Below is a description of the Norwegian BankID phishing campaign shown in the screenshots. The attack attempts to harvest multiple layers of authentication data.
Threat Analysis: BankID Phishing – Full Credential & 2FA Harvesting (Norwegian Variant)
This multi‑step phishing campaign impersonates BankID, the common Norwegian electronic identification system used by most banks. The attacker’s goal is to collect enough information to log into the victim’s online bank and authorise fraudulent transactions.
How the attack works (six‑step flow):
Threat Intel: This deceptive layout was logged, cross-checked, and neutralized firsthand by the Antiphishing.biz security team during our automated link scanning workflows. To protect the public, the hostile origin link has been completely disabled within our infrastructure. We document and analyze these live visual patterns to help security researchers and users recognize deceptive clone designs before financial damage occurs.
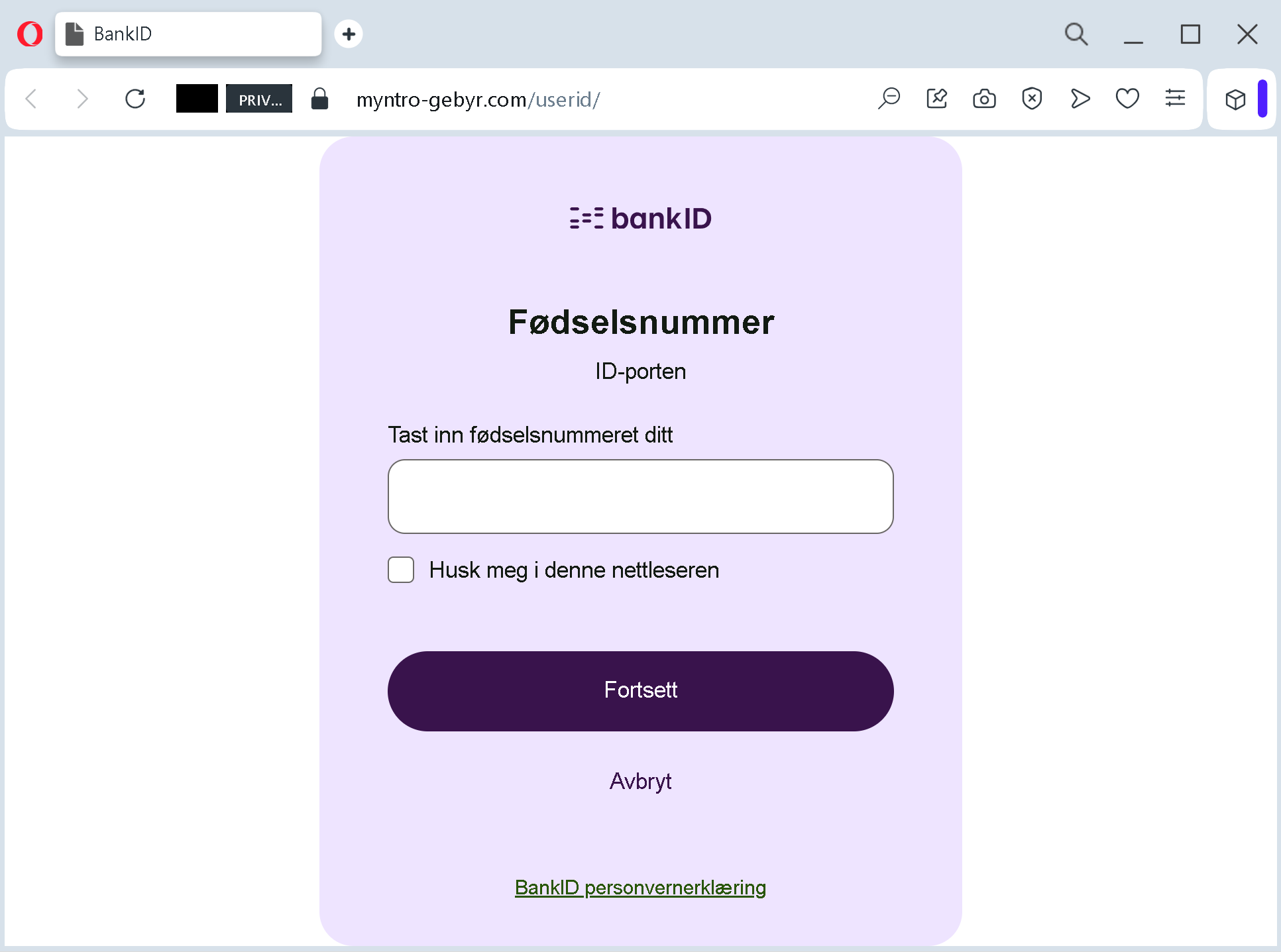
- Fødselsnummer (national ID) – The victim’s 11‑digit personal identification number is requested.
