🛡️ Phishing Alert: The “Fake Buyer” Marketplace Scam
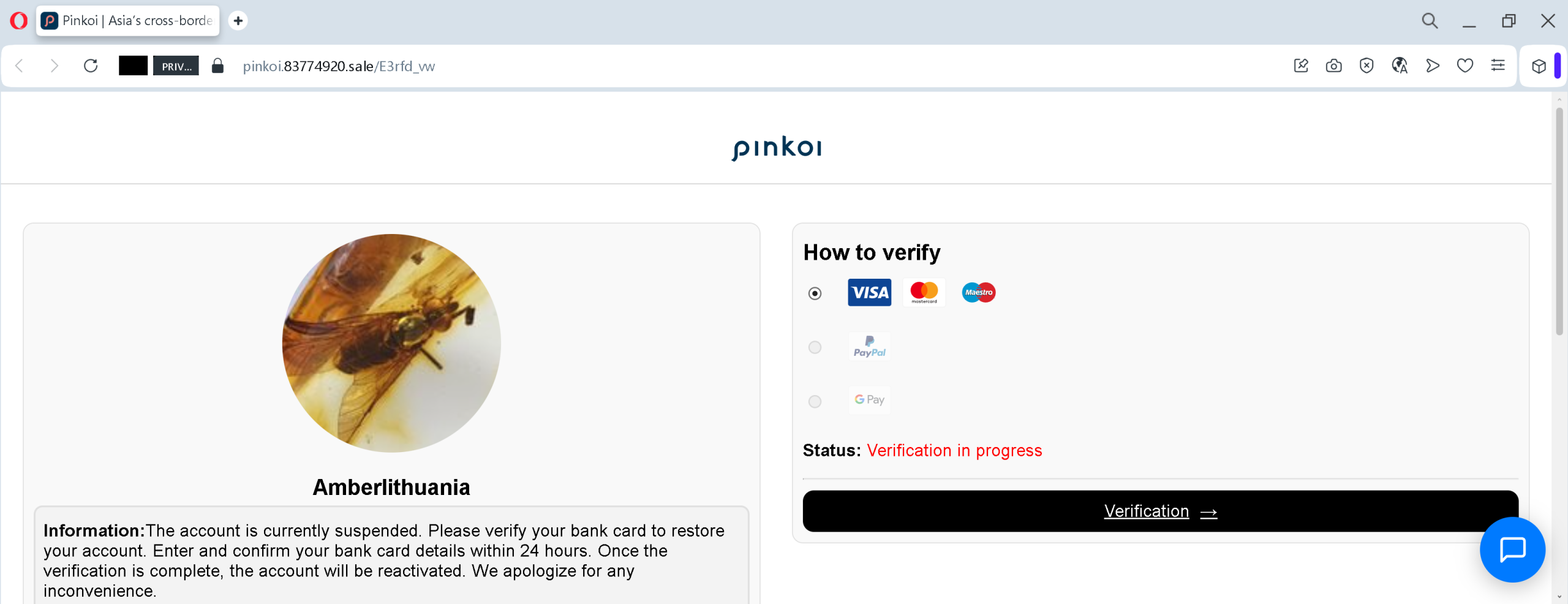
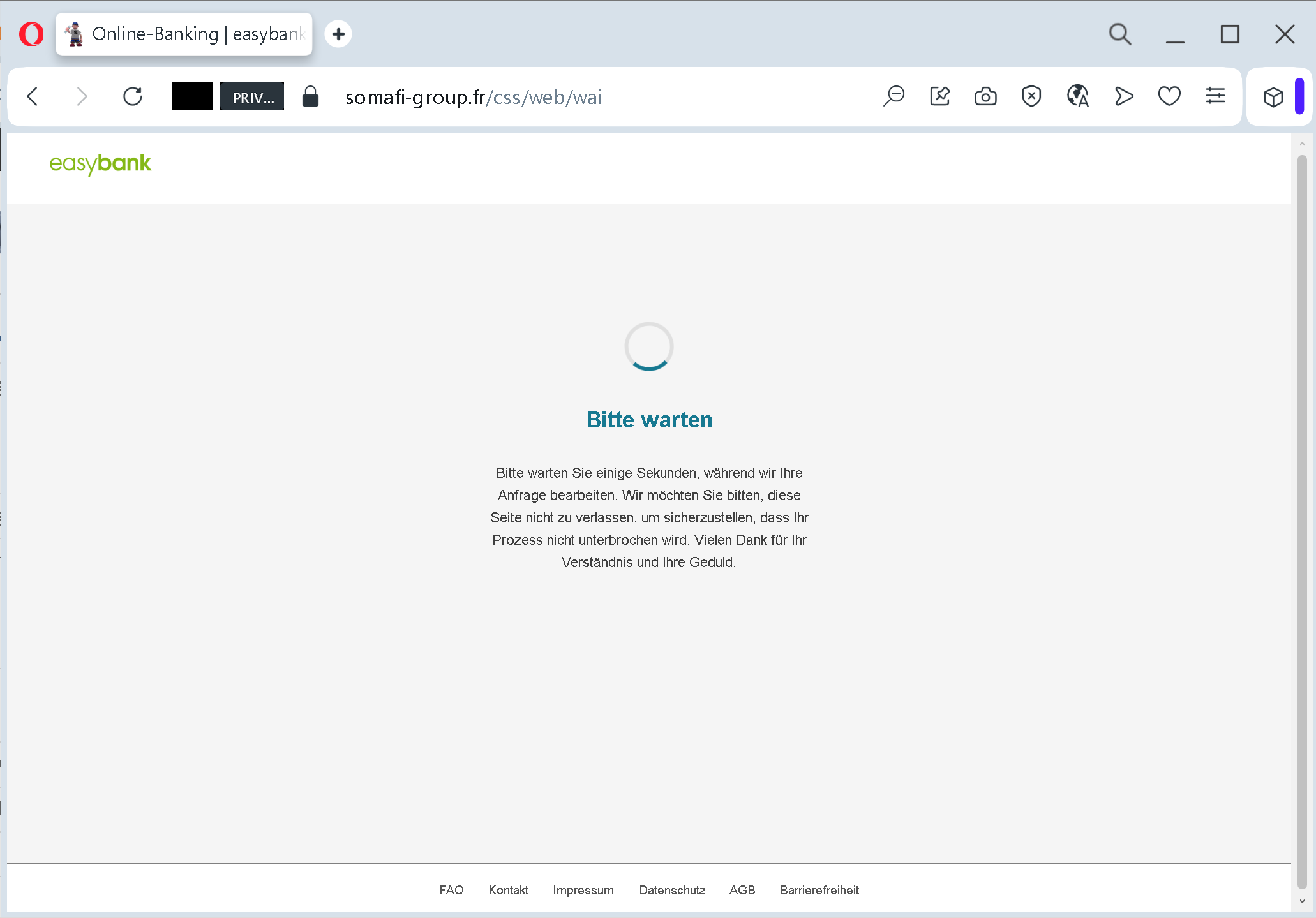
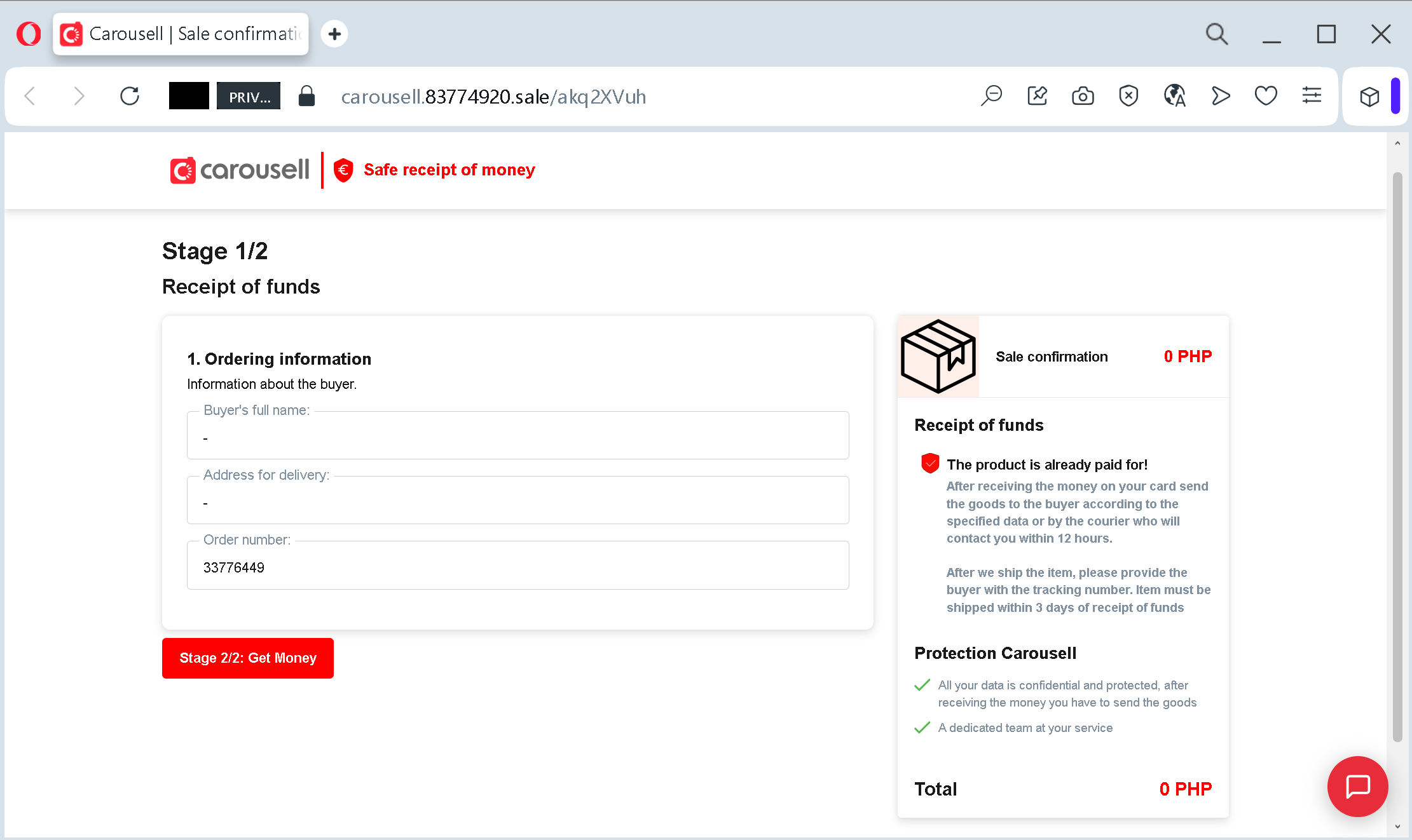
This screenshot demonstrates a common and dangerous phishing tactic used on classifieds and marketplace platforms (like Carousell, Olx, or Avito).
