
Free Fire “Skin Generator” Scam – Facebook Credential Harvesting
This phishing campaign targets players of Free Fire, a popular mobile battle royale game developed by Garena. The scam promises free in-game skins and diamonds through a fake “generator” tool. In reality, it is a multi-step scheme designed to steal victims’ Facebook login credentials (the primary method of logging into Free Fire on many devices).
How it works:
The victim encounters a link to this scam via YouTube videos, TikTok, Discord, Instagram, or other social media platforms, often with captions like “Free Fire Free Diamonds Generator 2023” or “Get Free Skins No Human Verification.”
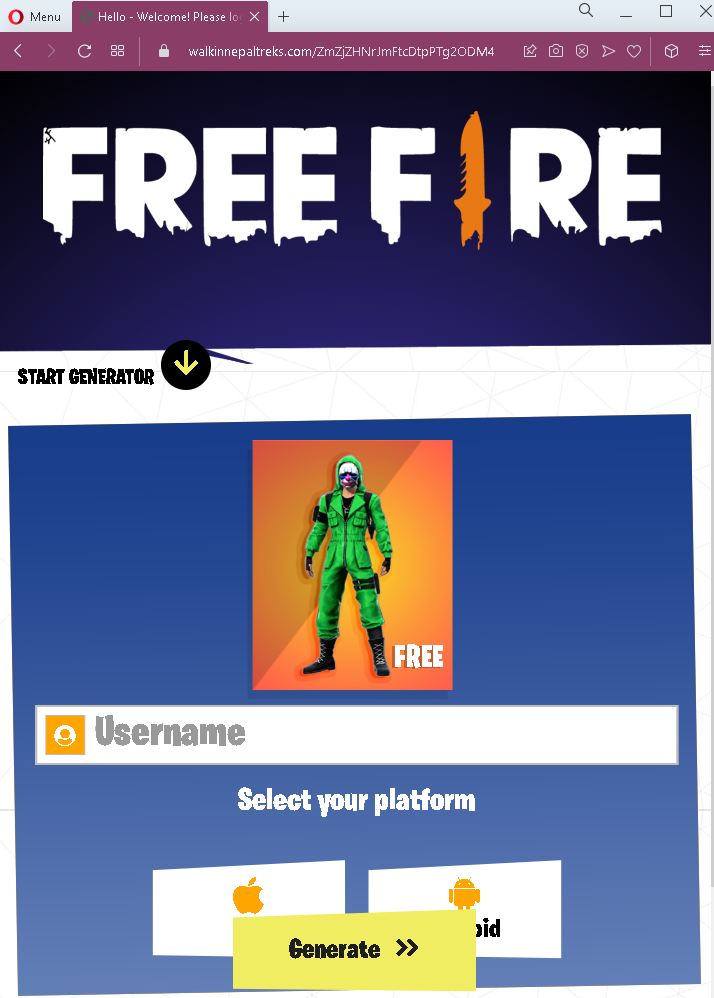
Step 1 – Selection Page (First Screenshot)
The victim is presented with a page showing various skins (e.g., “Chocolate”) and diamonds. The interface mimics a legitimate selection menu, asking the user to choose what they want to “generate.”
Step 2 – Username & Platform Entry (Second Screenshot)
The victim is asked to enter their Free Fire username and select their platform. This is designed to make the scam feel personalized and legitimate.
