Crédit Mutuel de Bretagne (CMB) “Security Key” Phishing
Target: Customers of Crédit Mutuel de Bretagne (France / Brittany region)
Threat Level: Critical (Real-time Account Takeover & “Clé Digitale” Hijacking)
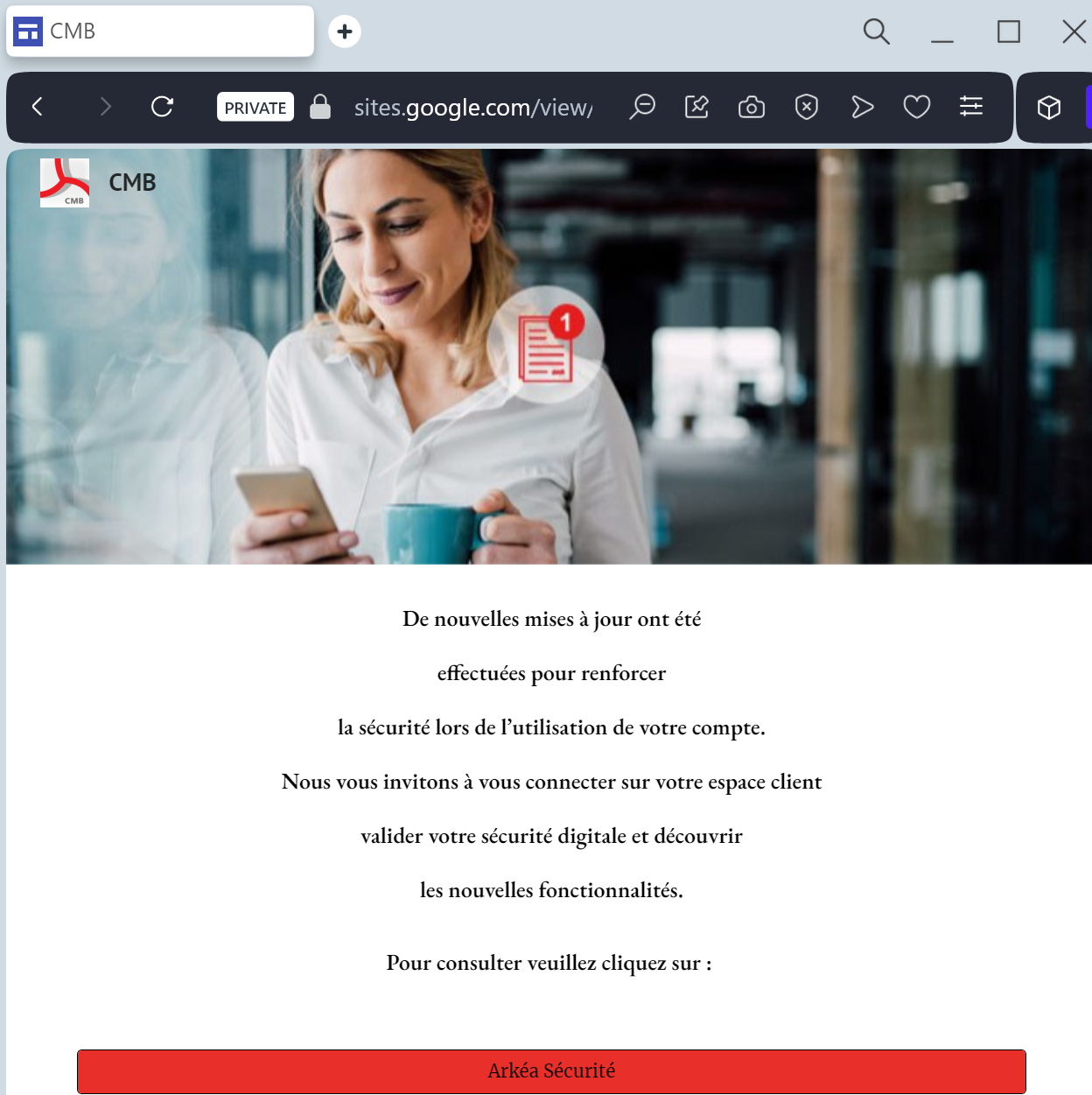
Phishing Method Description
This attack targets users of the CMB Online Banking and the “CMB suivi de compte” mobile app. Scammers use a “Security Alert” pretext, sending out Smishing (SMS) messages claiming that an “unauthorized transaction” has been detected or that the user’s “Digital Key” (Clé Digitale) must be synchronized immediately to avoid account suspension.
The link leads to a professional-looking clone of the CMB portal, featuring the distinctive red and grey triskelion-style logo. This sophisticated phishing kit is designed to harvest:
Identifiant / Login ID
Password / PIN: Captured via a fake interactive virtual keyboard that mimics the bank’s security feature.
Mobile Phone Number
Real-time Authorization: The fake site prompts the victim to confirm a notification in their official CMB app or enter an SMS code. This allows the attacker to authorize a fraudulent wire transfer or register a new “Trusted Device” to the account instantly.
⚠️ Red Flags to Watch For
The Deceptive URL: The official domain is cmb.fr. Phishing sites use addresses like votre-compte-cmb.online, securite-cmb-bretagne.net, or free subdomains like cmb-client.web.app.
Virtual Keyboard Glitches: While the fake site mimics the official numeric keypad, it may load slowly or fail to respond correctly to clicks, as it is capturing your input in real-time.
Unsolicited SMS with Links: CMB officially states they will never include a clickable link in an SMS regarding account security or “blocking” access.
💡 Expert Security Tip: The “Digital Key” Interception
The Method:
This case highlights a Man-in-the-Middle (MitM) attack targeting the French “Clé Digitale” (Digital Key) system. Scammers are not just looking for your password; they are waiting in real-time to intercept your app-based authorization.
The Trap:
When you enter your credentials on this fake page, the attacker simultaneously logs into the actual CMB server. The moment the bank sends a “Push Notification” to your phone to confirm your identity, the phishing site tells you to “Accept the notification on your smartphone to finish synchronization.” By tapping “Confirm,” you are actually authorizing the hacker’s login or a large fraudulent payment.
How to Protect Yourself:
Read Before You Tap: When you receive a confirmation prompt on your smartphone, read the text carefully. If it says “Confirm new device registration” or “Confirm a transfer of X €” while you were just trying to “log in” via a link, REJECT IT immediately.
The “Context” Rule: A digital key notification should only appear if YOU manually accessed the official www.cmb.fr website or opened the official app.
Zero Trust for SMS Links: If an SMS says your account is blocked and provides a link to “unblock” it, it is a scam. Log in directly through your official app to check for any real alerts.
