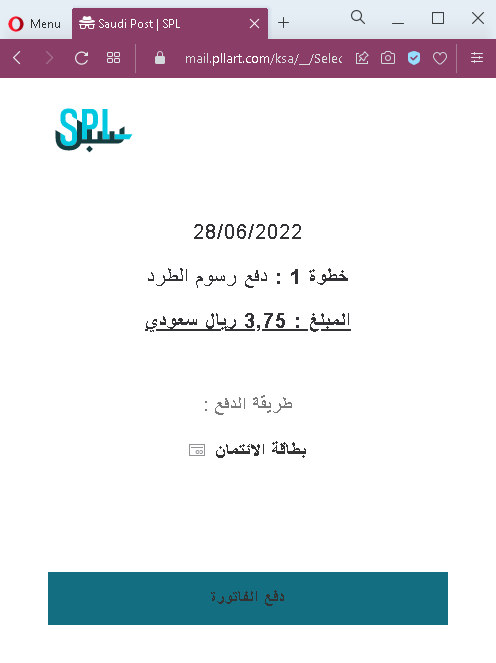
A phishing campaign targeting residents in Saudi Arabia impersonates Saudi Post (SPL) via SMS to steal personal information and credit card data through a fake “address correction” page. The attack uses realistic clones of the official SPL portal to harvest credentials and intercept one-time passwords (OTPs) for fraudulent transactions.
These phishing cases highlight attackers’ use of urgent, fake alerts to steal credentials and financial data through compromised “password reset,” billing, and parcel delivery scenarios. Key protections include ignoring unexpected links, verifying URLs against official domains, and using app-based 2FA to prevent account takeovers.
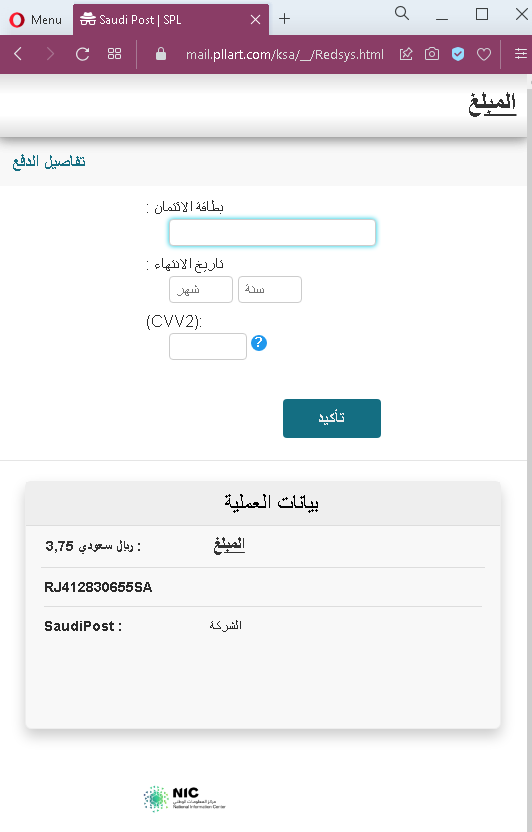
Recent phishing campaigns are exploiting trusted brands through urgent, fake security or billing notifications designed to harvest account credentials and financial data. Attackers are using real-time interception of 2FA codes and small, fake “delivery fees” to bypass security and steal sensitive personal information, including SSNs and CVVs. Always verify alerts directly through official apps rather than links in SMS or email messages.
