The two screenshots show a two‑step PayPal phishing attack. The first page impersonates a security alert, claiming a login from an unrecognized device. The victim is pressured to click a button to “remove” that device, which leads to a fake PayPal login page where the victim’s email and password are stolen.
Threat Analysis: PayPal Phishing – Fake “New Device Detected” & Credential Harvesting
How the scam works (two steps):
Step 1 – Fake Device Detection Alert (First Screenshot)
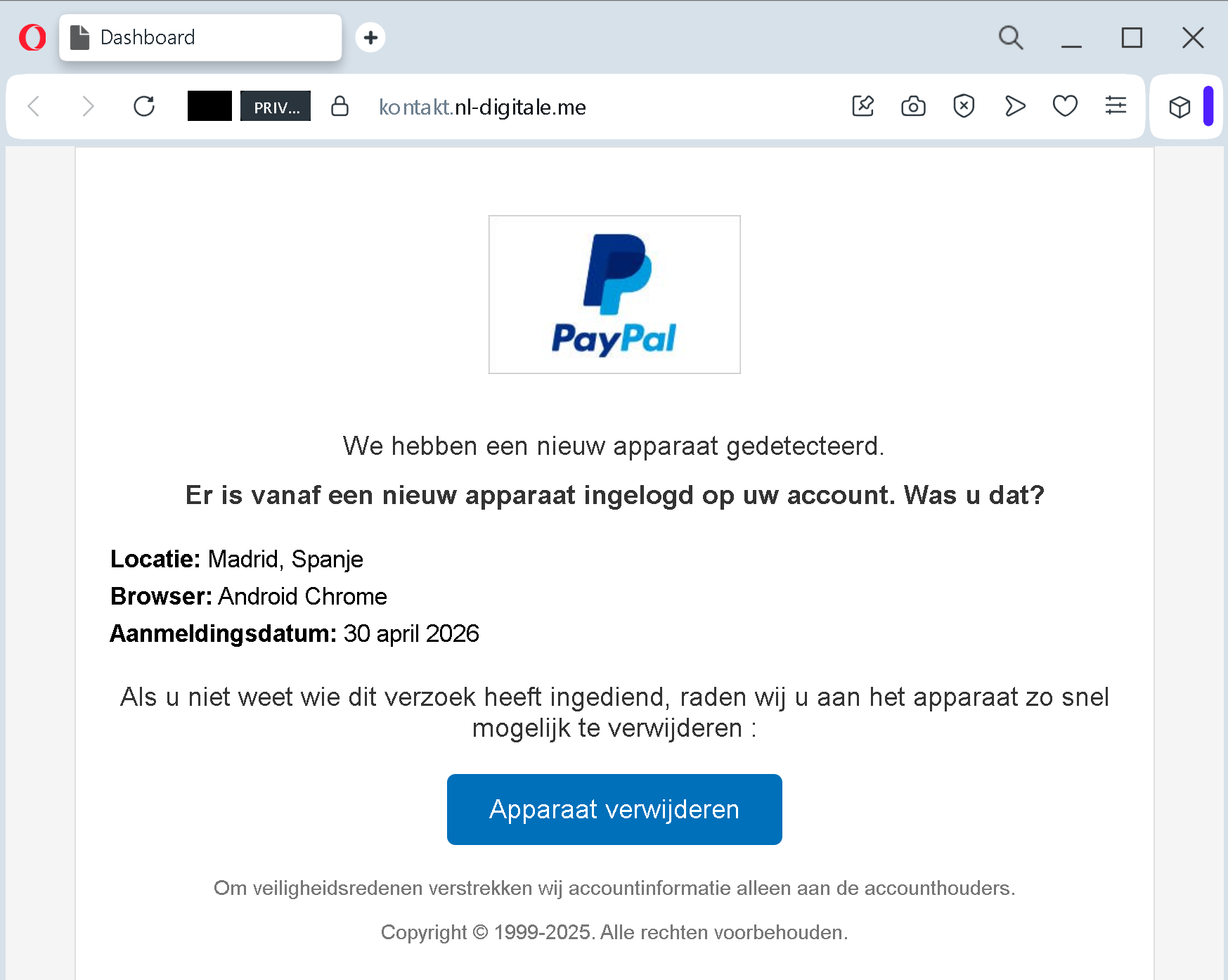
The victim receives an unsolicited email, SMS, or web pop‑up claiming that a new device has logged into their account. The message includes a fabricated location (e.g., Madrid, Spain), browser type (Android Chrome), and a recent date. It urges the victim to click a button to “remove the device” as a security measure.