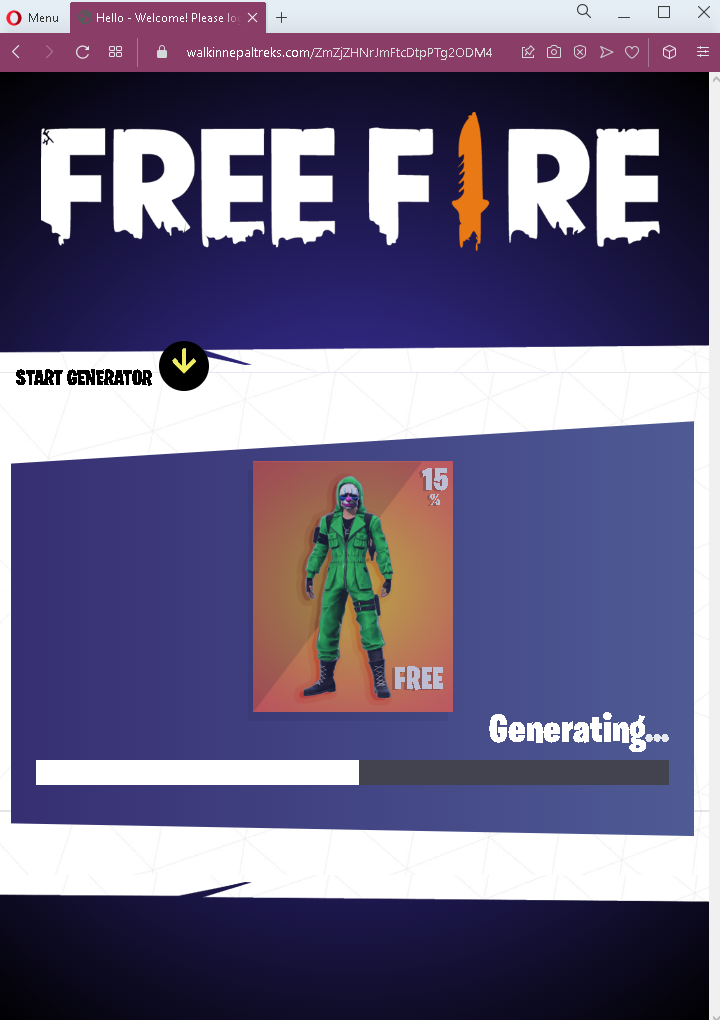
Step 3 – Fake Progress Indicator (Third Screenshot)
A progress bar appears showing “Generating…” with a percentage (e.g., 15%). This builds anticipation and tricks the victim into believing the generator is working.
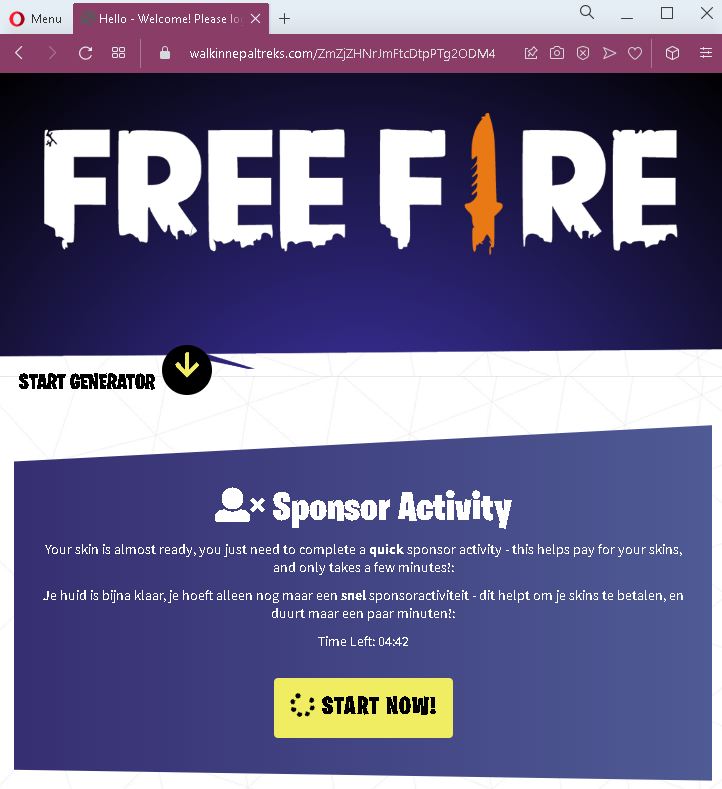
Step 4 – “Sponsor Activity” Requirement (Fourth Screenshot)
After the fake generation, the victim is told that to complete the process, they must complete a “sponsor activity” – typically described as a quick verification step that “helps pay for your skins.” A countdown timer (Time Left: 0442) creates urgency. The text appears in multiple languages (English and Dutch) to target a broader audience.
