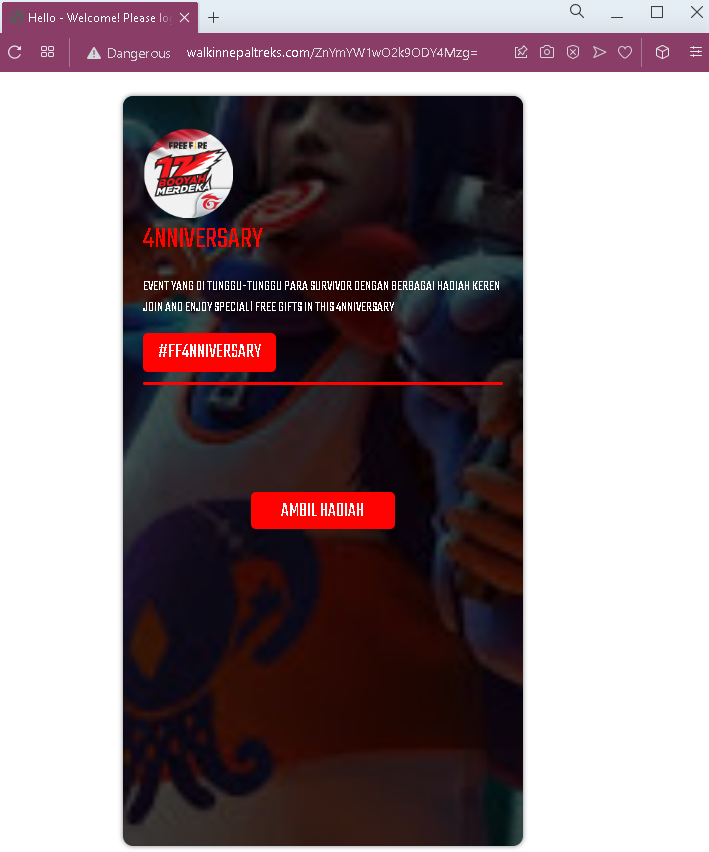
Free Fire “Rewards Generator” Scam – Facebook Credential Harvesting (Variant)
This phishing campaign targets Free Fire players by promising free in-game rewards (skins, diamonds, rare items) through a fake “generator” tool. The scam uses a multi-step process designed to steal victims’ Facebook login credentials, which are commonly used to access Free Fire accounts.
How it works:
The victim encounters a link to this scam via YouTube, TikTok, Discord, Instagram, or other social media platforms with enticing claims of free rewards.
