Our system just neutralized a sophisticated Pump & Dump scheme targeting the Singaporean market using North African infrastructure.
The Technical Anatomy of the Attack:
- Target Audience: Users in Singapore 🇸🇬.
- Traffic Vector: Paid advertisements on TikTok.
- Infrastructure: Managed from Morocco 🇲🇦 (IP cluster 154.144.253.x).
Deep Dive into TikTok Ads Metadata:
Our engine intercepted the link containing specific tracking parameters used by professional fraud-arbitrageurs:
- utm_source=tiktok & utm_medium=paid: Confirmed high-budget bypass of organic content filters.
- utm_id=CAMPAIGN_ID: A dynamic macro used in TikTok Ads Manager, indicating a template-based, scalable attack.
- utm_campaign=CAMPAIGN_NAME: Evidence of an automated “industrial” approach to scam distribution.
The Fraud Mechanism:
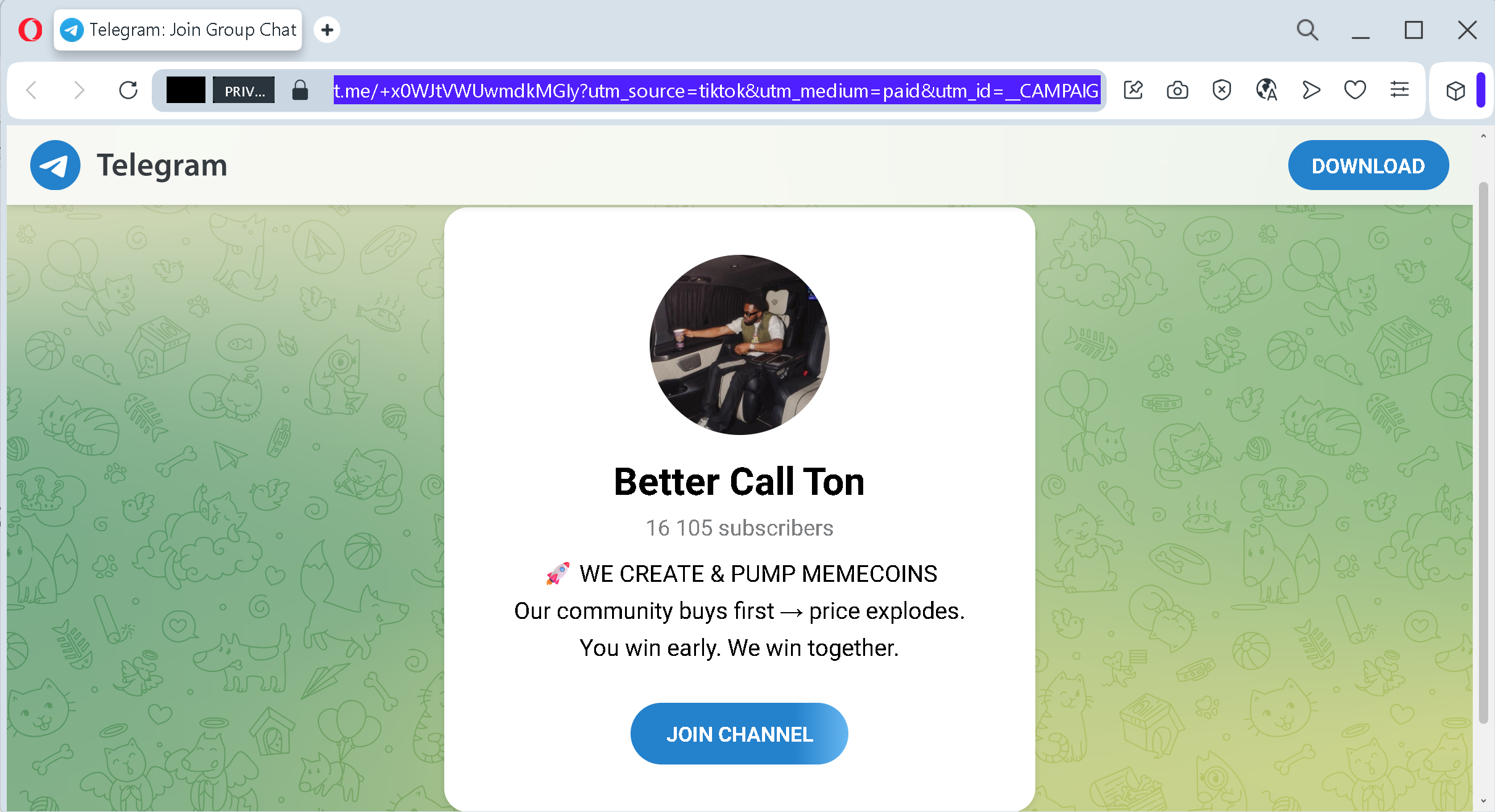
Scammers use paid TikTok ads to target affluent regions (Singapore) with “get-rich-quick” narratives. The traffic is funneled to a private Telegram channel “Better Call Ton”, where organizers manipulate TON-based memecoins. Our Covariance Matrix flagged the 10/10 risk score due to the extreme geographical mismatch and the use of automated advertising macros to promote market manipulation.
The Verdict:
The link is Permanently Blocked. The author’s IP is Blacklisted.
By analyzing metadata patterns, Antiphishing.biz stops fraudulent campaigns before they reach their peak.
