An analysis of a phishing campaign targeting Crédit Agricole customers reveals attackers preparing fraudulent infrastructure to intercept “SécuriPass” multi-factor authentication. The pre-emptive case study shows attackers setting up fake login pages designed to harvest account numbers and PINs to bypass security measures. The report highlights crucial indicators of compromise, including suspicious non-official domains and unsolicited “urgent” security alerts.
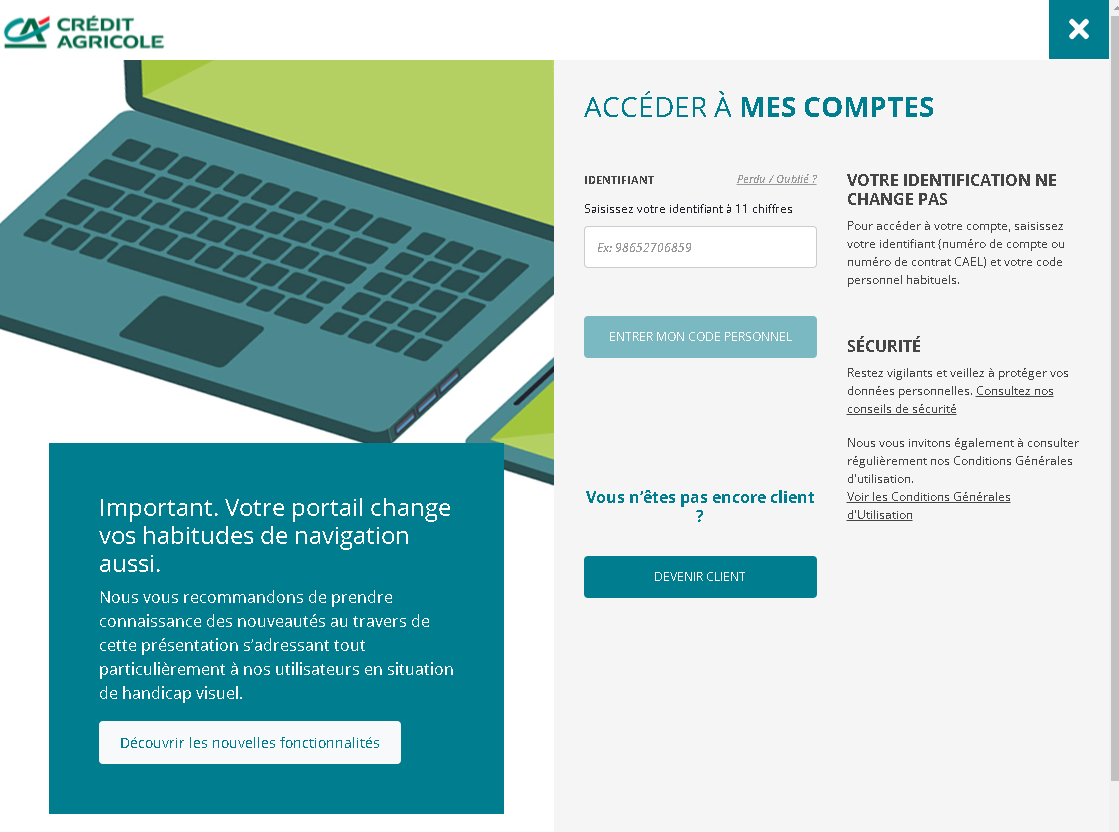
Screenshot #1 (Identifiant): This page captures the 11-digit account number, validating the victim’s customer status in real-time.
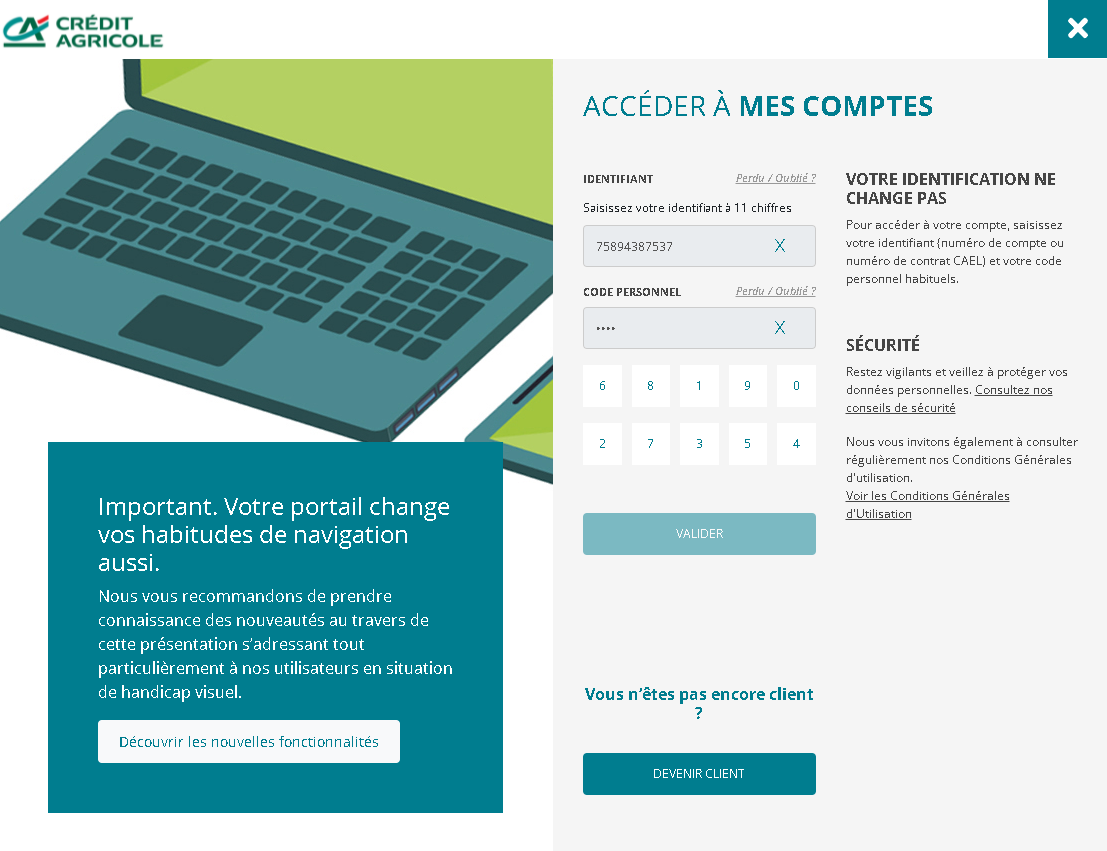
Screenshot #2 (Code Personnel): A fake virtual keypad captures password digits via keylogging, mimicking bank security.




Screenshot #3 (Processing Screen): The “wait” screen allows attackers time to use stolen credentials for unauthorized access on the real banking site.
A “staging” phishing attack against Crédit Agricole, allowing for early detection of infrastructure designed to capture account IDs and 6-digit codes via a cloned virtual keypad and real-time interception. The phishing campaign utilizes a fake login screen (“Identifiant”) and a deceptive loading screen to log credentials and facilitate a Man-in-the-Middle attack.
Protection Measures:
- Verify that the URL is exactly www.credit-agricole.fr.
- Never log in via links in emails or SMS.
- Reject unexpected SécuriPass notifications.
- Use the official “Ma Banque” mobile app.
