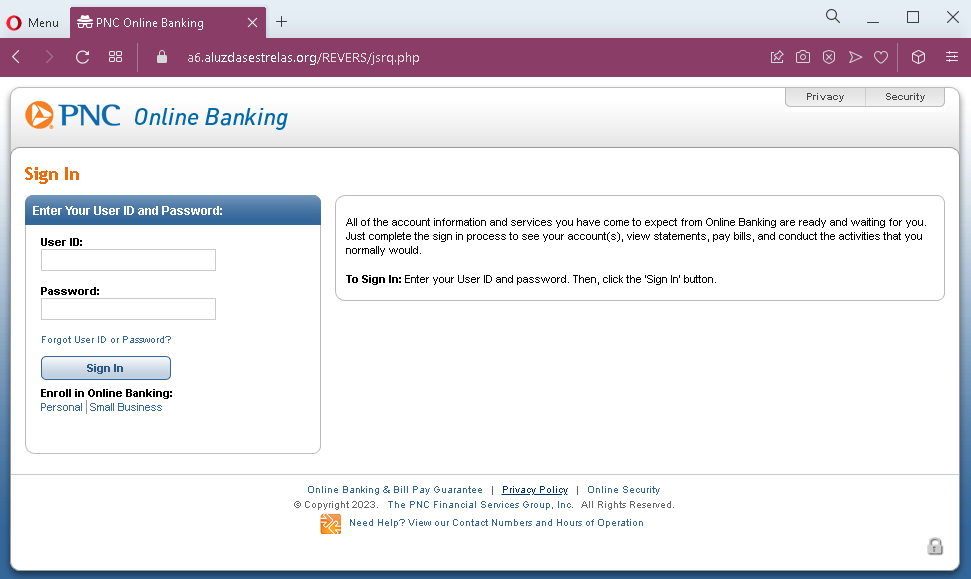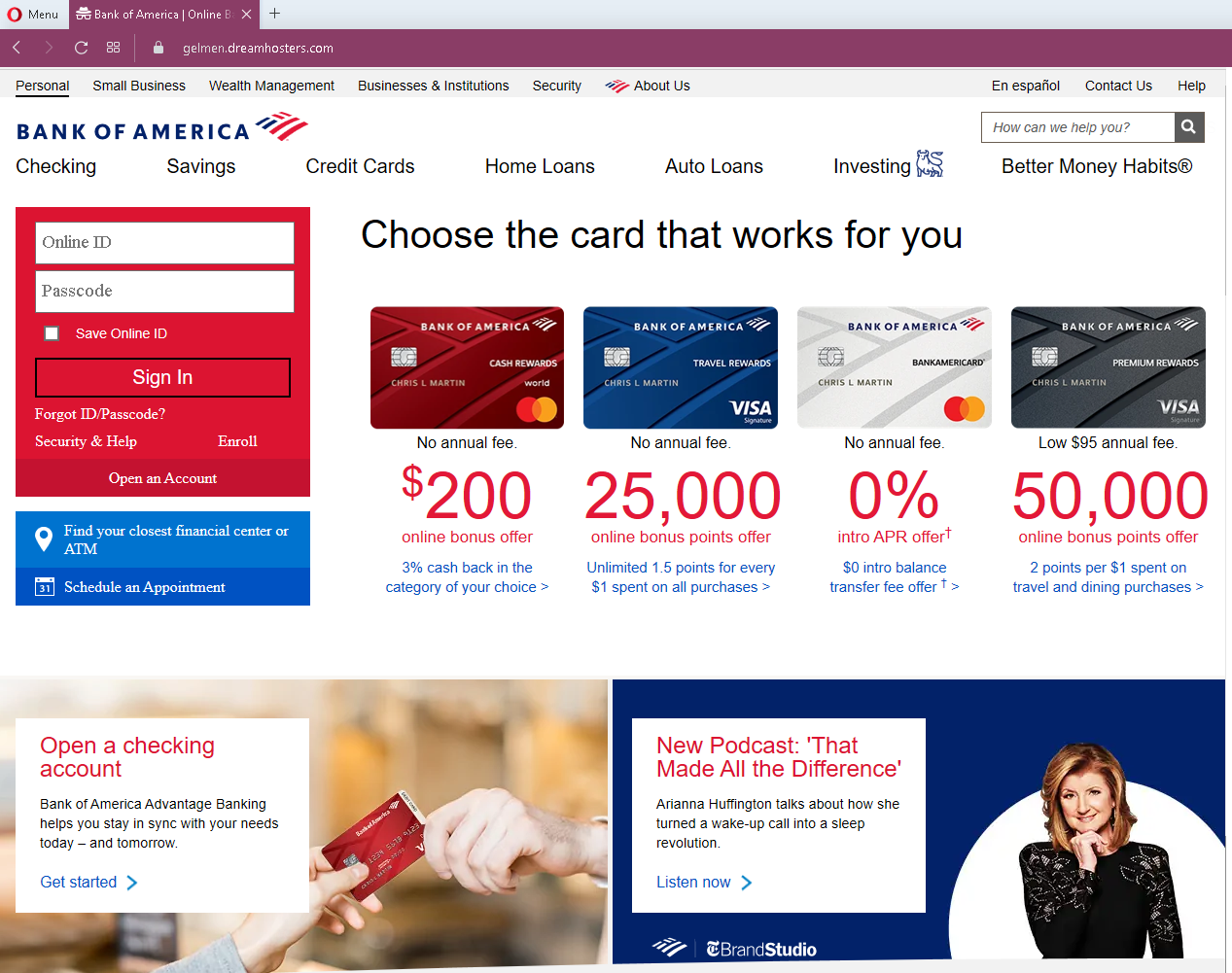
Threat Analysis: Banco Bisa Phishing – Fake “Banca EN-LINEA” Login Page
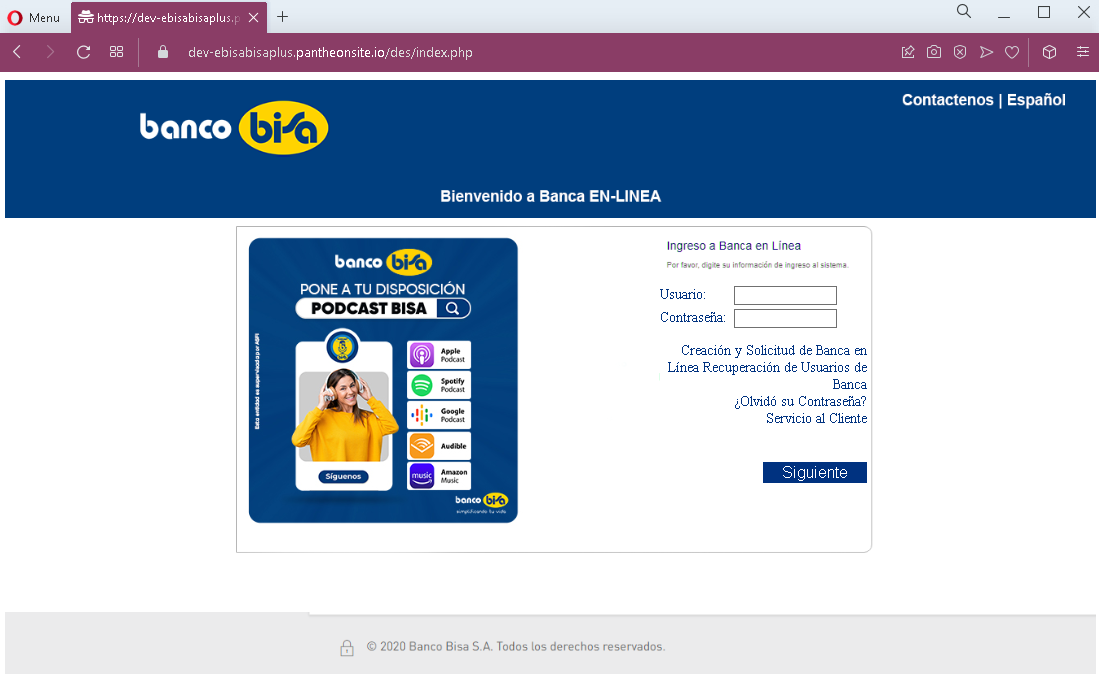
This phishing campaign impersonates Banco Bisa, a prominent Bolivian bank. The page mimics the bank’s “Banca EN-LINEA” (online banking) login interface to steal customers’ Usuario (username) and Contraseña (password).
