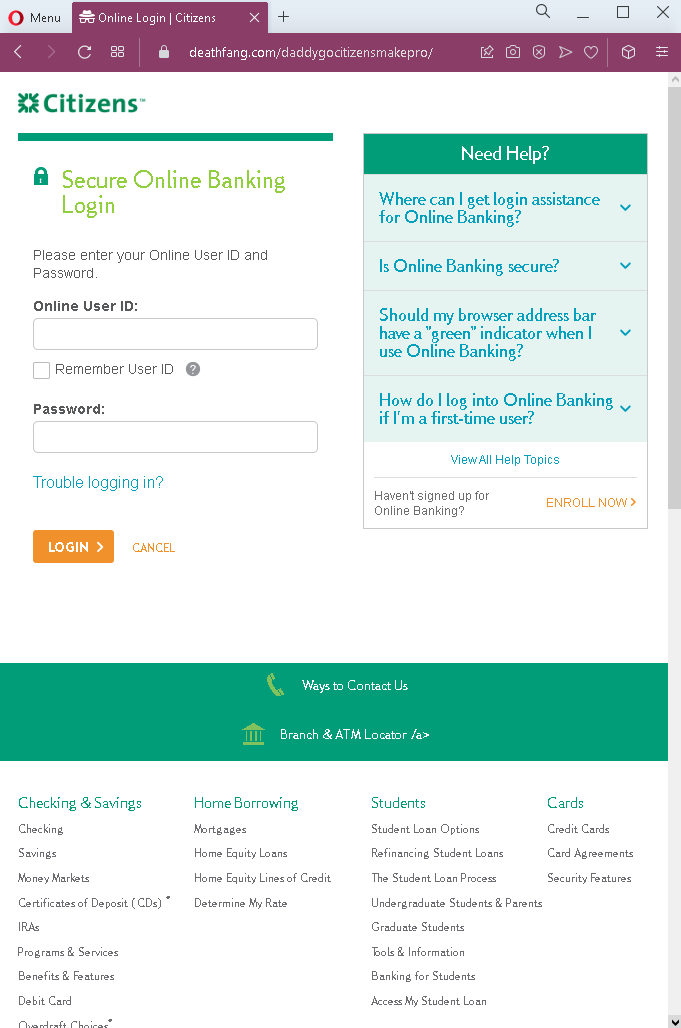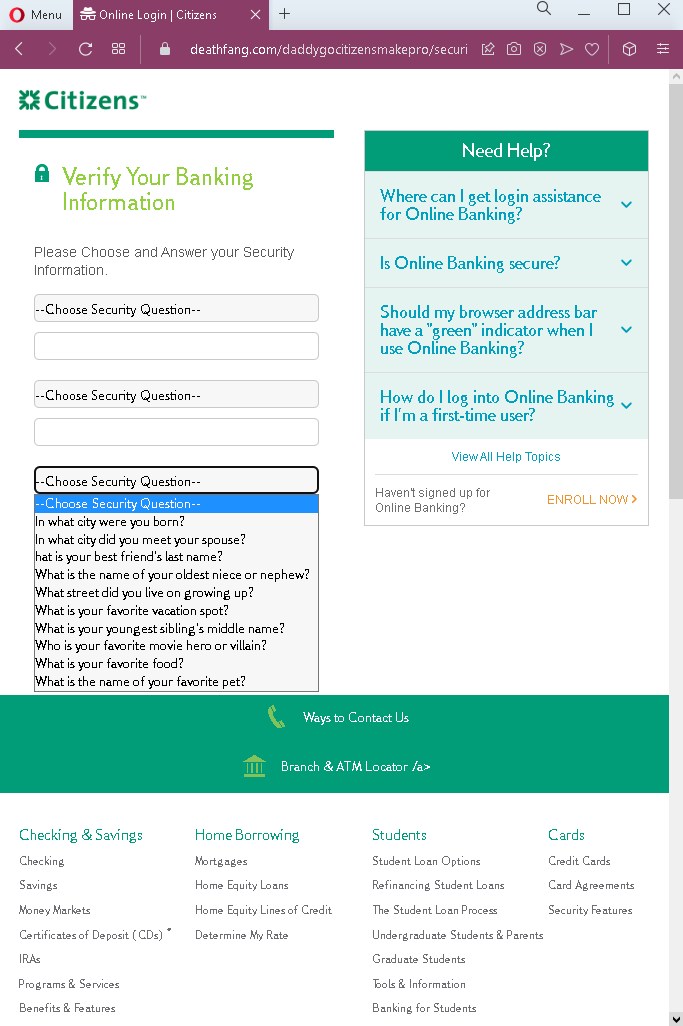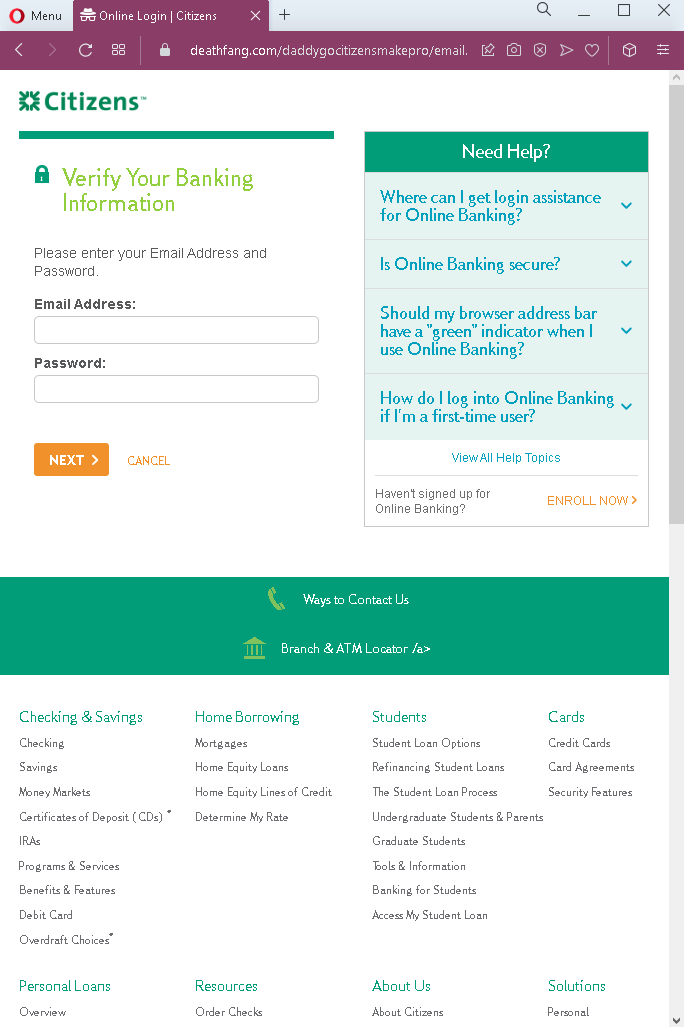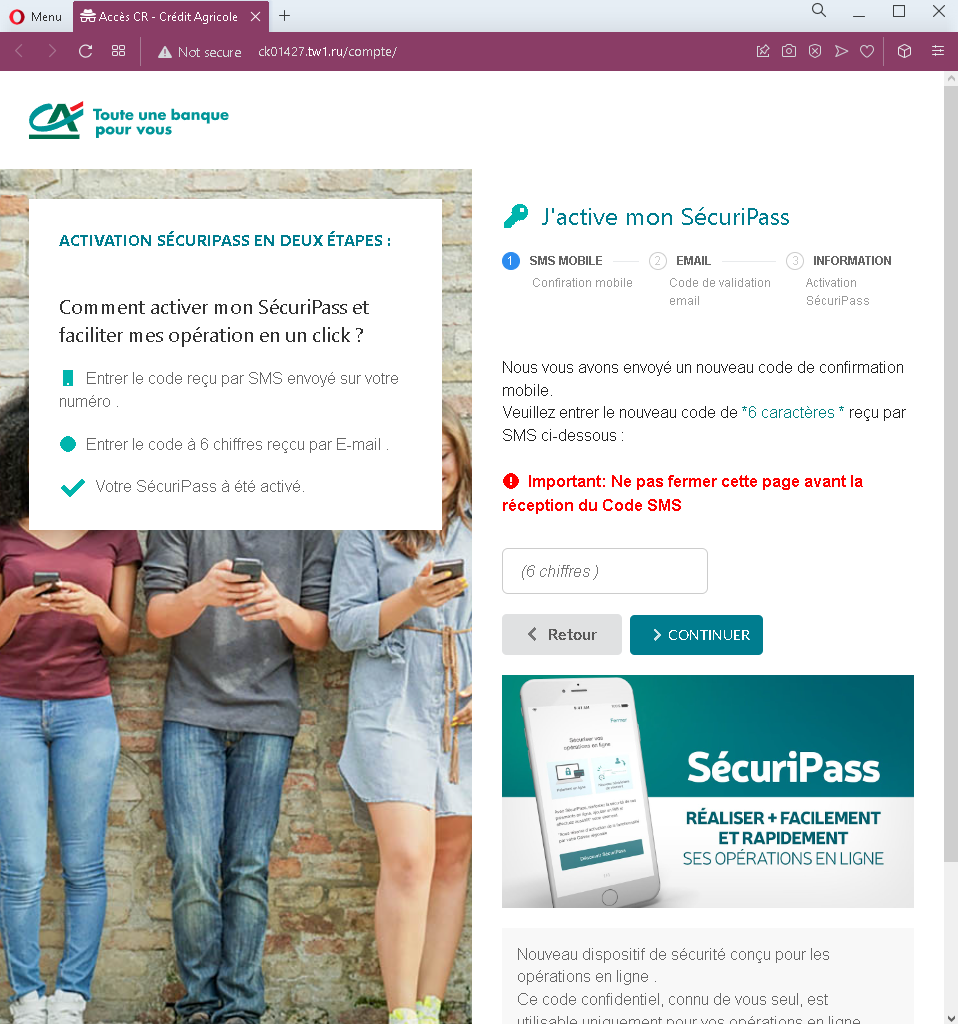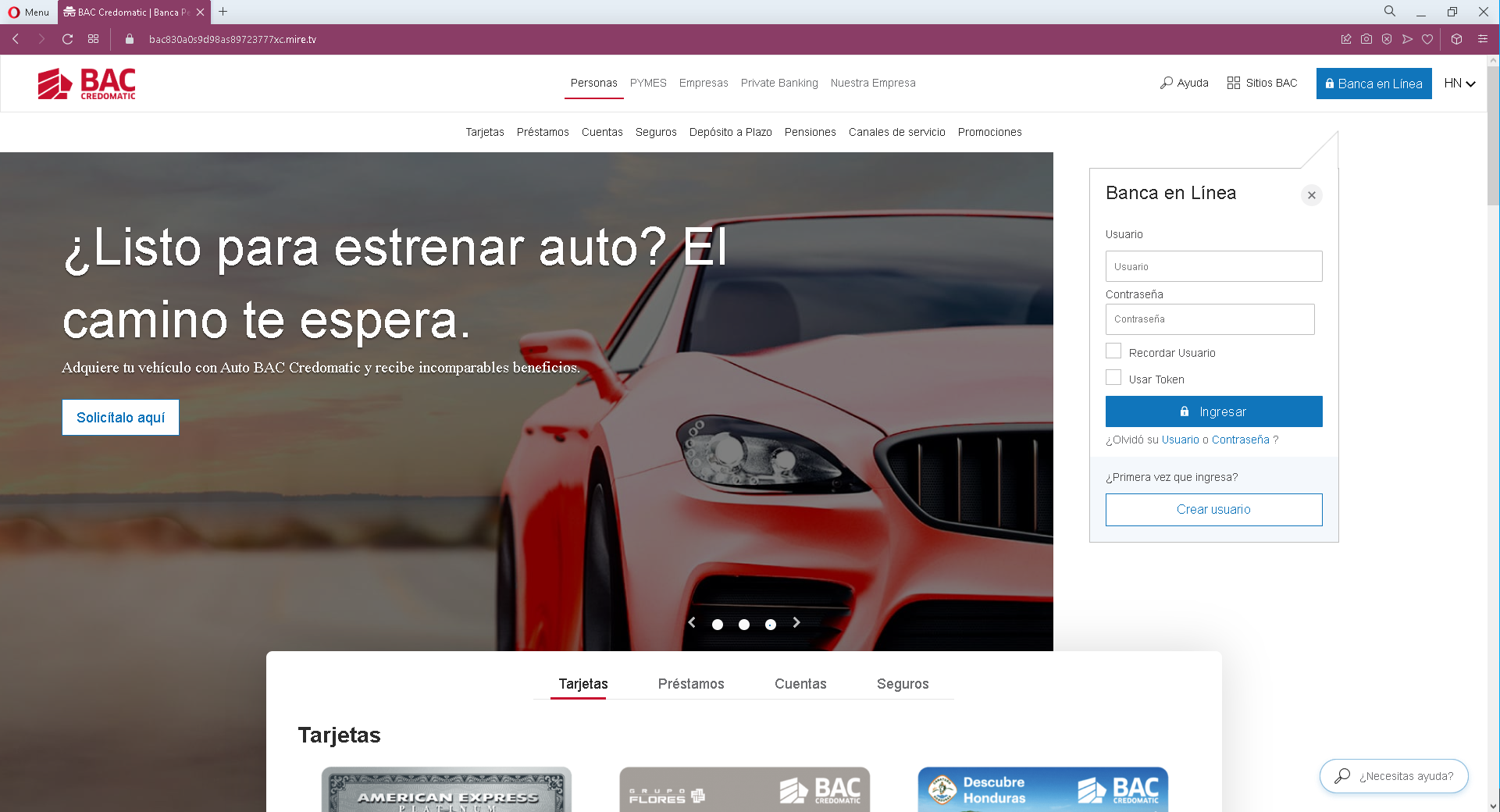
