A sophisticated phishing campaign targeting BAC Credomatic customers uses “Token Synchronization” to steal credentials and real-time OTP codes via fake banking portals, often distributed through Smishing or email. The attackers use high-fidelity clones of the bank’s portal to trick users into entering their username, password, and Código BAC, aiming to bypass multi-factor authentication for fraudulent transactions. To avoid this, users are advised to never follow links in security messages and only enter tokens when initiating transactions within the official app.
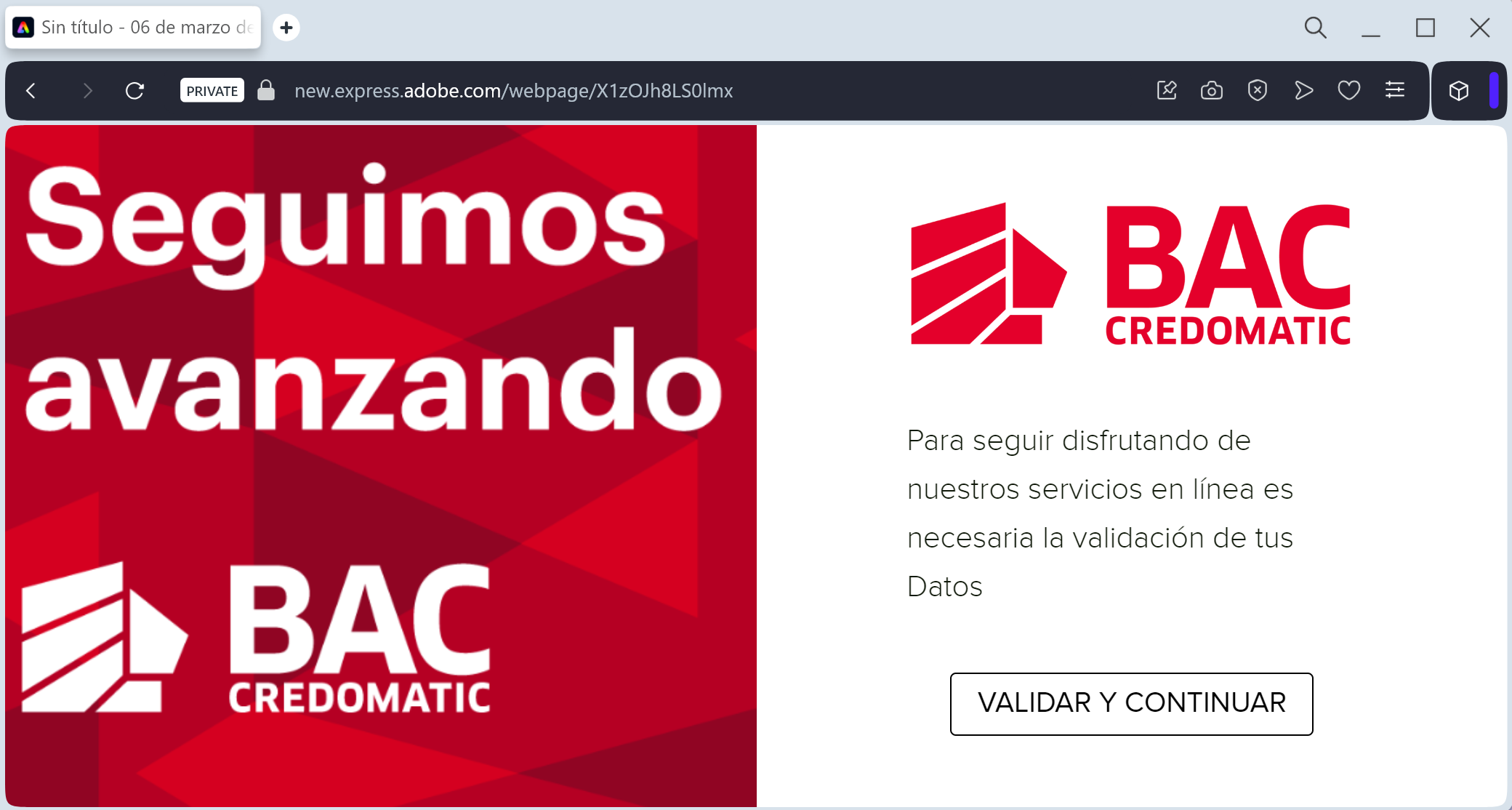
