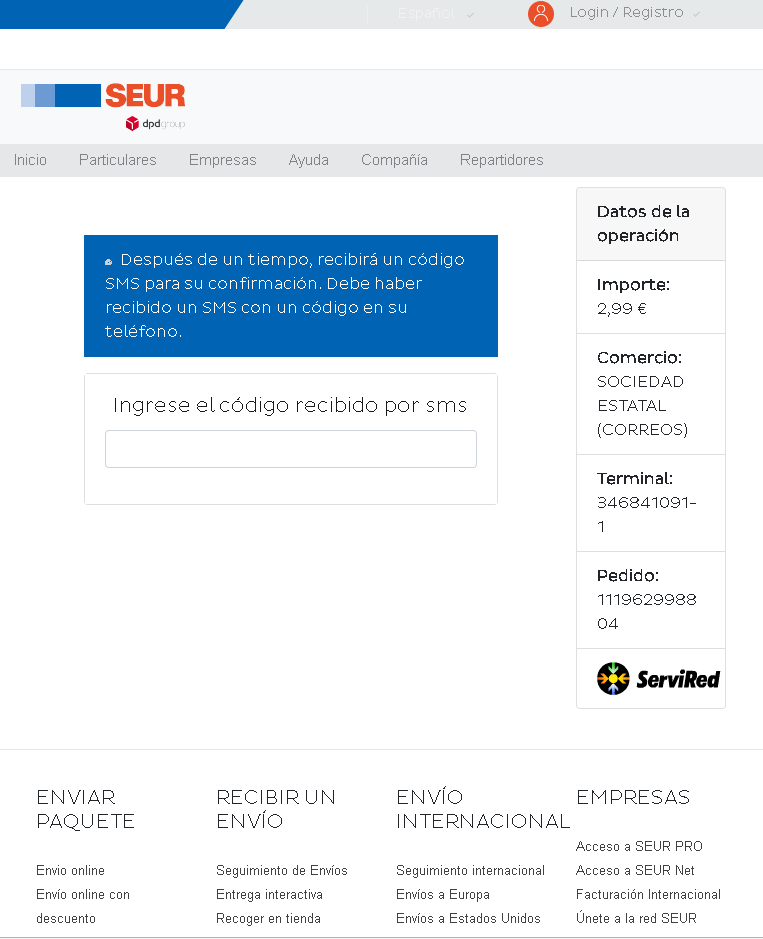
This screenshot shows a phishing page impersonating SEUR, a Spanish courier company. The scam asks the victim to enter an SMS code under the pretext of confirming a delivery or paying a small fee (€2.99). In reality, this code is likely a two‑factor authentication (2FA) code sent by the victim’s bank or card issuer – entering it gives the attacker full access to the victim’s financial account.
Threat Analysis: SEUR Phishing – SMS Code Harvesting (2FA Bypass)
How it works:
The victim receives an SMS or email claiming a package requires a small fee or delivery confirmation. The link leads to this page, which mimics SEUR’s interface. The victim is asked to enter an SMS code, often after having entered card details on a previous page (not shown here). The code is actually a 2FA code from the victim’s bank or card provider. By entering it, the victim allows the attacker to complete a fraudulent transaction or login.
The goal:
The attacker aims to:
- Steal an SMS-based two‑factor authentication code
- Use it together with previously stolen card or banking details to authorize unauthorized payments or account access
Red flags to watch for:
- Suspicious URL: The page is hosted on a domain that is not
seur.com. - SMS code request without context: SEUR does not ask for SMS codes in this manner for a delivery fee.
- Small fee shown: €2.99 is a tiny amount intended to lower suspicion.
- Copied branding: The page uses SEUR’s logo and navigation, but the underlying domain is fake.
What to do:
- Do not enter any SMS code.
- If you are expecting a SEUR delivery, track it directly by typing
seur.cominto your browser. - If you have already entered a code, contact your bank immediately – the attacker may have already used it to authorize a transaction.
- Report the phishing page to SEUR and to the relevant authorities.
Protective measures:
- Never enter an SMS code on a page you reached via a link. Legitimate services only ask for 2FA codes after you have initiated a login on their official site.
- Always type the courier’s official URL directly.
- Enable two‑factor authentication using an authenticator app instead of SMS where possible, to reduce this type of attack.