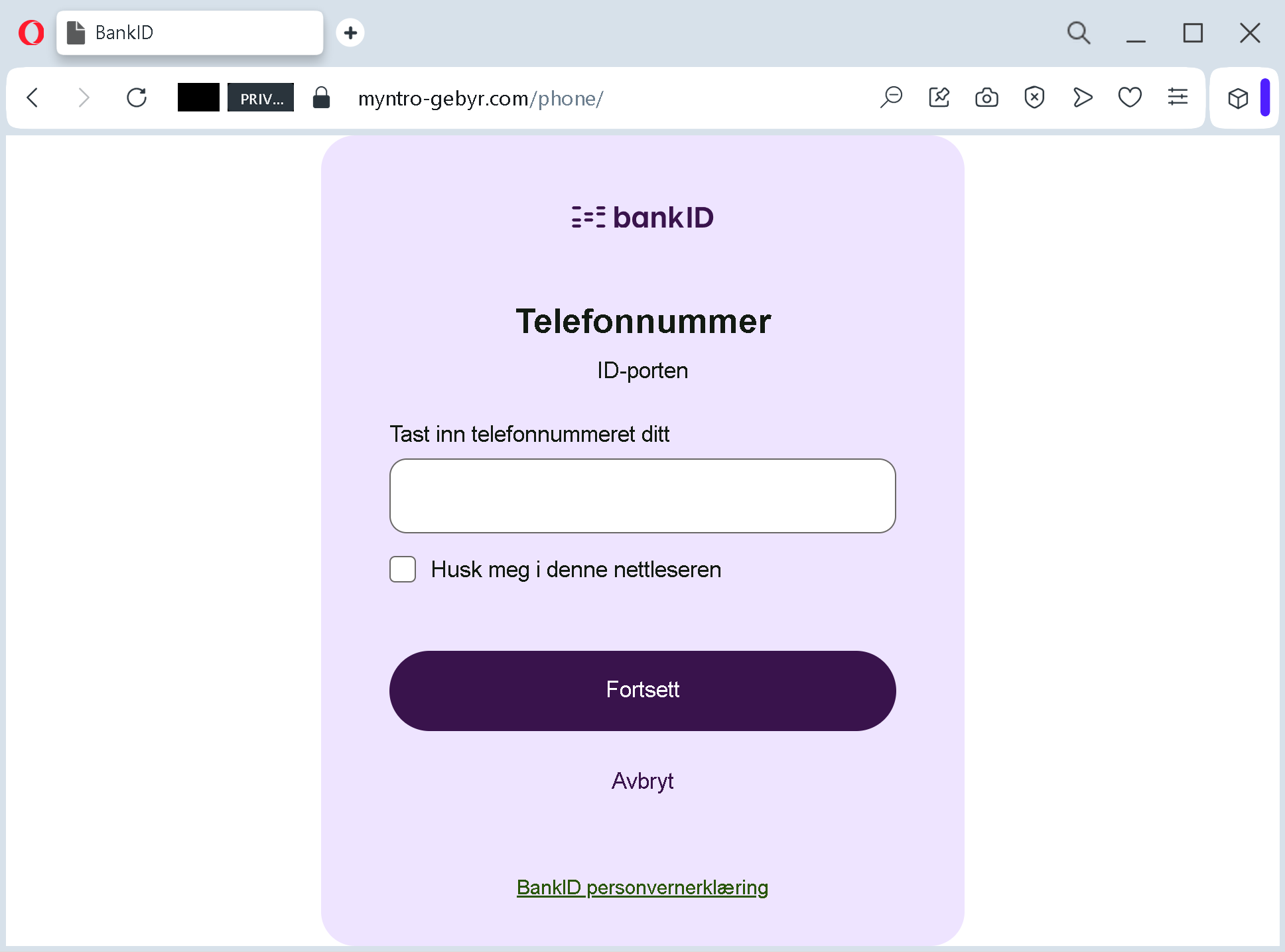
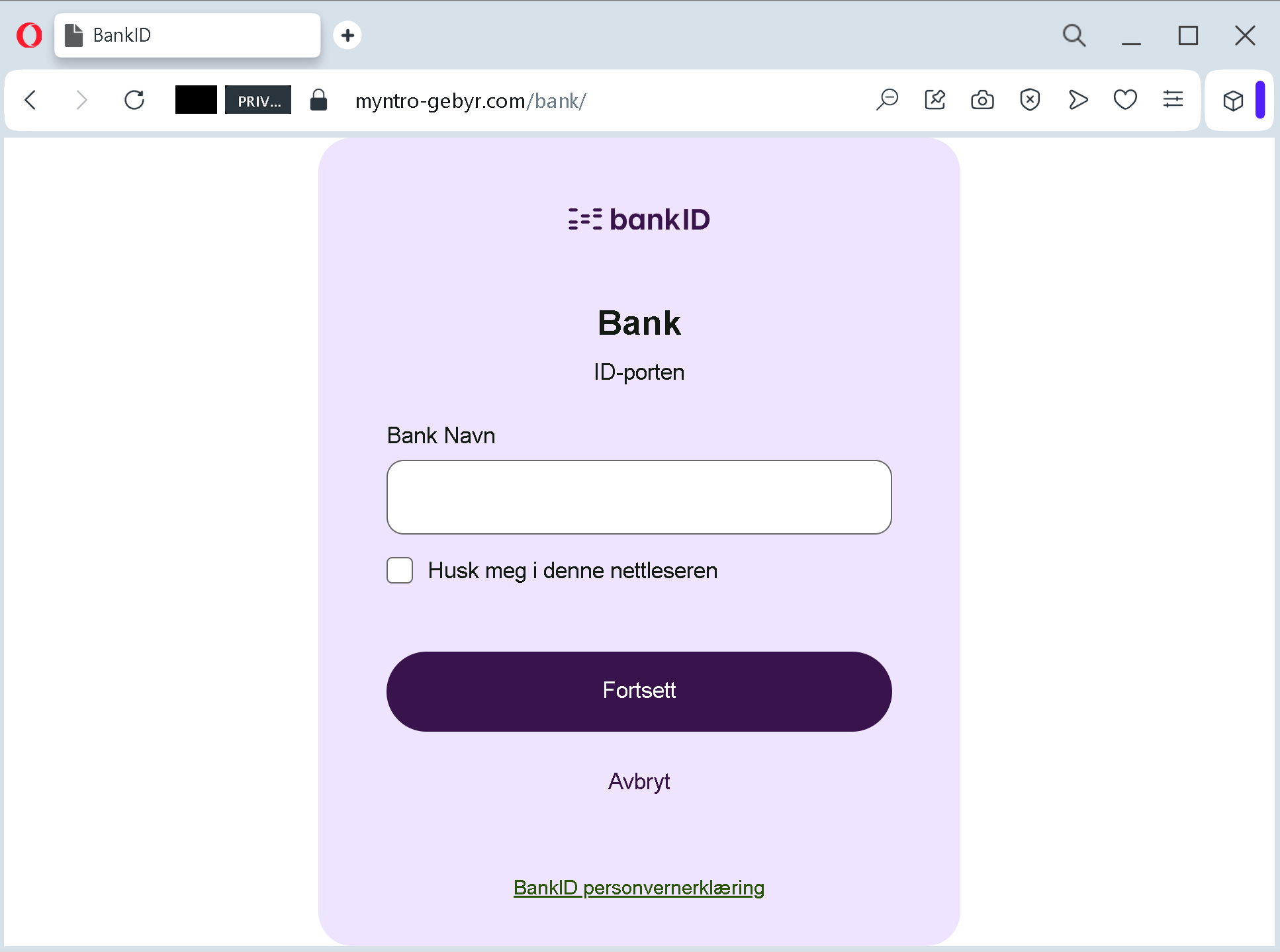
- Phone number – The victim is asked to enter their phone number (linked to BankID).
