Analysis Memo: This deceptive layout was logged, cross-checked, and neutralized firsthand by the
Antiphishing.bizsecurity team during our standard URL vetting operations. To protect the public, the phishing source domain has been fully defanged within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
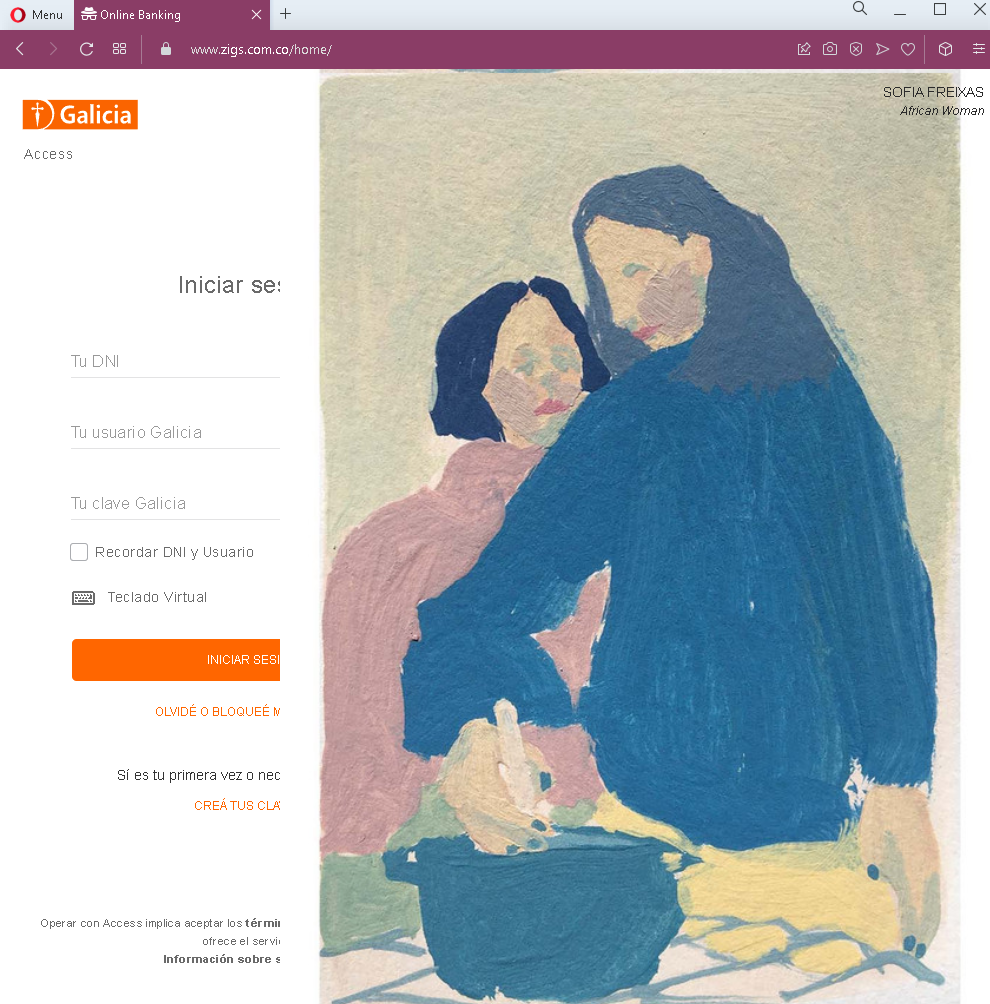
Threat Analysis: Banco Galicia Phishing – Fake “Acceso” Login Page
This phishing campaign impersonates Banco Galicia, one of the largest banks in Argentina. The page mimics the bank’s login interface to steal customers’ DNI (national identification number), Usuario Galicia (username), and Clave Galicia (password) —the three pieces of information typically required to access online banking.
How it works:
The victim receives a phishing email, SMS, or other message claiming a security alert, account issue, or the need to verify their information. The message includes a link to this fake Banco Galicia login page. When the victim enters their DNI, Usuario, and Clave and clicks “INICIAR SESIÓN” (the button is truncated but means “Log in”), the credentials are captured and sent to the attacker.
The goal:
The attacker aims to steal the victim’s Banco Galicia online banking credentials. With these, they can log into the victim’s real bank account, view balances, transfer funds, and commit fraud.
Red flags to watch for:
- Suspicious URL: The page is hosted on a domain that is not
banco-galicia.com.ar - Unsolicited login request: Banco Galicia does not send emails or messages with links requiring customers to log in to resolve account issues. Customers should always access online banking by typing the URL directly or using the official app.
- Missing security features: Legitimate Banco Galicia login pages typically include a virtual keyboard (which is mentioned but may not function) and a security image or personalized greeting. This page lacks the full security implementation.
- Typographical error: The login button reads “INICIAR SESI” (missing the final “ÓN”), which is likely a truncation error in the phishing page design. Official bank interfaces do not have such truncations.
- Poor grammar and truncated text: The text below the form is garbled and incomplete (“Olvidé o bloqueé n°1” followed by nonsensical Spanish). This is a clear indicator of a hastily assembled phishing page.
- Generic design: While the page uses the Banco Galicia logo and a simple form, it lacks the full navigation, account-specific information, and professional polish of the real bank website.
What to do if you encounter this:
- Do not enter your DNI, Usuario, Clave, or any other personal information on this page.
- If you are a Banco Galicia customer, always access online banking by typing
banco-galicia.com.ar - If you have already entered your credentials, contact Banco Galicia immediately through their official customer service hotline to secure your account and change your password.
- Report the phishing page to Banco Galicia’s fraud department.
Why this scam is effective:
Banco Galicia has millions of online banking customers in Argentina. The page uses the bank’s logo and familiar terminology (“DNI,” “Usuario Galicia,” “Clave Galicia”), which are standard for the bank’s login process. The mention of a virtual keyboard (a real security feature used by the bank) adds a layer of perceived legitimacy. However, the truncation errors and garbled text are red flags that attentive users might notice.
Protective measures:
- Bookmark the official Banco Galicia login page and use that bookmark to access online banking—never click links in emails or messages.
- Use a password manager: It will autofill only on legitimate
banco-galicia.com.ar - Enable two-factor authentication (2FA) on your Banco Galicia account if available, to add an extra layer of protection.
- Be suspicious of any unsolicited message that creates urgency and asks you to log in to your bank account.
- Check the URL carefully: Legitimate Banco Galicia domains end with
banco-galicia.com.ar - If in doubt, contact Banco Galicia directly using a phone number from your bank statement or the official website—never use contact information provided in a suspicious message.
