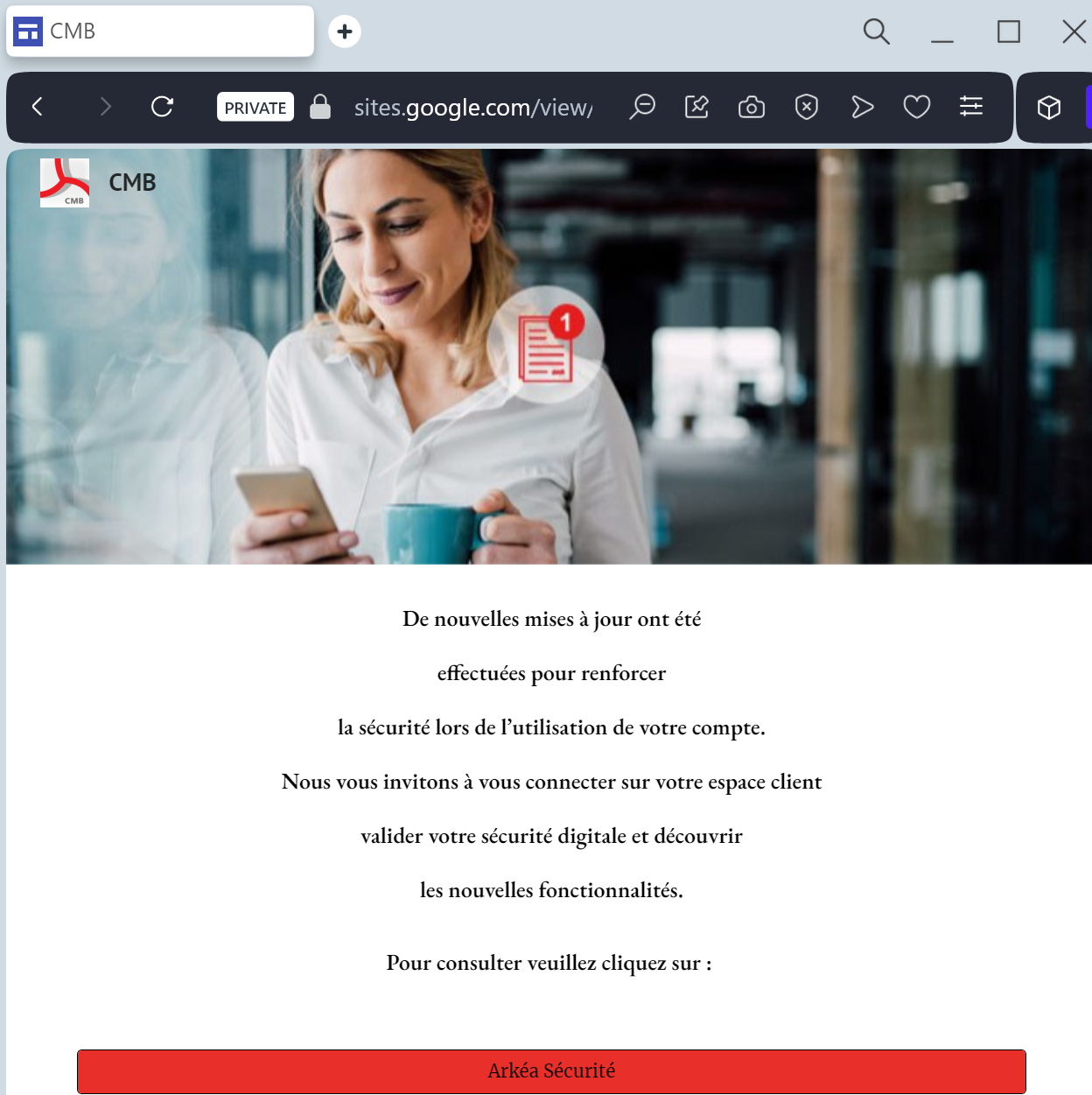
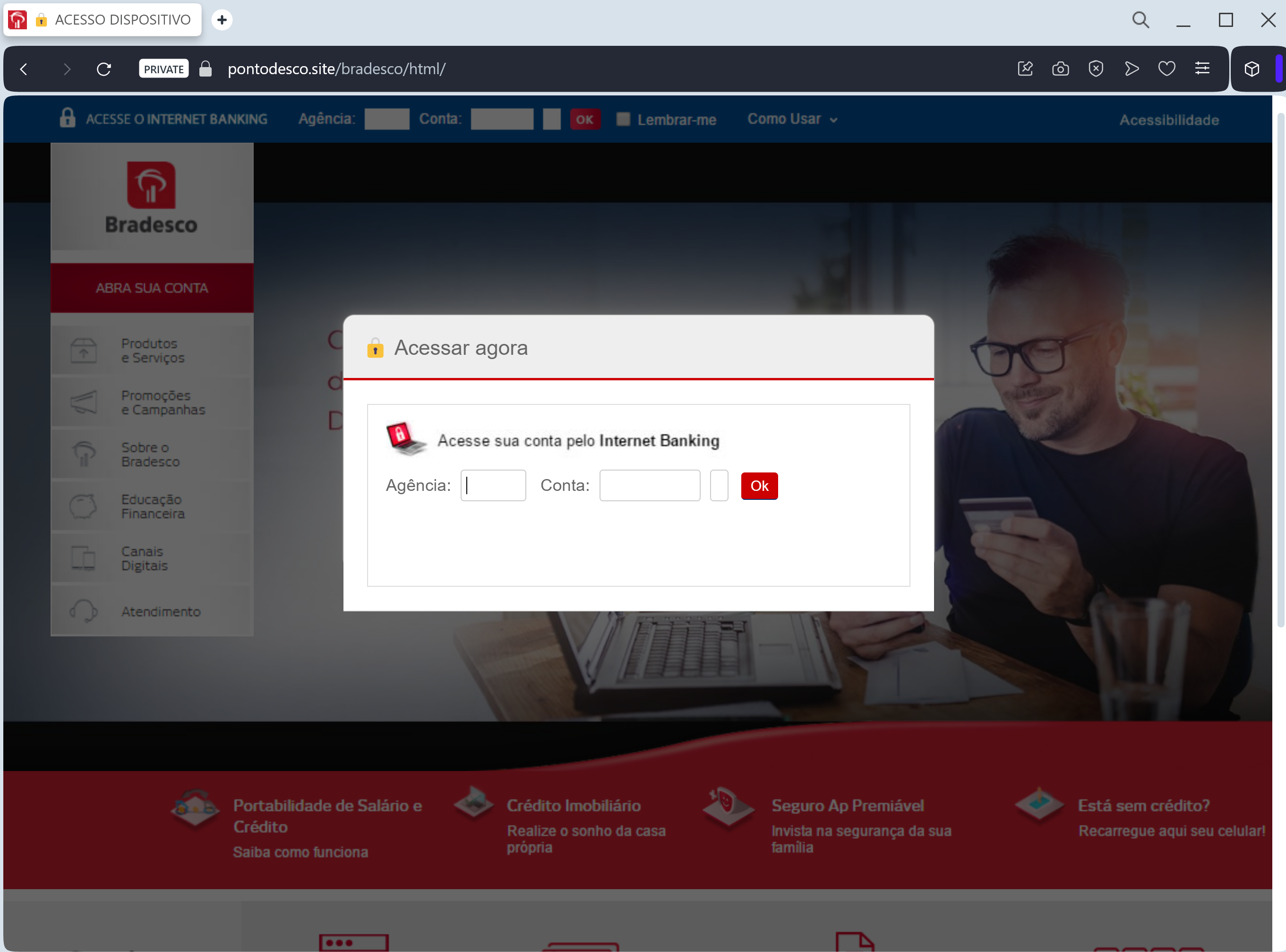
A sophisticated Banco Bradesco phishing campaign targeting Brazilian users through fake “security re-registration” messages to steal account credentials and security tokens in real time. This critical-level threat employs lookalike domains and smishing to intercept Agency/Account numbers, PINs, CPF numbers, and mobile token codes for full account takeover.
метода фишинга на основе скриншота? Чтобы люди были осведомлены, предупреждены, и не попались на обман.
A high-severity phishing campaign targeting Banco Bradesco customers in Brazil uses fraudulent “Security Key Update” alerts to steal login credentials and security tokens (Chave de Segurança) in real-time, enabling account takeovers. Attackers distribute malicious links via SMS or WhatsApp, leading to phishing sites that clone the official Bradesco portal to harvest Agência, Conta, and Token Digital codes. Users should avoid clicking links, verify URLs, and only manage accounts through the official Bradesco app, as the bank never requests security tokens for profile updates.
This Banco Bradesco phishing case highlights a sophisticated Man-in-the-Middle (MitM) attack designed to intercept security tokens in real-time, bypassing multi-factor authentication for full account hijacking. The attack uses SMS/email lures directing users to a fake portal, demanding a 6-digit ‘Chave de Segurança’ to authorize fraudulent PIX transfers immediately.
Expert Security Tip: Real-time token hijacking often involves scammers using stolen credentials to log into the legitimate banking site while the user is on the fake site, using the provided token to approve unauthorized actions. Never provide security token codes on websites reached through external links; treat any prompt for a token during login as an active phishing attempt.