Anatomy of a High-Tier Support & Billing Scam: The Trapped Invoice Method
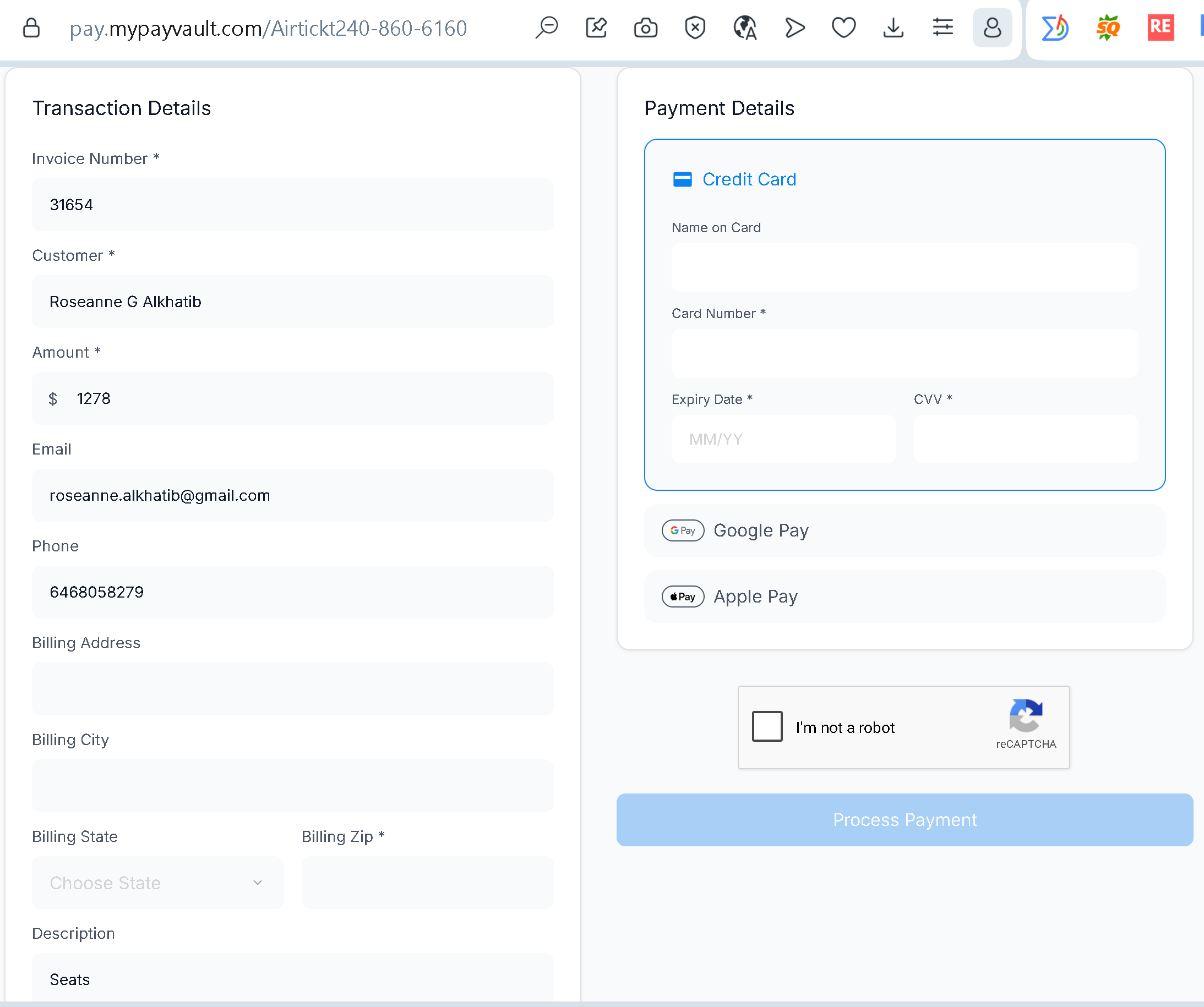
This image captures a live instance of an aggressive, targeted financial fraud operation known as a “Tech Support / Flight Booking Scam.” Unlike generic mass phishing, this method relies heavily on multi-channel social engineering and highly customized billing infrastructure to bypass traditional security detection.
The Vector of Attack
The deception begins before the victim ever encounters this payment gateway. Typically, the target receives an urgent email or SMS notification masquerading as an automated receipt from a well-known enterprise—frequently an airline, travel agency, or tech corporation.
The notification states that a substantial charge (in this case, $1,278) has already been authorized on their account for an item they never purchased (“Seats”). To create a state of panic, the message explicitly avoids containing a direct refund link. Instead, it provides a toll-free customer assistance number: 1-860-616-0240 (which the perpetrators subtly embedded directly into the URL path of the website).
The Call Center Intervention
When the panicked victim dials the provided number, they do not reach an automated enterprise system. They are connected directly to a fraudulent call center operative. The operative acts as a “support agent,” verifies the fake invoice number (31654), and assures the victim that they can reverse the pending transaction.
To “process the cancellation,” the operative generates a single-use, highly customized short link via an API and sends it to the victim via SMS or chat.
The Deceptive Interface Analysis
The screenshot reveals why this specific landing page is highly effective at exploiting human psychology and bypassing baseline technical automated defenses:
- Pre-Filled Immobilization (The JWT Exploit): Under “Transaction Details,” every field—including the victim’s full legal name, private email address, phone number, and exact target amount—is permanently hardcoded and locked. The fields are completely uneditable (editable: false inside the technical token). This creates an illusion of a secure, formal system that already “knows” who they are, reinforcing the false legitimacy of the support agent.
- The “Process Payment” Inversion: The psychological core of the trap relies on an absolute inversion of reality. The operative tells the victim that they are entering their payment details into a “secure cancellation portal” to verify their identity and receive a reverse credit. In reality, the victim is filling out a standard merchant billing portal. Clicking the blue button executes a live charge, immediately pulling $1,278 out of the victim’s account.
- Exploitation of Third-Party Trust: The page embeds official merchant integration styles for Google Pay and Apple Pay alongside a standard reCAPTCHA widget. The presence of these secure, recognizable global tech components lowers the victim’s critical suspicion, making them feel as though they are interacting with a heavily audited payment architecture.
Key Red Flags for Fraud Detection
- The Inversion of Refunds: Legitimate companies never require a customer to input a full credit card number, expiration date, and CVV code on a web form to receive an automated refund or cancellation.
- Raw IP and Unverified Domain Chains: The payment form relies on a completely unverified, external payment routing domain (mypayvault.com) that has no structural or legal affiliation with the company the victim initially believed they were contacting.
- URL Embedded Directives: Finding a phone number or consumer identifier hardcoded straight into the URL structure (/Airtickt240-860-6160) is a definitive technical marker of an automated campaign infrastructure rather than a standardized corporate billing route.
