A phishing campaign targeting Arabic-speaking Snapchat users in the MENA region uses fake password reset pages to steal credentials and bypass two-factor authentication (2FA). Attackers utilize high-fidelity clones of the Snapchat login portal and real-time credential relay tactics to hijack user sessions and private data.
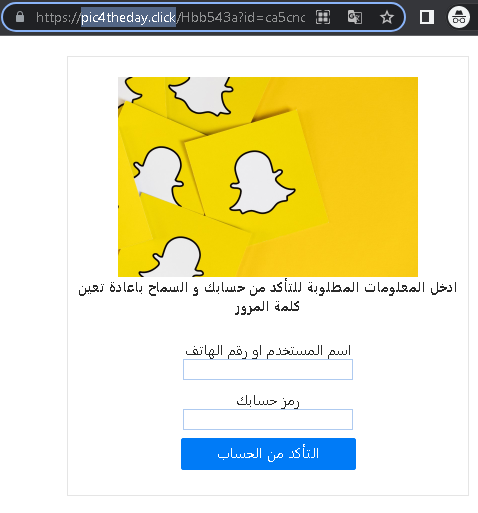
This case highlights a Real-Time Proxy Attack targeting Snapchat, where attackers use fake Arabic-language “Security Breach” notices to intercept user credentials and live 2FA codes, allowing immediate account takeover. The key security tip is the “Initiator” Rule: never enter a 2FA code on a page reached via a link; only provide codes on sites you accessed by manually typing the official URL.
