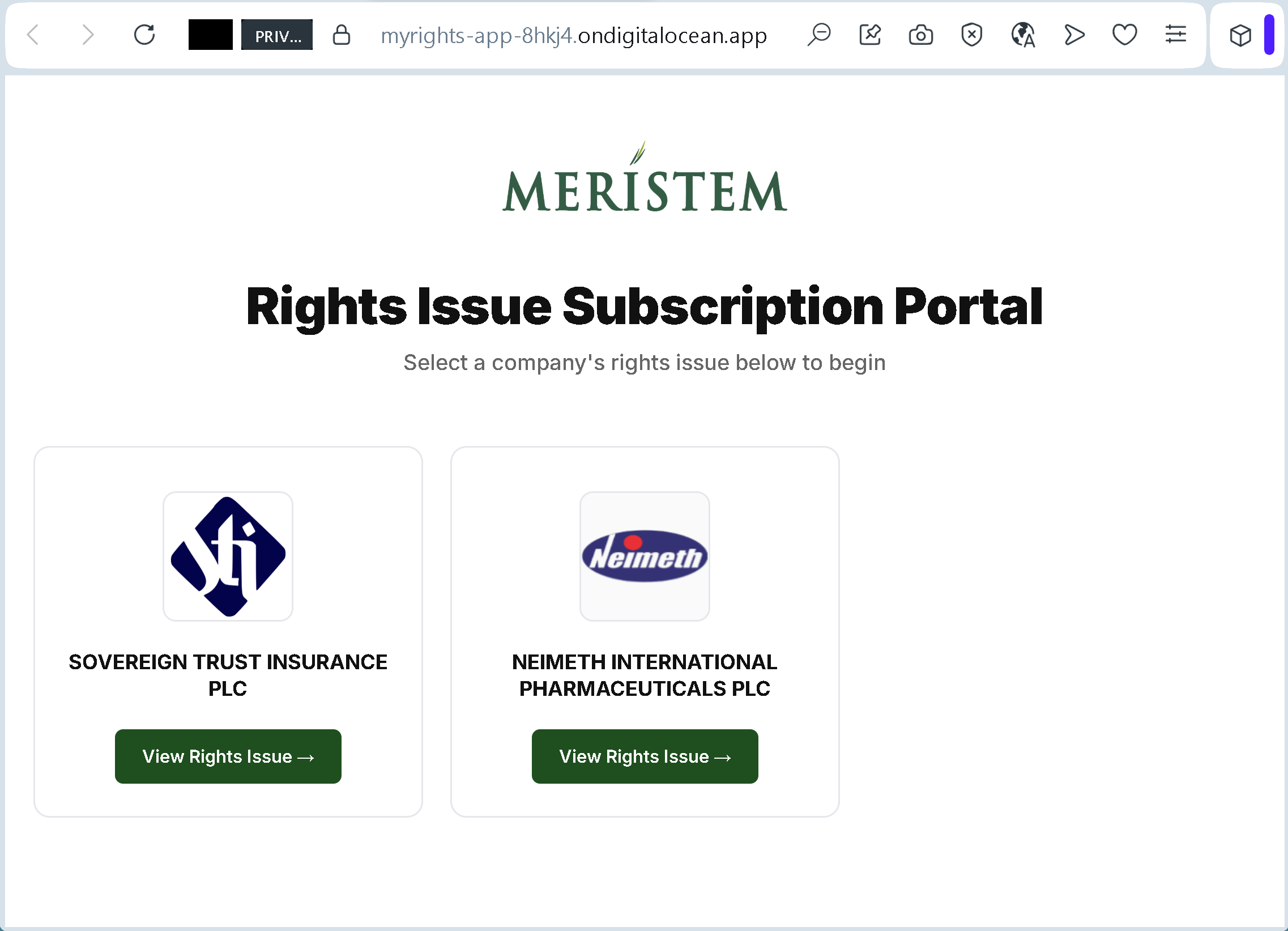
This image captures an active, highly targeted corporate asset hijacking portal hosted via developer cloud infrastructure (myrights-app-8hkj4.ondigitalocean.app). The interface demonstrates a sophisticated evolution in credential harvesting, utilizing a live, interactive database to verify victim telemetry in real time rather than deploying static phishing layouts.