Here is a breakdown of how this scam works to steal your banking information:
1. The Domain Deception
Look closely at the URL: carousell.83774920.sale/….
- The Trap: Scammers use a subdomain that includes the brand name (carousell) to create a false sense of security.
- The Reality: The actual domain is 83774920.sale. Official Carousell transactions will never happen on a random numeric domain or a .sale extension. They always stay within carousell.ph or the official app.
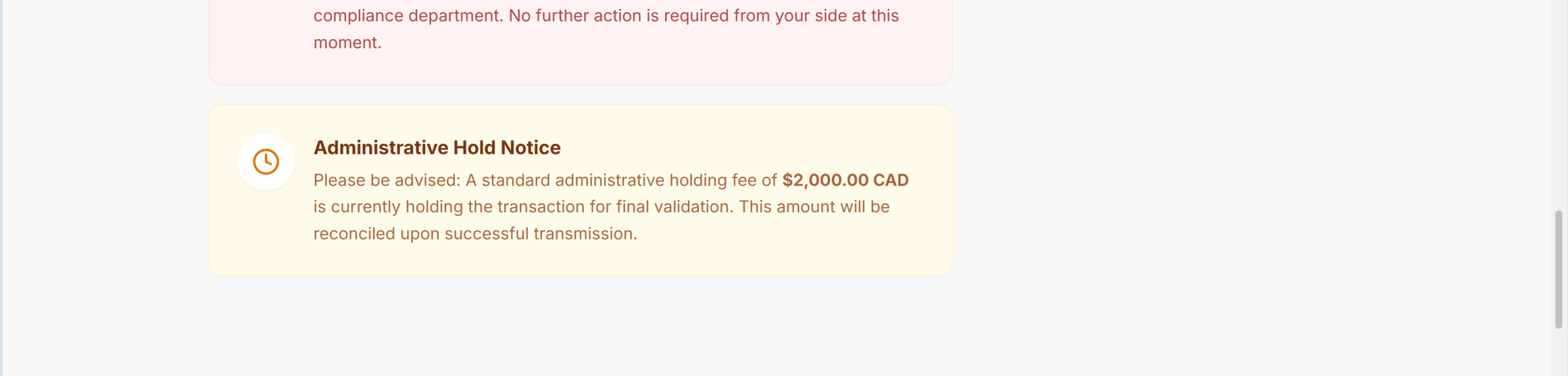
2. The Emotional Hook: “Receipt of Funds”
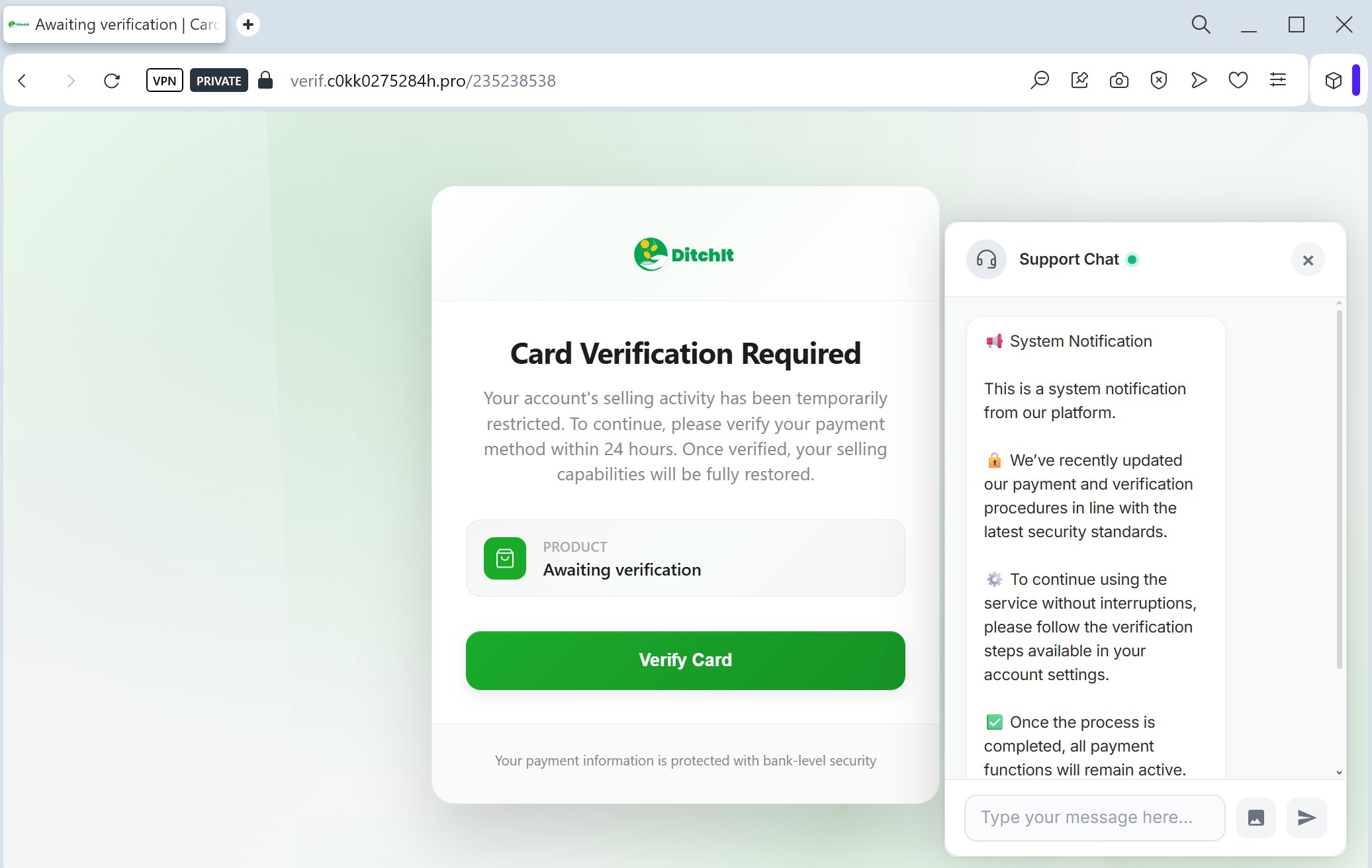
The page is designed to look like a legitimate “Safe Receipt of Money” portal.
