These three screenshots show a multi‑step phishing campaign targeting Free Fire players. The scam promises free in‑game rewards (diamonds, magic cubes, etc.) and then directs victims to a fake Facebook login page to steal their credentials.
Security Notice: This deceptive layout was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our daily link moderation procedures. To protect the public, the dangerous destination URL has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
Threat Analysis: Free Fire Reward Phishing – Facebook Credential Harvesting
How the scam works (3 steps):
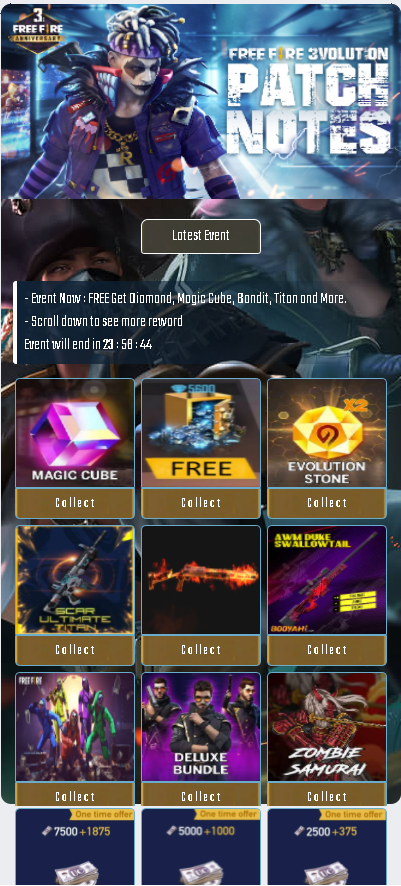
Step 1 – Fake Free Fire Event Page (First Screenshot)
The victim sees a page mimicking an official Free Fire announcement. It displays:
- A countdown timer (e.g., “23 : 56 : 44”) to create urgency
- Promises of free rewards: diamonds, magic cube, evolution stone, deluxe bundles
- “Collect” buttons for various items
The page is designed to look like a legitimate in‑game event. Clicking any “Collect” button leads to the next step.
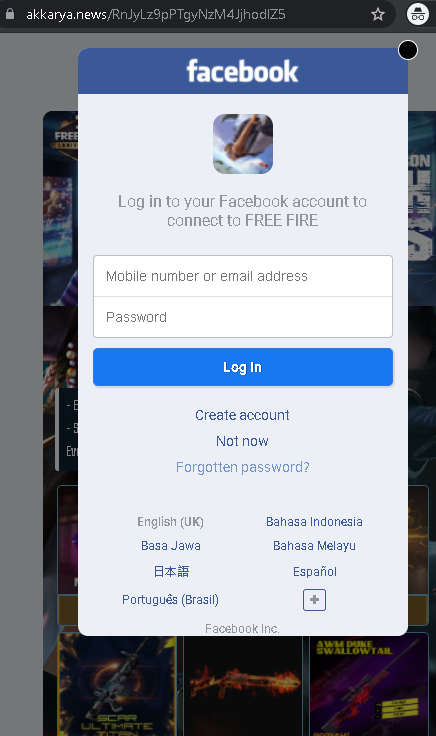
Step 2 – “Log in to claim prize” page (Third Screenshot)
The victim is told: “Selected prize locked. Log in using your FREEFIRE account to receive prize” and given an option to “Log in using Facebook account.” This is the transition to the credential harvesting page.
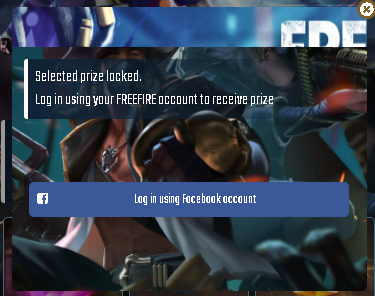
Step 3 – Fake Facebook Login Page (Second Screenshot)
The victim is redirected to a page that mimics the Facebook login interface. It asks for:
- Mobile number or email address
- Password
After the victim enters their credentials and clicks “Log In,” the information is captured and sent to the attacker.
The goal:
The attacker steals Facebook credentials to:
- Take over the victim’s Facebook account
- Access the linked Free Fire (Garena) account
- Use the account to spread the scam to friends
- Sell the account or its data on criminal markets
Red flags to watch for:
- Free reward lure: Garena / Free Fire does not give away diamonds and rare items through external websites. Legitimate events are inside the game.
- Login via Facebook on a third‑party page: A real reward would be claimed directly in the game, not by logging into Facebook via a random link.
- Suspicious URL: The pages are hosted on domains that are not
freefire.comgarena.comfacebook.com - Urgency tactics: Countdown timers and “limited time” messages pressure victims to act without thinking.
- No official branding / design inconsistencies: The event page uses generic graphics and does not match the official Free Fire style.
What to do if you encounter this:
- Do not click any “Collect” buttons or enter any Facebook credentials.
- If you have already entered your Facebook login details, change your password immediately and enable two‑factor authentication (2FA). Also check for any unauthorized activity or connected apps.
- Always claim in‑game rewards through the official Free Fire app – never through external links.
- Report the phishing pages to Facebook and to Garena.
Protective measures:
- Remember: no legitimate game reward requires you to log in via a link.
- Never log into Facebook on a page you reached from a game “reward” link.
- Use a password manager – it will not autofill on fake domains.
- Enable two‑factor authentication on your Facebook account.
- Be suspicious of any unsolicited offer that promises free premium currency.