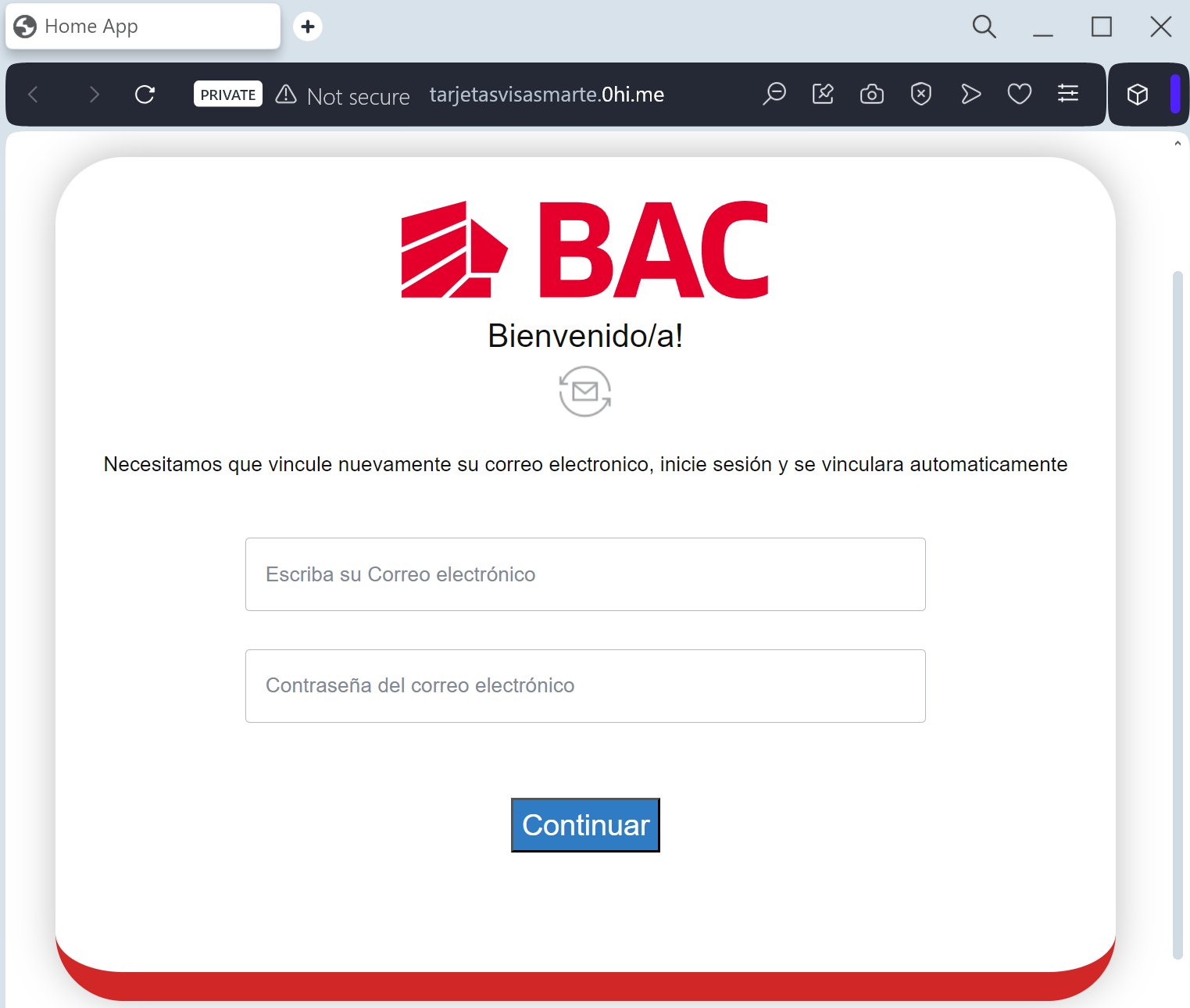
This case highlights a critical phishing threat targeting BAC Credomatic users, employing a “Digital Security Update” pretext to steal credentials, credit card details, and real-time Banca Móvil/Código BAC security codes. Scammers act as a “middleman,” utilizing intercepted OTP codes immediately to authorize fraudulent transfers or register new devices to the victim’s account. To protect against this, never enter security tokens to verify or unblock an account, and always use the official app rather than clicking links in alerts.