- The Tactic: The scammer contacts a seller and claims they have already paid for the item. They send this link to the seller, claiming it’s the only way to “accept” or “receive” the money.
- The Red Flag: Legitimate marketplaces do not require you to enter your full card details or address on a third-party link to receive a payment.
3. Psychological Manipulation
- Urgency: The text states the item “must be shipped within 3 days,” pushing the victim to act quickly.
- False Protection: Using terms like “Protection Carousell” and “Dedicated team” is a social engineering trick to make the victim lower their guard.
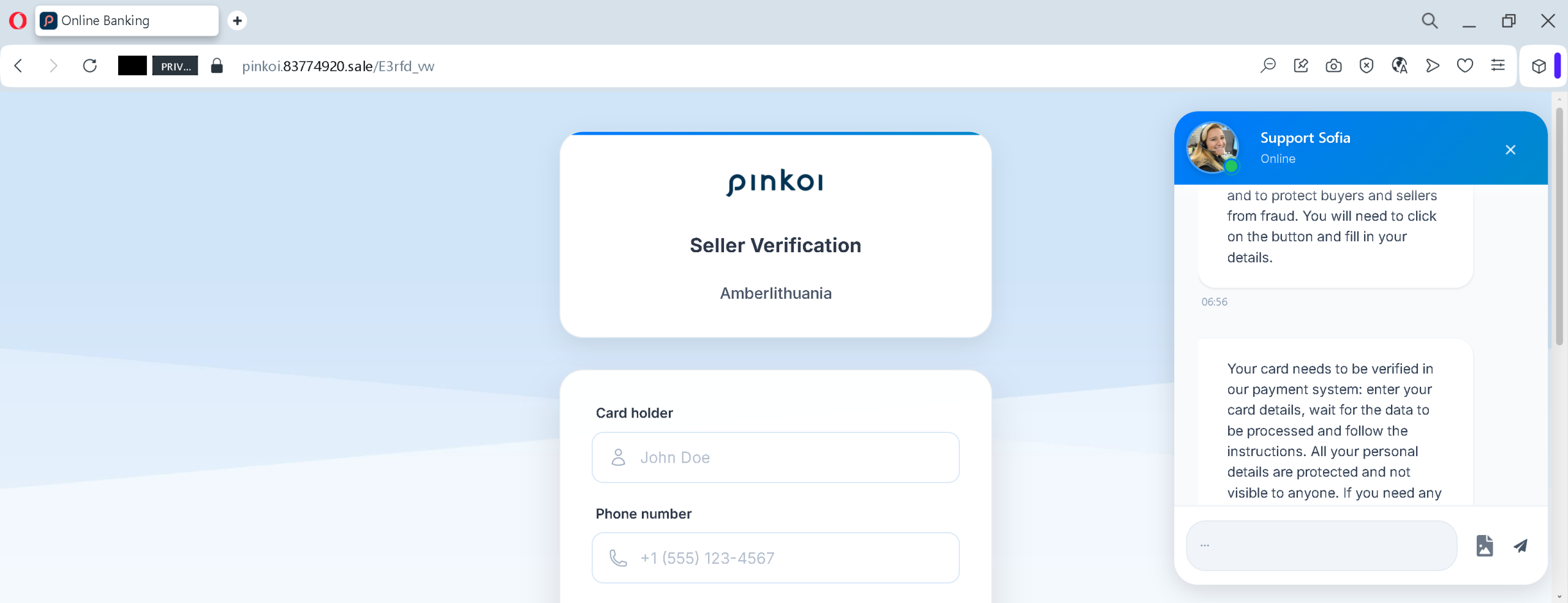
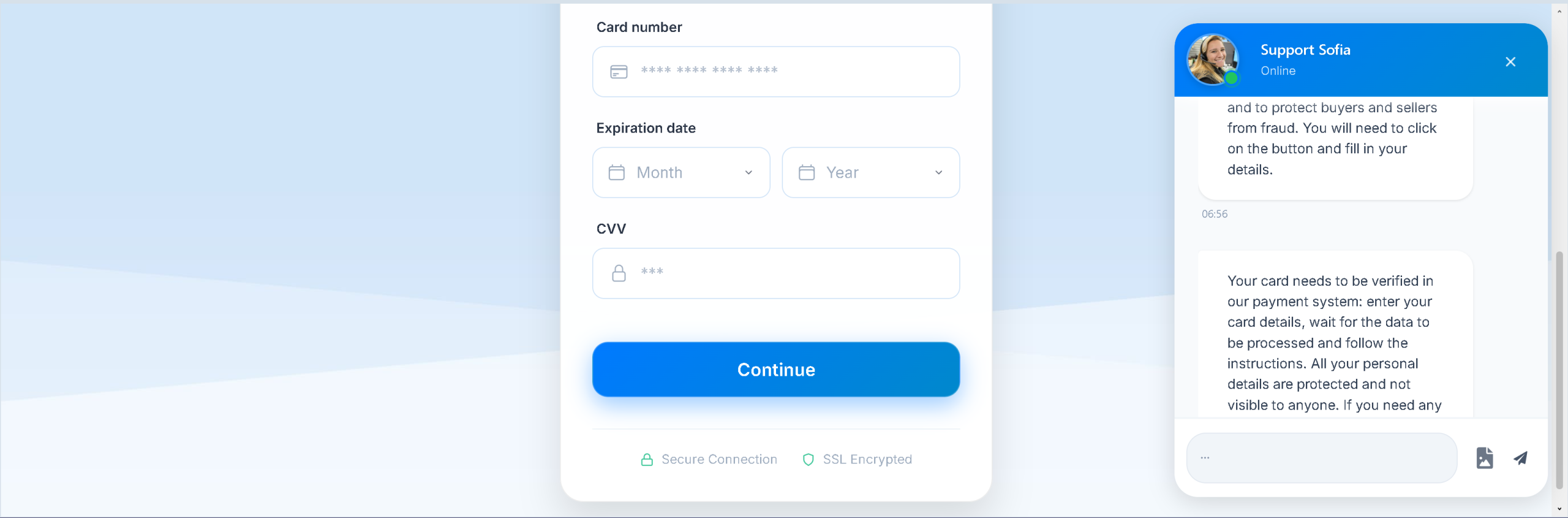
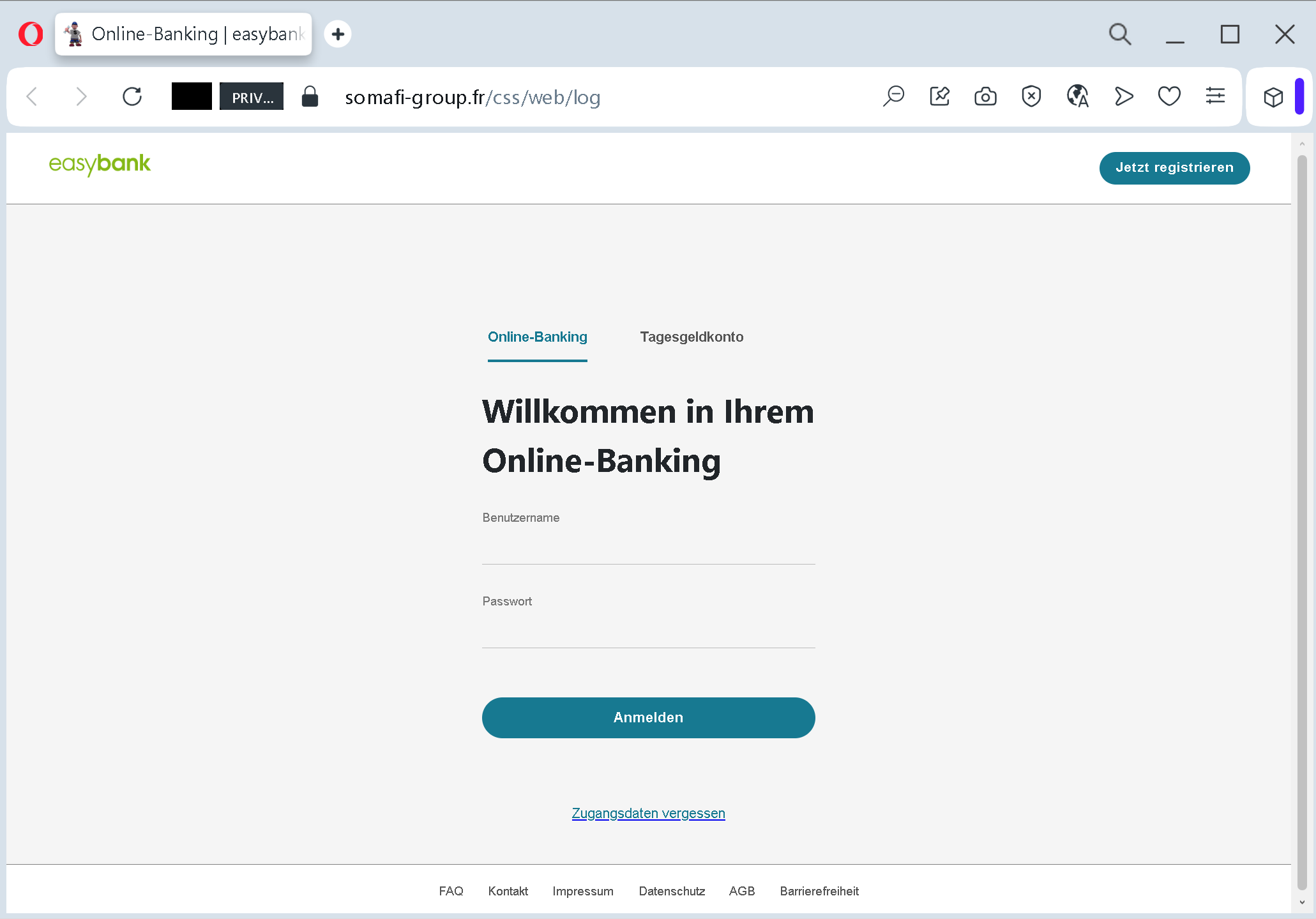
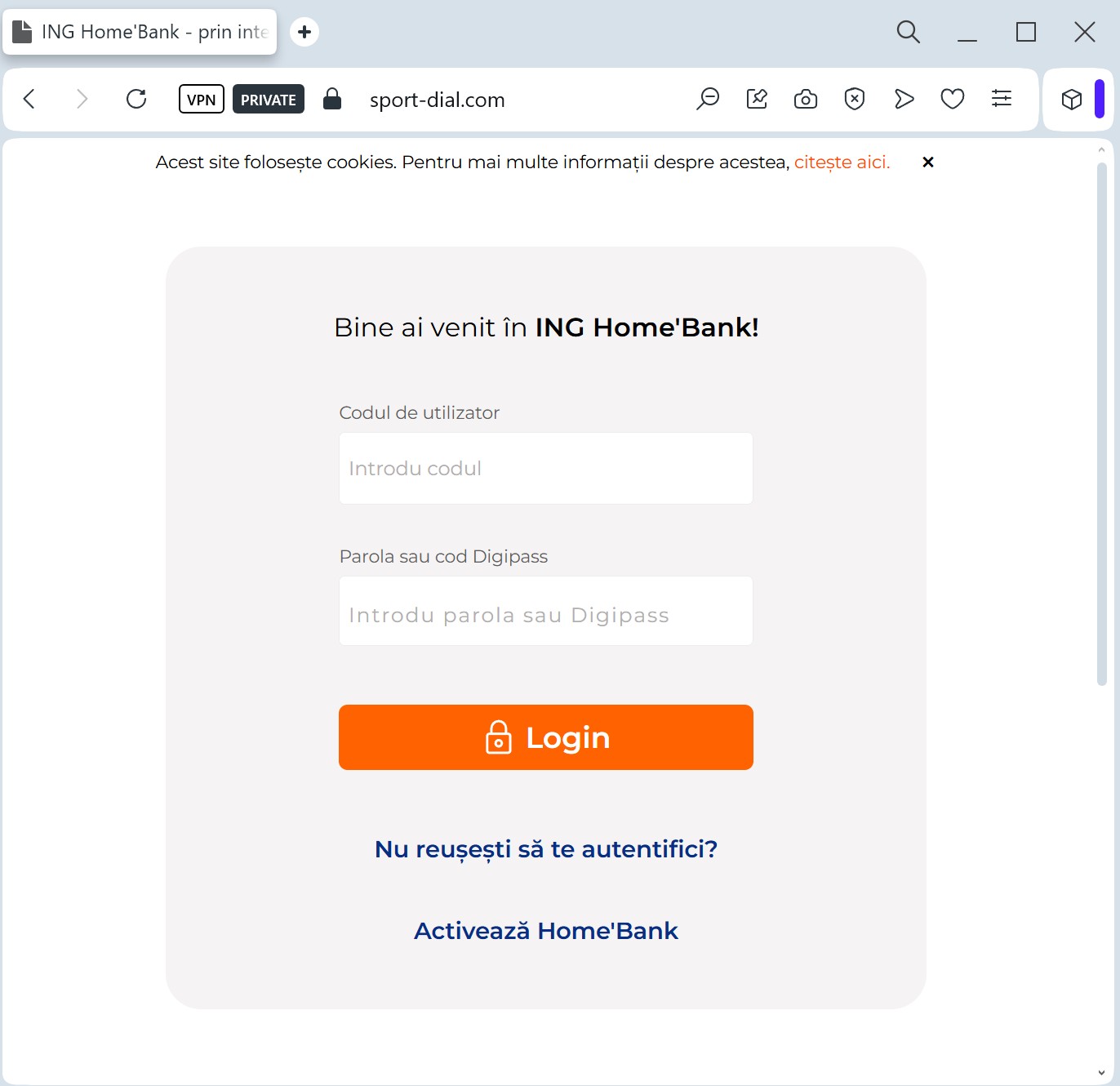
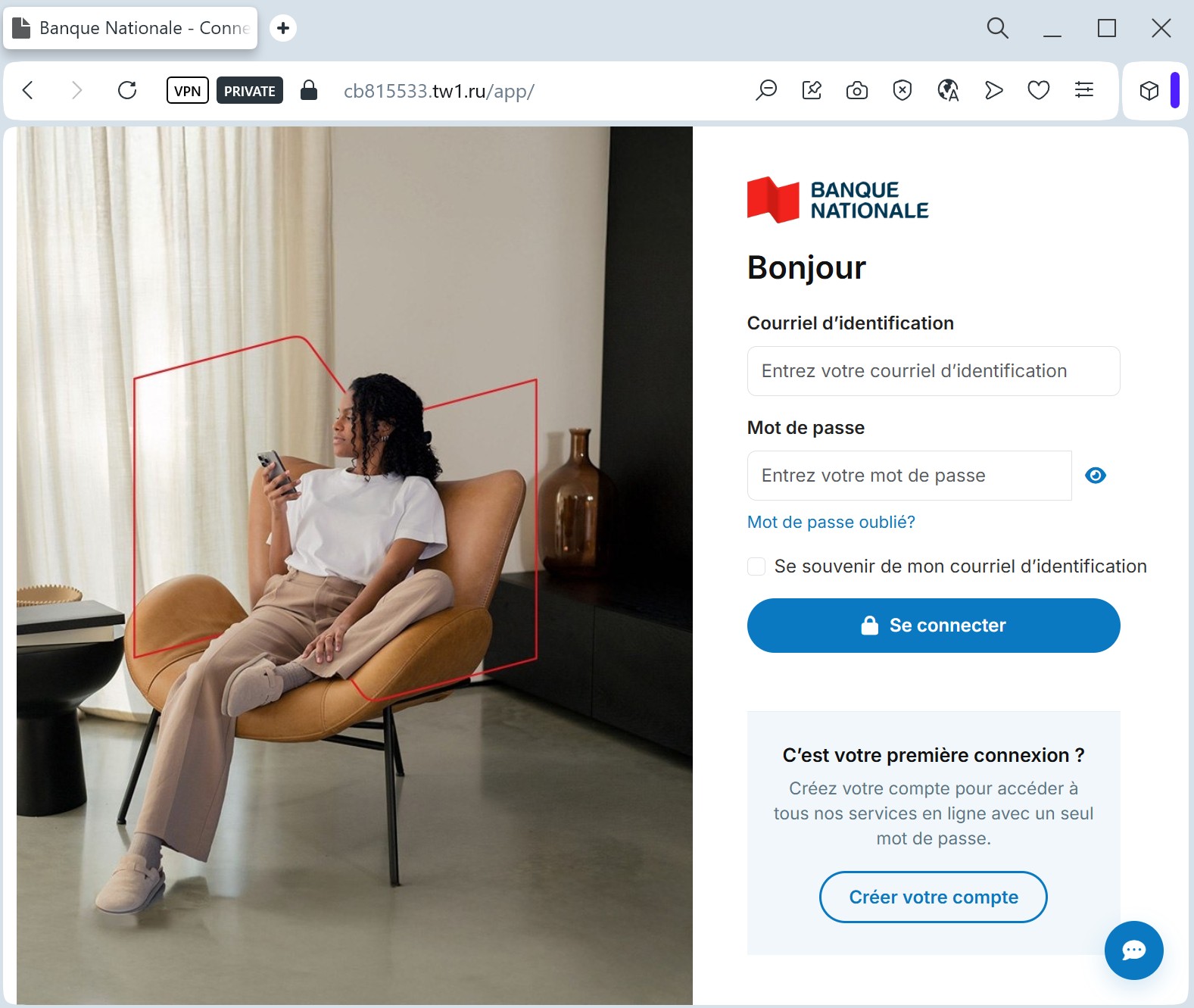
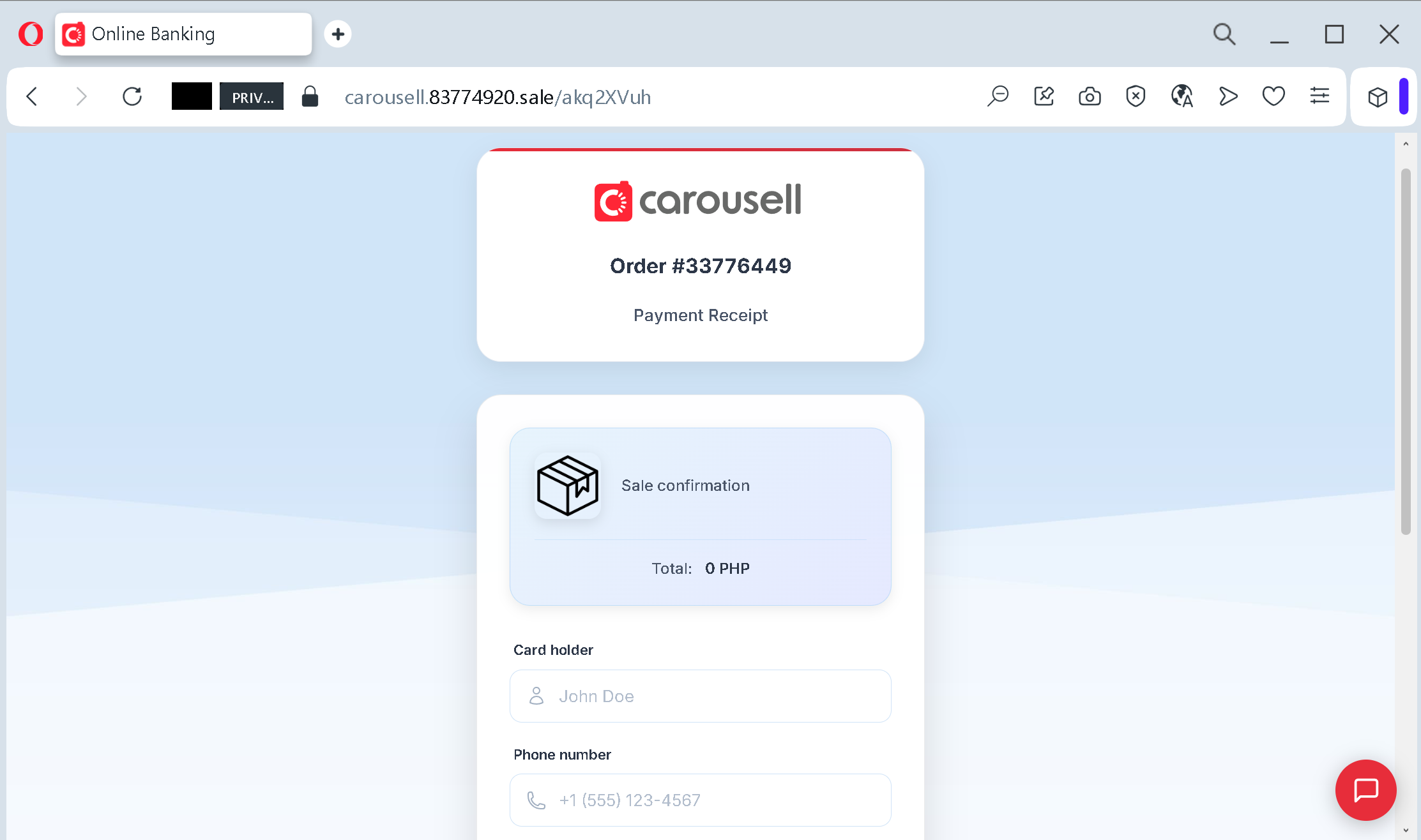
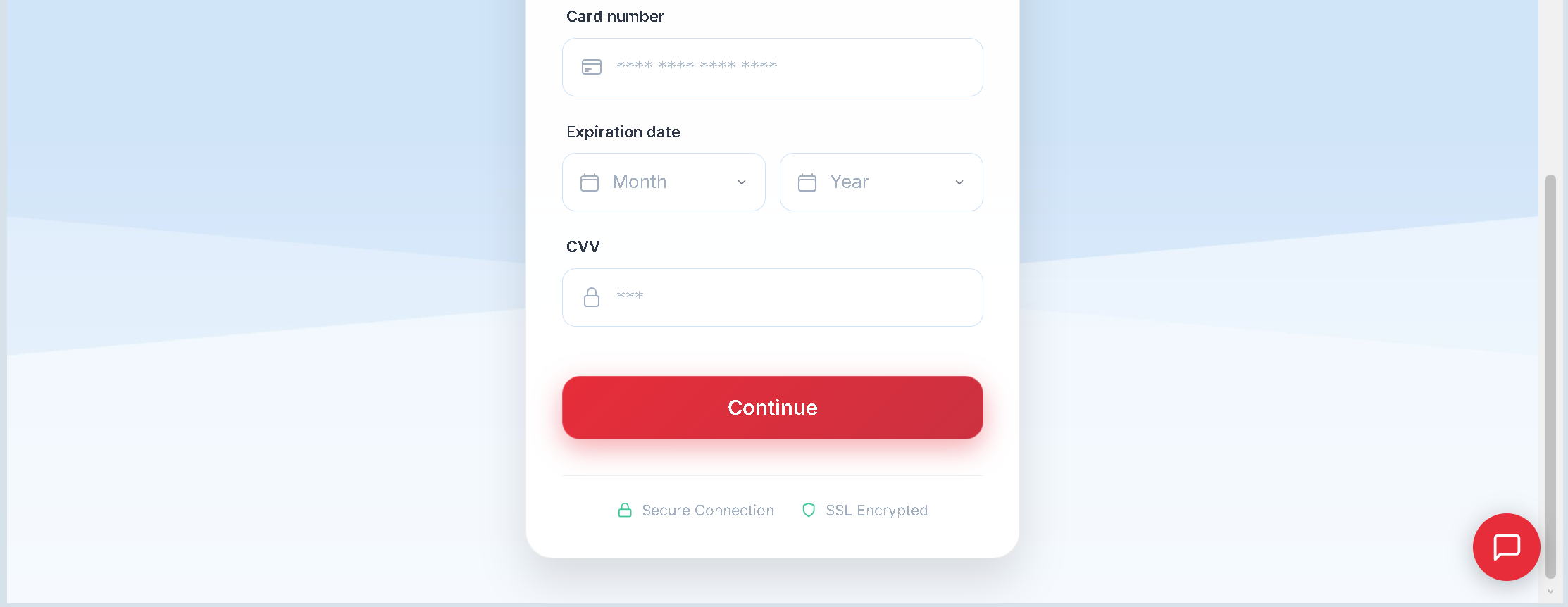
- The “Get Money” Button: The bright red button “Stage 2/2: Get Money” is the final trap. Clicking it will typically lead to a fake bank login page or a form asking for your card number, CVV, and SMS OTP.