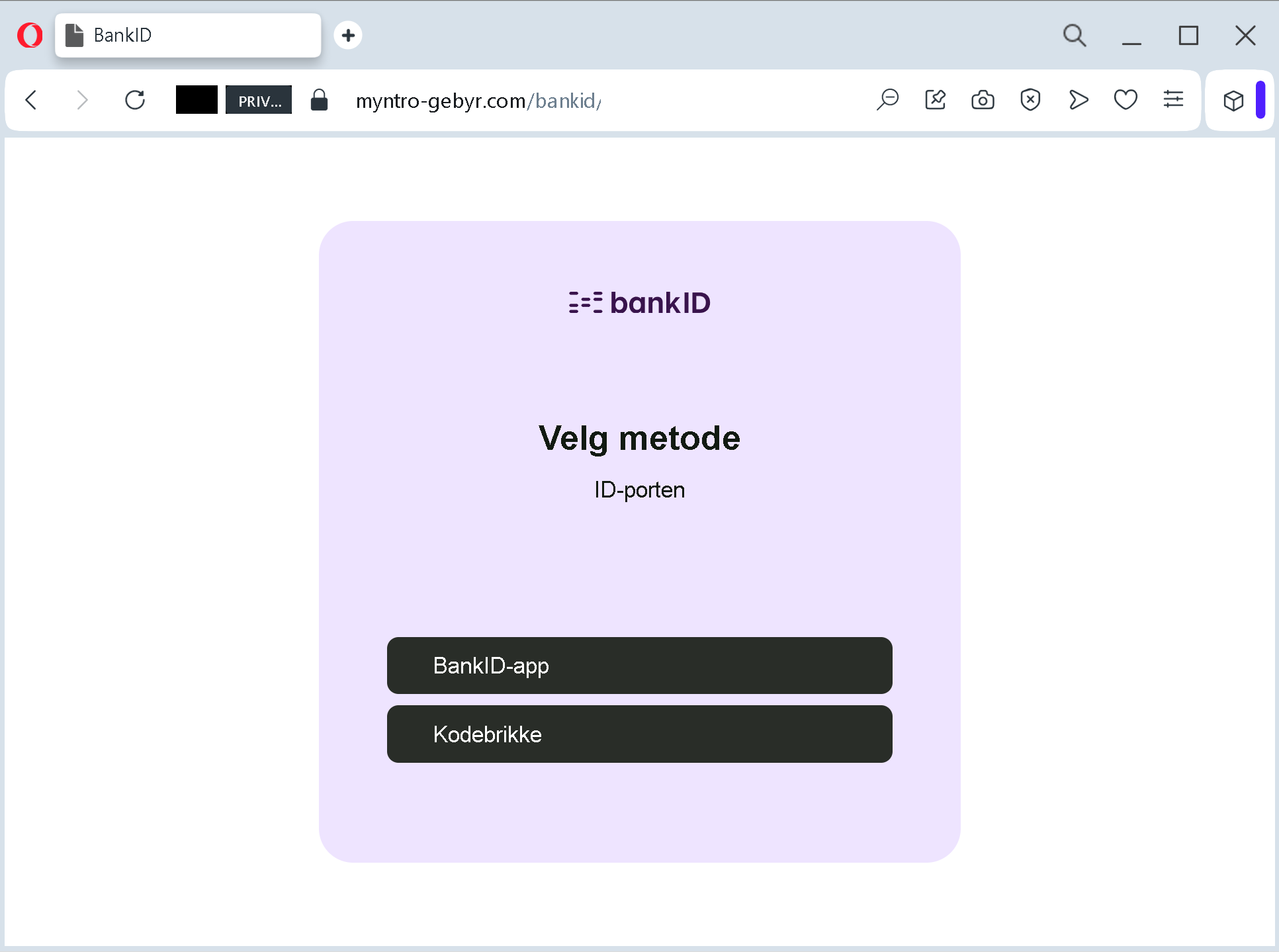
- Choice of BankID method – The victim selects between using the BankID app or a kodebrikke (physical code generator).
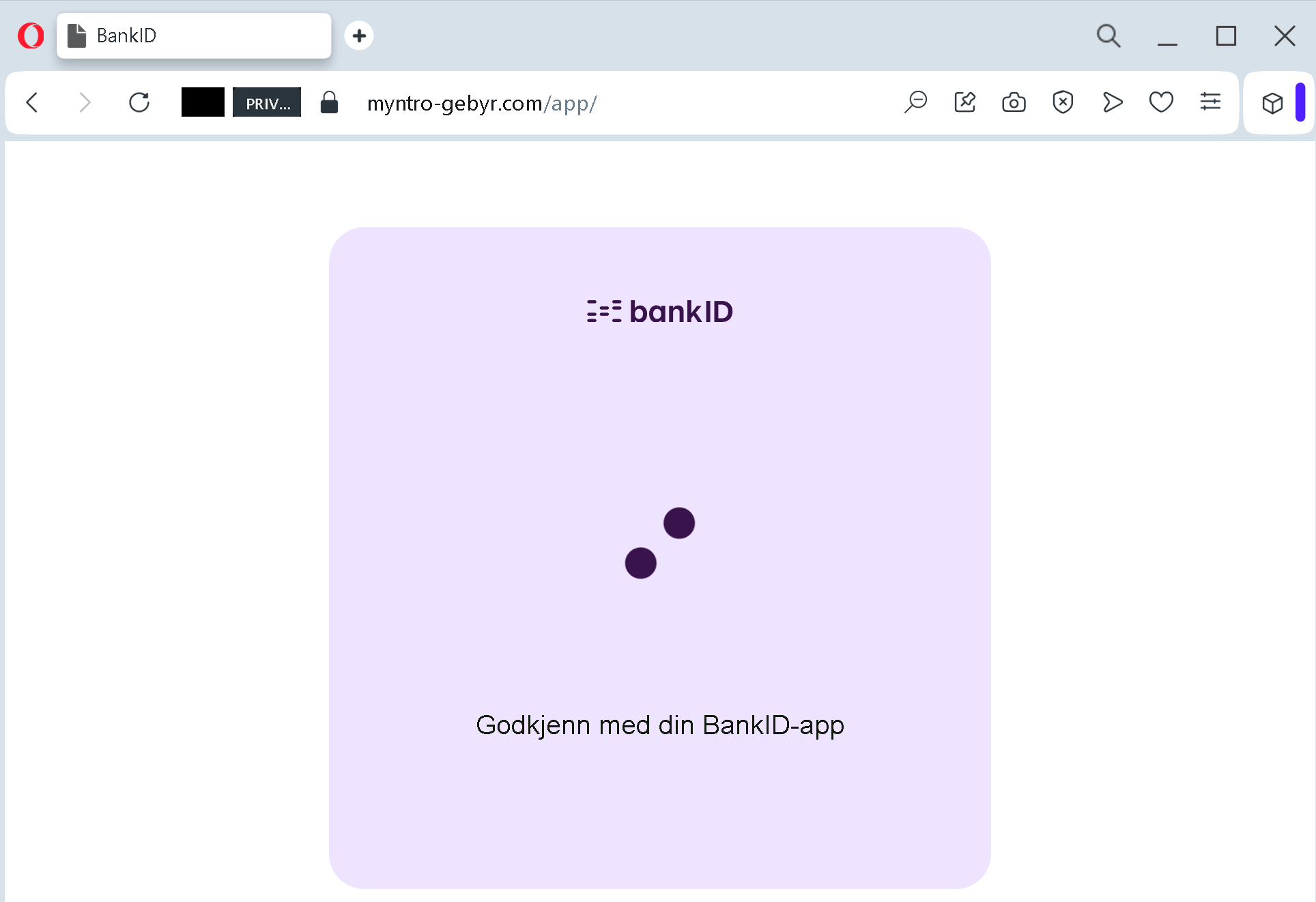
- If “app” is chosen – The victim sees a page stating “Godkjenn med din BankID‑app” (Approve with your BankID app). This is a waiting step, while the attacker uses the previously collected data to trigger a real push notification in the official app.
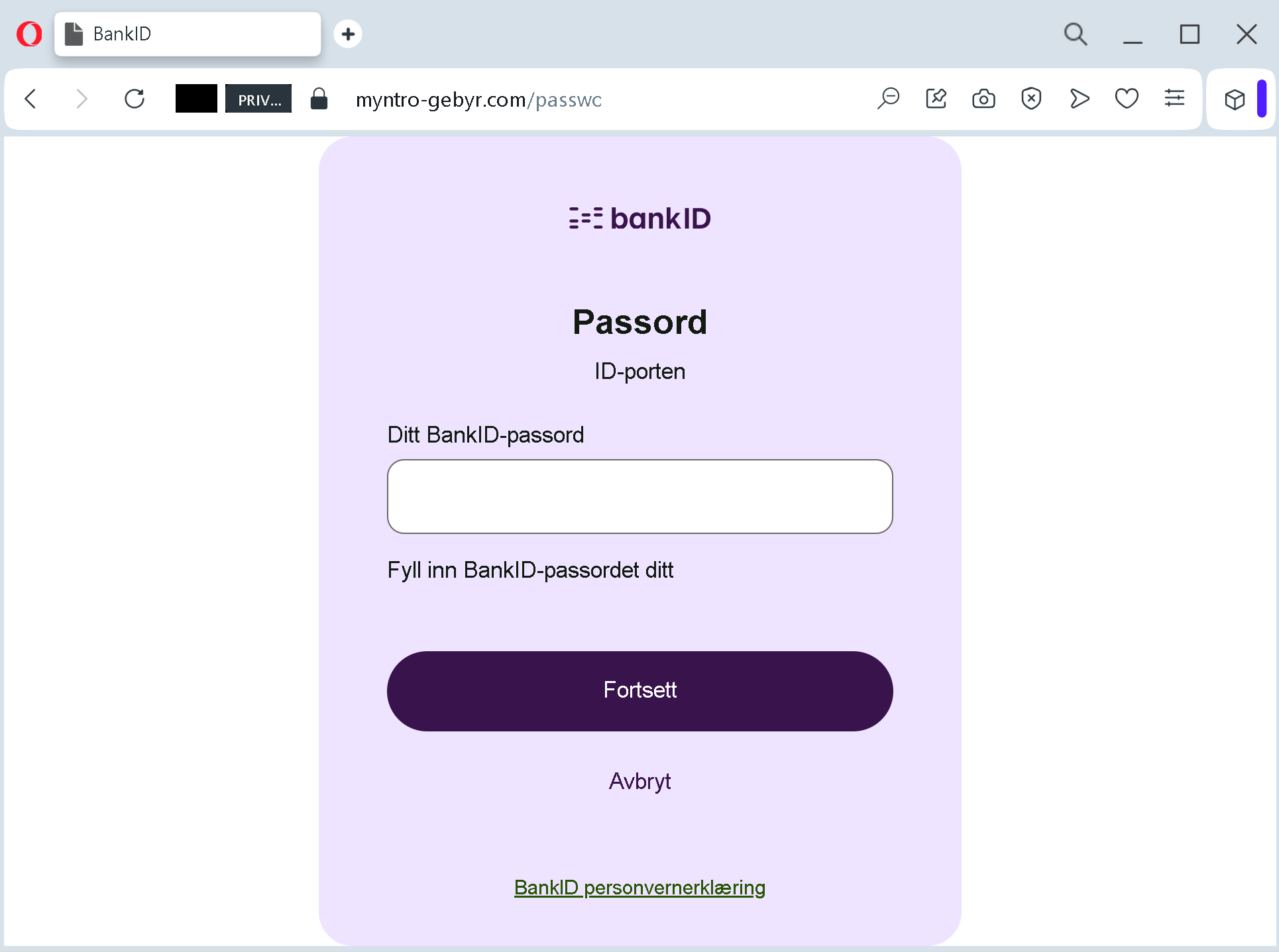
- If “kodebrikke” is chosen – The victim is asked for their BankID password (the one used with the physical code generator).
- Additional steps – Depending on the variant, the attacker may also ask for a response from the code generator or for an SMS‑code, all captured in real time.
The goal:
The attacker collects:
- Phone number (used to identify the victim in the banking system)