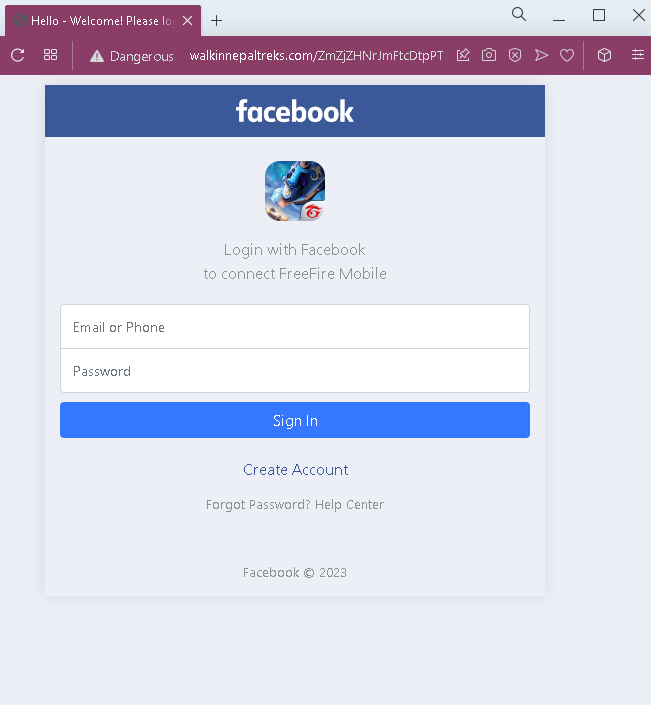
Step 5 – Facebook Login Phishing Page (Fifth Screenshot)
The “sponsor activity” leads to a fake Facebook login page. This page asks for:
Email or Phone
Password
Once the victim enters their Facebook credentials, the information is sent directly to the attacker.
The goal:
The attacker steals the victim’s Facebook login credentials. Since many Free Fire players log into the game using their Facebook account, gaining access to the Facebook account effectively gives the attacker control over the victim’s Free Fire account as well. Attackers can then:
Steal or sell the Free Fire account
Access personal information linked to Facebook
Use the compromised Facebook account to spread the scam further to the victim’s friends
Red flags to watch for:
“Too good to be true” offer: No legitimate service provides free in-game currency or rare skins through an external “generator.” Such items must be purchased or earned through official game events.
No official branding: The pages use generic “FREE FIRE” text but lack official Garena branding, logos, or copyright notices.
Request for credentials: The final step asks for Facebook login details. No legitimate in-game reward system ever requires entering Facebook credentials on a third-party site.
Fake “sponsor activity” concept: The “sponsor activity” is a common phishing tactic to justify why the user must complete an additional step, often involving a credential harvest or survey scam.
Multiple languages: The presence of Dutch text alongside English suggests a broad targeting but also indicates unprofessional localization—official Garena communications are consistently in one language per region.
Countdown timer: The timer creates artificial urgency to pressure the user into completing the “verification” without thinking.
Suspicious URL: All pages are hosted on domains that are not garena.com or facebook.com.
What to do if you encounter this:
Do not enter your Free Fire username, select a platform, or proceed through any steps.
Do not enter your Facebook email/phone and password on the final page.
If you have already entered your Facebook credentials, change your Facebook password immediately, enable two-factor authentication (2FA), and check for any unauthorized activity.
If you use the same password for other accounts, change those passwords as well.
Report the phishing page to Facebook and to Garena (Free Fire’s developer).
Why this scam is effective:
Free Fire is extremely popular, especially among younger audiences who may be eager for free in-game items. The multi-step process with progress bars and “sponsor activity” explanations makes the scam feel elaborate and legitimate. The use of Facebook as the final credential harvest is strategic because many Free Fire players have their game progress tied directly to their Facebook account—losing Facebook access means losing their game progress and purchases.
Protective measures:
Never trust third-party “generators” or “hacks” that promise free in-game currency or items. They are always scams.
Enable two-factor authentication (2FA) on your Facebook account to protect it even if your password is stolen.
Log into Free Fire only through the official app and official Garena methods.
Educate younger gamers about these scams, as they are frequently targeted.
