These screenshots show a phishing campaign that uses “FreeFire Rewards” as a lure to steal login credentials for either Facebook or Google. Victims are promised in-game rewards and then directed to fake login pages.
Incident Report: This scam layout was logged, cross-checked, and neutralized firsthand by the
Antiphishing.bizsecurity team during our automated link scanning workflows. To protect the public, the phishing source domain has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users detect replica fraud techniques before financial damage occurs.
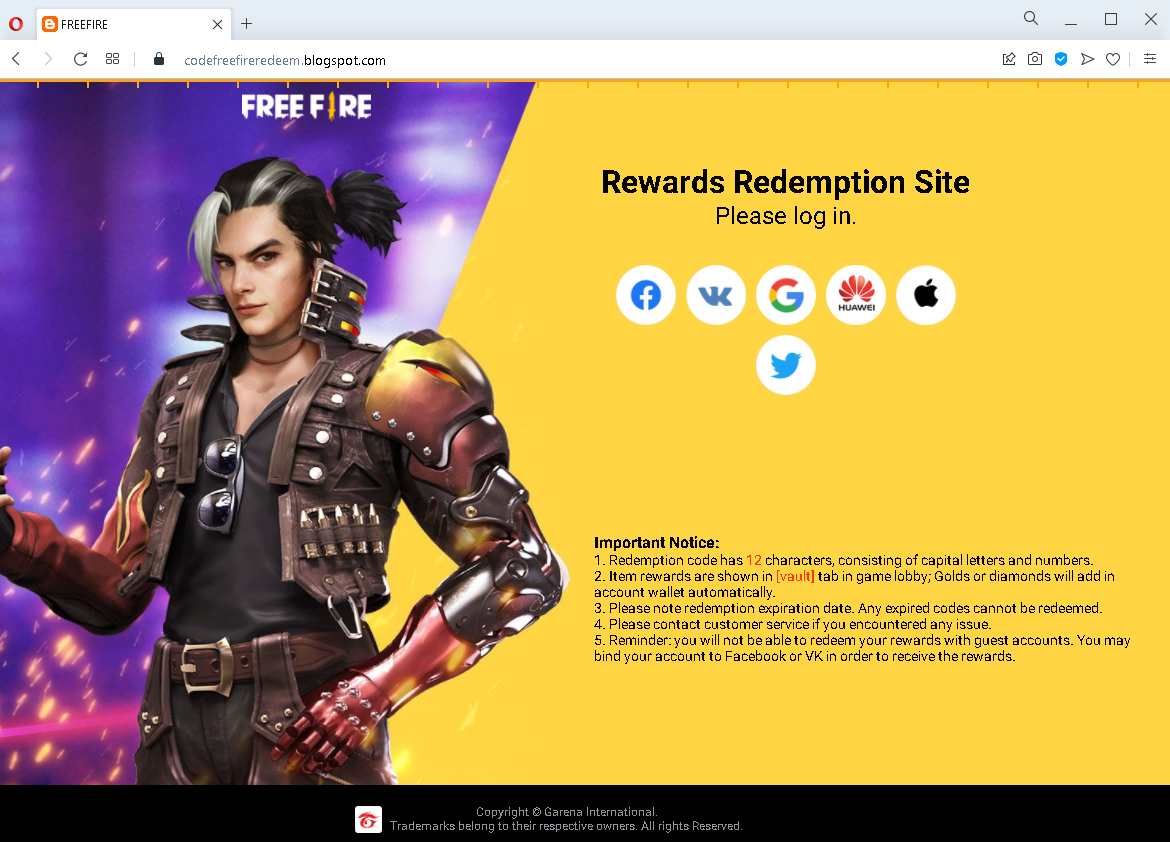
Threat Analysis: FreeFire Reward Phishing – Facebook & Google Credential Harvesting
How the scam works (common flow for both variants):
The victim receives a link (via social media, SMS, or messaging app) promising free rewards for the game FreeFire (e.g., diamonds, skins, or other in-game currency). The link leads to a page titled “Rewards Redemption Site.” The victim is told they must log in to claim the reward. Depending on the variant, the page mimics either the Facebook or Google login interface.