Infrastructure and Dynamic Exploitation Analysis
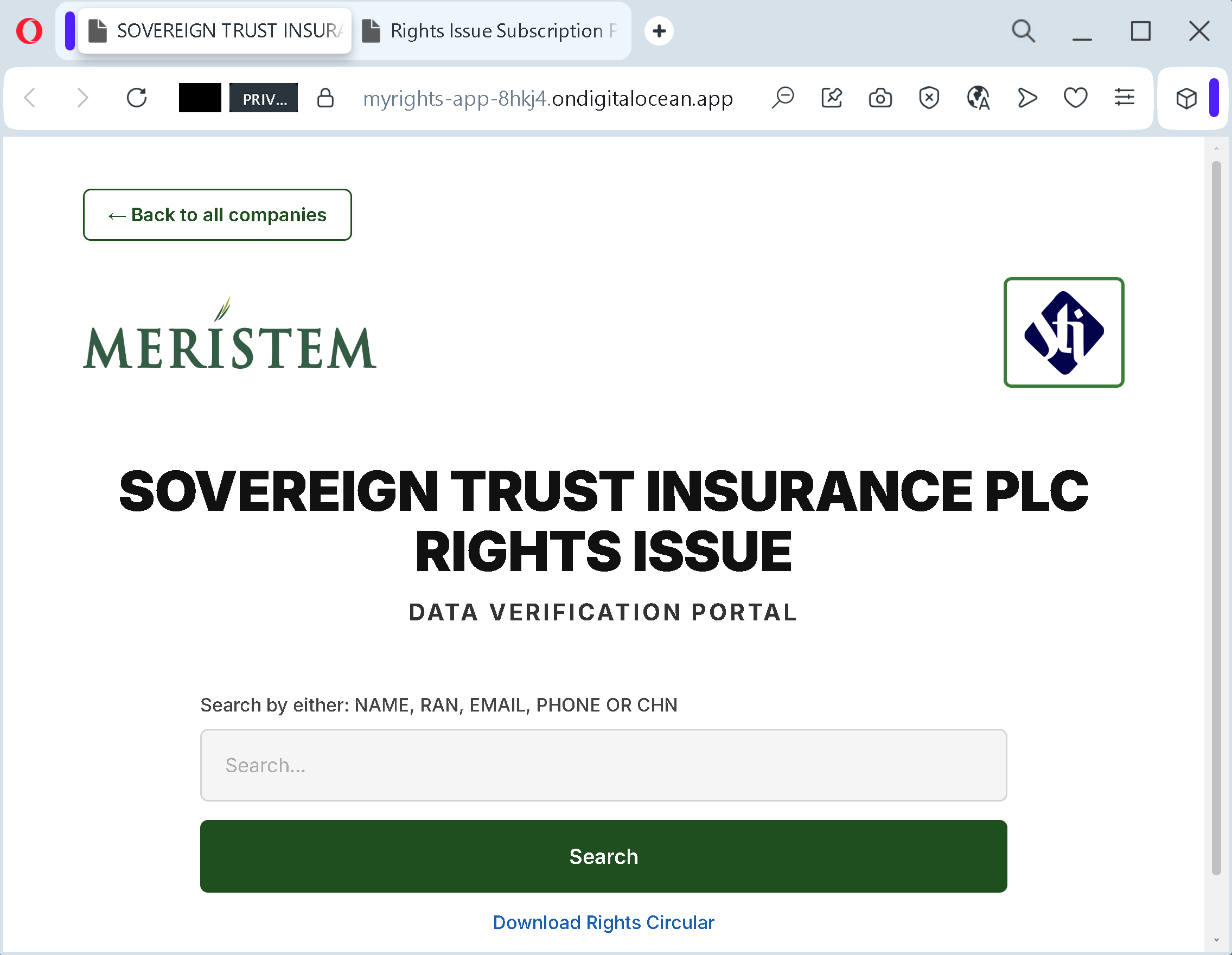
The fraudulent portal directly impersonates the identity of Meristem Registrars, an established stock registrar entity. The technical execution of this data harvesting operation functions through several critical components displayed in the compromised panel:
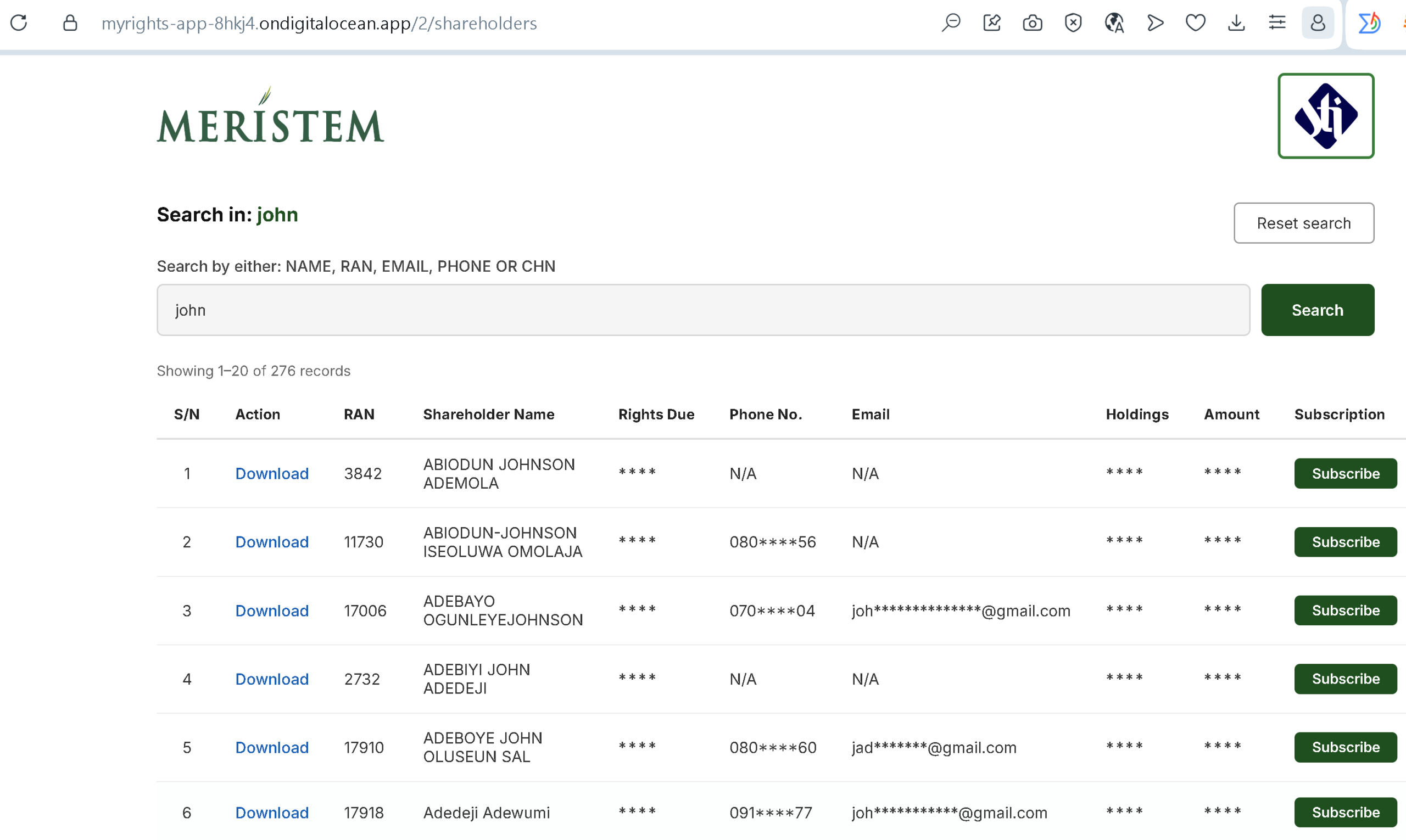
- Live Database Infiltration and Search Queries: The interface features a functional, dynamic search module allowing users to query records by Name, RAN (Registrar Account Number), Email, Phone, or CHN. A live query for the term “john” demonstrates the processing of an active database containing at least 276 authentic records of high-value corporate shareholders.
- Psychological Validation Mechanisms: The display of actual shareholder names alongside genuine assigned RAN identifiers (e.g., 3842, 11730) creates immense cognitive trust for the target. To reinforce the illusion of a secure, compliant banking system, the architecture strategically masks partial phone numbers and email addresses, mimicking official corporate data protection standards.
- The Call-to-Action Theft Vector: The interactive elements labeled “Download” and “Subscribe” serve as the direct monetization nodes. Once a victim identifies their name in the registry and initiates interaction, the platform prompts the user to input unmasked clearing house numbers, multi-factor authentication tokens, and direct bank routing codes to fraudulently redirect dividends and equity ownership parameters.
Strategic Mitigation Protocols
This instance demonstrates that modern phishing campaigns leverage robust backend databases to execute highly localized corporate fraud. Web routing engines must implement immediate, absolute pattern blocking on the exact sub-domain string. The presence of dynamic lookup tables targeting sovereign financial registries on completely unverified SaaS application instances constitutes a definitive sign of active cyber-financial warfare and requires systematic blacklisting across all secure edge proxies.
