Analysis Memo: This spoofed page was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the hostile origin link has been completely disabled within our infrastructure. We document and analyze these live visual patterns to help security researchers and users recognize deceptive clone designs before financial damage occurs.
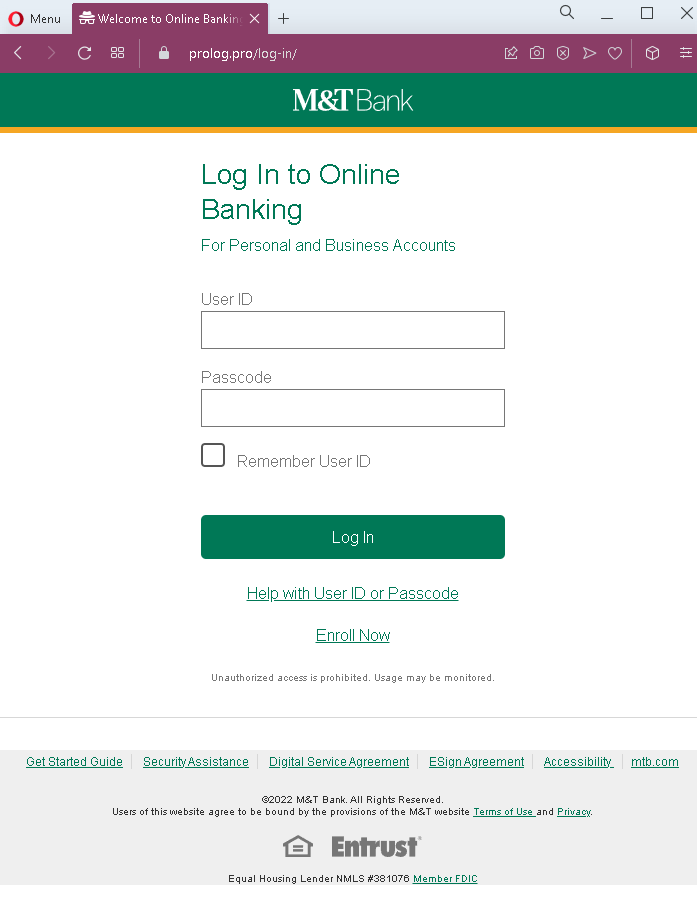
M&T Bank Online Banking Phishing – Credential Harvesting Page
This phishing campaign impersonates M&T Bank, a well-known bank in the United States, particularly active in the Northeast and Mid-Atlantic regions. The page is designed to steal customers’ online banking credentials—specifically the User ID and Passcode (password) used to access M&T Bank’s online banking platform.
How it works:
The victim receives a phishing email, SMS, or other message claiming a security alert, account suspension, or the need to verify their information. The message includes a link to this fake M&T Bank login page. The page mimics the real M&T Bank online banking interface, including familiar footer links. When the victim enters their User ID and Passcode and clicks “Log In,” the credentials are captured and sent to the attacker.
The goal:
The attacker aims to steal the victim’s M&T Bank online banking credentials. With these, they can log into the victim’s real bank account, view balances, transfer funds, pay bills, and potentially commit further fraud.
Red flags to watch for:
- Suspicious URL: The page is hosted on a domain that is not
mtb.commtb.com - Outdated copyright notice: The footer shows “©2022 MAT Bank” (with a typo: “MAT” instead of “M&T”) and an incorrect year. Legitimate pages display the current year and correct branding.
- Typographical error: The bank name is misspelled as “MAT Bank” in the copyright line—a clear indicator of a fake page.
- Unsolicited login request: M&T Bank does not send emails or messages with links requiring customers to log in to resolve account issues. Customers should always access online banking by typing the URL directly or using the official app.
- No personalization or security image: Legitimate M&T Bank login pages often display a security image or phrase after entering a User ID. This page lacks that additional security layer.
- Generic footer: While the footer contains links similar to the real M&T Bank site, the presence of these links does not make the page legitimate—attackers copy them from the real website.
What to do if you encounter this:
- Do not enter your User ID, Passcode, or any other personal information on this page.
- If you are an M&T Bank customer, always access online banking by typing
mtb.com - If you have already entered your credentials, contact M&T Bank immediately through their official customer service hotline to secure your account and change your password.
- Report the phishing page to M&T Bank’s fraud department (e.g., by forwarding the original message to
[email protected]or using their official reporting channels).
Why this scam is effective:
M&T Bank has millions of customers across the United States. The page closely mimics the design of the legitimate M&T Bank login interface, including the familiar header, form layout, and footer links. The typo in the copyright line (“MAT Bank”) is one of the few visual red flags—underscoring how carefully users must scrutinize every detail. Many users glance at the logo and layout without checking the URL or noticing small text errors.
Protective measures:
- Bookmark the official M&T Bank login page and use that bookmark to access online banking—never click links in emails or messages.
- Use a password manager: It will autofill only on legitimate
mtb.com - Enable two-factor authentication (2FA) on your M&T Bank account if available, to add an extra layer of protection.
- Be suspicious of any unsolicited message that creates urgency and asks you to log in to your bank account.
- Check the URL carefully: Legitimate M&T Bank domains end with
mtb.com - If in doubt, contact M&T Bank directly using a phone number from your bank statement or the official website—never use contact information provided in a suspicious message.