Threat Analysis: Nickel Phishing – Fake “Sponsorship” Offer Stealing Card Details
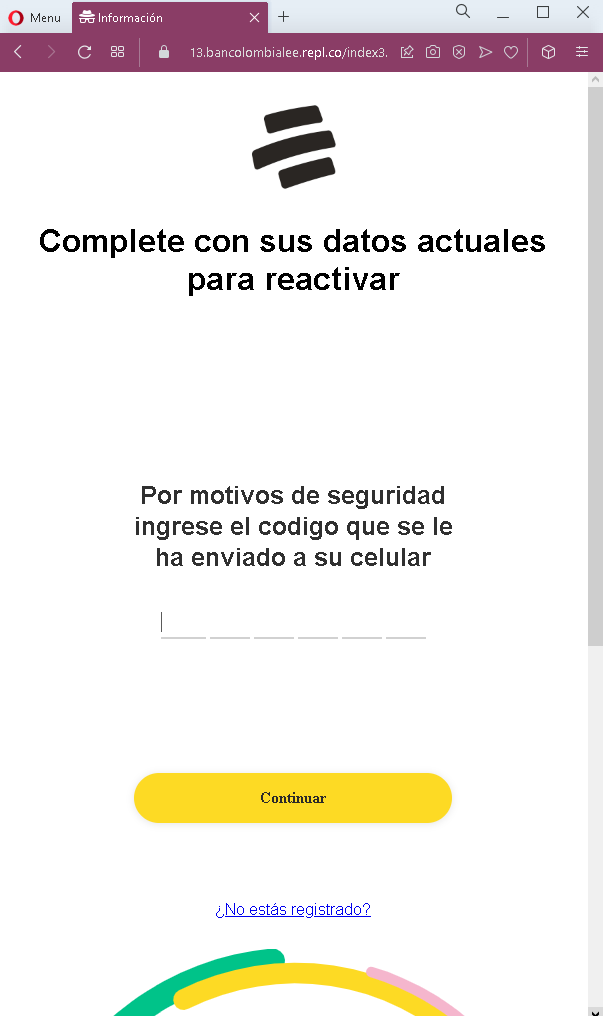
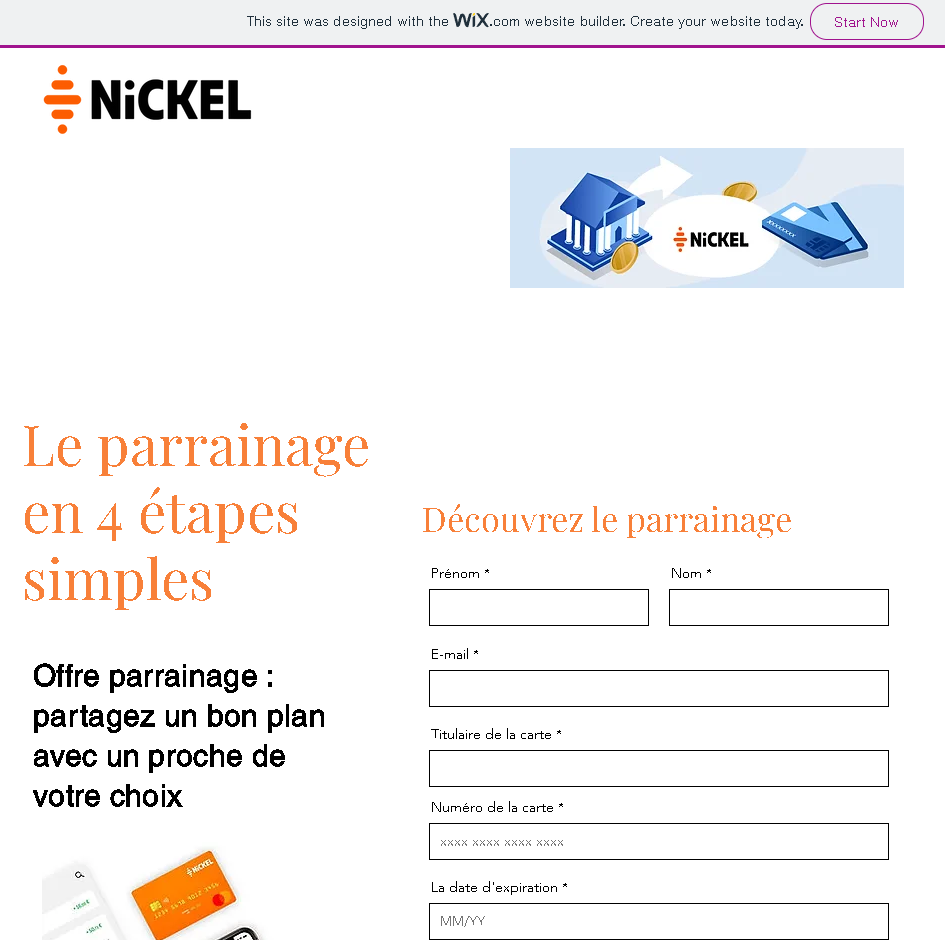
This phishing campaign impersonates Nickel, a French neobank (a subsidiary of BNP Paribas). The scam uses a fake “parrainage” (referral/sponsorship) offer to lure victims into providing their personal information and full card details under the guise of participating in a rewards program.