Step 2 – Fake PayPal Login Page (Second Screenshot)
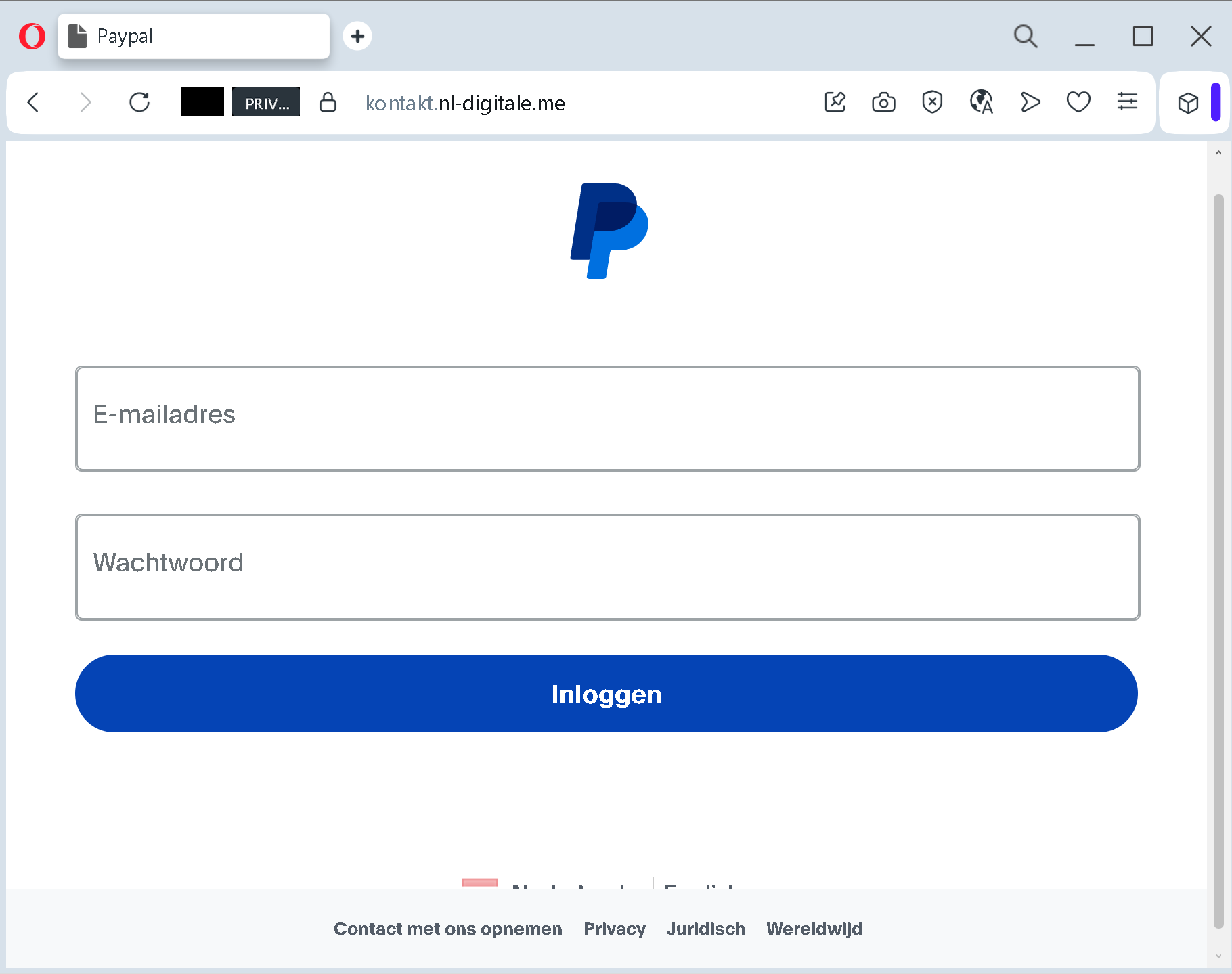
Clicking the button leads to a page that mimics the official PayPal login screen. The victim is asked to enter their email address and password. Once submitted, the credentials are sent directly to the attacker.
The goal:
The attacker steals the victim’s PayPal login credentials to:
- Access the PayPal account and view balance/transaction history
- Transfer funds or make unauthorized purchases
- Link the stolen credentials to other platforms where the same email/password combination is used
Red flags to watch for:
- Suspicious URL: The login page is hosted on a domain like
kontakt.nl-digitale.me, notpaypal.com. The first alert shares the same suspicious domain pattern. - Unsolicited security alert: PayPal never sends such alerts via random links. Real security notifications appear inside your PayPal account or come from official
@paypal.comemail addresses, and they never ask you to click a button to “remove” a device. - Threat / urgency: The message creates fear that an unauthorized device has accessed your account, pressuring you to act immediately without thinking.
- Generic design / missing account‑specific details: A real alert would include partial information about the actual device or location from your login history – this one uses generic placeholders.
- Copyright notice inconsistency: The footer shows “Copyright © 1999-2025”, but the alert itself uses a future year (2025) when the screenshot was taken earlier – a common sign of a templated phishing page.
What to do if you encounter this:
- Do not click the “Apparaat verwijderen” (Remove device) button.
- Do not enter your email or password on the following page.
- If you have already clicked and entered your credentials, change your PayPal password immediately, enable two‑factor authentication, and review recent account activity for any unauthorized transactions.
- Always access PayPal by typing
paypal.comdirectly into your browser. - Forward the suspicious email to
[email protected]and then delete it.
Protective measures:
- Never click links in unsolicited security alerts – always go directly to the official website.
- Use a password manager – it will not autofill on fake domains.
- Enable two‑factor authentication on your PayPal account (using an authenticator app, not SMS).
- Check the URL carefully – legitimate PayPal domains are
paypal.comandpaypal.nl(for the Netherlands). Look for misspellings, extra words, or unusual top‑level domains. - Be suspicious of any message that claims an unknown login and asks you to click a button to “fix” it.
