Threat Intel: This scam layout was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our daily link moderation procedures. To protect the public, the hostile origin link has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users detect replica fraud techniques before financial damage occurs.
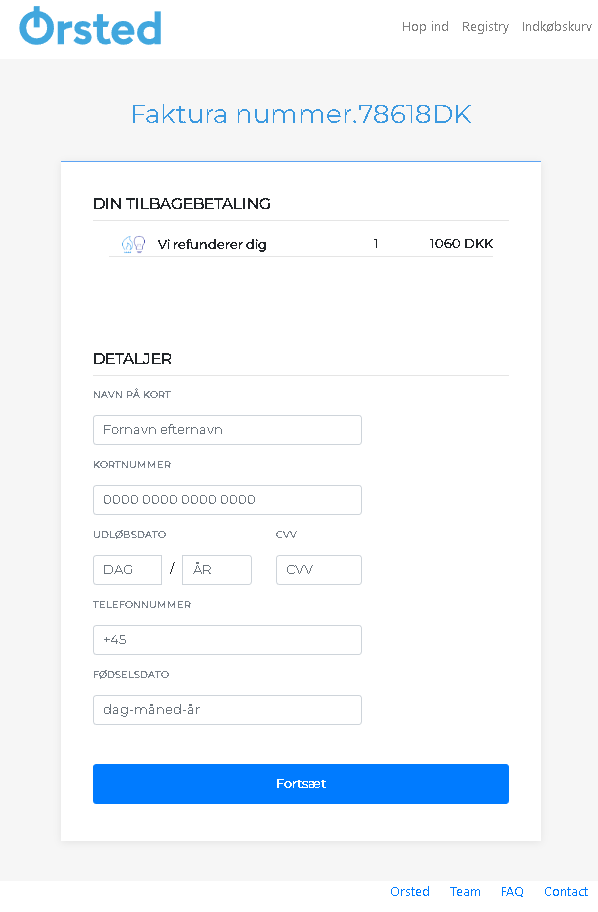
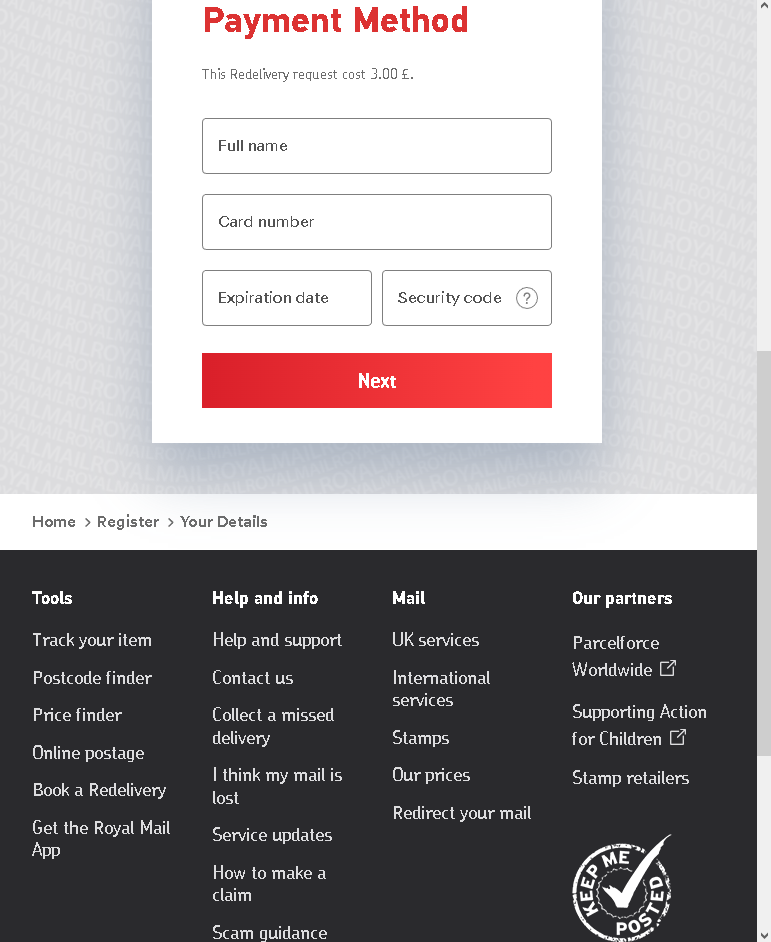
This screenshot shows a phishing page impersonating Ørsted, a Danish energy company. The scam uses a fake refund offer to harvest card details, phone number, and date of birth—sensitive personal and financial information.
Threat Analysis: Ørsted Refund Phishing – Card & Identity Data Harvesting
The page claims a refund is available (1,060 DKK) and asks the victim to provide:
- Cardholder name
- Full card number
- Expiration date and CVV
- Phone number (with Danish country code)
- Date of birth
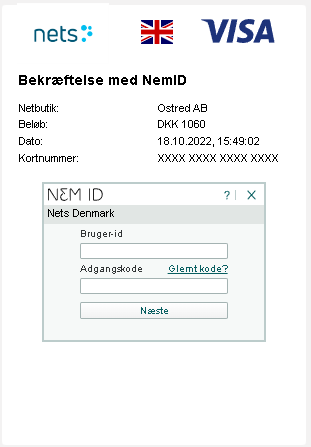
How it works:
The victim receives an email, SMS, or other message claiming a refund from Ørsted. The link leads to this page. By entering the requested details, the victim unknowingly hands over everything needed to make fraudulent transactions or commit identity theft.
The goal:
- Steal credit/debit card details for unauthorized purchases
- Obtain date of birth and phone number for identity theft or SIM swapping
Red flags to watch for:
- Suspicious URL: The page is hosted on a domain that is not
orsted.com - Request for full card details, CVV, and birth date for a refund: A legitimate refund does not require this information. Refunds are automatically processed to the original payment method.
- Unsolicited refund offer: Ørsted does not send unsolicited emails or messages asking customers to enter card details to receive a refund.
- Poor design: The page uses generic layout and lacks official branding beyond the Ørsted logo.
What to do if you encounter this:
- Do not enter any personal or card information.
- If you are an Ørsted customer, log into your official account directly to check for any legitimate refunds.
- If you have already entered your card details, contact your bank immediately to block the card and dispute any unauthorized transactions.
- Report the phishing page to Ørsted’s security team.
Protective measures:
- Never click links in unsolicited messages claiming refunds or payments.
- Always type the official company URL directly into your browser.
- Never provide your card CVV or date of birth to “receive” a refund.
- Enable two‑factor authentication on your bank and email accounts.