A phishing campaign targeting Banca Intesa Beograd customers uses fraudulent SMS and email messages to harvest login credentials and real-time SMS OTPs via a spoofed login page. This Man-in-the-Middle attack aims to steal credentials for the Banca Intesa Mobi app, with fake links often leading to lookalike domains rather than the official bancaintesa.rs site.
Security Notice: This malicious interface was detected, analyzed, and contained firsthand by the
Antiphishing.bizsecurity team during our daily link moderation procedures. To protect the public, the phishing source domain has been safely deactivated within our infrastructure. We document and analyze these live visual patterns to help security researchers and users spot lookalike phishing methods before financial damage occurs.
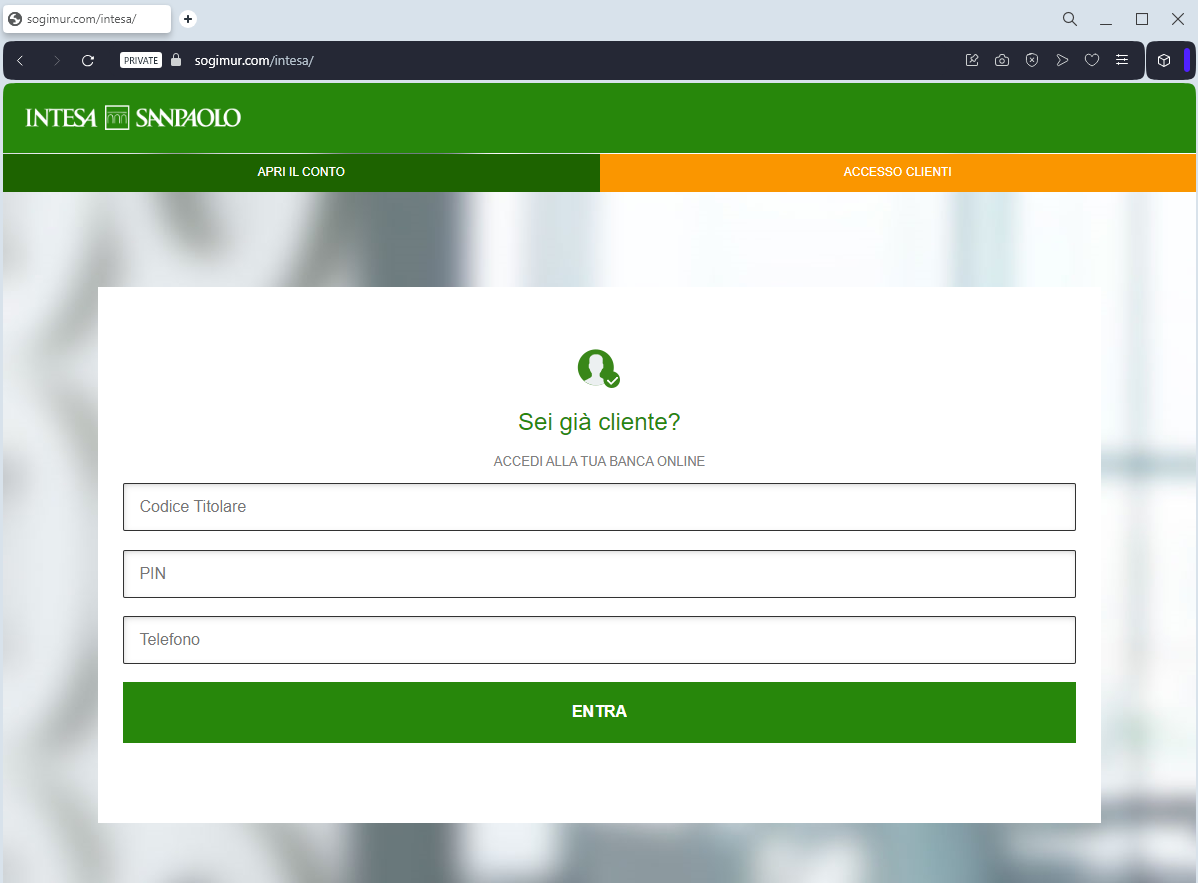
This phishing case targets Intesa Sanpaolo customers, employing smishing/phishing techniques to steal “MyKey” login credentials and real-time security codes to authorize fraudulent transactions. Scammers utilize realistic fake portals and phishing kits to bypass 2FA by acting as a middleman, prompting users to enter legitimate O-Key SMS/app codes directly into the malicious site.
Expert Security Tip: Always manually enter the bank’s URL, and never input O-Key SMS codes on a website, as the attacker is likely proxying your credentials to a live, official banking session.
