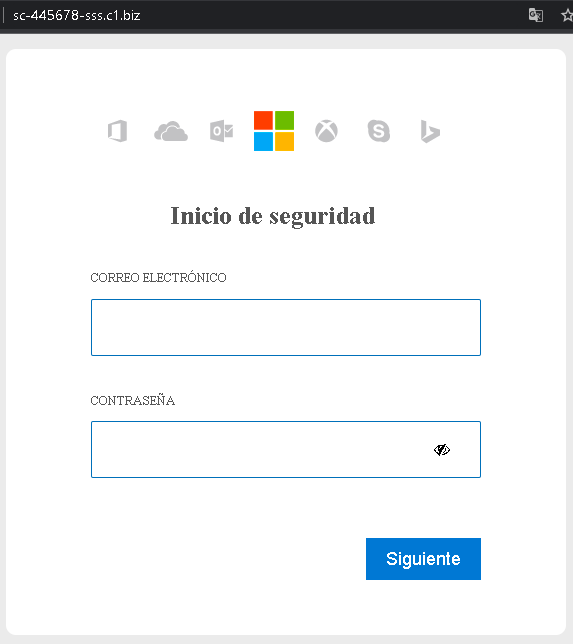
This screenshot shows a Spanish‑language phishing page designed to steal email credentials (correo electrónico and contraseña). The page is minimal and generic, making it adaptable to impersonate various services (Microsoft, Google, a bank, or an email provider).
Threat Analysis: Generic “Inicio de seguridad” Phishing – Credential Harvesting
How it works:
The victim receives a phishing email, SMS, or message claiming a security alert, account suspension, or the need to verify their information. The link leads to this page, which asks for:
- Email address
- Password
The “Siguiente” (Next) button suggests a multi‑step flow, where the victim would be taken to another fake page (e.g., for two‑factor authentication or additional personal data).
The goal:
The attacker steals the victim’s email credentials to:
- Access the email account (search for sensitive information, reset passwords for other services)
- Send further phishing messages to the victim’s contacts
- Use the credentials to compromise other accounts where the same password is reused
Red flags to watch for:
- Suspicious URL: The page is hosted on a domain like
sc-445678-sss.c1.biz, which is not an official domain for any legitimate service (e.g.,google.com,microsoft.com,outlook.com). - Generic design: The page has no logo, no company branding, and no personalized elements – a strong indicator of a broad phishing campaign.
- “Inicio de seguridad” pretext: This vague “security start” phrase is meant to create a false sense of urgency but lacks the professionalism of a real security alert.
- Unsolicited login request: No legitimate service sends links requiring users to log in to resolve “security” issues.
What to do if you encounter this:
- Do not enter your email or password.
- If you have already entered credentials, change your password immediately for that email account and for any other accounts using the same password. Enable two‑factor authentication (2FA) on your email account.
- Always access your email or online services by typing the official URL directly into your browser.
Protective measures:
- Never click links in unsolicited messages claiming security issues.
- Use a password manager – it will not autofill on fake domains.
- Enable two‑factor authentication on your email and other critical accounts.
- Check the URL carefully: Look for misspellings, extra words, or unusual top‑level domains.
