This phishing campaign targeting Ecuador’s Banco del Pacífico uses a fake “Intermático Security Sync” page to steal online banking credentials, security challenge questions, and One-Time Passcodes (OTP). Scammers employ a “sync” pretext in emails or SMS, directing victims to a malicious website that mimics the legitimate site to bypass multi-factor authentication and gain full account control. For protection, users must always access banking services by manually typing the official URL and never enter credentials through links provided in messages.
Incident Report: This spoofed page was logged, cross-checked, and neutralized firsthand by the Antiphishing.biz security team during our daily link moderation procedures. To protect the public, the dangerous destination URL has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
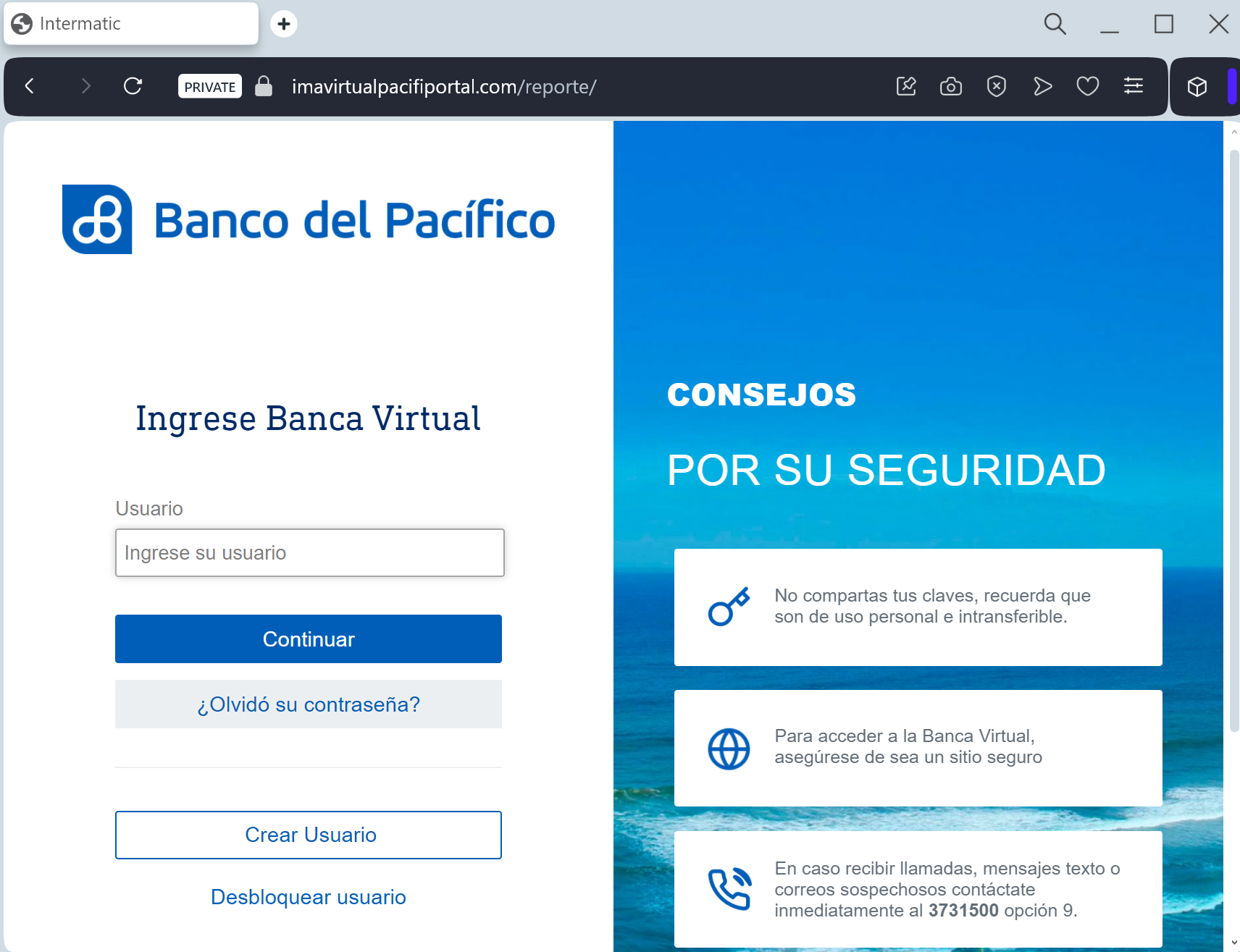
This phishing case highlights a sophisticated Real-Time Token Interception attack, where attackers use a fake Banco del Pacífico portal to steal credentials and prompt for 6-digit OTP security codes in real-time. By acting as a live “middleman,” the attacker uses the intercepted code to authorize fraudulent transfers or register a new device instantly, rather than just stealing credentials for later use.
Expert Security Tip:
Real-Time Session HijackingIf a website asks for a Token/OTP code immediately after you log in, and you have not initiated a transfer, it is a major red flag indicating a scam. Always type the official bank URL directly into your browser, as Banco del Pacífico will never ask for security tokens to “verify” your profile via an email or SMS link.