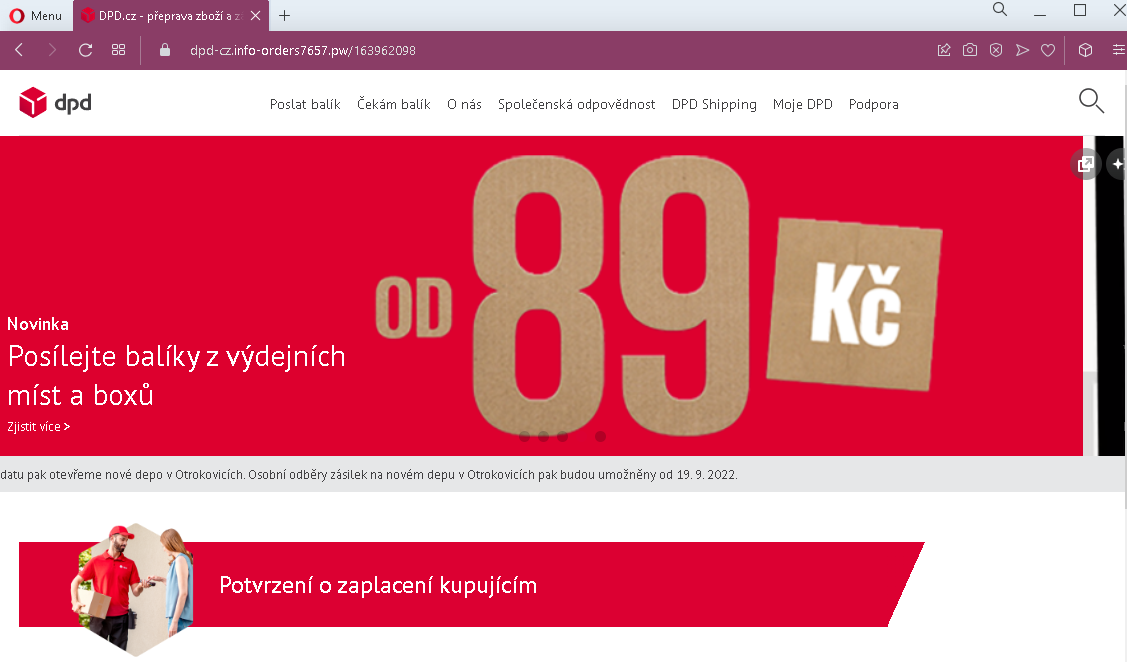
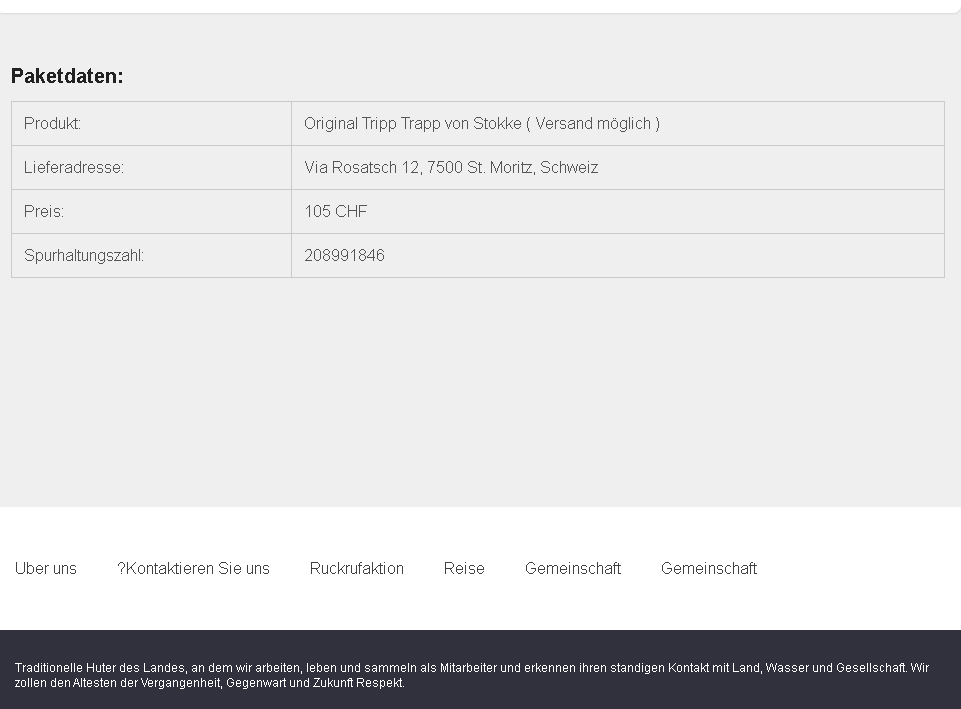
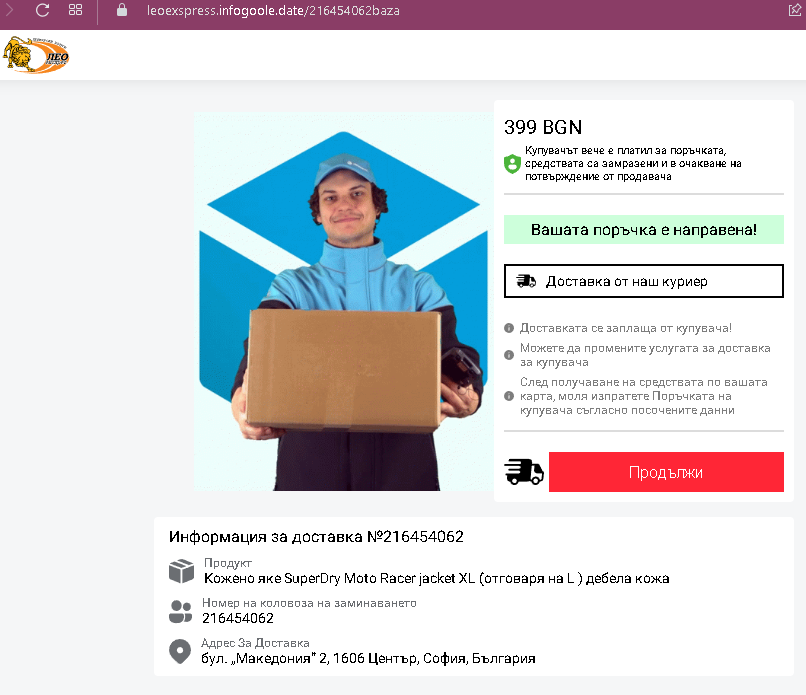
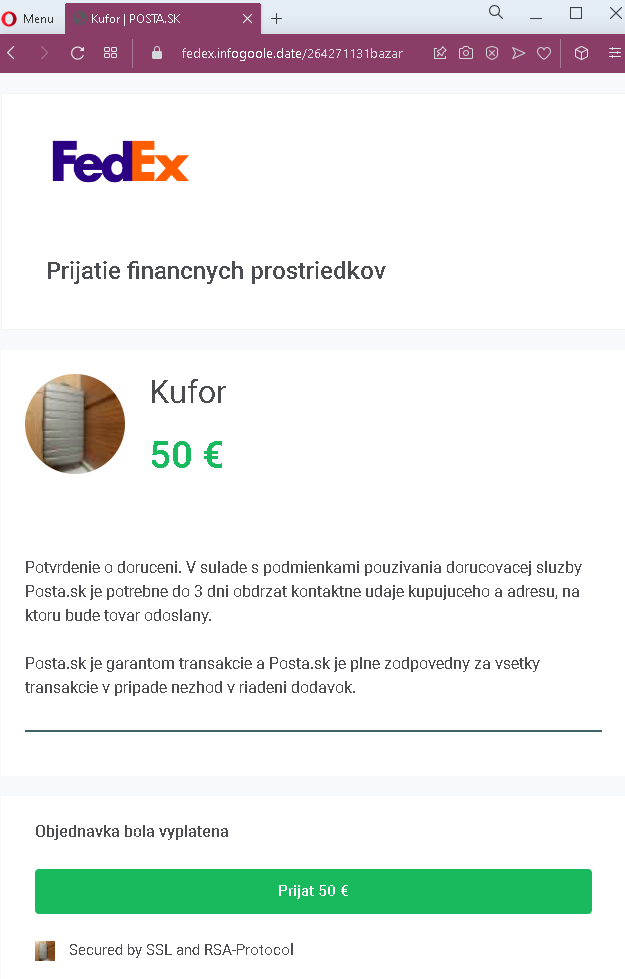
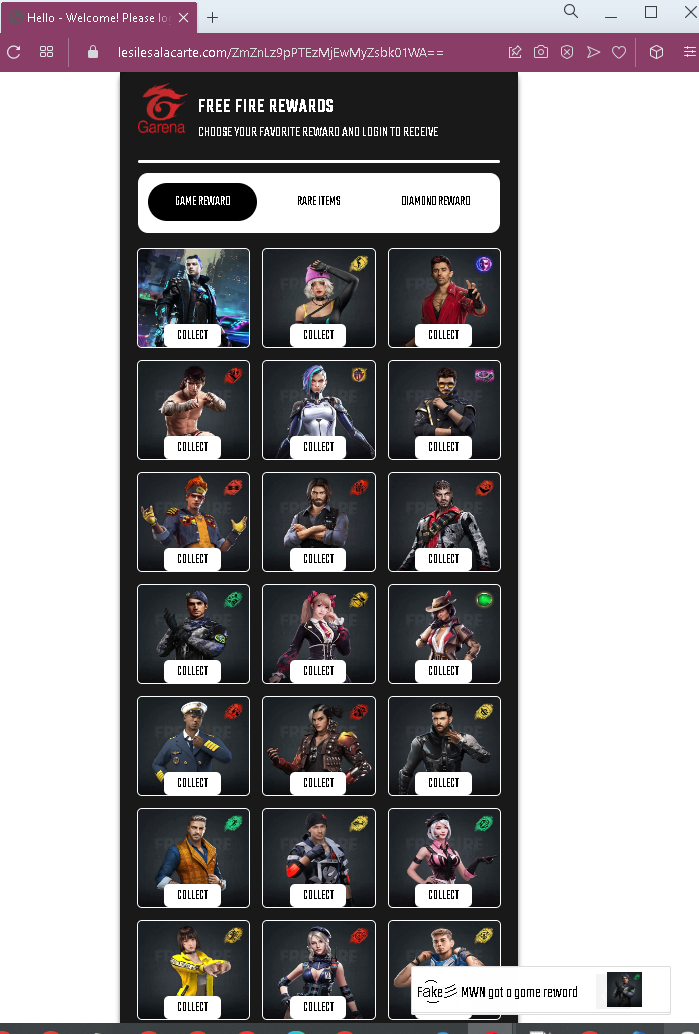
Step 1 – Reward Selection Page (First Screenshot)
The victim lands on a page displaying numerous reward icons (weapons, skins, items) with “COLLECT” buttons. The page includes:
A suspicious URL: lesilesalacarte.com/… (not associated with Garena)