How it works:
The victim receives a phishing email, SMS, or other message claiming a security alert, account issue, or the need to verify their information. The message includes a link to this fake Banco Bisa login page. When the victim enters their Usuario and Contraseña and clicks “Siguiente” (Next), the credentials are captured and sent to the attacker.
The goal:
The attacker aims to steal the victim’s Banco Bisa online banking credentials. With these, they can log into the victim’s real bank account, view balances, transfer funds, and commit fraud.
Red flags to watch for:
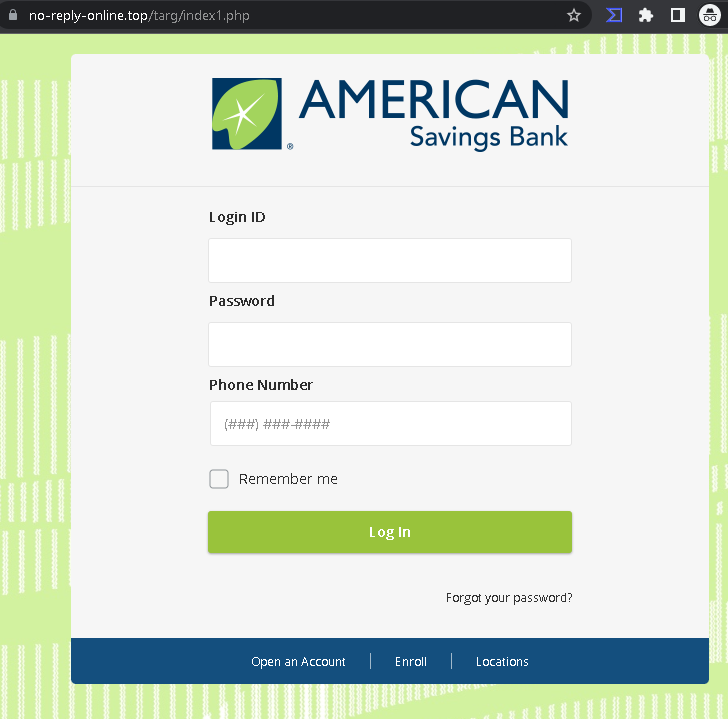
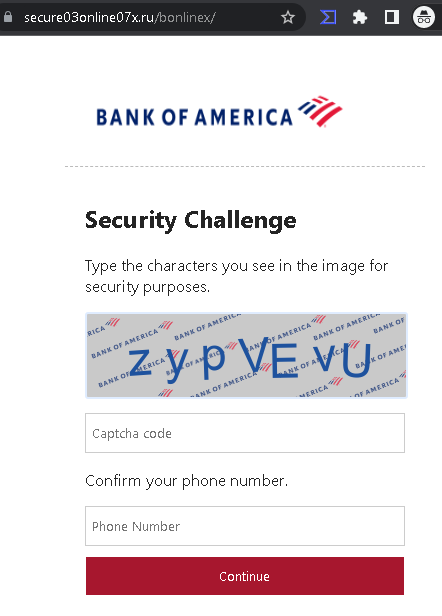
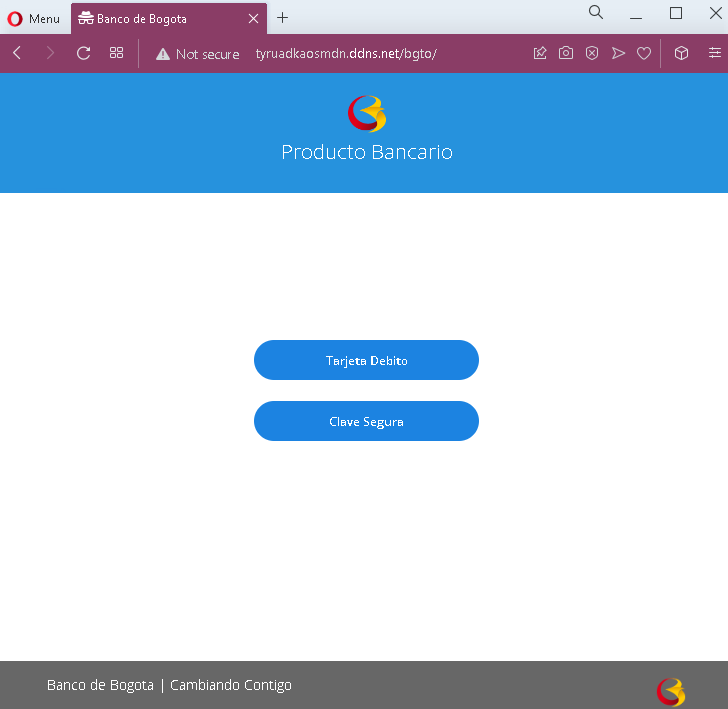
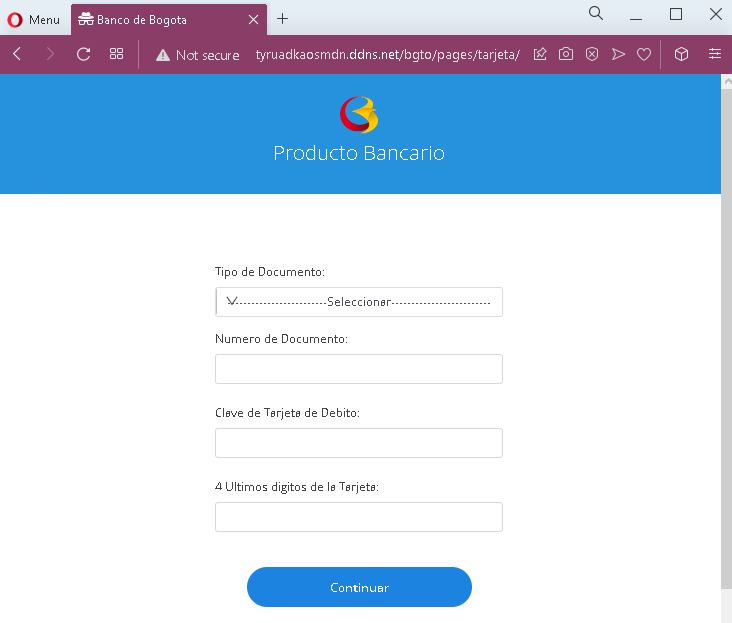
- Suspicious URL: The page is hosted on a domain that is not
bisa.comor any official Banco Bisa domain. Legitimate Banco Bisa online banking is accessed through the bank’s official website. Always check the address bar. - Mixed branding: The footer includes references to “PODCAST BISA” and logos for Apple Podcast, Spotify, etc. While Banco Bisa may have a legitimate podcast, the inclusion of these elements on a login page is unusual and suggests copied content. More importantly, the footer incorrectly shows “© 2020 Banco Bisa S.A.” when the screenshot is from 2023—an outdated copyright notice is a common phishing oversight.
- Unsolicited login request: Banco Bisa does not send emails or messages with links requiring customers to log in to resolve account issues. Customers should always access online banking by typing the official URL directly or using the official mobile app.
- Minimal design: The page lacks the full navigation, security notices, and personalized security elements (such as a security image or phrase) that would appear on a legitimate Banco Bisa login page.