How to Stay Safe:
- Stay on the App: Never follow links sent by buyers in external messengers (WhatsApp, Viber, Telegram).
- Verify the URL: Always check the main domain. If it’s not the official platform address, it’s a scam.
- No Card Info for Receiving: You do not need to provide your CVV or a one-time password (OTP) to receive money. These are only for sending money.
Phishing Scheme: Fake “Safe Payment” Receipt
How the scam works:
The Approach: A scammer contacts a seller on a marketplace (Carousell), posing as a legitimate buyer. They claim to have already made the payment through the platform’s internal “safe deal” system.
The Link: The scammer sends a generated link (like the one above) via an external messenger (WhatsApp/Viber), claiming it’s the official “Receipt of Funds” page.
The Trap: The page looks identical to the official marketplace design. It displays a “Stage 1/2: Receipt of Funds” form, asking the seller to confirm their details.
The Theft: When the seller clicks “Get Money,” they are redirected to a fake payment gateway that asks for Full Card Number, Expiry Date, CVV, and even an SMS OTP (One-Time Password). Instead of receiving funds, the victim’s account is drained.
Warning Signs:
External Links: Official platforms never send payment links via third-party messengers.
Fake Domain: Always check the root domain. In this case, it is 83774920.sale, which has nothing to do with the official carousell.ph.
Receiving Money Doesn’t Require CVV: You never need to provide your card’s CVV or an SMS confirmation code to receive a payment.