Text indicating “Fake ⬆ MWM got a game reward” (likely a tester’s note)
Garena branding to appear legitimate
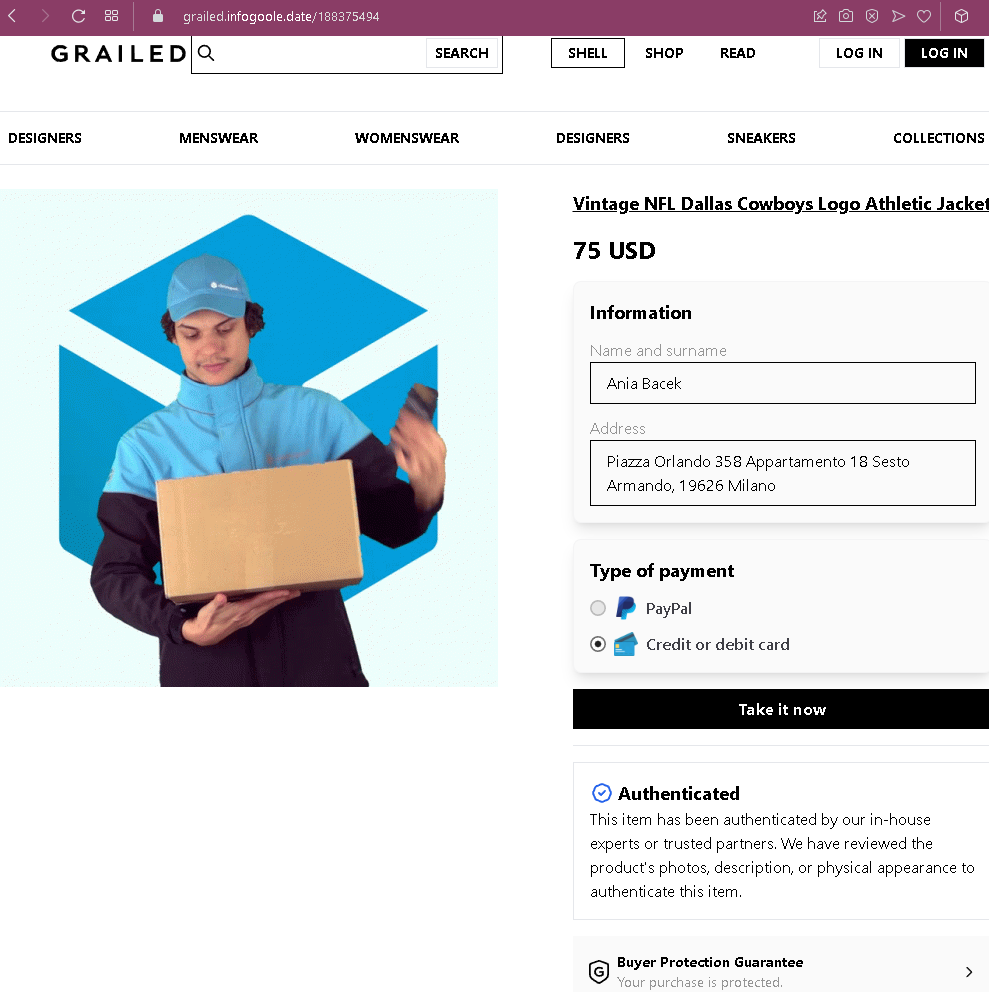
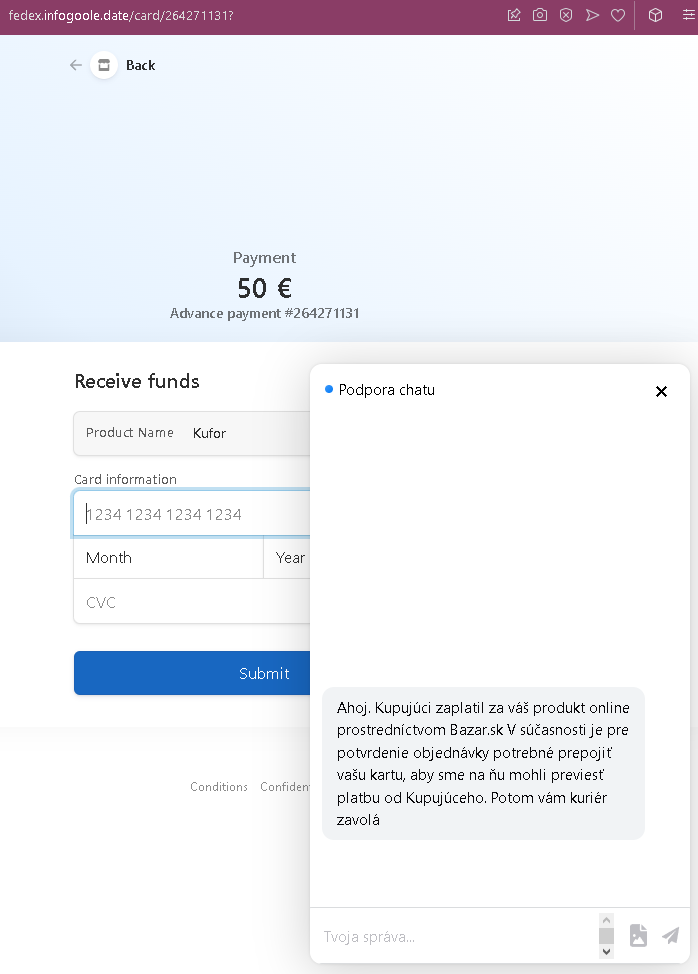
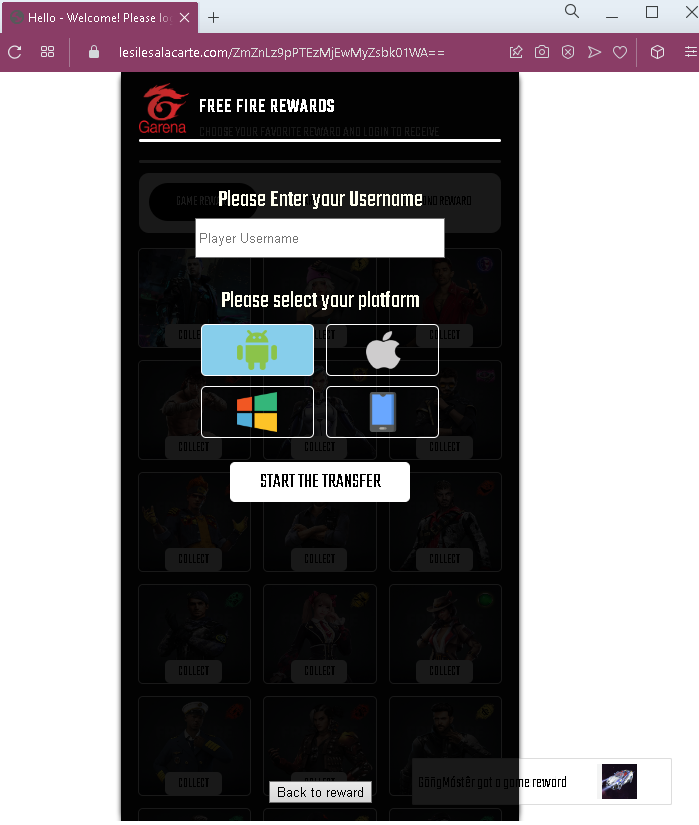
Step 2 – Username & Platform Entry (Second Screenshot)
The victim is asked to:
Enter their Player Username (Free Fire in-game name)
Select their platform
Click “START THE TRANSFER”
This step collects basic information and creates the illusion of a personalized reward delivery.