How it works:
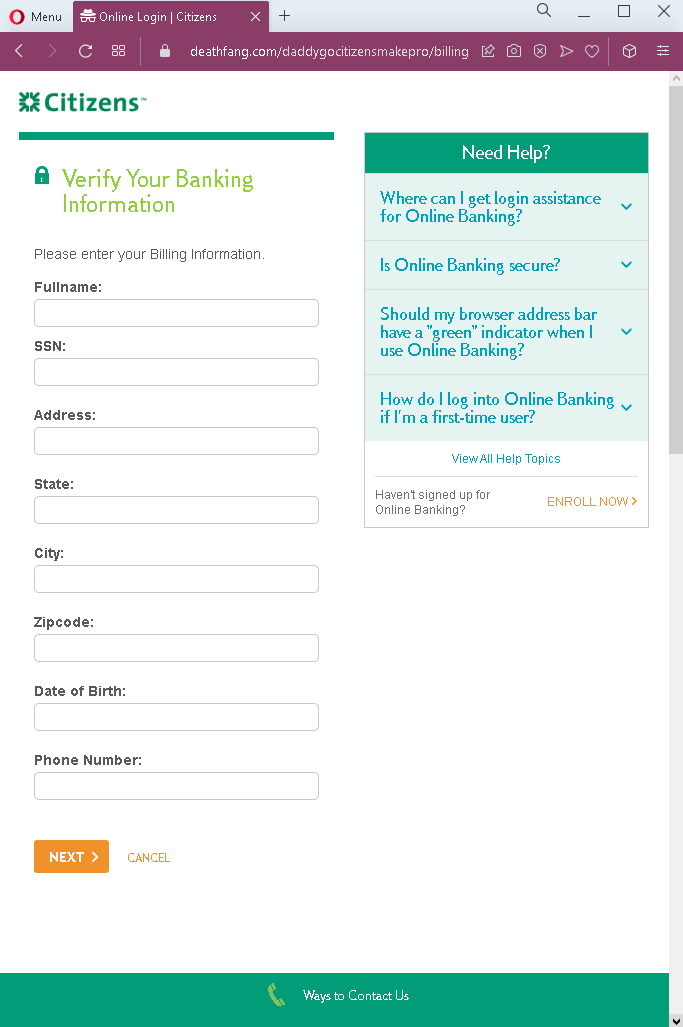
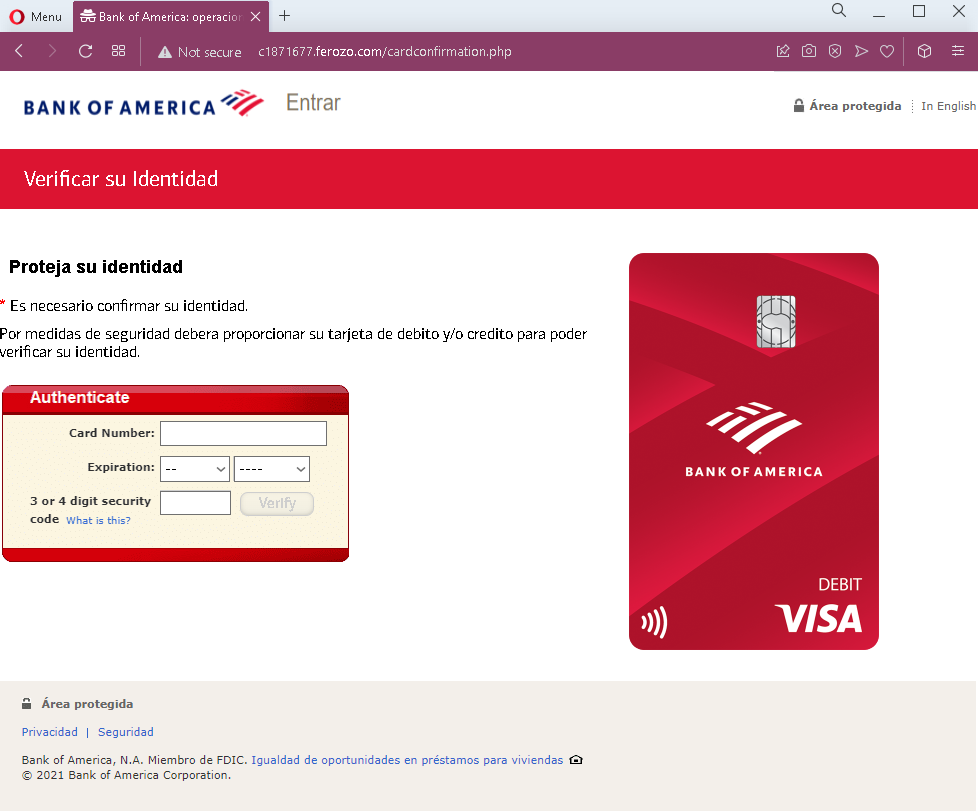
The victim encounters this page via a phishing email, SMS, social media post, or other message promoting a lucrative “sponsorship” offer from Nickel. The page claims to offer a reward for referring a friend. To participate, the victim is asked to enter:
- First name and last name
- Email address
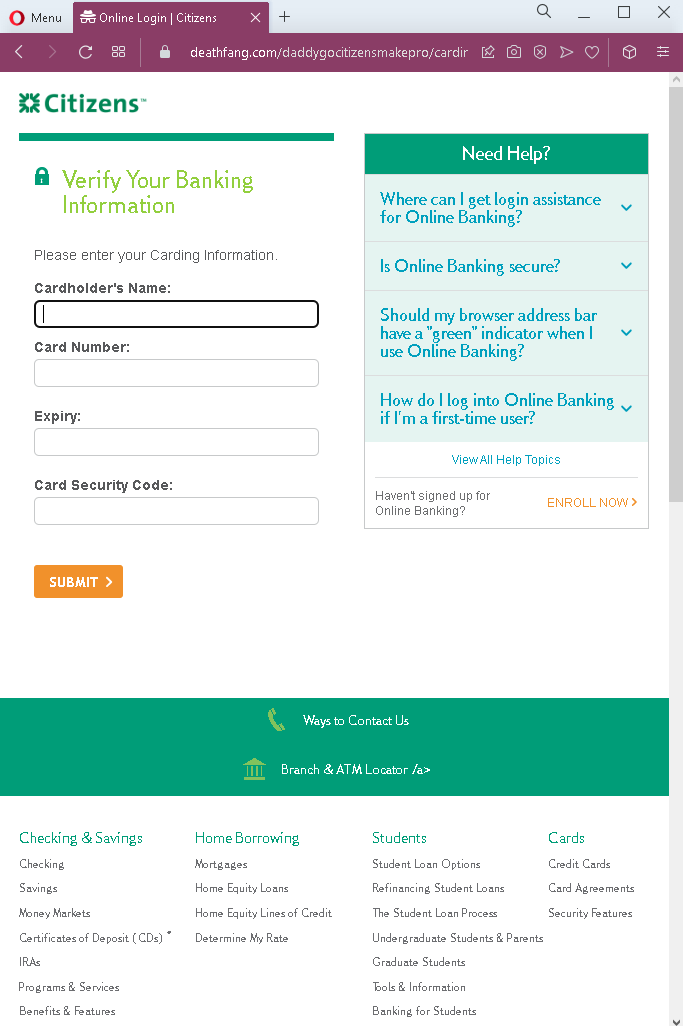
- Cardholder name
- Full card number
- Expiration date (MM/YY)
The goal:
The attacker aims to:
- Steal the victim’s full card details (card number, cardholder name, expiration date)
- Obtain the victim’s email address and full name for identity theft or further attacks
With the card details, the attacker can make unauthorized online purchases, create cloned cards, or sell the information on criminal marketplaces.