- National ID number (fødselsnummer)
- BankID password (if the code generator method is used)
- In the case of the app method, the attacker will also capture the push‑notification approval (by tricking the victim into approving a fraudulent login or transaction).
With this information, the attacker can:
- Log into the victim’s bank account
- Authorise payments or money transfers
- Commit identity theft or sell the data
Red flags to watch for:
- Suspicious URL: The pages are hosted on
myntro-gebyr.com(and subdomains), not on any official Norwegian bank or BankID domain (e.g.,bankid.no). - Unsolicited request: You should never receive a link to enter your BankID credentials. Real BankID authentication always starts from the bank’s official website or app, not from an external link in a message.
- Multiple steps with increasing sensitivity: A legitimate BankID login asks for either a single push notification or a one‑time code, not for phone number, national ID, password, and choice of method all in one session.
- Mixed Norwegian / English wording: Official BankID pages are consistently in Norwegian (Bokmål or Nynorsk). The presence of “ID‑porten” (the national authentication portal) is real, but the URL gives it away.
- No personalisation: Legitimate BankID steps show a partially masked name or a known device – this page does not.
What to do if you encounter this:
- Do not enter any personal information, BankID password, or approve any request from your BankID app.
- If you have already entered your phone number and fødselsnummer, contact your bank immediately to block your BankID.
- If you have entered your BankID password, change it immediately (through the official bank website, not via any link).
- If you approved a push notification from your BankID app, call your bank’s fraud department immediately – the attacker may already have authorised a transaction.
- Always access BankID by typing your bank’s official URL directly or by using the official BankID‑app without any external link.
Protective measures:
- Never click links in unsolicited messages claiming payment issues, package delivery, or account problems – especially if they ask for BankID.
- Use a password manager – it will not autofill on fake domains.
- Enable BankID with push notifications (app) – and never approve a request unless you have just initiated a login yourself.
- Check the URL carefully – legitimate BankID pages are on
bankid.noor your bank’s domain. - If in doubt, contact your bank directly using a phone number from your bank card or official website – never use numbers from a suspicious message.