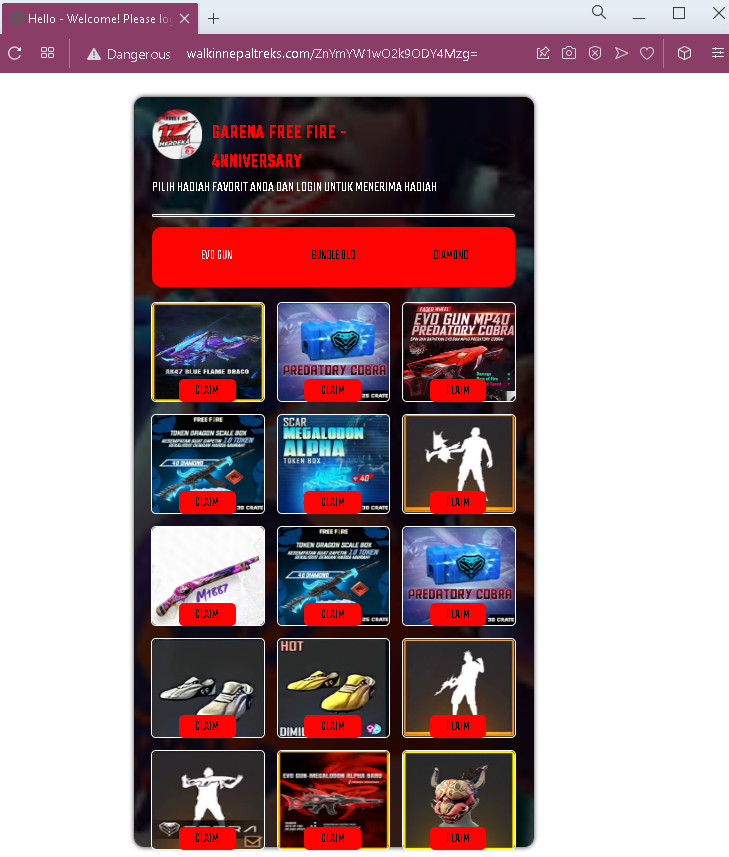
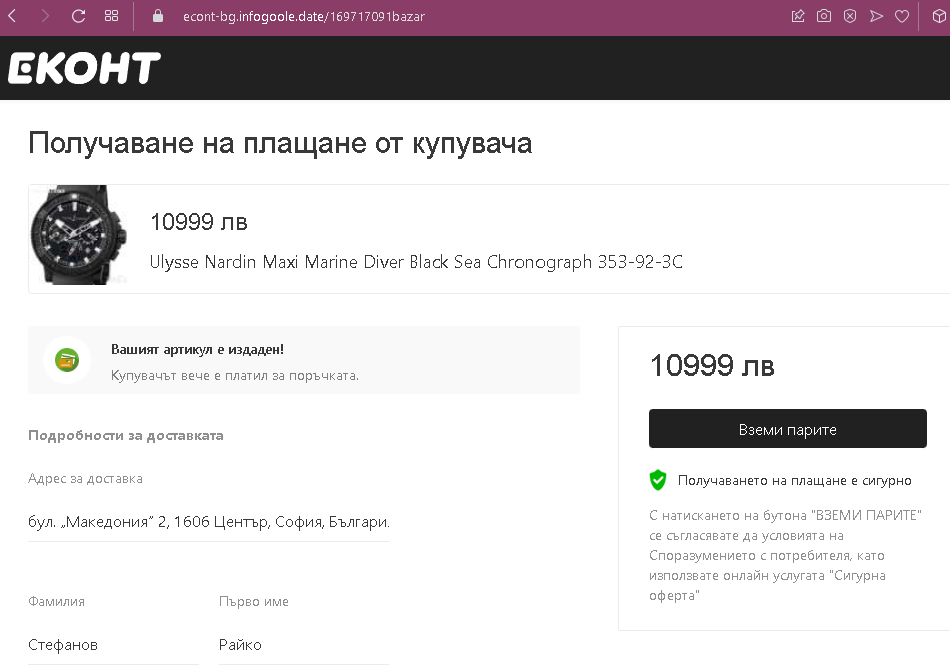
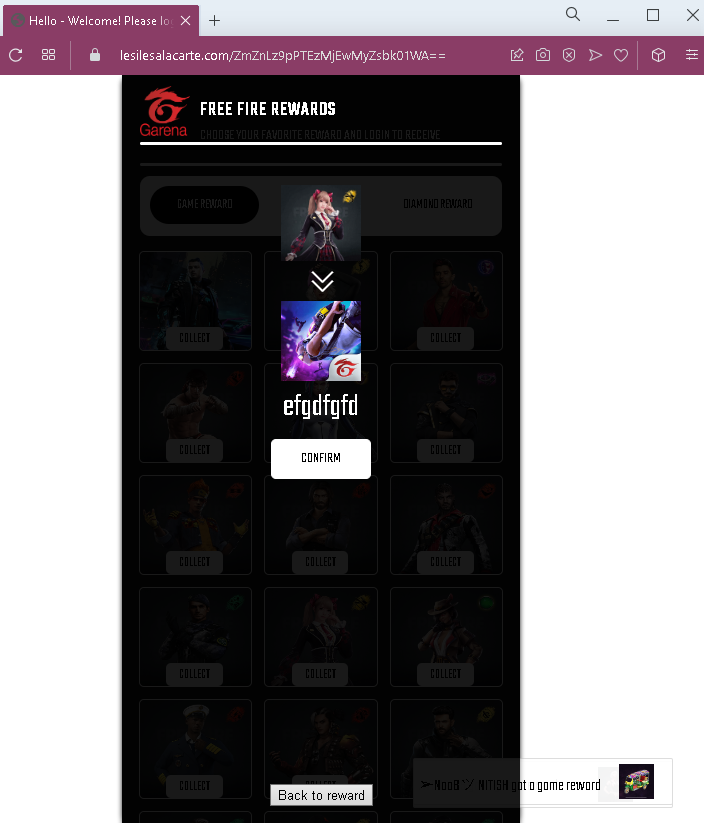
Step 3 – Reward Confirmation (Third Screenshot)
After entering credentials, the victim sees another page filled with reward icons and “COLLECT” buttons. This reinforces the belief that rewards are ready to be claimed. A “Back to reward” link allows navigation, but all paths lead to the verification trap.