Red flags to watch for:
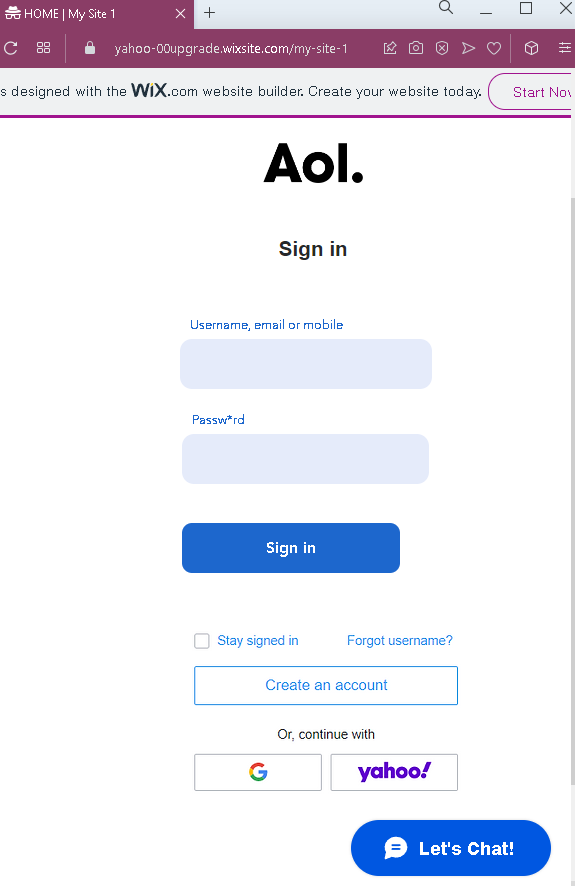
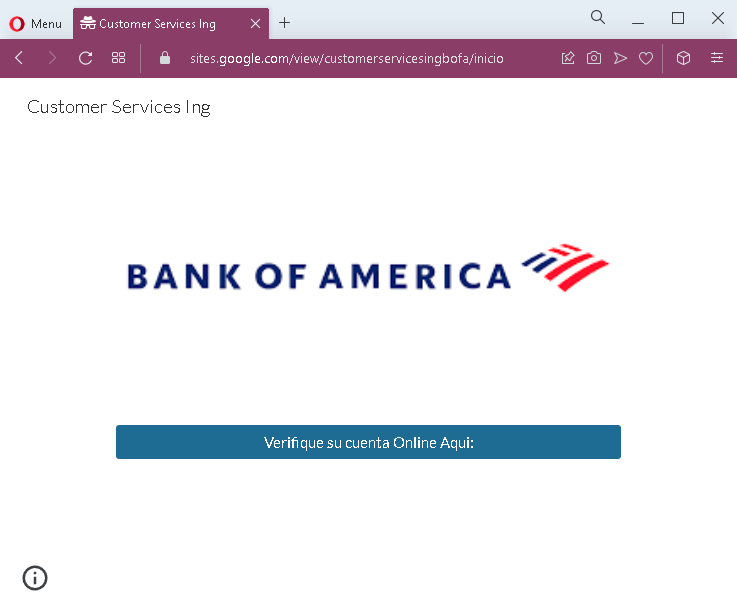
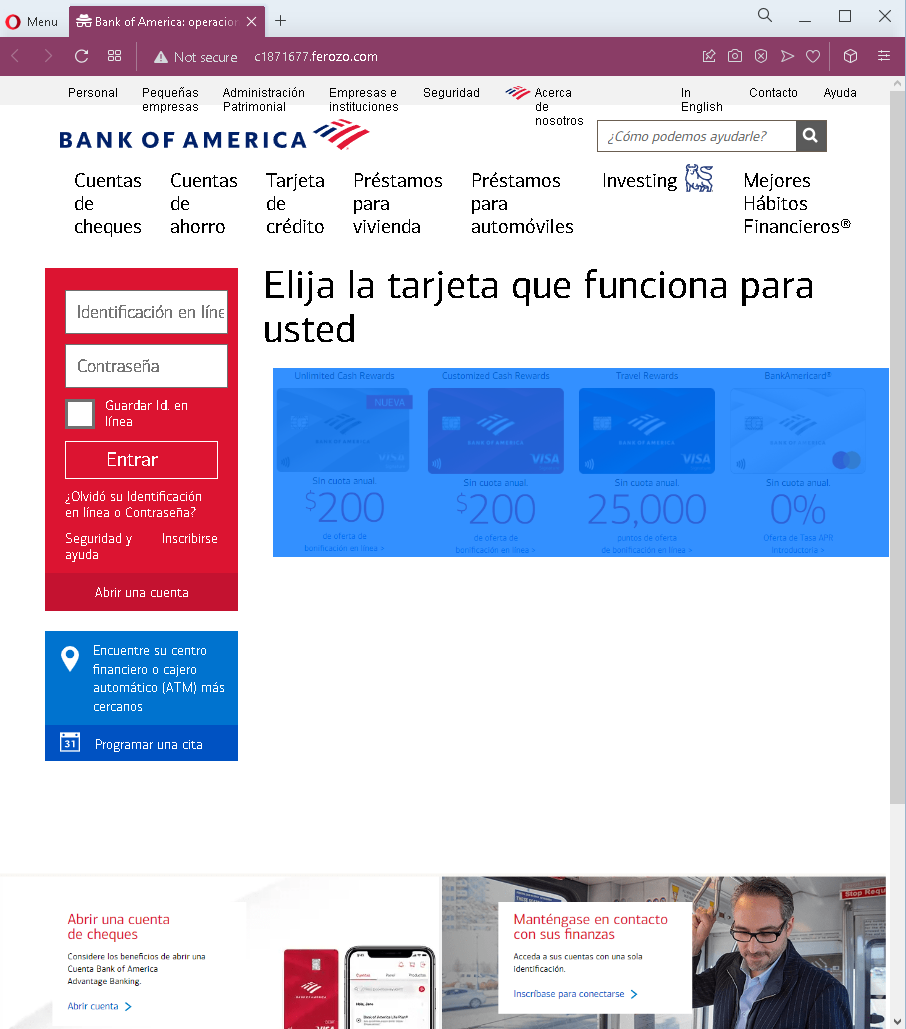
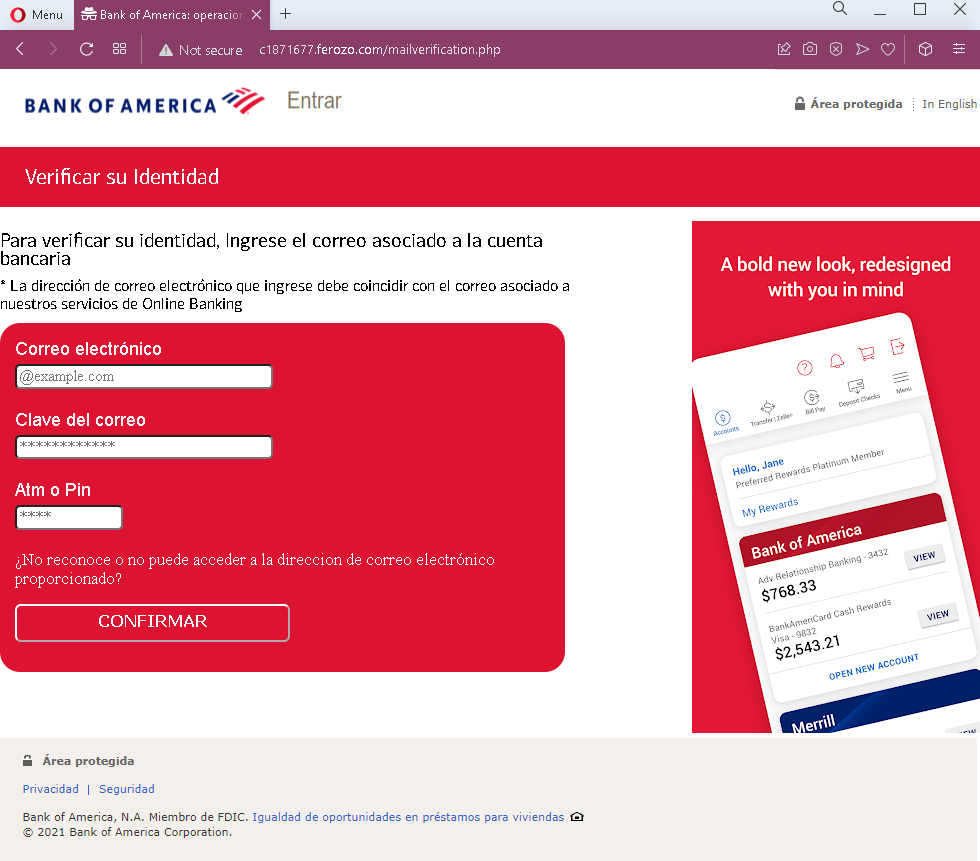
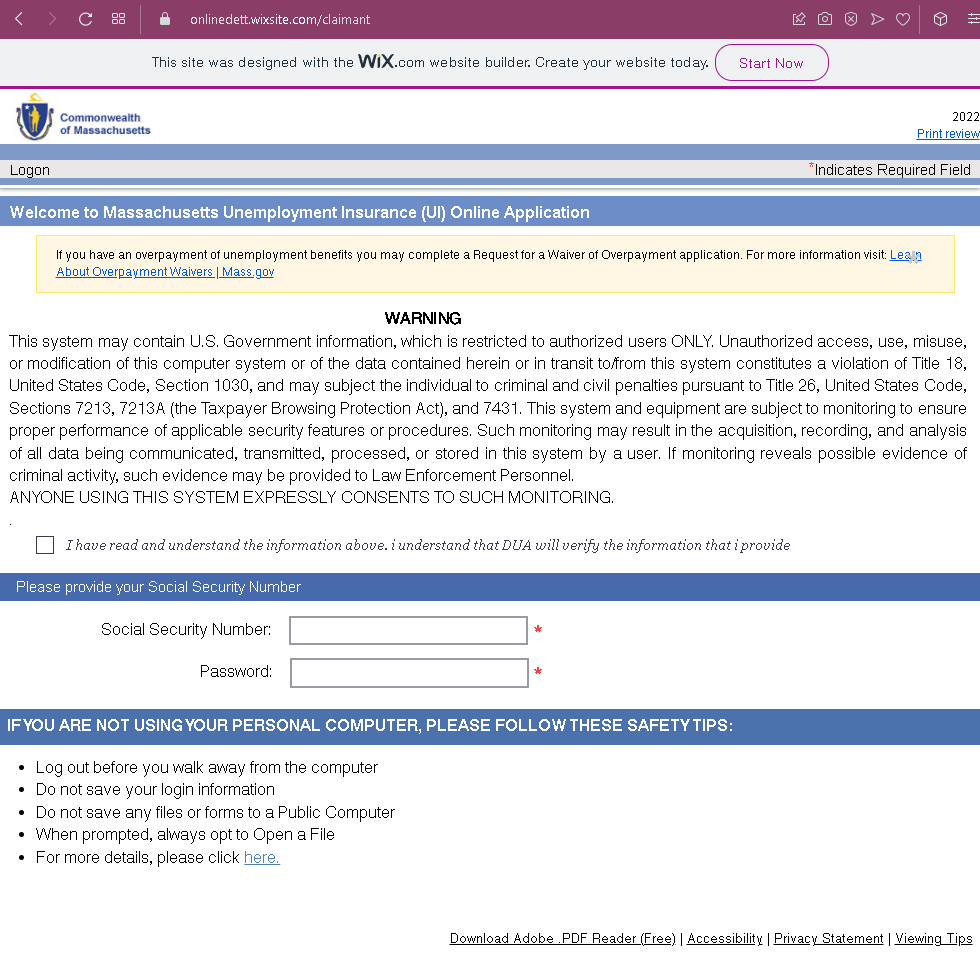
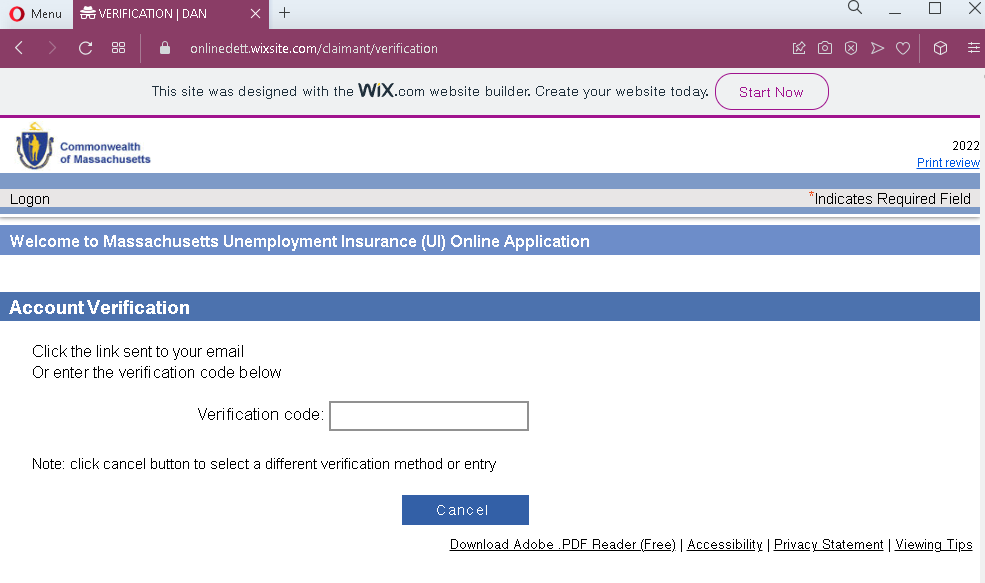
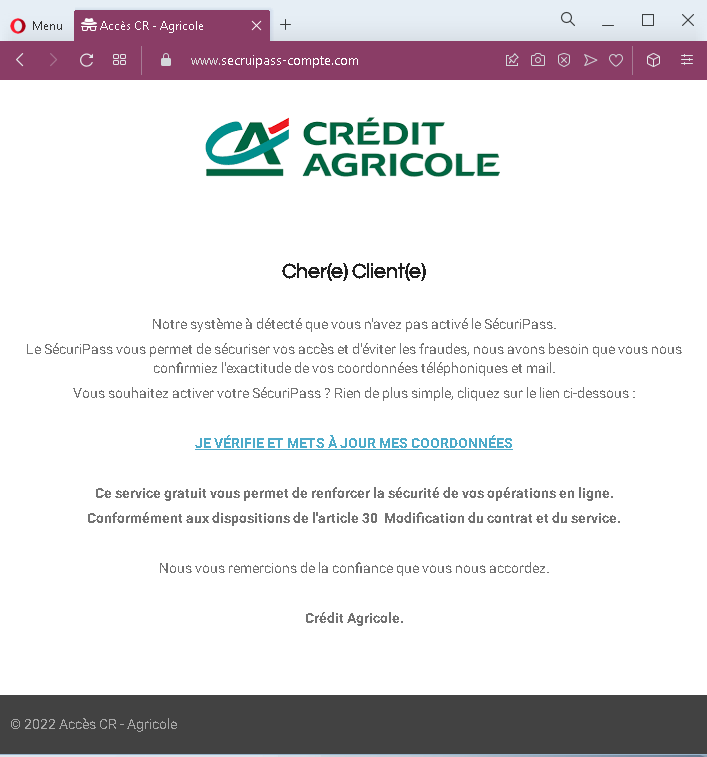
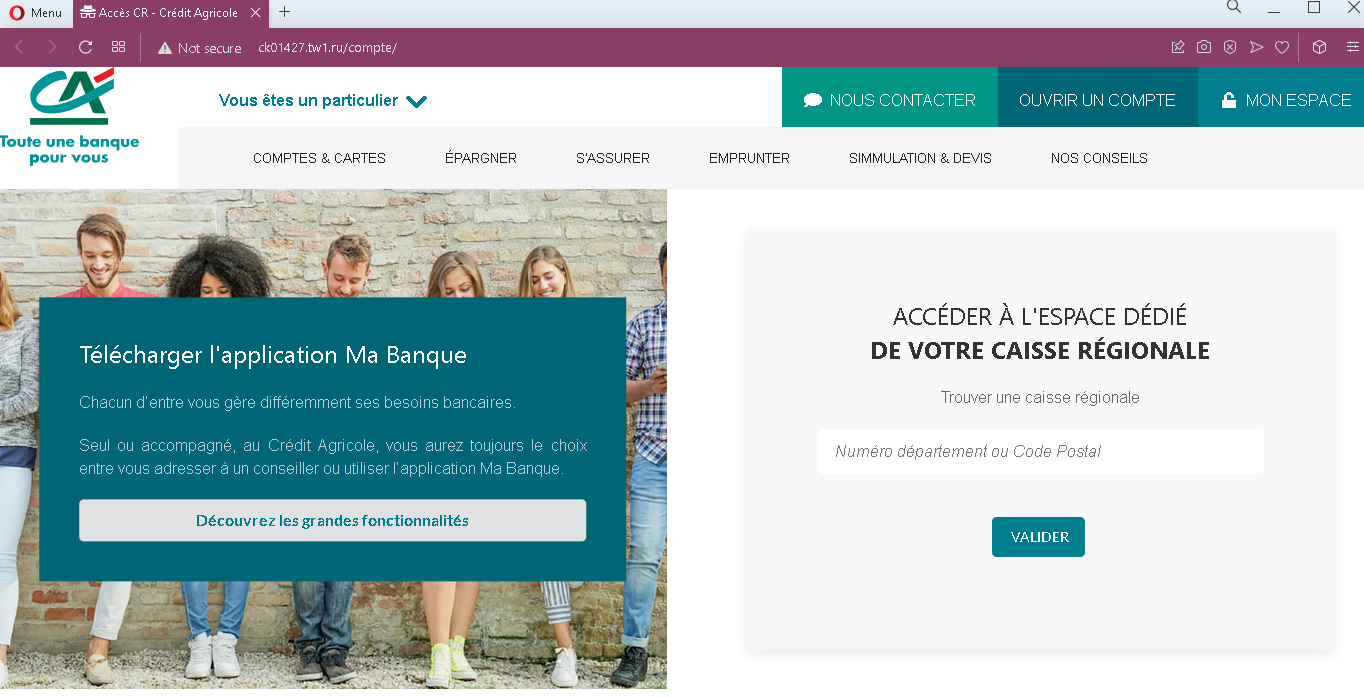
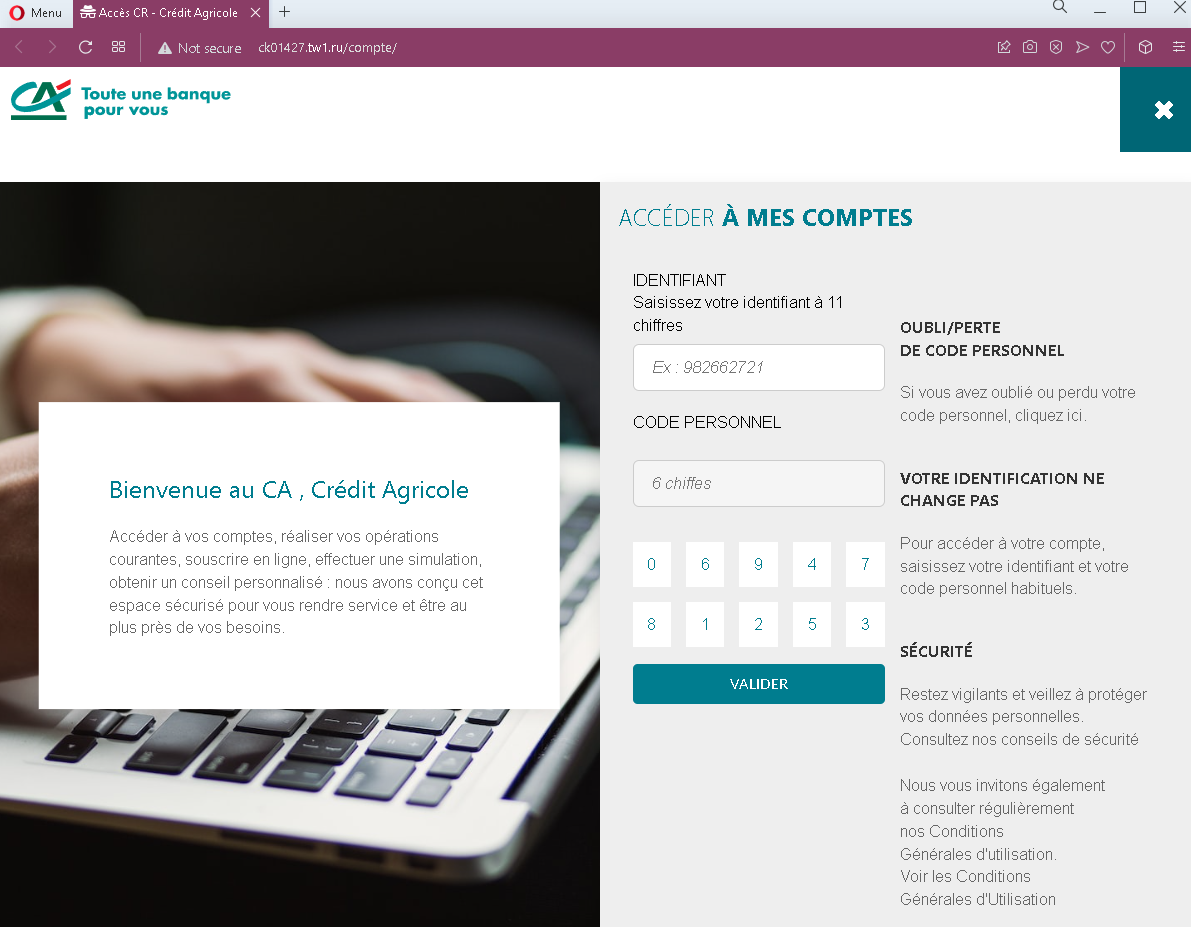
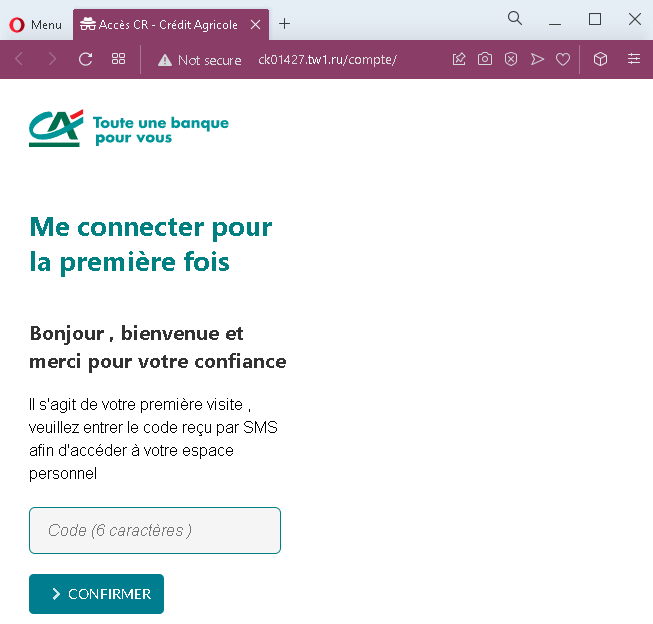
- Suspicious URL: The page is hosted on a domain that is not
nickel.euor any official Nickel domain. The presence of “WIX.com” website builder branding at the top indicates this is a cheap, quickly created phishing page, not an official bank site. - Request for full card details for a sponsorship program: A legitimate referral program would never require the participant’s full card number and expiration date. This is a clear indicator of a phishing attempt.
