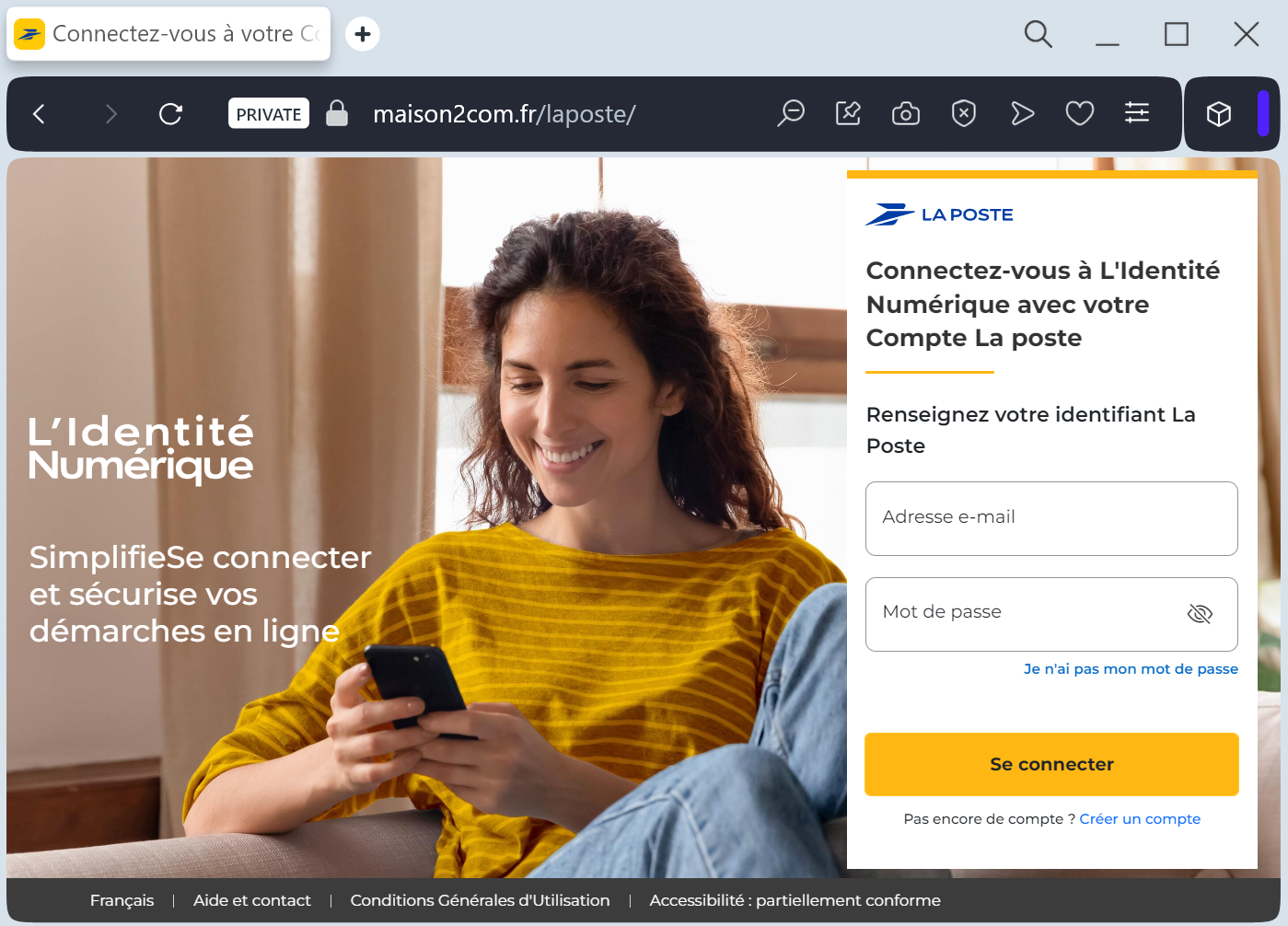
A phishing campaign targeting La Poste customers in France uses “address confirmation” scams to harvest full credit card details and bypass 3D-Secure protections [1]. Attackers utilize SMS and emails prompting a small fee to lead victims to cloned sites, stealing credentials and real-time security codes.
Security Notice: This malicious interface was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our automated link scanning workflows. To protect the public, the dangerous destination URL has been fully defanged within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
This phishing campaign targeting BAC Credomatic users in Central America employs SMS and email threats to force victims to a fake “Banca en Línea” portal. The attack, which impersonates “Codigo BAC” synchronization, is designed for real-time hijacking of user credentials and 2FA tokens to perform unauthorized transactions.
Key Defense Information
- Method: Scammers act as a middleman to steal username, password, and the 6-digit security token (Codigo BAC) in real-time.
- Warning Signs: Urgent language threatening account suspension and links to deceptive, non-official domains (e.g.,
sucursal-bac-seguridad.com). - Protection: Always manually type ://
baccredomatic.comin the browser and never enter your security token on sites reached via links [1].
This BAC Credomatic phishing case demonstrates a real-time proxy attack where attackers act as a middleman to intercept 6-digit Codigo BAC security tokens in real time. By tricking users into entering this token, scammers authorize fraudulent transactions or register new devices immediately, highlighting that two-factor authentication can be bypassed if the user provides the code directly to the threat actor.