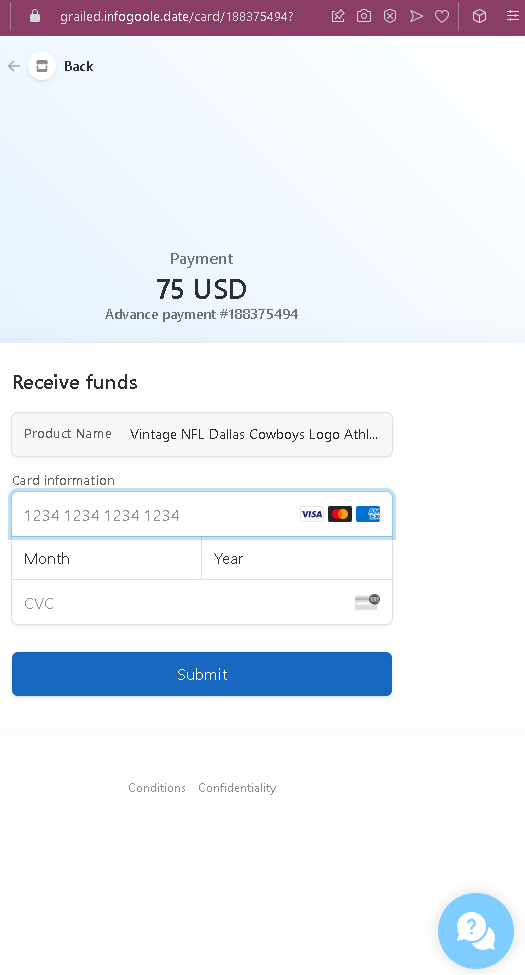
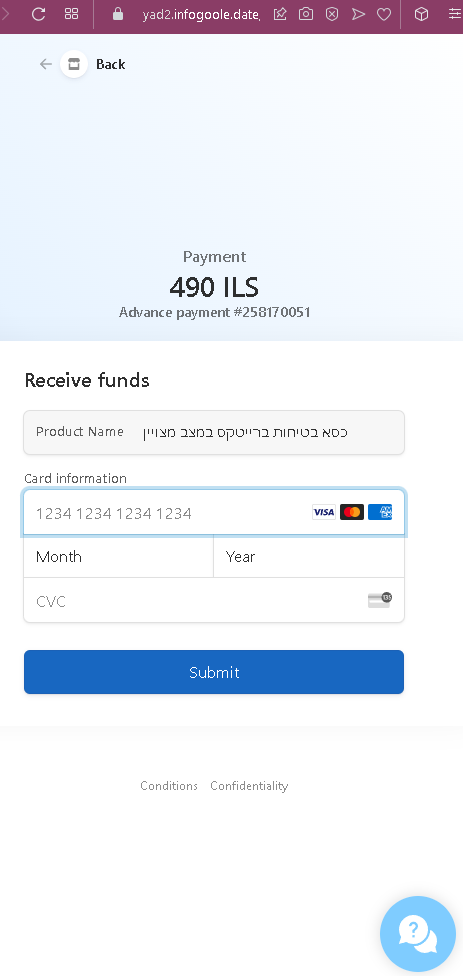
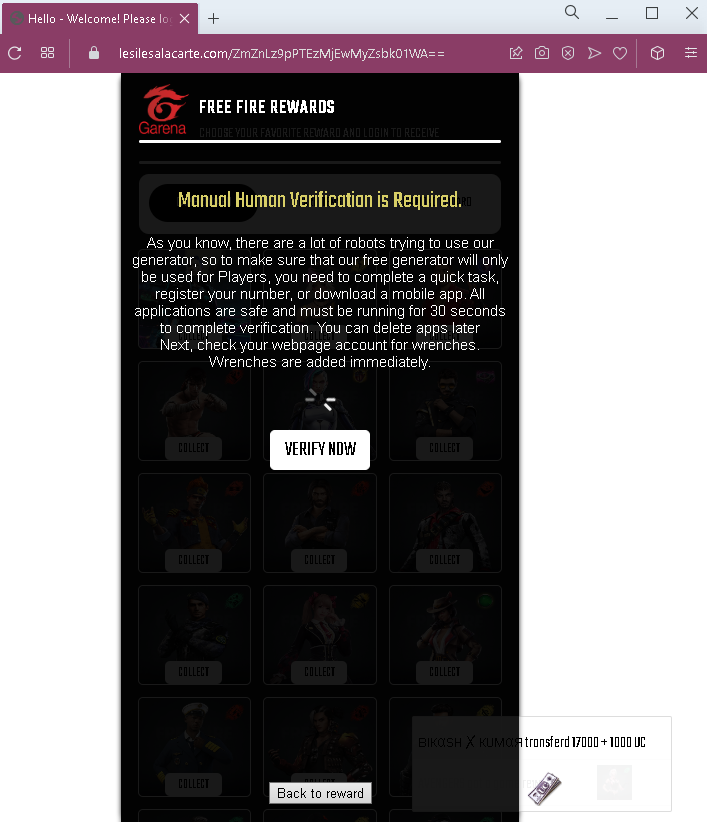
Step 4 – “Manual Human Verification” Requirement (Fourth Screenshot)
This page claims:
“Manual Human Verification is Required.”
