A phishing campaign targeting Steam users with fake digital gift cards that steal credentials and 2FA codes for full account takeover. Scammers utilize realistic clones of the Steam login page and real-time Steam Guard code interception to hijack accounts and steal virtual items.
Analysis Memo: This deceptive layout was intercepted, verified, and locked down firsthand by the Antiphishing.biz security team during our daily link moderation procedures. To protect the public, the phishing source domain has been fully defanged within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.


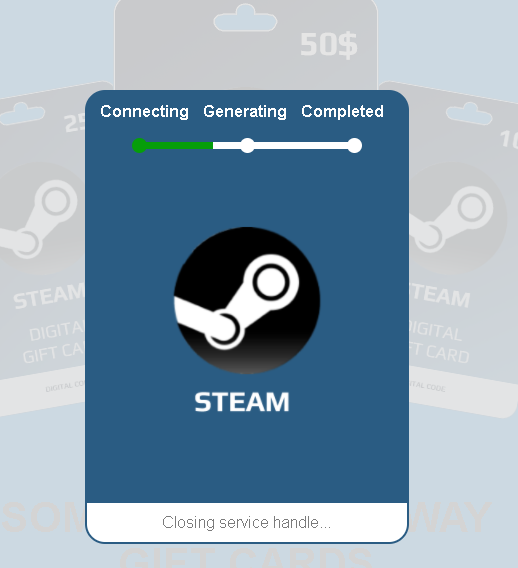
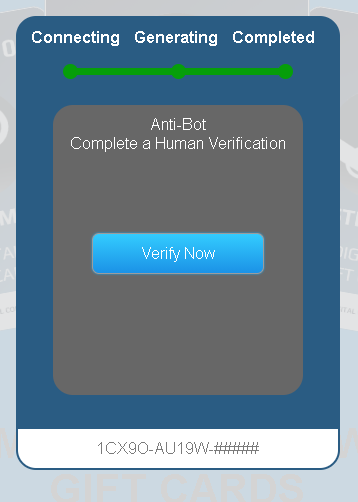

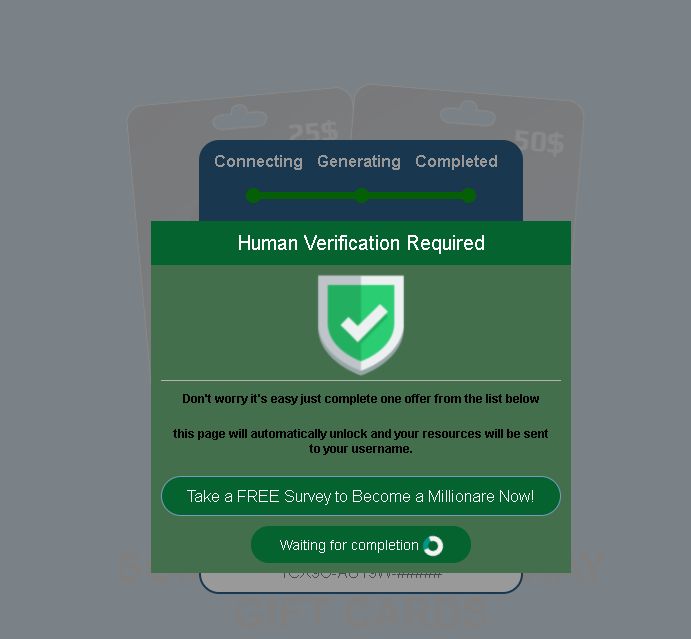
The “Steam Digital Gift Card” and “Walmart Gift Card” cases exemplify a “Reward Baiting” social engineering attack designed to steal user credentials through fake verification steps. By promising high-value rewards, scammers lure victims into entering login data on phishing sites to gain full account access.
Expert Security Tip: The “Free Reward” Verification Trap
- The Trap: Attackers use convincing, high-quality landing pages to promise free $50-$100 gift cards, requiring users to complete “human verification” (surveys, app downloads) before stealing credentials via a fake login page.
- Protection Method:
- “No Free Lunch” Rule: Major brands do not offer high-value gift cards via third-party surveys; such offers are scams.
- Verify Domain: Only trust official domains (e.g., steampowered.com); any variation is likely phishing.
- Never Login via Reward Link: A requirement to log in to claim a gift is a direct credential theft attempt.
- 2FA Red Flag: Never enter a 2FA code (Steam Guard/SMS) to claim a reward, as this authorizes a hacker’s login.