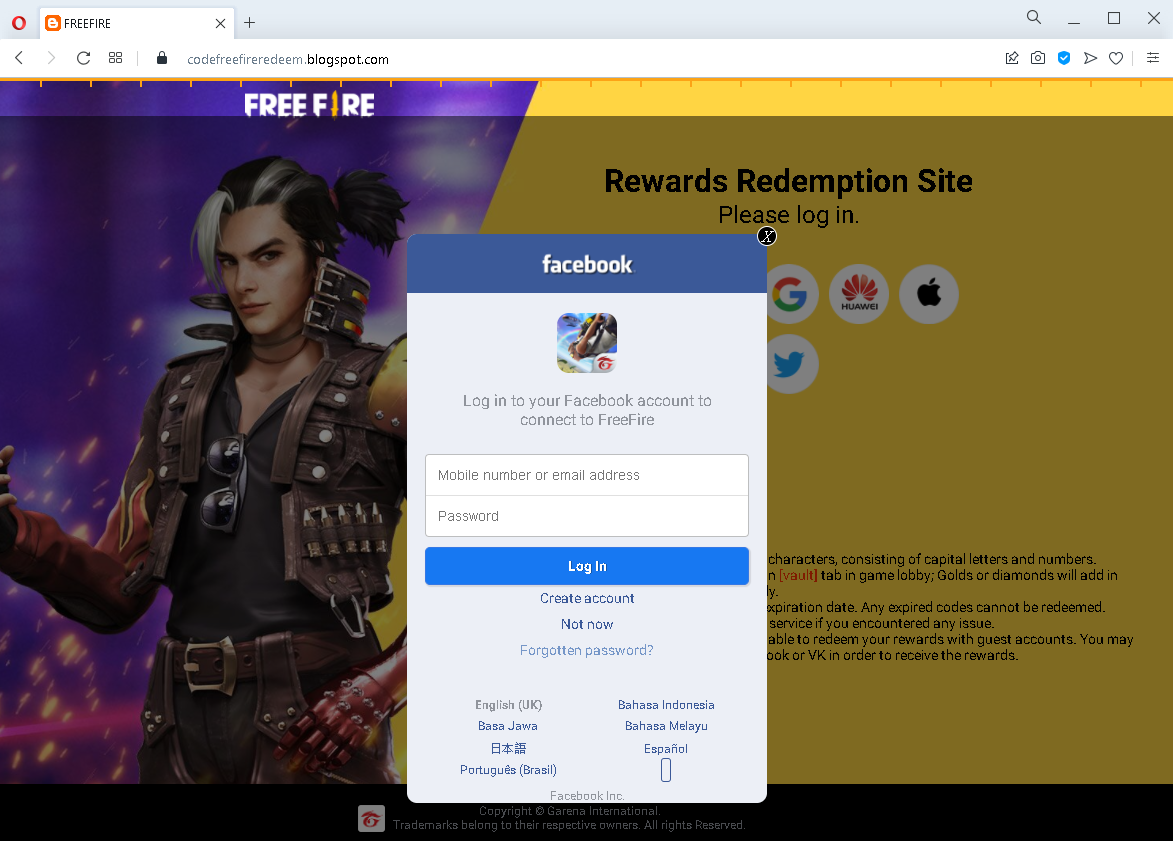
Variant 1 – Fake Facebook Login Page (First Screenshot)
The page asks for:
- Mobile number or email address
- Password
It includes Facebook branding, language options, and a copyright notice for Garena to appear legitimate.