Explanation: many robots try to use the generator, so to prove the user is human, they must complete a “quick task” (register a phone number or download a mobile app).
The instructions claim: “All applications are safe and must be running for 30 seconds to complete verification. You can delete apps later.”
This is a classic social engineering tactic to convince victims to complete the next step.
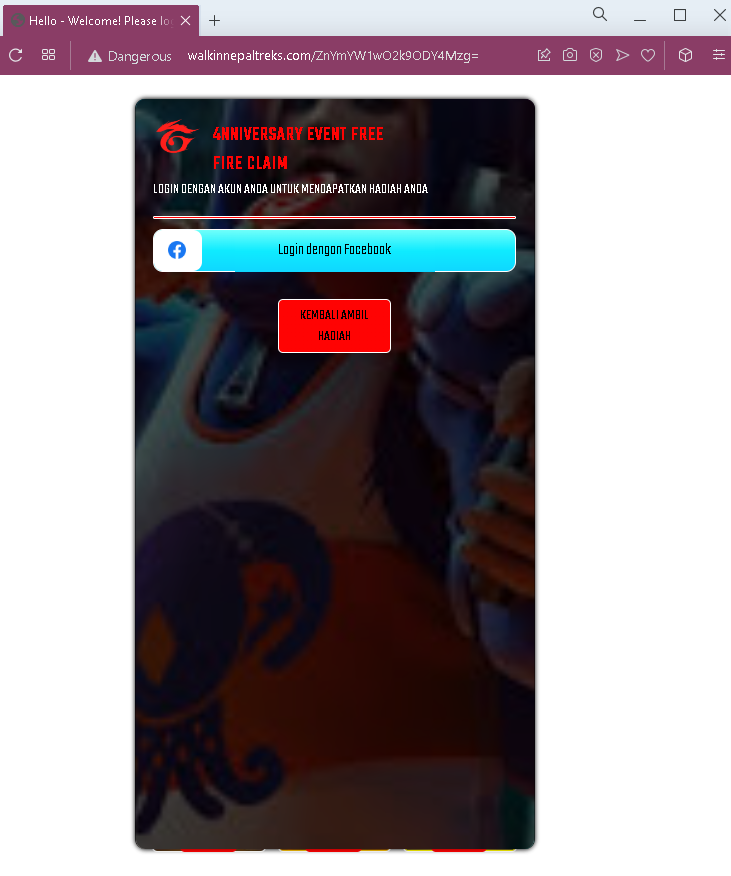
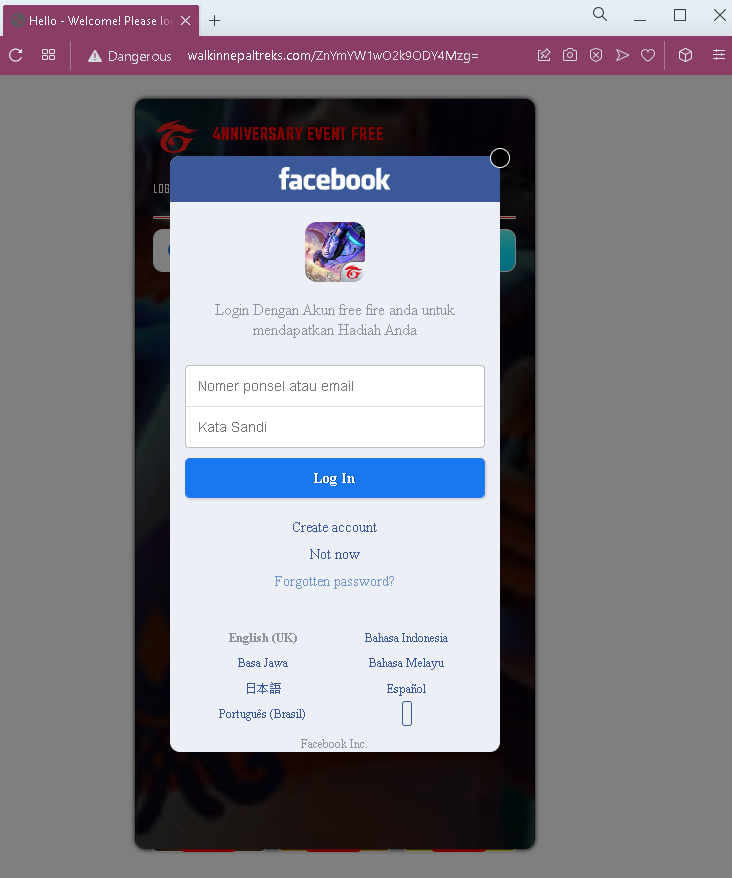
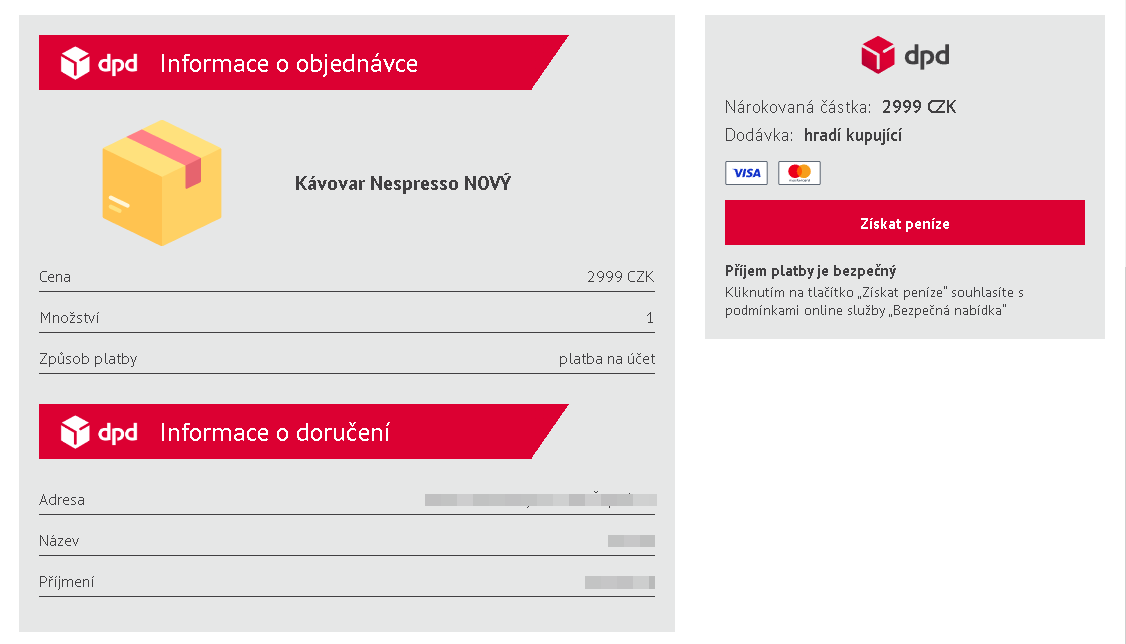
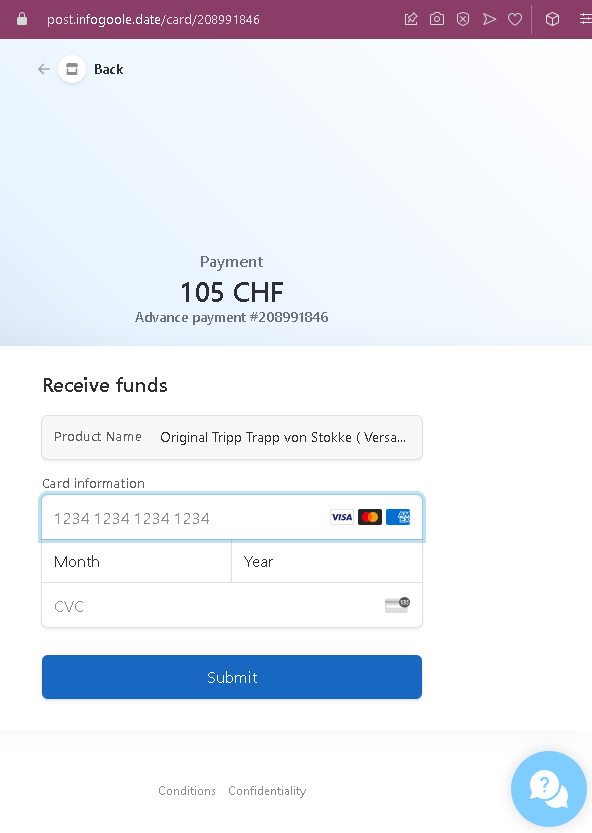
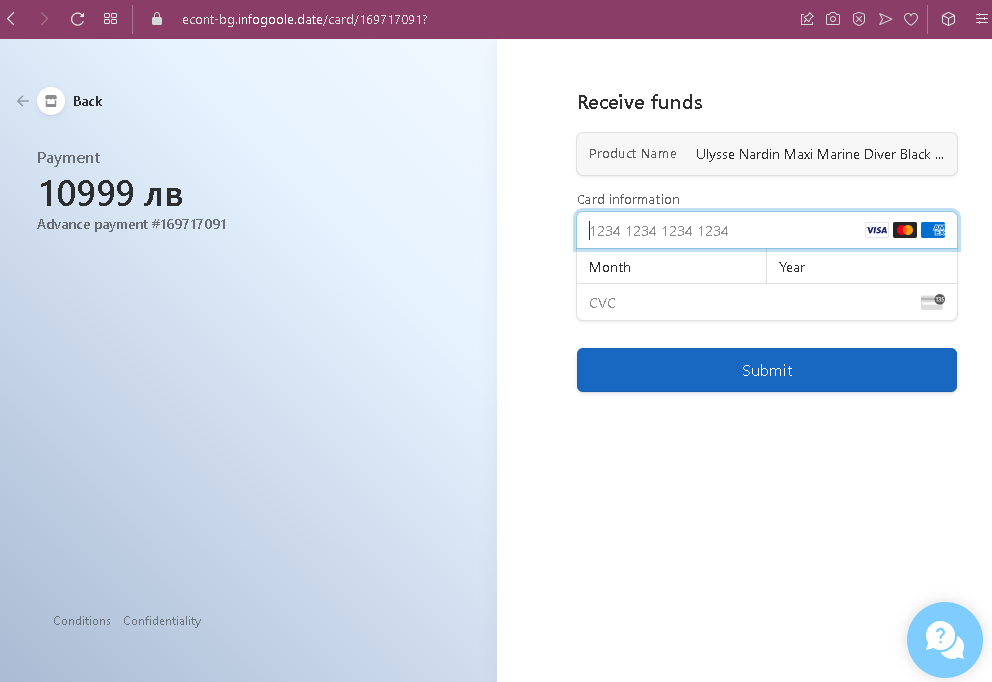
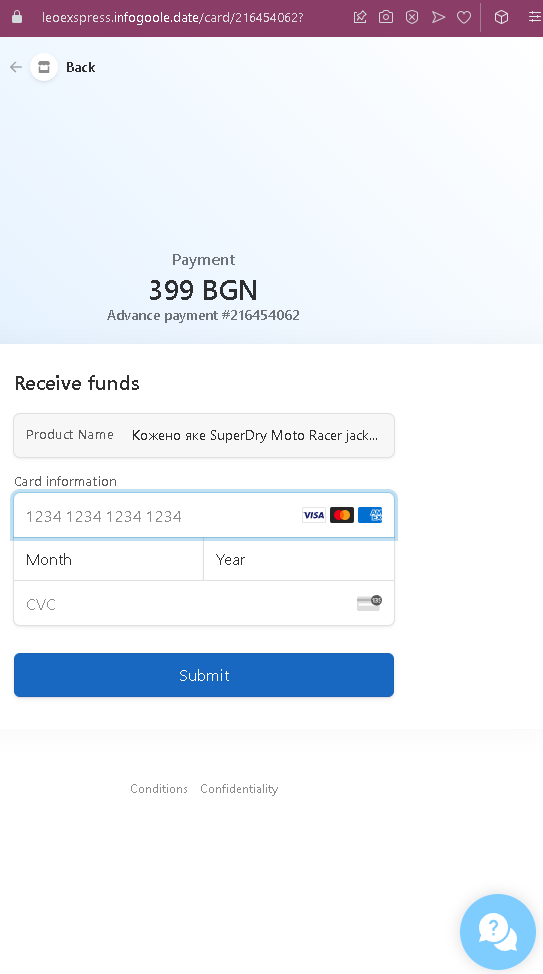
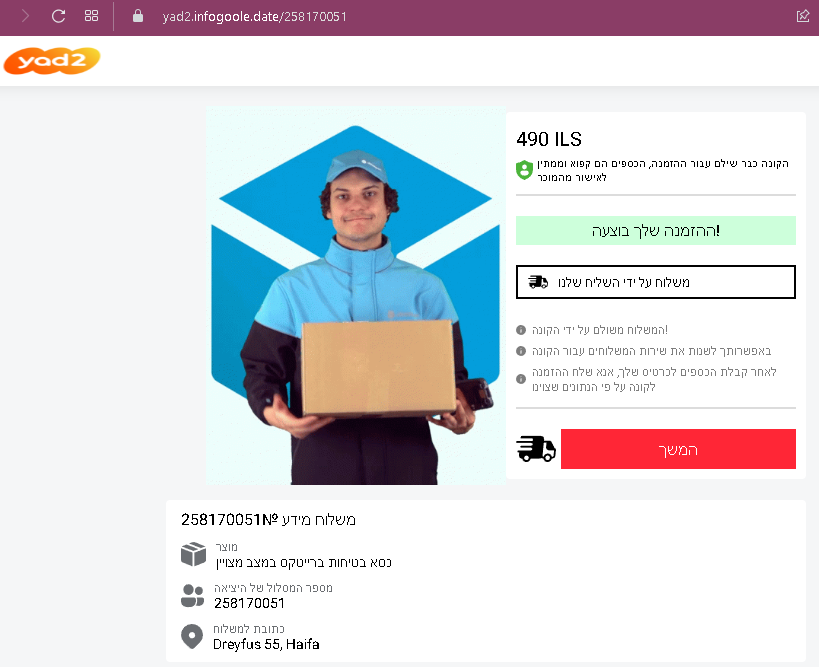
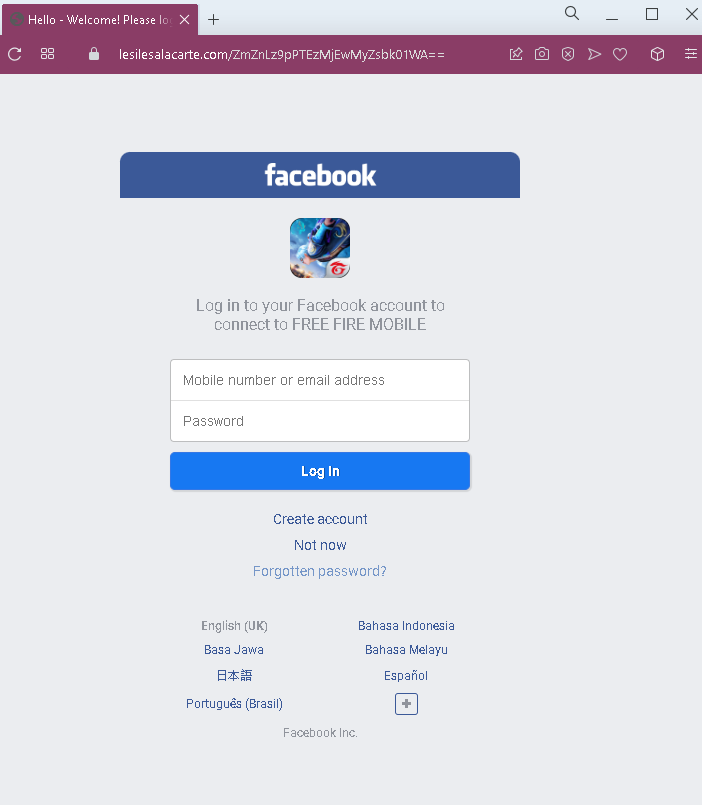
Step 5 – Facebook Login Phishing Page (Fifth Screenshot)
The “VERIFY NOW” button leads to a fake Facebook login page. This page asks for:
Mobile number or email address
Password
The page mimics Facebook’s mobile login interface and includes multiple language options to appear authentic.
The goal:
The attacker steals the victim’s Facebook credentials. Since Free Fire accounts are often linked to Facebook, this grants the attacker access to both the Facebook account and the associated Free Fire game account. Attackers can then:
Steal or sell the Free Fire account (including any purchased items or progress)
Access personal information on Facebook