- Too good to be true offer: Fake “sponsorship” or “referral” offers are commonly used to trick victims into providing personal information under the promise of easy rewards.
- Missing security features: The page lacks any of the security indicators expected on a legitimate banking site (SSL certificate details, official domain, padlock icon in the address bar).
- Unprofessional design: The page is extremely simple and lacks the full branding, navigation, and legal information that would appear on the legitimate Nickel website.
- No account login required: A legitimate referral program would require the user to log into their existing Nickel account—not enter card details directly on a promotional page.
What to do if you encounter this:
- Do not enter your name, email address, card number, expiration date, or any other personal information on this page.
- If you are a Nickel customer, always access official promotions and your account by typing
nickel.eudirectly into your browser or by using the official Nickel mobile app. - If you have already entered your card details, contact Nickel immediately through their official customer service hotline to block your card and dispute any unauthorized transactions.
- Report the phishing page to Nickel’s fraud department.
Why this scam is effective:
Nickel accounts are often used by individuals who appreciate the simplicity and accessibility of the service. “Parrainage” (referral) programs are common in French banking and often offer real rewards, so users may be familiar with the concept. The promise of an easy reward can prompt users to enter information without carefully scrutinizing the URL or the legitimacy of the page. The request for card details may not raise immediate suspicion if the victim believes it’s required to “verify” their account for the reward.
Protective measures:
- Always type the official bank URL directly into your browser—never click links in emails or messages claiming to offer rewards or promotions.
- Never enter your full card number, expiration date, or CVV in response to a promotional offer. Legitimate banks do not require this information for referral programs.
- Be suspicious of any unsolicited message that offers easy rewards in exchange for personal information.
- Check the URL carefully: Legitimate Nickel domains end with
nickel.eu. Look for misspellings, extra words, or unusual top-level domains. Also be wary of pages hosted on free website builders like WIX, Weebly, or similar platforms. - If in doubt, contact Nickel directly using a phone number from your bank statement or the official website—never use contact information provided in the suspicious message.