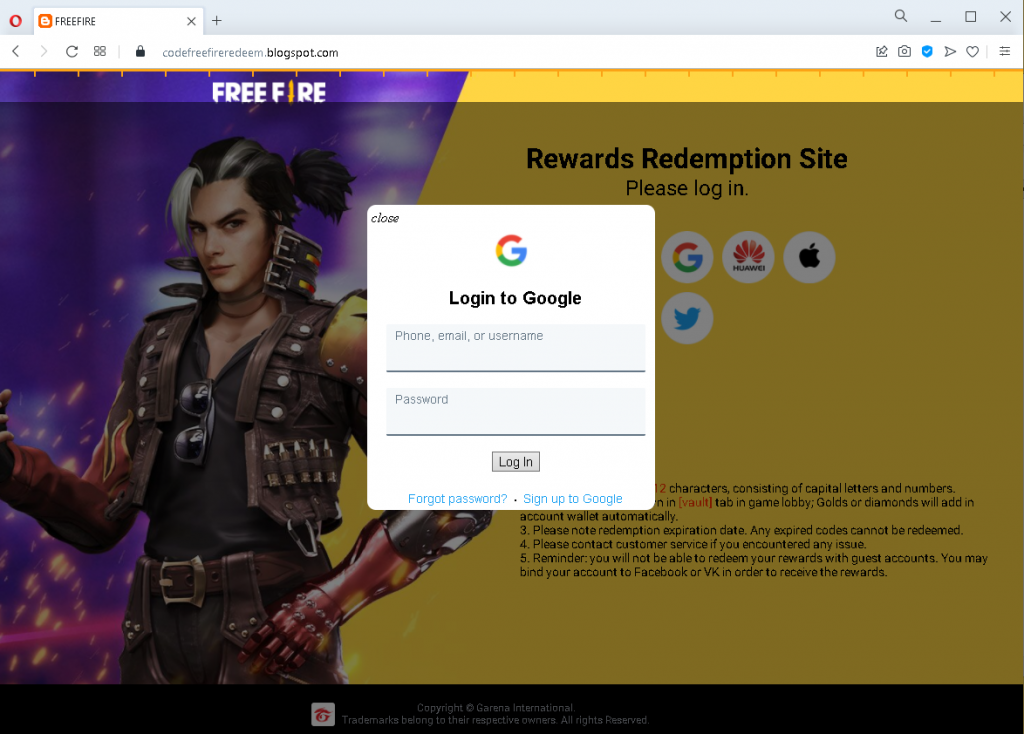
Variant 2 – Fake Google Login Page (Second Screenshot)
The page asks for:
- Phone, email, or username
- Password
It includes Google branding and additional “redemption rules” (e.g., “account wallet automatically,” “expiration date,” “bind your account to Facebook or VK”) to make the offer seem credible.
The goal:
The attacker steals the victim’s Facebook or Google credentials to:
- Take over the victim’s account
- Access linked FreeFire (Garena) game progress
- Use the compromised account to spread the scam to friends
- Attempt credential reuse on other platforms
Red flags to watch for (both variants):
- Suspicious URL: The pages are hosted on domains that are not
facebook.comgoogle.com - Reward lure: FreeFire does not distribute in-game currency through third‑party “Rewards Redemption Sites” that require logging in via Facebook or Google.
- No official branding / inconsistencies: While the pages copy logos and layout, they lack the full security indicators (e.g., proper SSL certificate, two‑factor authentication prompts, personalized security images).
- Unsolicited offer: Any unsolicited message promising free game rewards in exchange for logging in via a link is almost certainly a scam.
- Copyright notice for Garena: The presence of a Garena copyright on a fake Facebook page does not make it legitimate – attackers copy such text to appear credible.
What to do if you encounter this:
- Do not enter your Facebook or Google credentials.
- If you have already entered your credentials, change your password immediately on the real platform (Facebook or Google) and enable two‑factor authentication (2FA).
- Always access official game rewards through the FreeFire app itself – never through external links.
- Report the phishing pages to Facebook, Google, and Garena.
Protective measures:
- Bookmark the official login pages for Facebook (
facebook.comgoogle.com - Use a password manager – it will not autofill on fake domains.
- Enable two‑factor authentication on all your accounts.
- Remember: no legitimate reward requires you to log in via a link sent in a message.