- Generic form: The page only asks for Usuario and Contraseña without additional context or verification steps typical of the real bank’s login flow.
What to do if you encounter this:
- Do not enter your Usuario, Contraseña, or any other personal information on this page.
- If you are a Banco Bisa customer, always access online banking by typing
bisa.comdirectly into your browser or by using the official Banco Bisa mobile app. - If you have already entered your credentials, contact Banco Bisa immediately through their official customer service hotline to secure your account and change your password.
- Report the phishing page to Banco Bisa’s fraud department.
Why this scam is effective:
Banco Bisa is a well-known bank in Bolivia, and “Banca EN-LINEA” is its standard online banking portal. The page uses the bank’s logo and familiar layout. The inclusion of podcast links and other promotional content (copied from the real bank’s website) can make the page appear legitimate at first glance. However, the outdated copyright year (2020) and the unusual placement of promotional content on a login page are subtle red flags.
Protective measures:
- Bookmark the official Banco Bisa login page and use that bookmark to access online banking—never click links in emails or messages.
- Use a password manager: It will autofill only on legitimate
bisa.comdomains, not on phishing sites. - Enable two-factor authentication (2FA) on your Banco Bisa account if available, to add an extra layer of protection.
- Be suspicious of any unsolicited message that creates urgency and asks you to log in to your bank account.
- Check the URL carefully: Legitimate Banco Bisa domains end with
bisa.com. Look for misspellings, extra words, or unusual top-level domains. - If in doubt, contact Banco Bisa directly using a phone number from your bank statement or the official website—never use contact information provided in a suspicious message.