Use the compromised Facebook account to spread the scam to the victim’s friends
Red flags to watch for:
“Too good to be true” offer: No legitimate service provides free in-game currency or rare items through an external website. Garena sells diamonds and items only through official channels.
Suspicious URL: The initial page is hosted on lesilesalacarte.com, a domain completely unrelated to Garena (garena.com) or Free Fire.
No official branding consistency: While the pages use the Free Fire and Garena names, they lack official logos, copyright notices, and professional design elements.
“Human verification” scam pattern: The requirement to “verify” by completing a task (phone registration, app download) is a classic phishing tactic. No legitimate game reward system uses such methods.
Facebook login request: The final step asks for Facebook credentials. Legitimate in-game rewards never require logging into Facebook through a third-party site.
Multiple “COLLECT” buttons: The repetitive design is meant to overwhelm the user and create a sense of abundance, but it is unprofessional and inconsistent with official Garena interfaces.
“Back to reward” loop: The navigation allows users to go back, but all paths eventually lead to the same phishing request.
What to do if you encounter this:
Do not enter your Free Fire username, select a platform, or click any “COLLECT” or “START THE TRANSFER” buttons.
Do not complete any “human verification” tasks, especially those asking for phone numbers or app downloads.
Do not enter your Facebook email/phone and password on the final page.
If you have already entered your Facebook credentials, change your Facebook password immediately, enable two-factor authentication (2FA), and check for any unauthorized activity.
Report the phishing page to Facebook and to Garena (Free Fire’s developer).
Why this scam is effective:
Free Fire has a massive global player base, especially among younger audiences who may be more susceptible to offers of free premium content. The multi-step process with multiple reward icons and the “human verification” explanation makes the scam appear legitimate and elaborate. The use of Facebook as the final credential harvest is strategic—once attackers have Facebook access, they can compromise the game account and potentially spread the scam further.
Protective measures:
Never trust third-party “generators” or “hacks” that promise free in-game currency or items. They are always scams.
Enable two-factor authentication (2FA) on your Facebook account to prevent unauthorized access even if your password is stolen.
Log into Free Fire only through the official app and official Garena methods.
Educate younger gamers about these scams, as they are frequently targeted through social media platforms.